Cato XDR ist die branchenweit erste SASE-basierte Erkennungs- und Reaktionslösung, die Sicherheitsteams mit granularen und effizienten Tools zur Untersuchung und Beseitigung von Bedrohungen ausstattet. Die KI- und ML-Algorithmen von Cato XDR helfen bei der Identifizierung von Bedrohungen im massiven Data Lake und machen sie für die Analyse und Behebung innerhalb der Cato Management Application überschaubar.
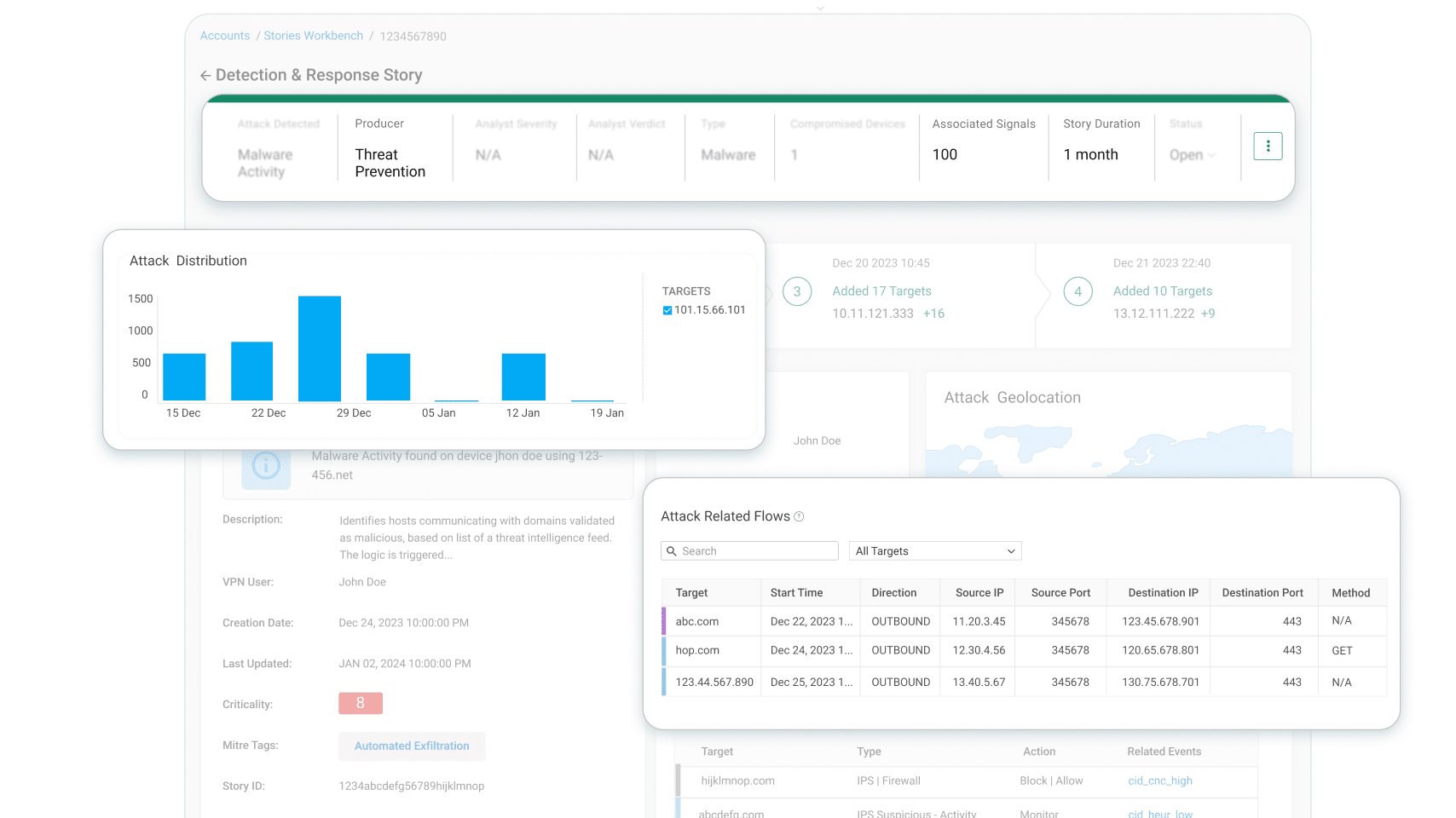
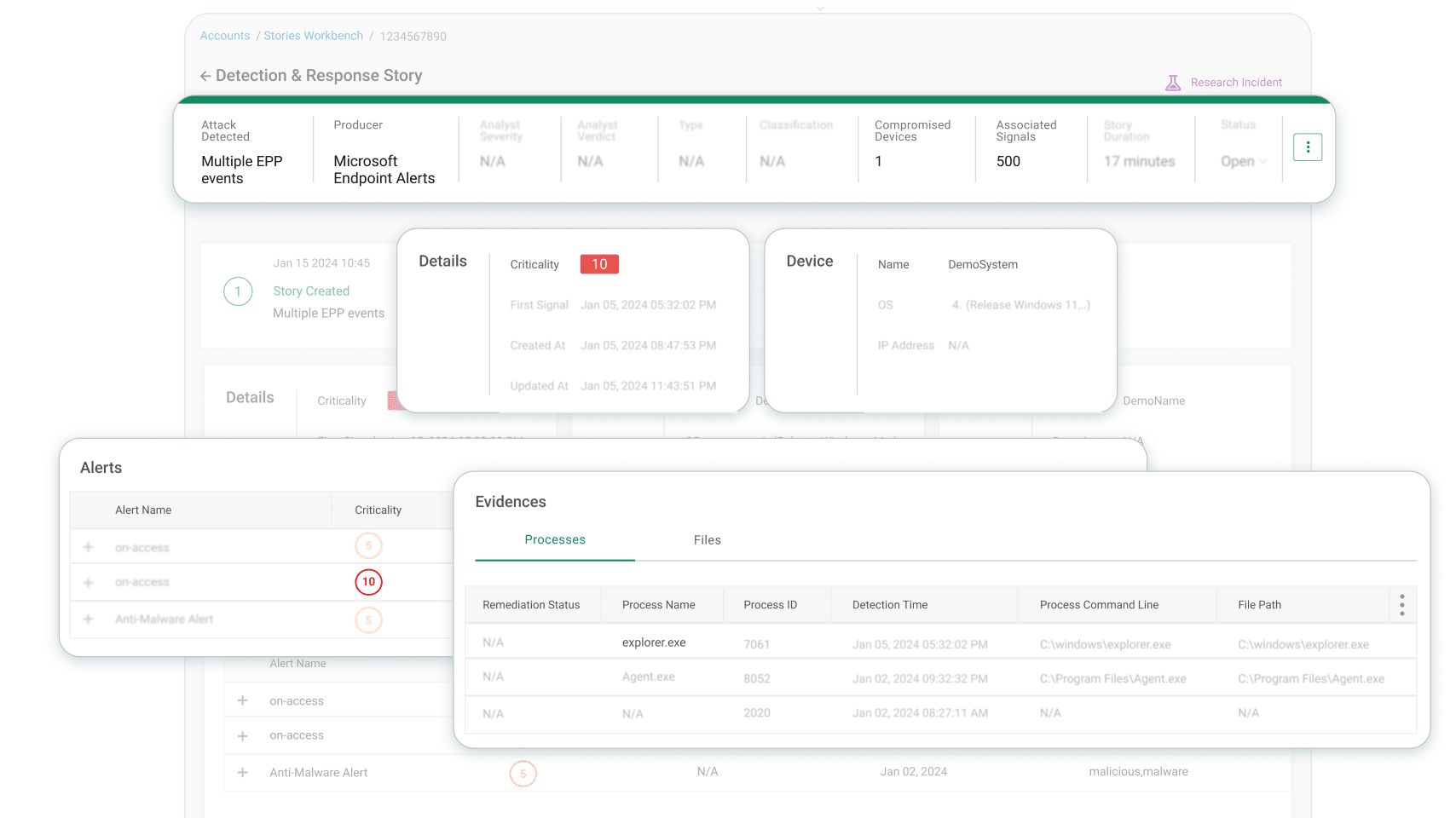
Cato XDR fasst die von den Echtzeit-Sicherheits-Engines von Cato generierten Block-Ereignissen zusammen und gruppiert sie zu einem einzigen Bedrohungsabwehrvorfall. Diese Vorfälle helfen den Sicherheitsteams, die Alarmmüdigkeit zu überwinden, ein gefährdetes Gerät sofort zu erkennen und geeignete Maßnahmen zur Eindämmung und Behebung zu ergreifen.
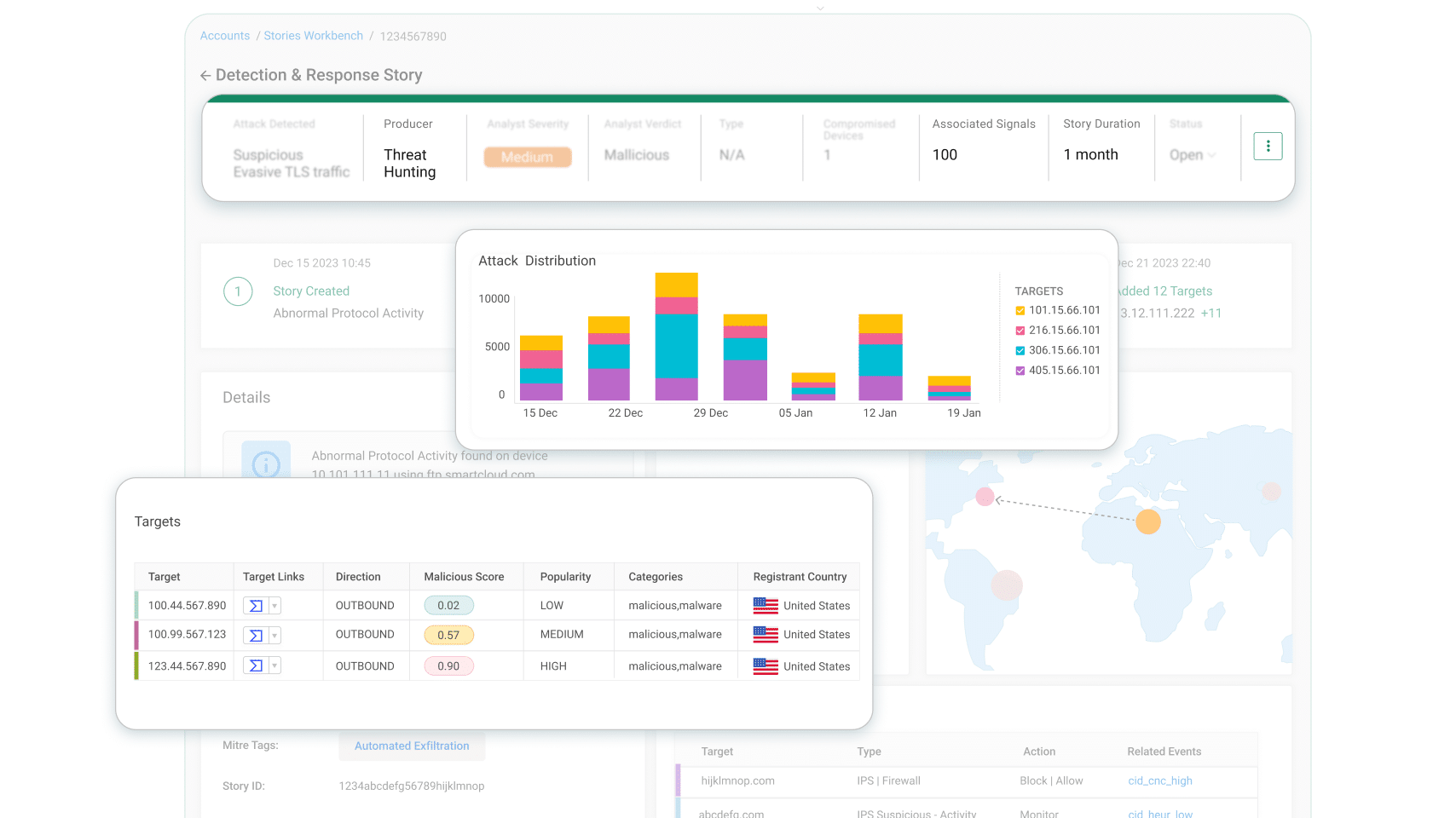
Cato XDR Threat Hunting-Vorfälle werden von Catos AI/ML-Engines erstellt. Die Threat Hunting-Engine durchsucht den Data Lake kontinuierlich nach anomalen Indikatoren für residente Bedrohungen, die von den Präventionsschichten nicht blockiert wurden. Die Threat Hunting-Engine fasst die verschiedenen Signale zu einem einzigen Vorfall zusammen, der von den Sicherheitsanalysten weiter untersucht wird. Darüber hinaus schlagen ML-Algorithmen eine Risikobewertung für jeden Vorfall vor, um Sicherheitsteams bei der Priorisierung der Untersuchung von Bedrohungen zu unterstützen.
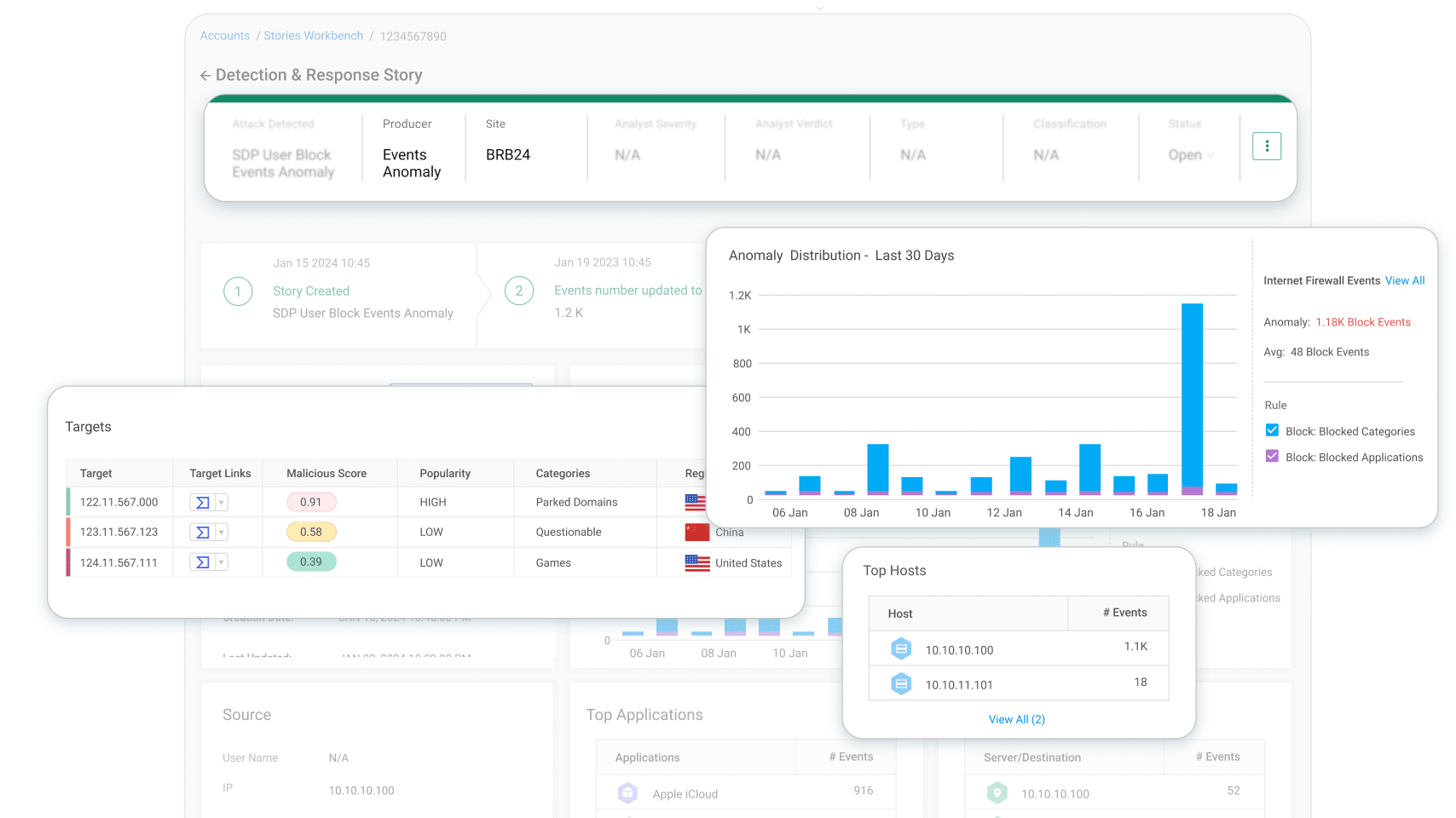
Cato XDR integriert EUBA (End-User Behavioral Analytics)-Funktionen, um ungewöhnliches Verhalten zu erkennen, das auf eine böswillige Absicht hinweisen könnte. AI/ML-Engines für die Anomalieerkennung vergleichen die Netzwerkaktivität des Nutzers mit einer vorberechneten Basislinie und warnen bei verdächtigen Abweichungen durch die Erstellung von Anomalie-Erkennungsvorfällen. Die Sicherheitsteams erhalten detaillierte Informationen und Einblicke, um den gemeldeten Vorfall effizient zu untersuchen und festzustellen, ob es sich um einen bösartigen oder harmlosen Vorfall handelt, und entsprechende Maßnahmen zu ergreifen.
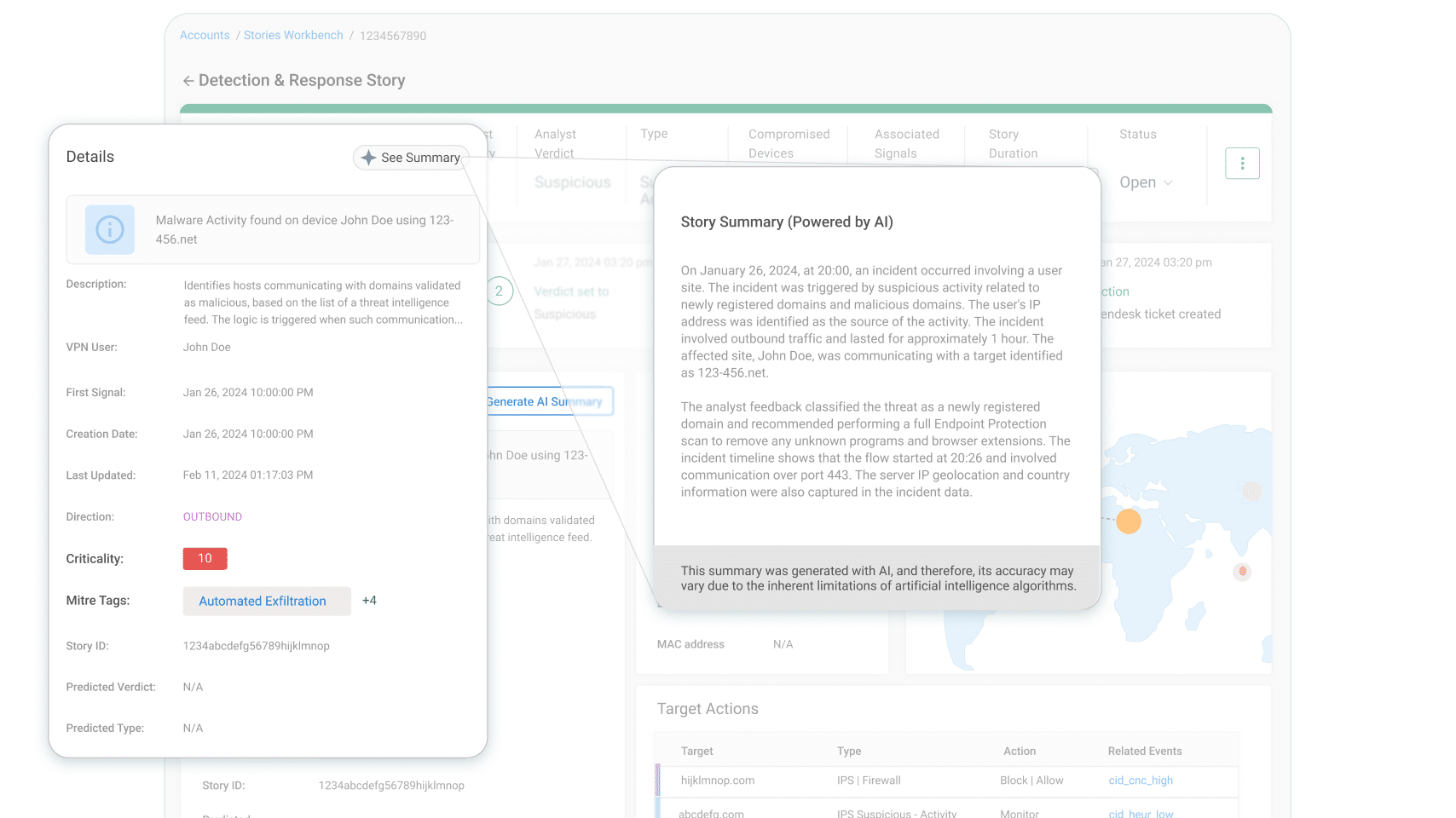
Cato XDR setzt mehrere KI-Technologien ein, um einen effizienten Betrieb von Sicherheitsteams zu ermöglichen. Generative KI wird im „Storyteller“ des Cato XDR-Vorfalls verwendet, der die Datenpunkte eines Vorfalls nahtlos mit einer Threat Narrative verknüpft und so eine leicht verständliche und einfach zu kommunizierende Zusammenfassung erstellt.
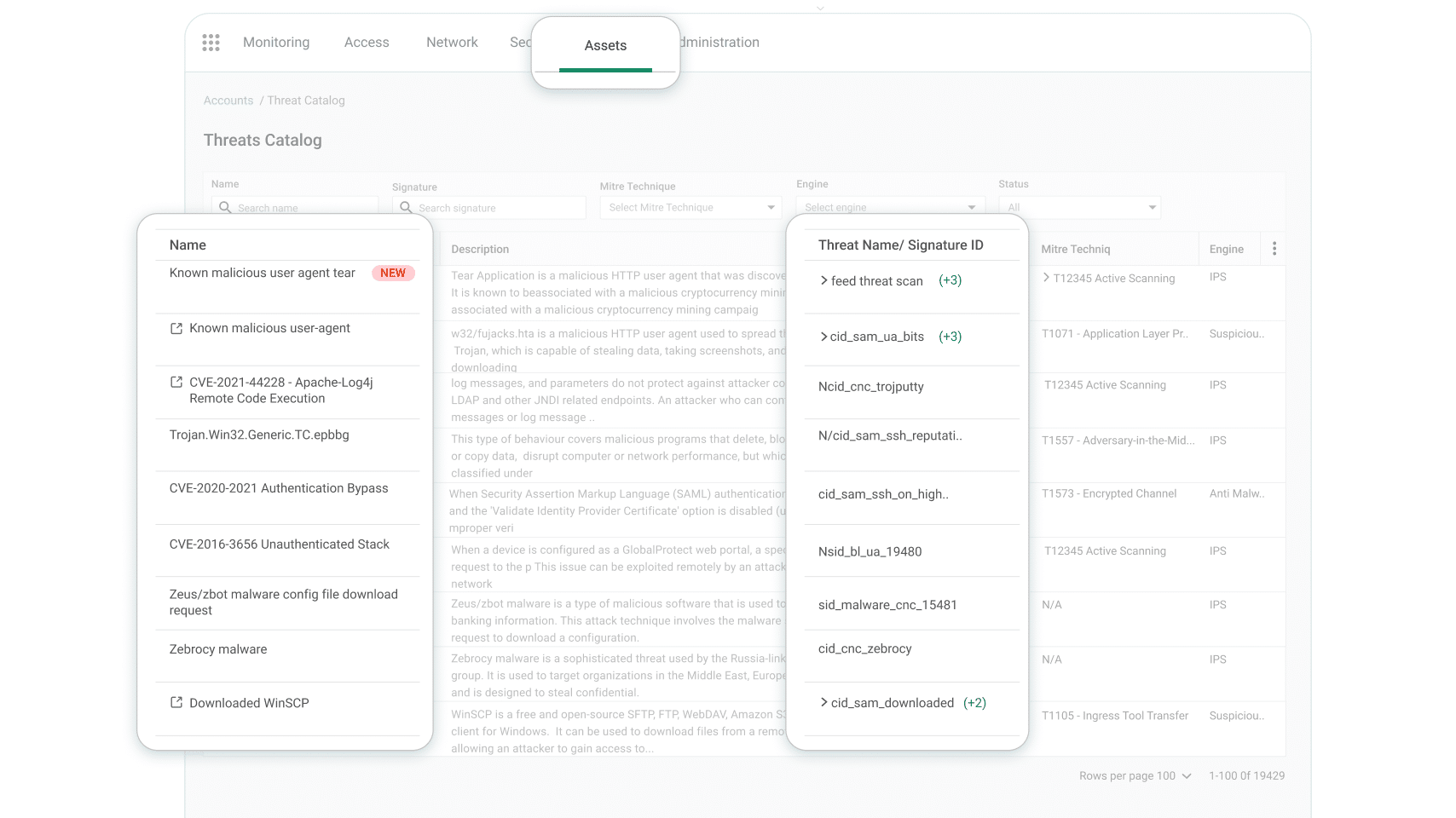
Zur weiteren Unterstützung der Bedrohungs- und Risikoanalyse werden Cato XDR-Vorfälle spezifischen MITRE ATT&CK TTPs (Tactics Techniques and Procedures) zugeordnet, so dass Sicherheitsteams den Fortschritt des Angreifers in der Angriffskette genau verstehen können.
Eine häufige Herausforderung bei XDR-Lösungen besteht darin, dass Abhilfemaßnahmen über unterschiedliche Plattformen ausgeführt werden.
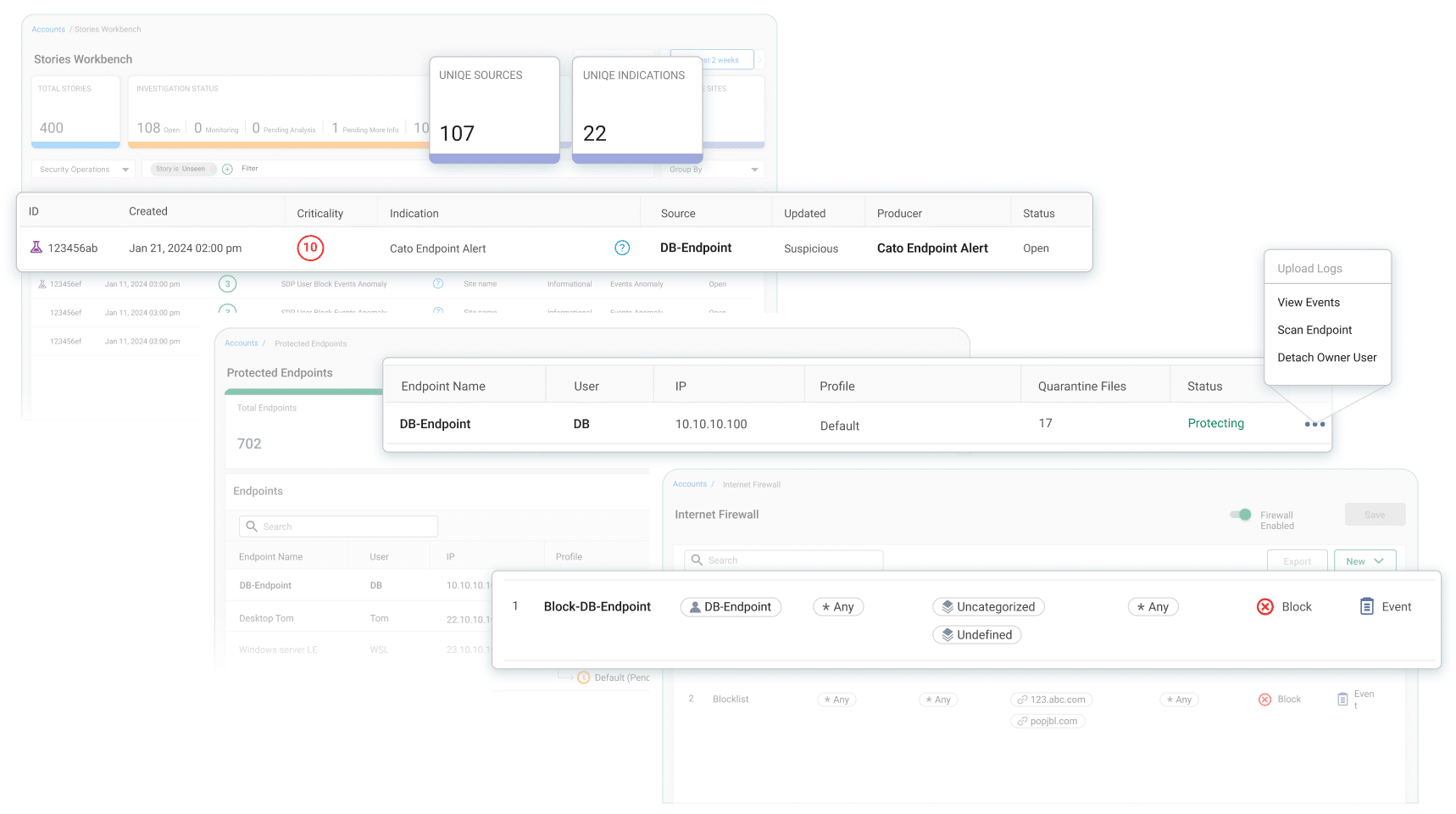
Cato XDR ist eine native Funktion der Cato SASE Cloud-Plattform, die es Sicherheitsteams ermöglicht, aktive Bedrohungen innerhalb der gleichen Lösung zu beseitigen. Firewall-Regeln zur Eindämmung von Endpoints und Angriffen lassen sich innerhalb von Minuten einrichten, um bösartigen Datenverkehr vom und zum Internet zu blockieren und die weitere Verbreitung von Malware über das WAN zu verhindern. Der EPP-Scan kann sofort ausgelöst werden und bereinigt möglicherweise infizierte und kompromittierte Endpoints proaktiv – alles über eine einzige Verwaltung.
Cato XDR ist eine offene XDR-Lösung, die Rohdaten von nativen Sensoren der Cato SASE Cloud-Plattform, angereichert mit Ereignissen von externen Sensoren, wie z. B. EDR-Lösungen von Drittanbietern, in einem einzigen Data Lake sammelt. Cato XDR nutzt fortschrittliche KI- und ML-Algorithmen für die Bedrohungsjagd und Anomalieerkennung. Die Algorithmen wurden von ehemaligen Sicherheits- und Datenanalysten des Militärs entwickelt, auf Petabytes von Daten und Billionen von Ereignissen trainiert und haben sich bereits bei Zehntausenden von bestätigten Sicherheitsvorfällen bewährt. Cato XDR ermöglicht es SOC-Teams, die Verweildauer von Bedrohungen zu verkürzen und Sicherheitsvorfälle schnell zu beheben.
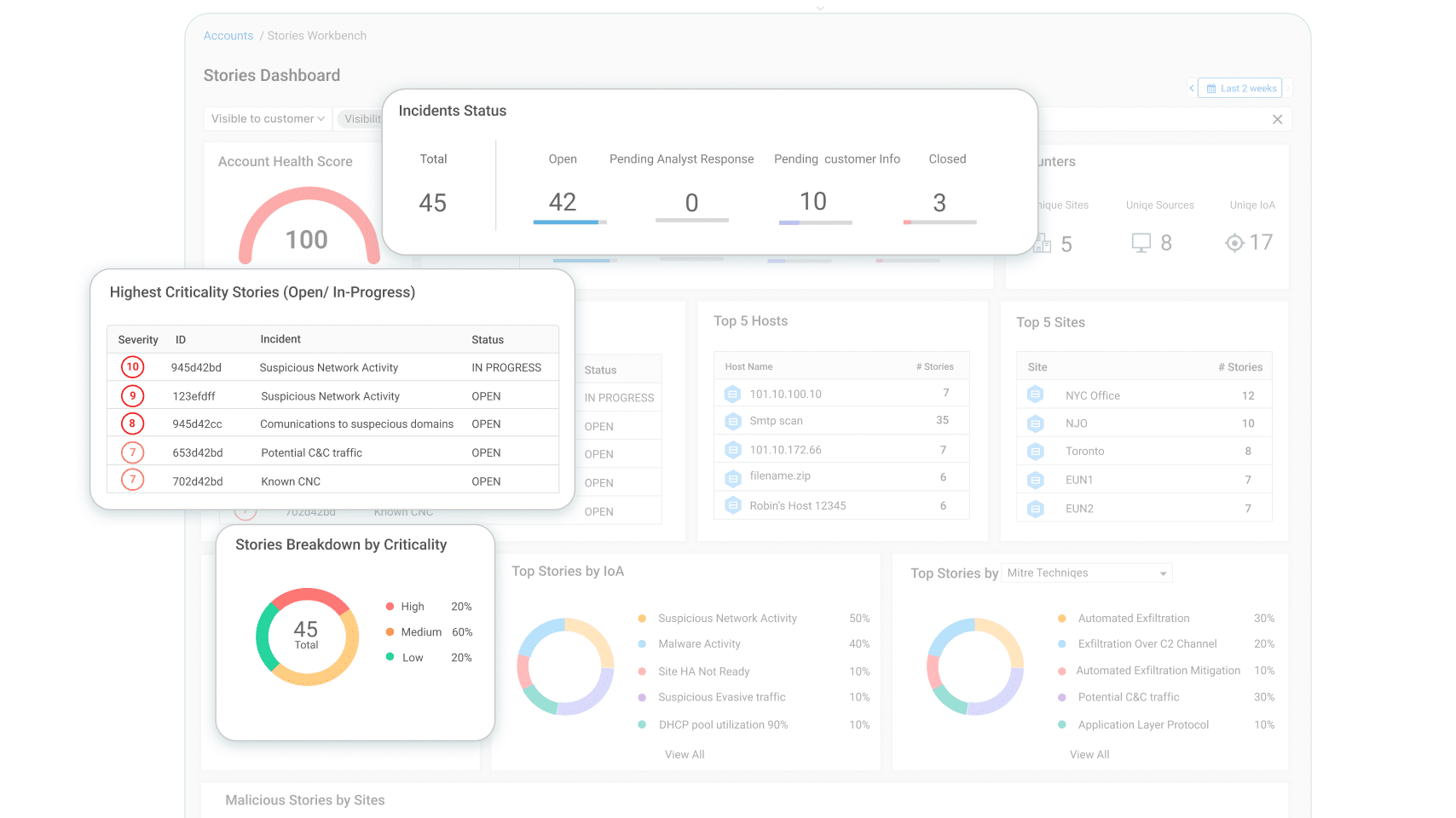
Cato XDR bietet SOC-Teams eine einzige Konsole zur Verwaltung des gesamten Lebenszyklus von Vorfällen. Das XDR-Dashboard in der Cato Management Application (CMA) zeigt alle Vorfälle, ihren Status, ihr ML-berechnetes Risiko und ihre Priorität. Die Untersuchung einzelner Vorfälle ist nur einen Mausklick entfernt, mit einer gemeinsamen Struktur der Datenpräsentation für weitere Analysen, angereichert durch KI-gestützte Erkenntnisse und Empfehlungen. Die Behebung erfolgt über dieselbe Schnittstelle, so dass SOC-Teams nicht zwischen verschiedenen Verwaltungskonsolen wechseln müssen, was die Effizienz steigert und die Gefahr menschlicher Fehler verringert.
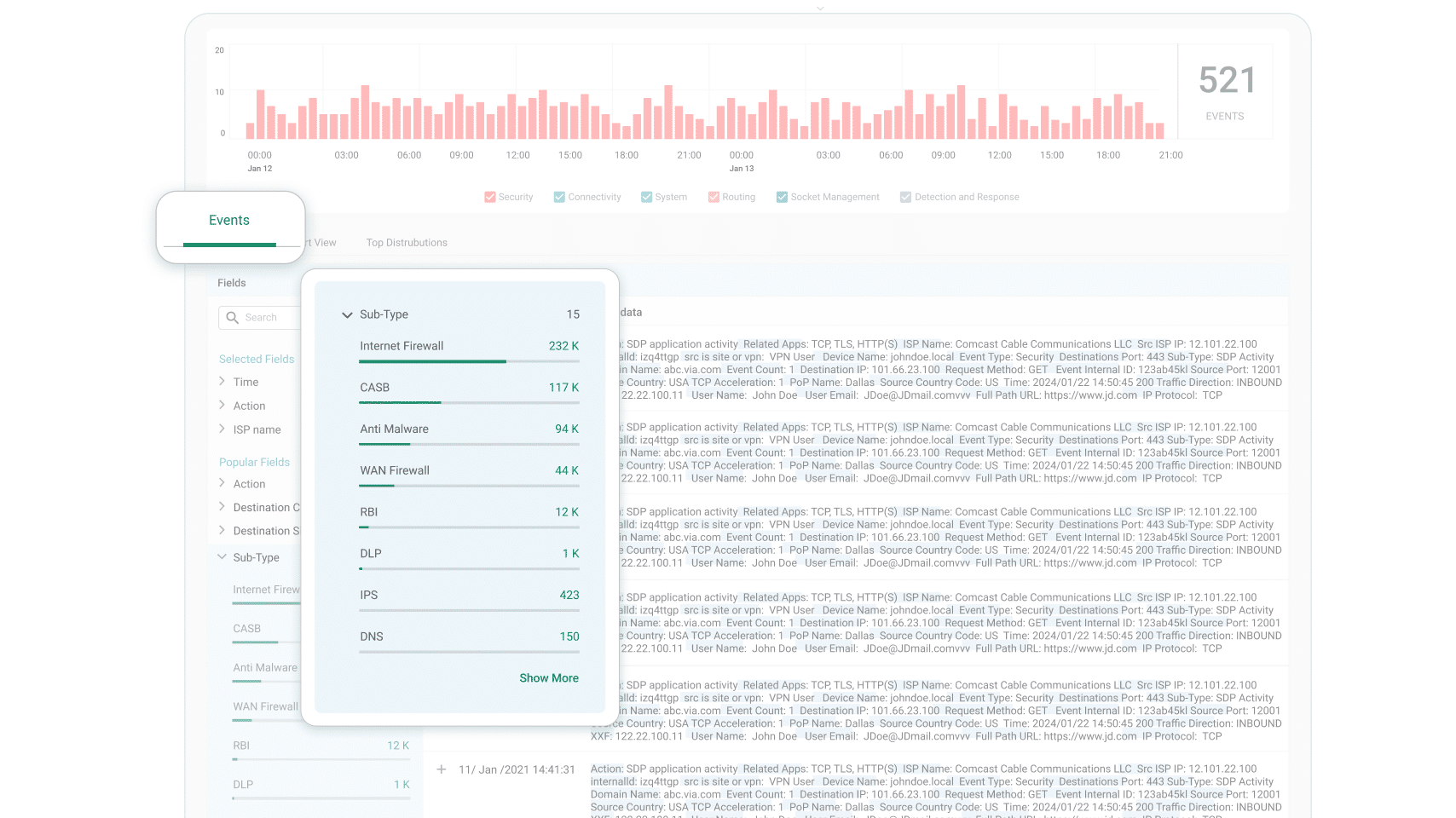
Cato XDR nutzt die Sicherheitsfunktionen der Cato SASE Cloud-Plattform als native Sensoren. Die Daten von Cato NGFW, SWG, IPS, NGAM, DNS Security, CASB, DLP und RBI werden im Cato Data Lake gespeichert und dienen als hochwertiger Input für Cato XDR. Da die Daten nativer Sensoren an der Quelle nicht reduziert werden, ist die Wahrscheinlichkeit, dass die AI/ML-Algorithmen von Cato XDR kritische Signale übersehen, deutlich geringer als bei AI/ML, die Daten aus externen Quellen verarbeiten. SOC-Teams profitieren von einer beispiellosen Genauigkeit bei der Untersuchung von Vorfällen und einer großen Datenfülle.
Cato XDR wird durch mehr als 250 Threat Intelligence-Quellen ergänzt und liefert über 5 Millionen Datensätze mit gültigen IoCs. Cato nutzt eine speziell entwickelte, Cloud-skalierte ML-Plattform, um Bedrohungsdaten-Feeds aus Hunderten von Quellen aufzunehmen, jeden darin enthaltenen IoC-Datensatz zu verarbeiten und zu untersuchen und eine genaue und aktuelle Blacklist und Whitelist zu verwalten – ohne menschliches Eingreifen.
Cato gibt Sicherheitsteams aktuelle Bedrohungsdaten an die Hand, damit sie effizient arbeiten können und die Zahl der Fehlalarme gegen Null tendiert.
Kunden nutzen Cato, um komplexe Legacy-Architekturen mit mehreren Sicherheits-Point-Solutions und kostspieligen Netzwerkdiensten zu eliminieren.
Die einzigartige SASE-Plattform von Cato bietet überall und für jeden einen sicheren und optimierten Anwendungszugang.
Cato Networks wurde im Gartner® Magic Quadrant™ for Single-Vendor SASE 2024 als Leader ausgezeichnet.
„Cato Networks ist das Aushängeschild für ZTE und SASE.“
Cato Networks als Wachstums- und Innovationsführer im Bereich SASE anerkannt
Cato SASE im GigaOm Radar-Bericht als „Leader“ eingestuft
Cato Networks als weltweiter SSE-Produktführer anerkannt
WAN-Transformation mit SD-WAN: Schaffung einer ausgereiften Grundlage für den SASE-Erfolg


„Wir haben einen Einbruchs- und Angriffssimulator auf Cato laufen lassen, die Infektionsraten und die laterale Bewegung sind einfach gesunken, während die Erkennungsraten gestiegen sind. Dies waren Schlüsselfaktoren für das Vertrauen in die Sicherheit von Cato.“
Die Lösung, auf die IT-Teams gewartet haben
Lassen Sie sich überraschen!