|
Listen to post:
Getting your Trinity Audio player ready...
|
A growing percentage of Internet traffic is protected by encryption. While estimates vary, most agree that at least 80% of Internet traffic uses SSL/TLS to ensure confidentiality, integrity, and authenticity of the data being transmitted. According to Google, approximately 95% of web browsing uses the encrypted HTTPS protocol.
This trend toward traffic encryption has been driven by a few different factors. As users become more educated about the differences between unencrypted HTTP and encrypted HTTPS and the threat of various attacks, they are opting for the more secure option wherever possible. Web browser vendors like Google are encouraging this trend by defaulting to the encrypted version of sites and labeling sites that only support HTTP as unsafe and reducing their SEO scores.
The move toward data encryption is a mixed blessing for cybersecurity. On one hand, the widespread use of SSL/TLS can help protect against phishing attacks or the exposure of user credentials and other sensitive data to someone eavesdropping on corporate network traffic. On the other hand, the same encryption that protects against eavesdroppers can also limit the effectiveness of an organization’s cybersecurity tools. Identification of malware and other malicious content with network traffic requires the ability to inspect the contents of packets traveling over the network. If this traffic is encrypted and network security solutions do not have the encryption key, then their threat prevention and detection capabilities are limited.
Network security solutions can overcome these challenges, but it comes at a cost. As the volume of network traffic increases and a growing percentage is encrypted, traditional network firewalls are falling behind, creating unnecessary tradeoffs between network performance and security.
Encrypted Traffic Inspection is a Bottleneck
Some organizations address the challenges that traffic encryption poses to security by performing TLS inspection. Security solutions that have access to the encryption keys used to protect network traffic can decrypt that traffic and inspect it for malicious content or data exfiltration before allowing it to continue on to its destination.
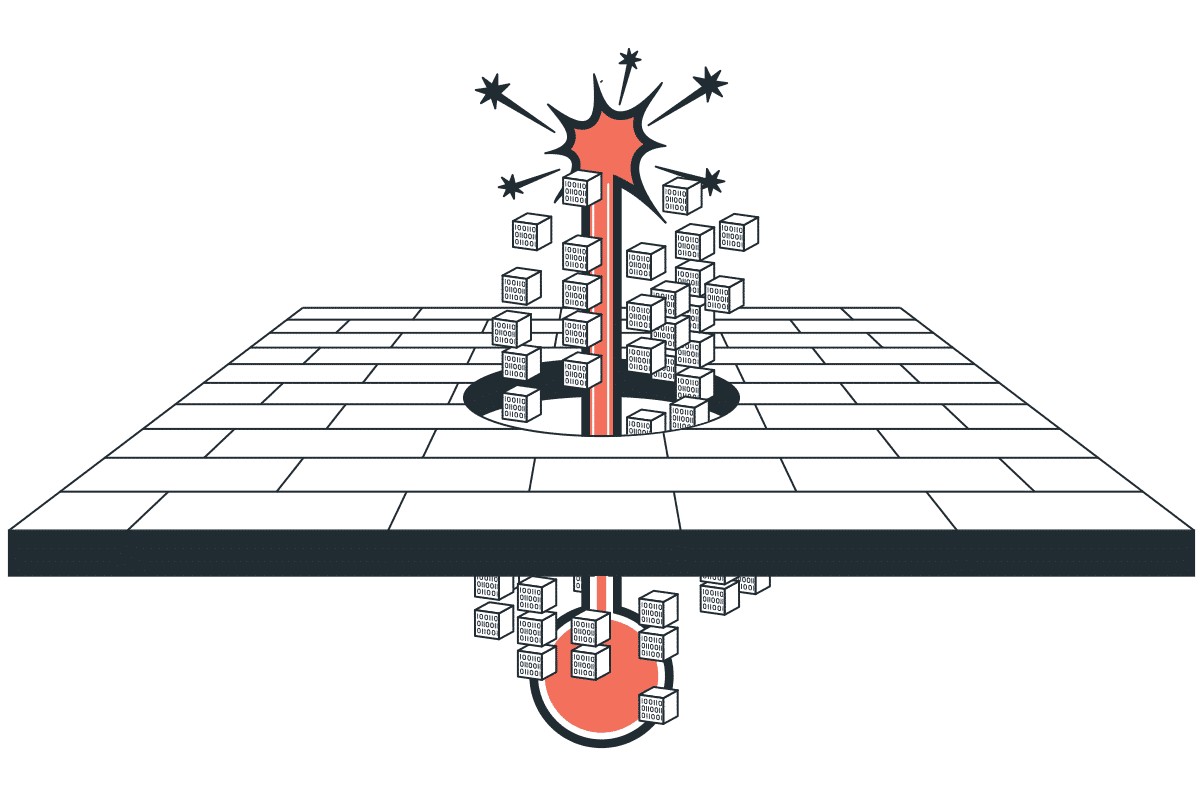
SSL inspection provides the ability to perform the deep packet inspection that security solutions need to do their jobs. However, decryption is a computationally expensive and time-consuming process. With growing volumes of encrypted traffic, decryption functionality within security solutions can create a significant bottleneck and degrade network performance. These issues are exacerbated by the fact that multiple solutions within an organization’s security architecture may need insight into the contents of network packets to fulfill their role. For example, firewalls, intrusion prevention systems (IPSs), secure web gateways (SWGs), and other security solutions may decide whether to allow or block traffic based on its contents.
The Upside-Down World of Networking & Security | WebinarDecrypting TLS traffic can exhaust these security tools’ compute capacity, creating a bottleneck. If an organization has deployed multiple solutions that independently perform TLS decryption and deep packet inspection, then the effects of decryption on network performance are cumulative.
TLS inspection is essential to identifying and blocking threats before they enter an organization’s network and to stopping data exfiltration before it becomes a breach. However, the costs of doing so can be high, creating a tradeoff between network performance and security.
SASE Enables Scalable Enterprise Security
TLS inspection is a vital capability for many security solutions because it enables deep packet inspection and detection of malicious content within network traffic. One of the primary barriers to implementing TLS inspection at scale is that security solutions’ resources are exhausted, which can create significant latency as each tool in an organization’s security architecture individually decrypts and inspects network traffic.
Secure Access Service Edge (SASE) provides the ability to perform TLS inspection while minimizing the impacts on network performance and latency. Three core capabilities that make this possible include:
#1. Solution Convergence: SASE solutions converge a full network security stack into a single solution. This makes it possible to decrypt traffic once and provide all security solutions with access to the decrypted data for inspection without jeopardizing security. By eliminating the individual traffic decryption by each device, SASE dramatically decreases the impact of TLS inspection on network performance.
#2. Cloud-Native Design: SASE points of presence (PoPs) are built with cloud-native software. By deploying security functionality in the cloud, SASE can take advantage of cloud scalability, eliminating the bottlenecks created by computationally expensive decryption operations.
#3. Cost Saving: By offloading all the TLS inspection work to an elastic cloud-native SASE service, enterprises don’t need to worry about upgrading on-premises appliances prematurely. This saves the organization both the procurement and the integration costs of the new appliances.
TLS inspection is vital to companies’ ability to protect themselves against evolving cyber threats. As the volume of encrypted traffic grows, traditional firewalls can’t keep up, creating tradeoffs between network performance and security. SASE is vital to the future of enterprise security because it enables strong corporate network security without compromising performance.
Cato provides the world’s most robust single-vendor SASE platform, converging Cato SD-WAN and a cloud-native security service edge, Cato SSE 360, including ZTNA, SWG, CASB/DLP, and FWaaS into a global cloud service. With over 75 PoPs worldwide, Cato optimizes and secures application access for all users and locations, and is easily managed from a single pane of glass. Learn more about improving your network visibility, performance, and security with Cato SASE Cloud by signing up for a demo today.