Protect Your Systems Now from the Critical Windows SMBv3 RCE Vulnerability
Table of Contents
|
Listen to post:
Getting your Trinity Audio player ready...
|
At the beginning of the month, Microsoft released an advisory and security patch for a serious Windows Server Message Block (SMB) vulnerability called the Windows SMBv3 Client/Server Remote Code Execution Vulnerability (AKA Windows SMBv3 RCE or CVE-2020-0796). The Server Message Block (SMB) protocol is essential for Windows network file and print sharing. Left unpatched, this new SMB vulnerability has the potential to create a path for dangerous malware infection, which is why Microsoft has labeled it Critical.
Windows SMBv3 RCE isn’t the first vulnerability in SMB. In May 2017, the infamous Wannacry ransomware attack disabled more than 200,000 Windows systems in 150 countries using a similar (but not the same) SMB vulnerability. One of the hardest hit victims, the British National Health Service (NHS), had to cancel more than 19,000 appointments and delay numerous surgeries. Microsoft had already issued a security patch but Wannacry was able to infect thousands of unpatched systems anyway.
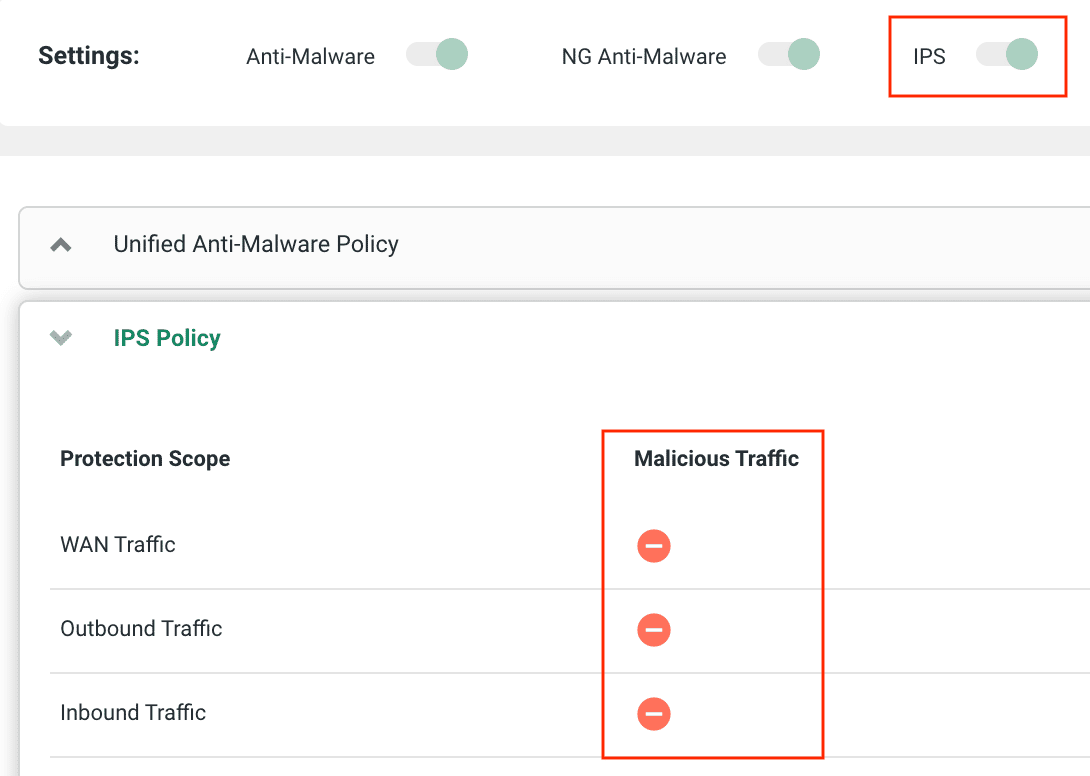
Cato urges every organization to apply the Microsoft patch (CVE-2020-0796) now across all relevant Windows systems, which we’ll discuss here. Cato also updated its IPS to block any exploit using this new vulnerability. As long as customers have their Cato IPS to Block mode, their systems will be protected. There’s no need to run IPS updates as you would with a security appliance or on-premises software. Thanks to Cato’s cloud-native architecture, the update is already deployed for all Cato customers.
How CVE-2020-0796 Works
Unlike Wannacry that exploited vulnerabilities in older versions of Windows, this new vulnerability lies in the latest version of Windows 10. Specifically, vulnerability is found in the decompression routines of SMB version 3.1.1 (SMBv3) found in Windows 10, version 1903 and onwards for both 32- and 64-bit systems, the and recent versions of Windows Server Core used in applications such as Microsoft Datacenter Server.
An attacker could exploit this vulnerability to execute malicious code on both the SMB server and client side. They could attack Windows SMB server directly or induce an SMB client user to connect to an infected SMB server and infect the client.
An attack using this vulnerability could happen in a few ways. A hacker could attack systems from outside the enterprise network directly if a system’s SMB port has been left open to the Internet. By default, Windows Firewall blocks external connections to the SMB port, however. A more common scenario would involve a user inadvertently installing malware on their system by clicking on a malicious link in a spam email. The malware would then exploit the new SMBv3 vulnerability to spread across other Windows systems on the network.
How to Protect Yourself
The best way to protect your organization from malware exploiting this critical vulnerability is to make sure all Windows 10 systems and any remote, contractor or other systems accessing the enterprise network have applied the Microsoft security patch. If you need to delay patching for any reason or can’t be sure every system is patched, there are other measures IT can take.
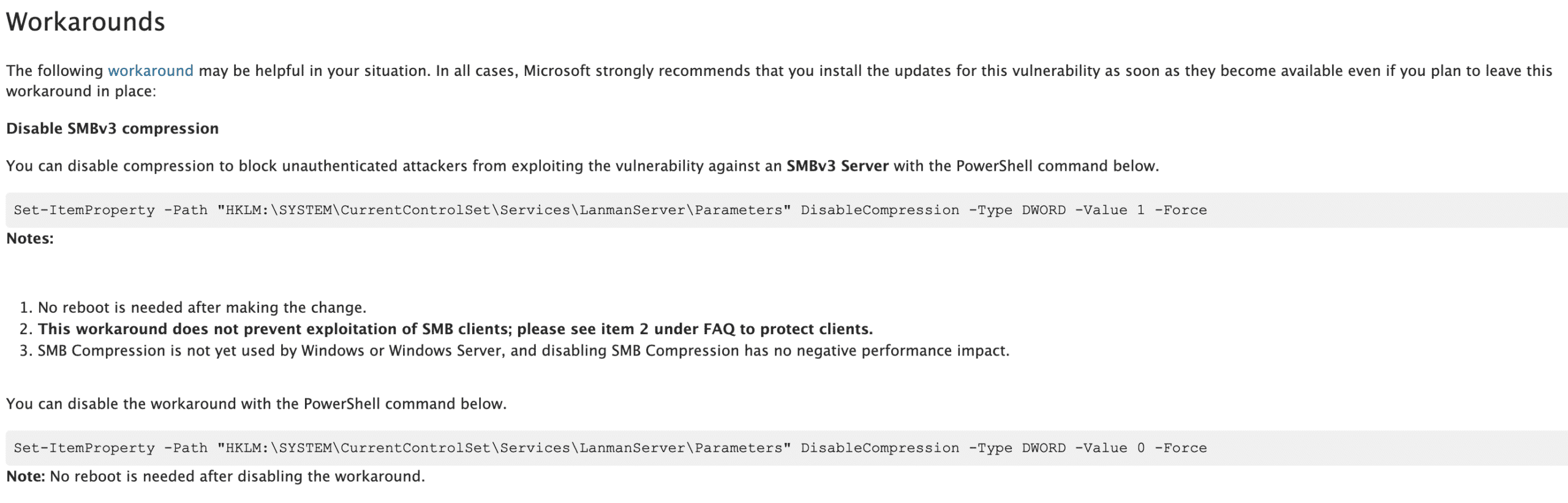
The easiest is to simply disable SMBv3 compression on all systems via registry key changes, which wouldn’t have any negative impact as SMBv3 compression isn’t used yet. Microsoft describes how to do this in its advisory (see figure 1 below) and it could be accomplished over hundreds of systems via Group Policy. This would solve the problem for SMB servers but not SMB clients.
You could also block inbound TCP Port 445 traffic, but that port may be used for other Windows components and would only protect you from attacks from the outside, not attacks spreading internally.
As for internal network flows, it’s always prudent to segment your network to restrict unnecessary traffic in order to prevent attacks like these from spreading laterally. There is no reason, for example, that a client system from your finance department should have network access to systems in human resources via the Windows SMB protocol.
How Cato Protects You
There are two ways Cato protects its customers. Thanks to its cloud-native architecture, Cato continually maintains and updates its extensive security stack across every Cato PoP, protecting all communications across the Cato network, whether a branch office or mobile user connects over the Cato backbone to the datacenter or with another branch office or mobile user. Cato’s cloud-native architecture applied all security updates, including the IPS signature for this newly announced vulnerability, shortly after Microsoft released its advisory. Enterprise IT doesn’t have to do anything, such as updating a security appliance. All exploits that take advantage of this vulnerability are already blocked as long as your IT department has set the Cato IPS for Block mode on all traffic scopes (WAN, Inbound and Outbound).
Even without this IPS update, however, Cato’s security stack uses other means to detect and alert on any traffic anomalies that could indicate an attack, even a zero-day attack. For example, if a host normally communicates using SMB with one or two other hosts and then suddenly communicates with hundreds of hosts, Cato’s IPS will detect those anomalous flows. It can alert IT or even cut off the flows depending on configuration. This may not block an attack completely, but it will allow IT to limit the damage and apply necessary measures to prevent the attack in the future.
We’ll continue to keep you abreast of any critical Windows vulnerabilities in the future. Cato customers can rest assured that Cato will take all possible measures to protect their networks against new vulnerabilities, immediately.