Cato Malware Prevention delivers a multi-layered security approach to protect organizations against all types of malware. By leveraging Cato Next-Generation Anti-Malware (NGAM) to block both known and unknown threats, and Cato Sandbox to analyze malware behavior for deep forensic insights, Cato delivers a comprehensive defense against sophisticated attacks. This powerful combination enables security teams to contain threats, minimize impact, and investigate with precision.
Cato’s NGAM detects zero-day and polymorphic malware in real-time. In partnership with SentinelOne, a machine learning algorithm maps connections between thousands of data points to return a verdict of benign, suspicious, or malicious.
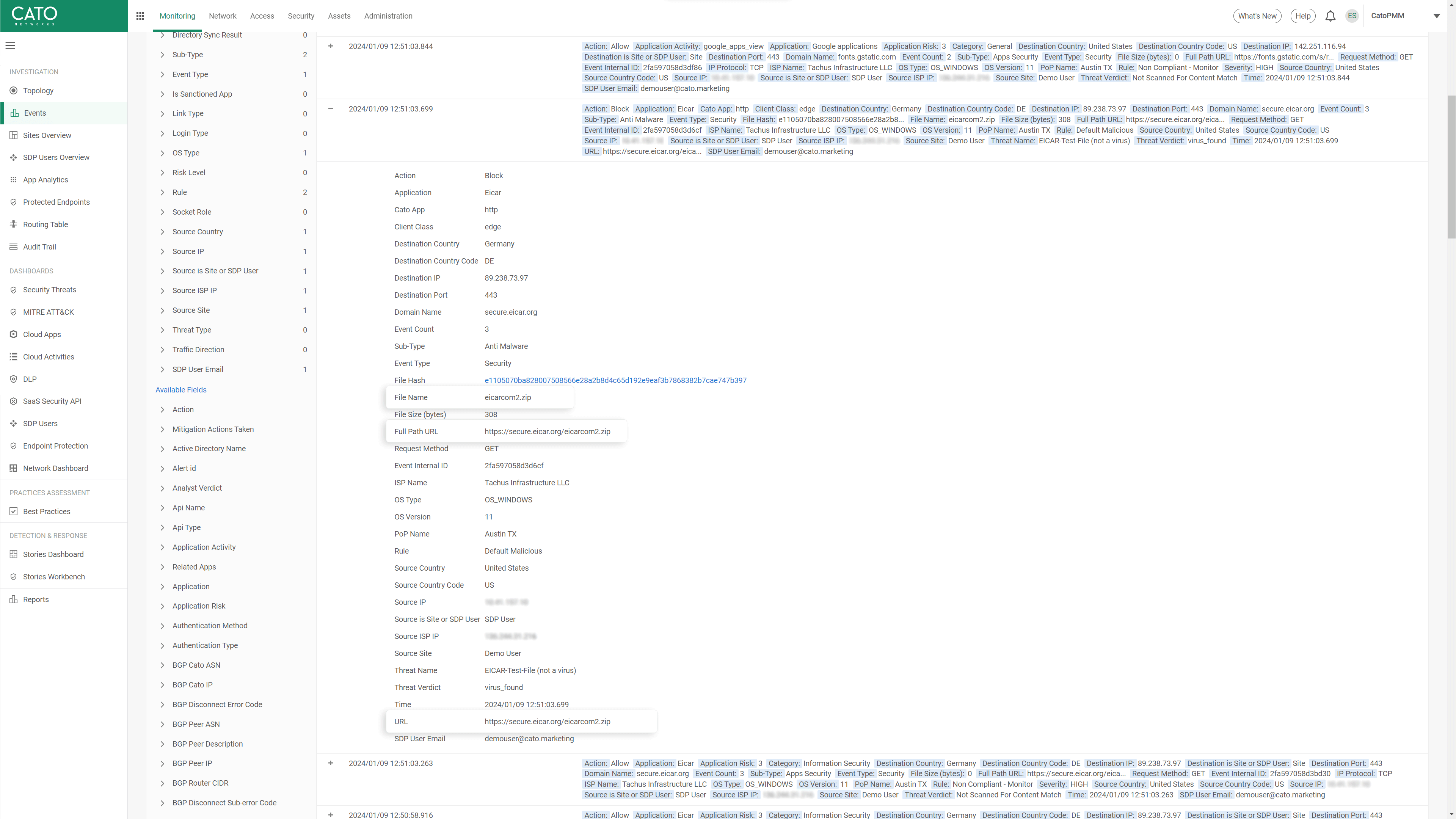
Policies are simple to manage, and administrators can define allow, and block actions based on context such as Internet or WAN, source (user, IP address, Host), application, and more. Aligning with the enterprise’s needs, exceptions can be specific or global to the entire account. With Cato, organizations can adopt a stricter security approach while maintaining the agility to meet business needs with policy changes taking effect globally in just minutes.

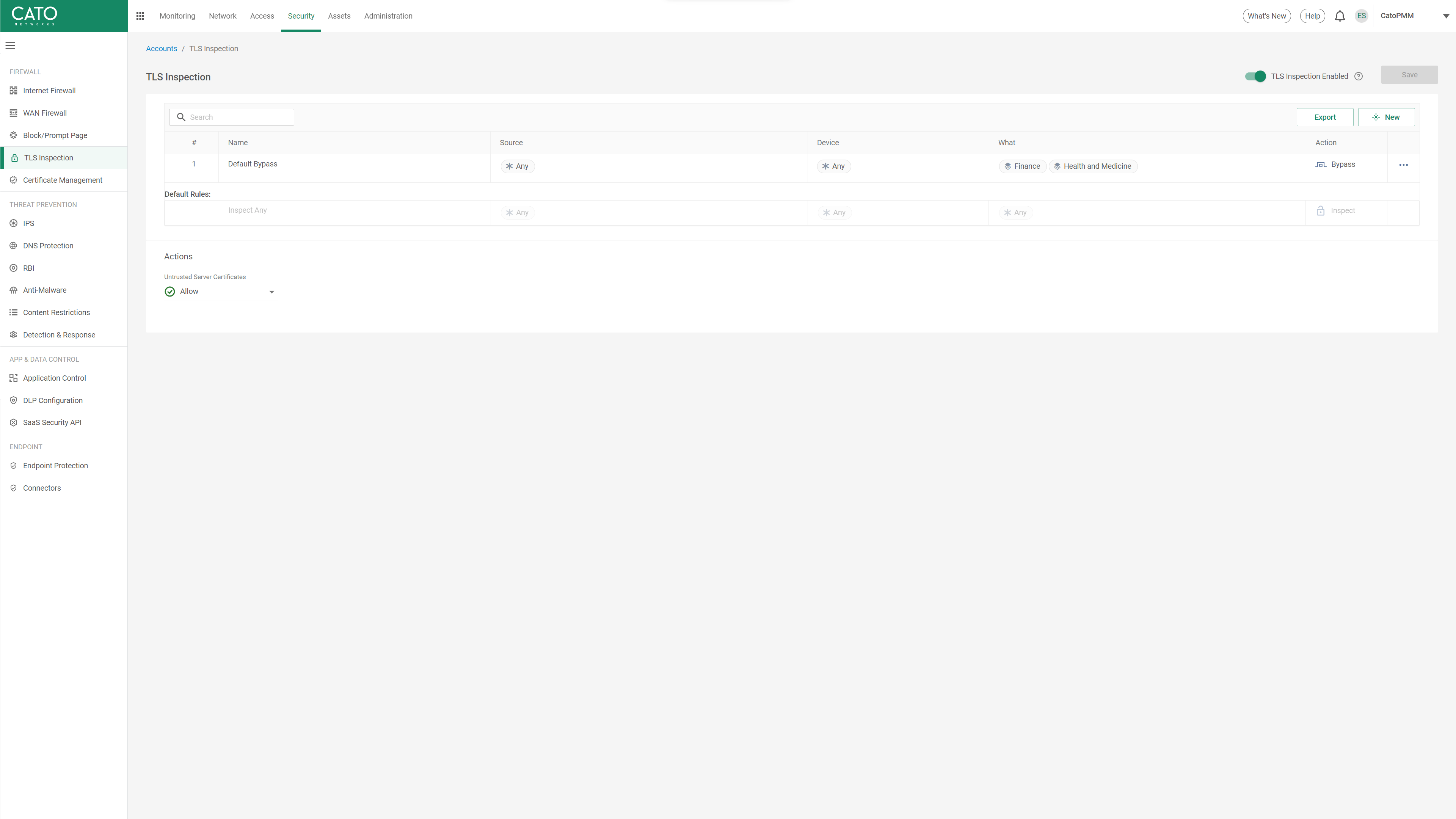
More than 90% of web traffic is encrypted and enterprises that aren’t inspecting this traffic are blind to threats hiding in it. Cato’s SASE cloud performs TLS inspection at scale, eliminating the need to size and scale legacy appliances. Inspection policies can be granularly applied, allowing organizations to inspect as much traffic as desired. Enabling TLS inspection has no impact on performance and allows Cato’s NGAM complete visibility to detect and block the most malware possible.
Cato’s NGAM supports multiple file types and can scan multiple levels within nested archive files. Archive files are held until the engine confirms that the entire contents of the files are free from malware. Encrypted and password-protected files cannot be scanned but can be blocked by policy rules. These features help secure organizations by addressing one of the techniques used by threat actors to bypass security engines.
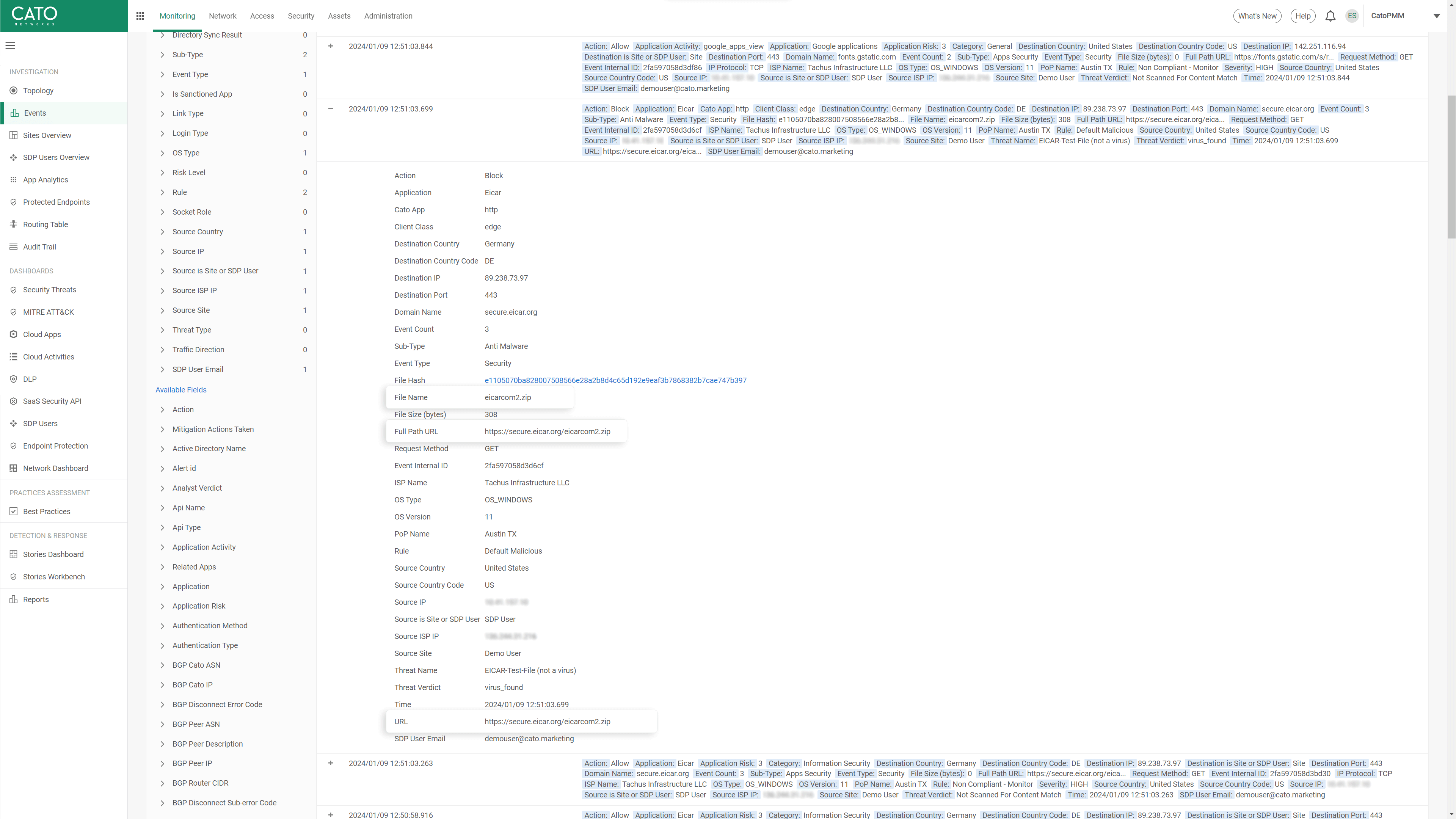
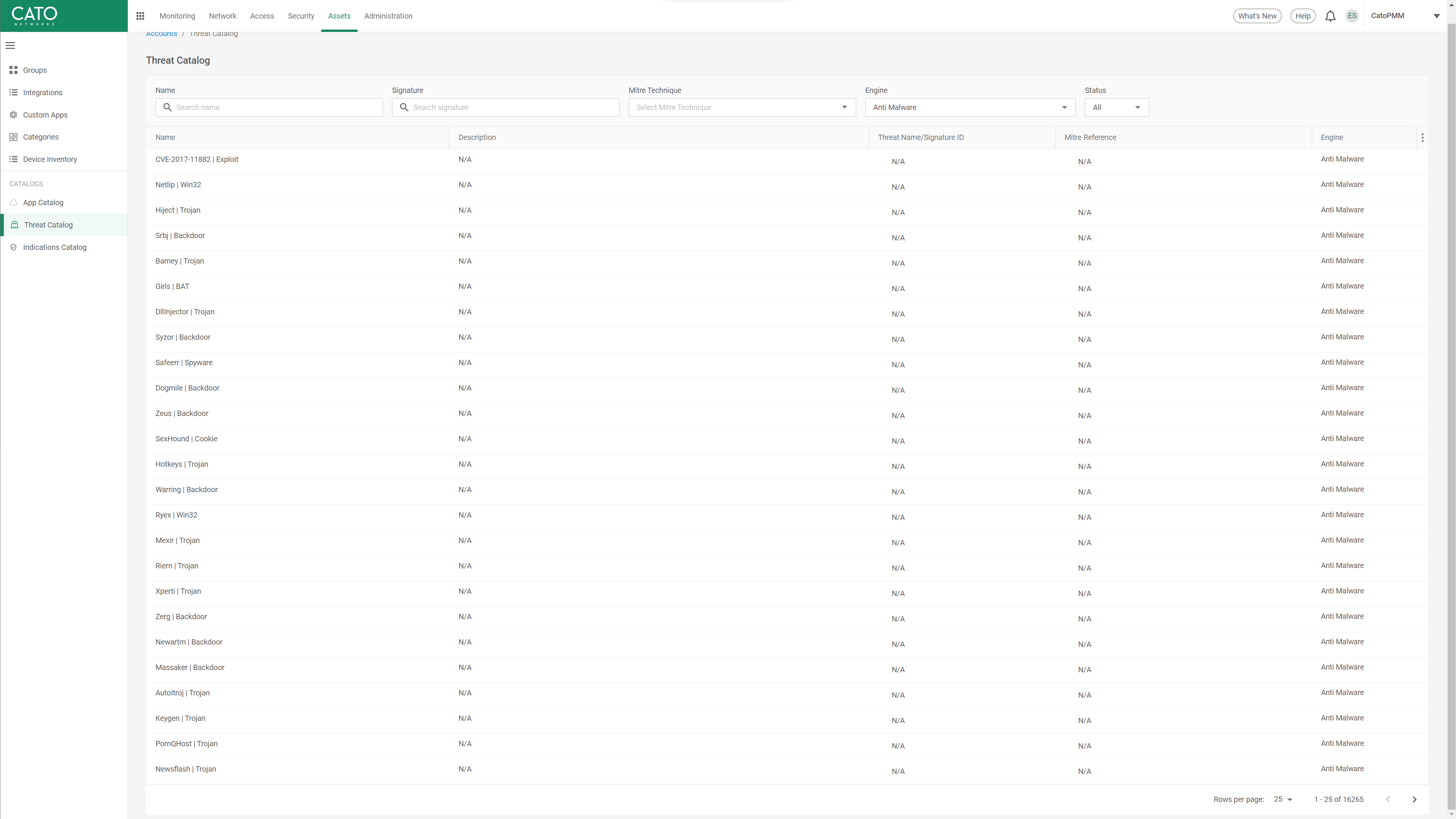
Cato scans every file at wire speed, continuously evaluating the files against a signature and heuristics database that is continuously updated. Organizations benefit from the most up-to-date protection without the manual labor of managing the infrastructure and operational complexities of legacy solutions. Customers can replace the anti-malware engine of traditional firewalls and UTMs, ensuring that all files are evaluated against a comprehensive signature database without the constraints of fixed appliance resources.
Cato Sandbox automatically sends any suspicious or malicious files for sandbox analysis, executing it in a controlled, isolated environment. This generates rich, detailed forensic reports, including Indicators of Compromise (IOCs) and attack behavior insights. Security teams can download these reports directly from the Cato Management Application (CMA) to accelerate incident response and enhance forensic investigations, improving their ability to detect, analyze, and mitigate advanced threats.
Customers use Cato to eliminate complex legacy architectures comprised of multiple security point solutions and costly network services. Cato’s unique SASE platform consistently and autonomously delivers secure and optimized application access everywhere and to everyone.
Cato Networks named a Leader in the 2025 Gartner® Magic Quadrant™ for SASE Platforms. Again.
Cato Networks Named a Leader and an Outperformer in the GigaOm 2025 SASE Radar
Cato Networks recognized as a Growth and Innovation Leader in SASE
Cato Networks Recognized as Global SSE Product Leader
WAN Transformation with SD-WAN: Establishing a Mature Foundation for SASE Success


“We ran a breach-and-attack simulator on Cato, Infection rates and lateral movement just dropped while detection rates soared. These were key factors in trusting Cato security.”
The Solution that IT teams have been waiting for.
Prepare to be amazed!