Cato Transforms SD-WAN with Identity-Aware Routing
Routing and prioritizing traffic based on identity simplifies IT operations and enables end-to-end, business-process optimization
TEL AVIV, Israel, July 18, 2018 – Cato Networks, provider of Cato Cloud, the world’s first secure, global SD-WAN as a service, introduced the first identity-aware routing engine for SD-WAN. Identity awareness abstracts policy creation from the network and application architecture, enabling business-centric routing policies based on user identity and group affiliation. Identity awareness headlines a series of SD-WAN enhancements Cato is introducing today for Cato Cloud.
“We founded Cato on the premise that IT needed a new kind of carrier, one where simplicity isn’t just a mission statement but part of the company’s DNA,” says Shlomo Kramer, co-founder and CEO of Cato Networks. “Identity awareness adds business context to our end-to-end, converged and secure MPLS alternative, making it easier and simpler for IT to align with today’s dynamic business requirements and deliver an optimal user experience, everywhere.”
Identity Awareness Transforms SD-WAN Agility, Visibility, and Usability
Enterprises have long sought to make their networks easier — easier to configure, easier to deploy and easier to manage. Essential to that goal has been abstracting network policy definition to better mirror business context.
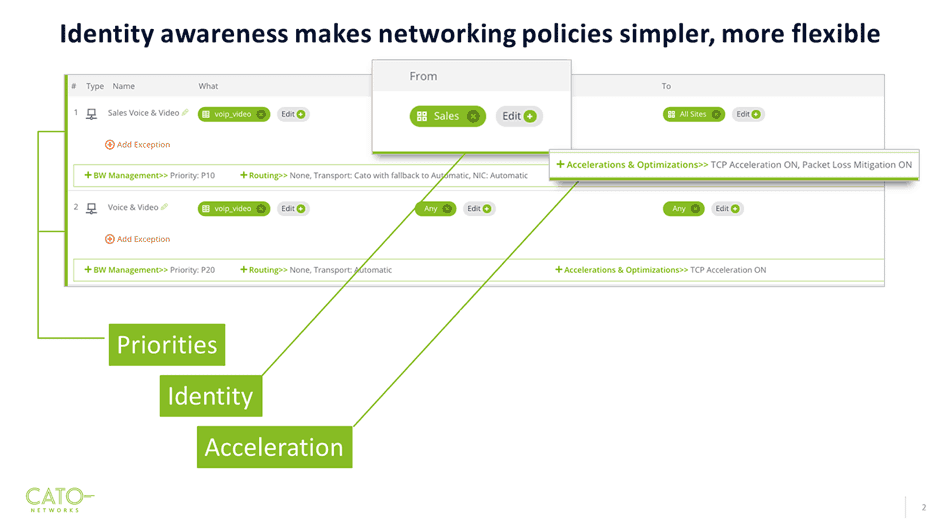
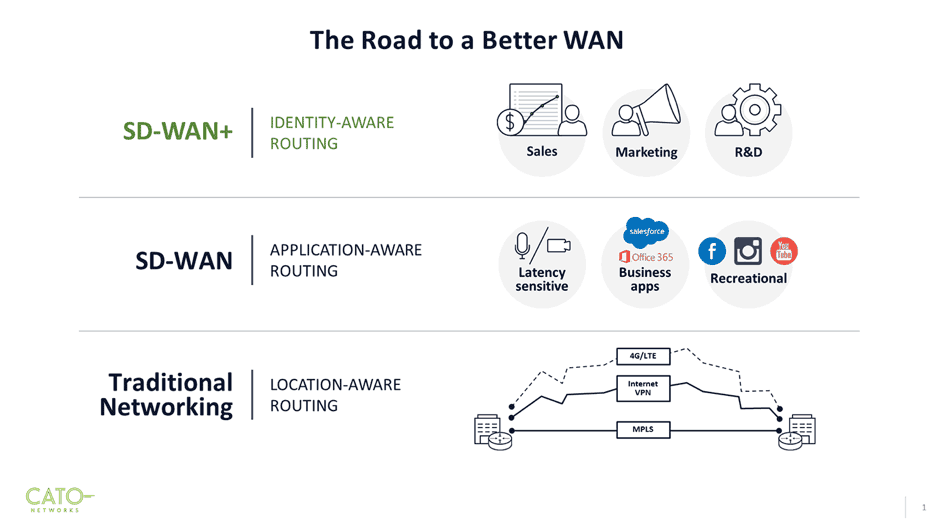
Routing policies across legacy networks were machine-aware, requiring IP addressing information that bore little resemblance to the business. SD-WANs popularized application-aware routing policies, bringing us closer to reflecting business context in our networks. Identity-aware routing completes this evolution by utilizing organizational entities. With identity awareness, networking and security policies can direct traffic or restrict resource access based on team, department, and individual users.
Cato implements identity-aware routing seamlessly without changing the network infrastructure or the way users work. Cato dynamically correlates Microsoft Active Directory (AD) data, across distributed AD repositories, and real-time AD login events to associate a unique identity with every packet flow. Organizational context, such as groups and business units, is derived from the AD hierarchy.
Adding identity attributes to networking policies allows Cato to deliver:
- Business process QoS where prioritization is based not just on application type but the specific business process. Business-critical voice calls, such as from executive or sales, can be prioritized over other calls; file transfers, normally given low priority, can be prioritized when involving business-critical processes, such as an engineering team transferring design files for an impending product release.
- Highest level of policy abstraction where route policy definition can use familiar groups, such as departments, teams, and usernames. Identity naturally extends network policies to the user regardless of the particular devices being used or the location — whether in the office or on the road. This simplifies network management as policies are easier to define, and fewer policies need be instantiated and maintained.
- Business-centric network visibility allows detailed insight into the activity for all business entities — sites, groups, hosts, office users and mobile users. IT can quickly see how business entities use the network to help with network planning and scaling.
Industry Leading SD-WAN Features
Along with identity awareness, Cato is introducing today numerous enhancements and improvements to Cato Cloud’s SD-WAN capabilities. New or enhanced features include:
- Multi-segment, policy-based routing dynamically selects the optimum path at each segment — the first mile, middle mile, and last mile. Segment-specific protocol acceleration technologies maximize global throughput. Using the robust DPI engine underlying its converged security solution, Cato is able to detect and classify hundreds of SaaS and datacenter applications regardless of port, protocol, or evasive technique and without SSL inspection. Applications are routed based on real-time link quality or preferred transport.
- Real-time network analytics expands Cato robust reporting for advanced troubleshooting. IT managers can view throughput, jitter, packet loss, latency, packet discarded, and dropped indicators with graphs for both upstream and downstream traffic as well as the top hosts and applications for real-time and historical traffic.
- Affordable and simple high availability (HA) deployment has been expanded to include more HA options. Cato Socket, Cato’s SD-WAN appliance, supports a broader mix of active/active and active/passive failover configurations for MPLS and Internet connections. Cato’s Affordable HA carries no additional recurring charge and deployment is simple with zero-touch provisioning and needing just a private or public IP address.
- Intelligent last-mile resilience has been improved to include flow-by-flow packet duplication and fast packet recovery as part of Cato’s Multi-Segment Optimization. Last-mile congestion, a significant cause of packet loss, is also mitigated through advanced QoS support for upstream/downstream bandwidth.
- Cloud and WAN traffic optimization using Cato’s Multi-Segment Optimization reduces latency by routing traffic along the optimum path to the destination site (WAN traffic) or to the entrance of the cloud service (cloud traffic). A variety of TCP enhancements increase throughput when accessing cloud and WAN resources.
Cato Cloud: The Power of Converging SD-WAN and Security into the Cloud
Cato revolutionized the industry with the introduction of the first secure, cloud-based SD-WAN service. Since then Cato expanded the comprehensive set of converged security services in Cato Cloud with the Cato Threat Hunting System (CTHS), IPS, and more. Identity awareness and the rest of the enhancements being introduced today build on that momentum. All features are currently available.
To see Cato’s secure SD-WAN capabilities in action and learn more about identity-aware routing, click here to join our upcoming online demonstration of Cato Cloud.




