The Value of Security Simplicity
|
Listen to post:
Getting your Trinity Audio player ready...
|
A Complex Landscape
As time passes, technology and human innovation have advanced rapidly. This is not only in terms of available connectivity, bandwidth, and processing power but also in terms of the networking and security landscape as well. For every technological advancement in consumer and business productivity, IT systems, operations and security must also try and keep pace.
We must consider not only the speed and capacity at which these tools must operate, but also the emergence of entirely new technical domains. The industry has moved away from castle and moat designs and replaced them with cloud platforms for a variety of services, effectively moving from endpoint security to network security and finally to cloud security and cloud-delivered network security. But with each new need and technical area, a multitude of vendors and products emerge only adding to the complexity.
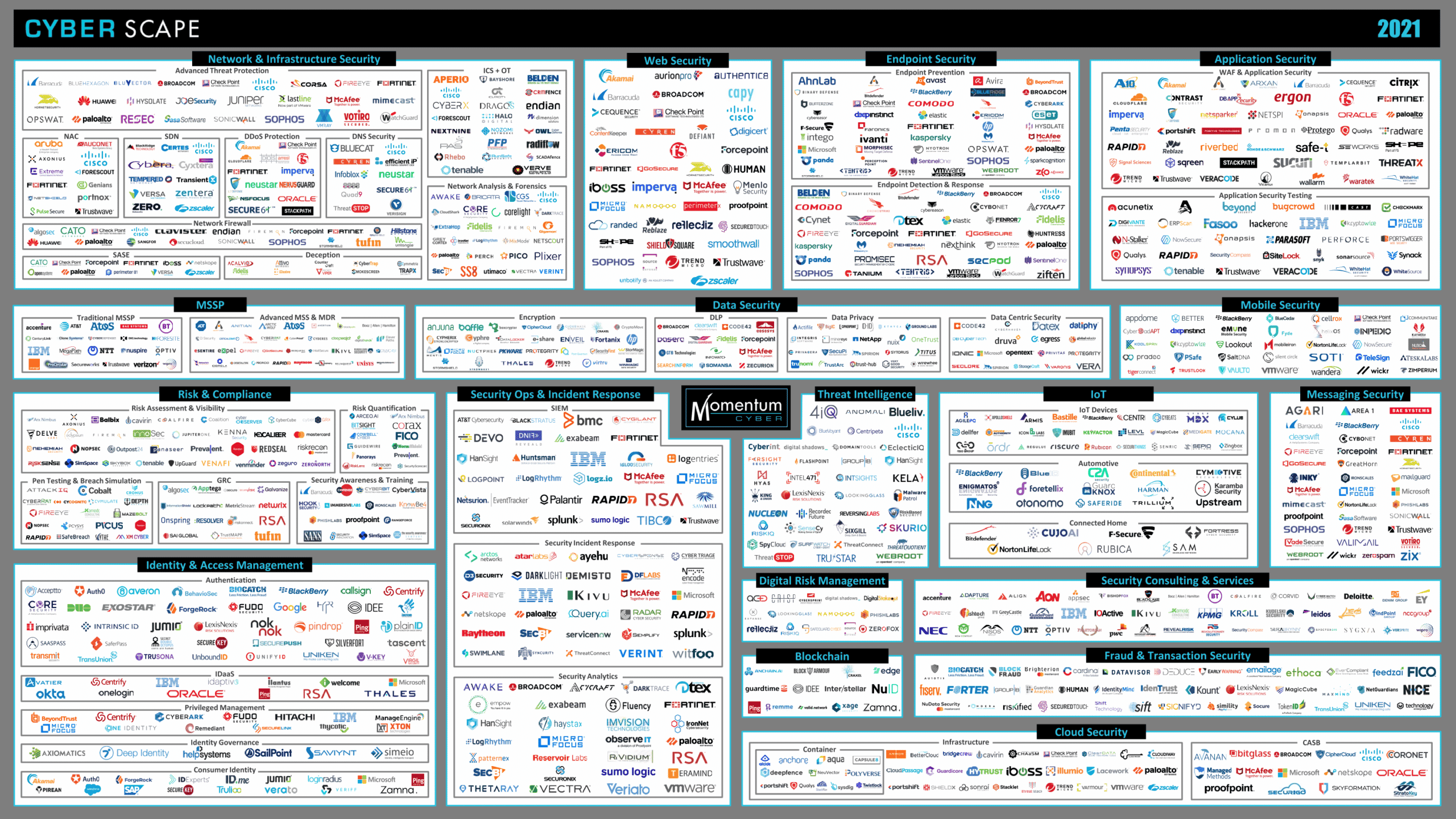
IT and security leaders must consider multiple security product categories such as network & infrastructure, web, endpoint, application, data, mobile, risk & compliance, operations & incident response, threat intelligence, IoT, IAM, email/messaging, risk management, and more. Adding to the challenge, for each category there are multiple vendors with different product sets, architectures and capabilities. It can be time consuming and challenging to prioritize security investments while selecting the ideal vendor for your business. While each product that you purchase and implement is intended to strengthen your security posture and reduce risk, these products may also be increasing the complexity of your environment.
Ransomware is on the Rise – Cato’s Security as a Service can help | Get the eBookComplexity Erodes Security
Many have considered it a best practice to purchase products based on the perception in the market as “best of breed.” This approach seems logical but can be detrimental as getting these products to work together can be difficult or impossible. Even products from the same vendor can be lacking in integration, especially if the product was the result of an acquisition. Furthermore, even with out-of-the-box integrations, getting everything to work as desired can still be very time-consuming.
You may have already learned through experience that integration is not convergence. If you are still questioning the difference between the two, here are two examples. A converged solution will have a single management application for all functions of the platform. Separate consoles or a pseudo-unified console that requires downloading, installing, and managing plugins are not converged. For cloud-delivered offerings, a converged solution will offer all capabilities at all PoPs. A vendor that uses some PoPs for capabilities like DLP and remote access and other PoPs for things like NGFW and SWG is not converged. Non-converged solutions can drastically increase management touch, increasing administrative overhead and cost while eroding security value.
How does this happen? For every new product and management application, the opportunity for misconfiguration increases as does the number of policies. Misconfigurations can easily lead to high profile security incidents, while multiple sets of separate policies can lead to gaps that are difficult to identify. A converged security platform provides holistic visibility into your organization’s policies and even makes it easier when you need to conduct compliance audits. Of course, the market has responded to this, and you can spend more money on third-party integration and management tools, or developers that can build custom integrations for you. However, CISO’s live in the real world and do not have unlimited budget, nor do they typically want to own a software development life cycle for home-built integrations. Just remember, more vendors and more products can easily mean more problems.
Is Your Security Stack Weighing You Down?
In addition to hurting your organization’s budget and security posture, point-security products also reduce your ability to be agile and innovate. You may need to manage an update schedule for each of your devices and products. While most vendors have automatic update options, the best practice is to test updates before putting them into production and monitor impacts after production. For example, a content update on a Palo Alto Networks PA-220 Firewall is estimated to take up to 10 minutes.* If you have 1,000 PA-220s, that is more than 166 hours of update time, not including downloading, testing, and verifying. Updates to the device’s firmware or operating system will likely take longer and can lead to outages or device failures. All this time spent on maintaining what you already own can slow other projects in your organization.
“[Content update] installation can take up to 10 minutes on a PA-220 firewall” * Source
Beyond your organization’s ability to innovate, you should also consider the impacts on yourself or your team. Most security products require specialized technical expertise. This can make hiring challenging, especially if you need someone who can manage multiple aspects of your deployment. This means that hiring cycles will take longer, work/life balance may be compromised, and new hire ramping time is increased. Furthermore, complex deployments can make it difficult for skilled individuals to be promoted or take vacation time.
Your security stack represents a significant investment, but is it serving all users, locations, and applications? The costs of deploying and managing your own security architecture will often lead to compromises. You may have a few datacenters and probably backhaul traffic to them to secure. But often enough due to performance and other requirements, you may also be excluding specific locations, users, or applications from some or all security functions. This creates inconsistency in your security posture and user experience and will hurt your organization.
SASE Is the Way
You probably have heard of the Secure Access Service Edge or SASE, a term that Gartner coined in 2019. SASE is the way forward for most modern organizations and represents the convergence of networking and security capabilities delivered from the cloud. This allows organizations to remain agile and flexible, reducing complexity, while securing and enabling their users. The SASE market is relatively new, but there are already multiple vendors who want your business.
When looking at SASE, don’t forget about simplicity, many vendors don’t have converged solutions and the complexity of legacy technology still lurks in their products. Management time and policy sets should be reduced, while deployments and new feature adoption should be seamless. Updates are the vendor’s responsibility, keeping you more secure and giving you time for other projects. You may have heard the acronym K.I.S.S. before, but I’ve changed it a bit for a SASE world: Keep It Simple & Secure.
“When we learned about the Cato solution, we liked the idea of simple and centralized management. We wouldn’t have to worry about the time-consuming process of patch management of on-premise firewalls,” – Alf Dela Cruz, Head of IT Infrastructure and Cyber Security at Standard Insurance










