SSE 360: Security as a Service
Enterprises are facing a tough choice between running complex infrastructure with multiple network and security point solutions or paying heavily to service providers to “bundle it” for them. Sizing security appliances for different locations often means having inconsistent security policies across the network. Cato provides the only SASE and SSE platform built with the global reach, self-service, and agility of the cloud. Cato replaces security point solutions with a converged cloud-native security stack built using the Cato Single Pass Cloud Engine (SPACE).
Cato SSE 360 is built directly into the Cato SASE Cloud. Security policies are applied consistently across all traffic traversing the network, eliminating the need for disparate edge security devices.
Cloud-native Security for Today’s Enterprises
With Cato SSE 360, you gain the benefit of consistent security across your entire network while offloading the day to day management to Cato. No more capacity planning, software upgrades, operational complexities, or hidden costs. At the same time, you maintain granular control of all your security policies, with easy configuration through Cato’s Management Application.
Our network was designed with security in mind. All our PoPs are interconnected using fully-meshed, encrypted tunnels. Customers connect to Cato through encrypted tunnels, established by the Cato Socket (a zero-touch appliance deployed at physical locations), or through IPsec tunnels from existing devices. All our security capabilities are backed by our massive data warehouse to detect and protect your network from the most advanced threats. As part of the service, Cato employs a dedicated research team of security experts, Cato Security Research Labs, which continuously monitor, analyze and tune all the security engines, risk data feeds, and databases to optimize customer protection.
Access Control Across Your Network
Cato provides enterprises with access control capabilities through our next-generation firewall (NGFW) and secure web gateway (SWG). Our NGFW provides full application awareness with the ability to inspect the payload of packet data and distinguish between different types of web traffic. Cato’s SWG allows customers to monitor, control and block access to websites based on predefined and customizable categories.
Next-generation Firewall
The Cato NGFW inspects both WAN and Internet traffic. It can enforce granular rules based on network entities, time restrictions, and type of traffic. The Deep Packet Inspection (DPI) engine classifies the relevant context, such as application or services, as early as the first packet and without having to decrypt the payload. Cato provides a full list of signatures and parsers to identify common applications. In addition, custom application definitions identify account-specific applications by port, IP address or domain.
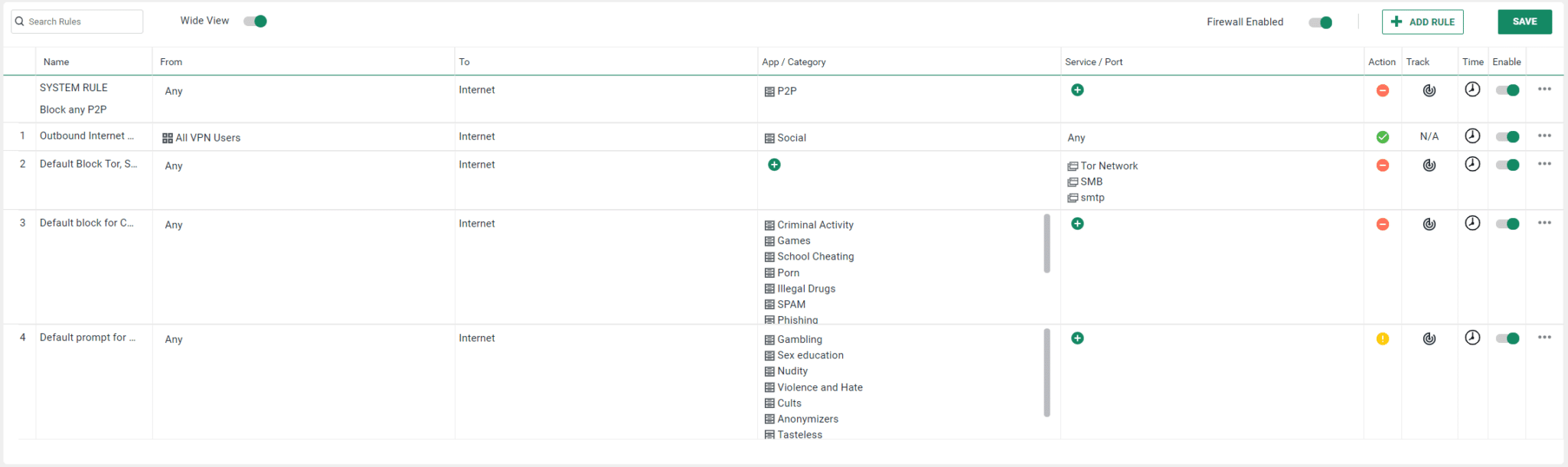
Internet Firewall Rules
Secure Web Gateway
Cato provides a SWG to give you granular control over your Internet-bound traffic, enabling enforcement of corporate policies and preventing downloads of unwanted or malicious software. We provide predefined policies for dozens of different URL categories and support custom rules, enhancing the granularity of web access control. As with the rest of our service, the SWG is easily managed through Cato’s management portal and covered by a full audit trail.
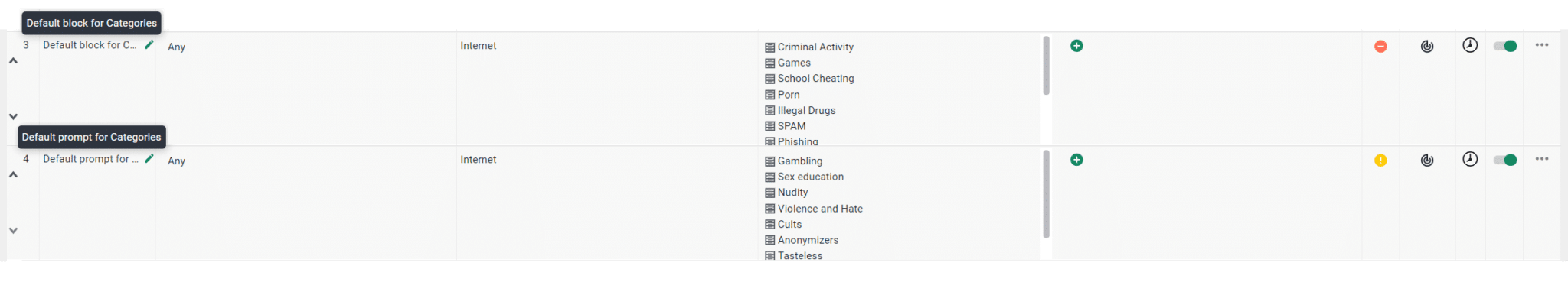
URL Categories and Default Action
Cloud and Data Security
Cato’s SASE Cloud enables enterprises to gain better visibility and control over their cloud-hosted applications. Cato’s Cloud Access Security Broker (CASB) provides in depth visibility into SaaS usage and enables IT leaders to better cope with shadow IT. Cato’s Data Loss Prevention (DLP) provides protection from accidental or malicious attempts to upload or extract sensitive information.
Cloud Access Security Broker (CASB)
Cato’s Cloud Access Security Broker (CASB) provides IT managers with comprehensive insight into their organisation’s cloud application usage, covering both sanctioned and unsanctioned (Shadow IT) applications. Cato’s CASB enables assessment of each SaaS application in order to evaluate its potential risk, and definition of highly granular and flexible access rules to ensure least privileges and minimal risk exposure.
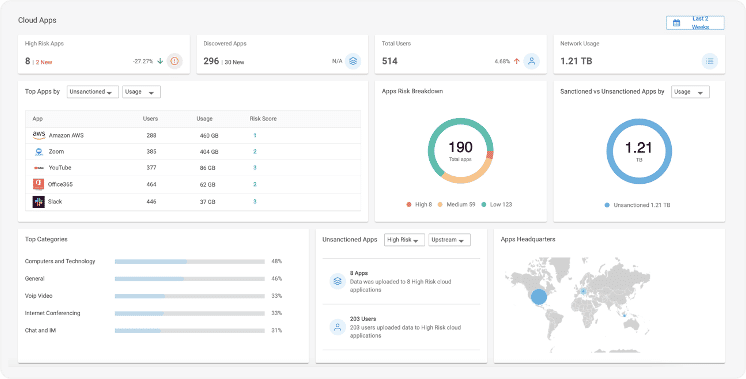
Shadow IT Dashboard
Data Loss Prevention (DLP)
Cato’s Data Loss Prevention (DLP) enables enterprises to protect sensitive information from being uploaded to, or extracted from, cloud or physical datacenters. The solution inspects traffic to detect sensitive data or file types and takes the defined action when a match is found. DLP helps enterprises achieve regulatory compliance, for example with the General Data Protect Regulation (GDPR), by detecting Private Identifiable Information (PII), as well as with industry specific standards such as Payment Card Industry (PCI) and Health Insurance Portability and Accountability Act (HIPAA).
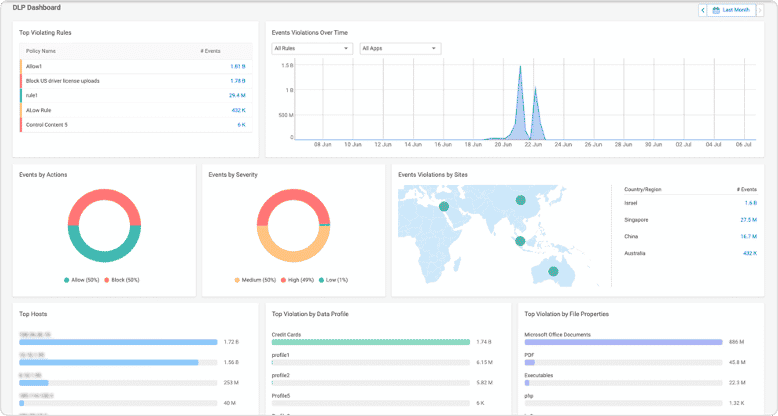
DLP Dashboard
Remote Browser Isolation (RBI)
Cato RBI provides secure browsing through a virtualization service that streams web pages safely to the user’s device. Page code is executed remotely, protecting users from ransomware, phishing and other threats. Rather than block unknown sites, RBI provides an ‘Isolate’ option to let users browse them safely. It adds another layer of protection against user error and new, undocumented sites and attacks. It’s a seamless part of the Cato service, accessible with a few clicks, with nothing to install or patch.
Advanced Threat Prevention
As part of Cato’s Advanced Threat Protection, Cato offers next-generation anti-malware (NGAM) protection and Intrusion Prevention System (IPS) capabilities. Both services inspect WAN and Internet traffic. Additionally, Cato PoPs inspect TLS-encrypted traffic in the massively-scalable Cato Cloud, so there is no scaling constraints with on-premises equipment or additional latency from cloud-based traffic inspection.
Next Generation Anti Malware
Malware Detection and Prevention leverages multi-layered and tightly-integrated anti-malware engines. First, a signature and heuristics-based inspection engine, which is kept up-to-date at all times based on global threat intelligence databases, scans files in transit to ensure effective protection against known malware. Second, we’ve partnered with SentinelOne, an industry leader, to leverage machine learning and artificial intelligence to identify and block unknown malware. Unknown malware can come as either zero-day attacks or, more frequently, as polymorphic variants of known threats that are designed to evade signature-based inspection engines. With both signature and machine learning-based protections, customer data remains private and confidential, as Cato does not share anything with cloud-based repositories.
Managed Intrusion Prevention System (IPS)
Cato delivers a fully managed and adaptive cloud-based IPS service. Cato Research Labs updates, tunes and maintains context-aware heuristics, both those developed in house (based on big-data collection and analysis of customers’ traffic) and those originating from external security feeds. This dramatically reduces the risk of false positives compared to other IPSs that lack an experienced SOC behind them. Cato Cloud scales to support the compute requirements of our IPS rules, so customers don’t have to balance protection and performance to avoid unplanned upgrades as processing load exceeds available capacity.
- Identify deviations from normal or expected traffic based on behavioral signatures
- Block known compromised or malicious IPs based on reputational feeds
- Stop traffic based on the source or destination country
- Validate packet conformance to the protocol, reducing the attack surface from exploits using anomalous traffic
- Protect against known CVEs and rapidly adapt to identify new vulnerabilities
- Stop outbound traffic to C&C servers
- Detect and block bots

IPS Protection Engine
Managed XDR to Reduce Dwell Time
Cato’s Managed XDR enables enterprises to offload the resource-intensive and skill-dependent process of detecting compromised endpoints to the Cato SOC team. Cato seamlessly applies a full Managed XDR service to customer networks. We automatically collect and analyze all network flows, verify suspicious activity, and notify customers of compromised endpoints. This is the power of networking and security convergence to simplify network protection for enterprises of all sizes.








