Manufacturing
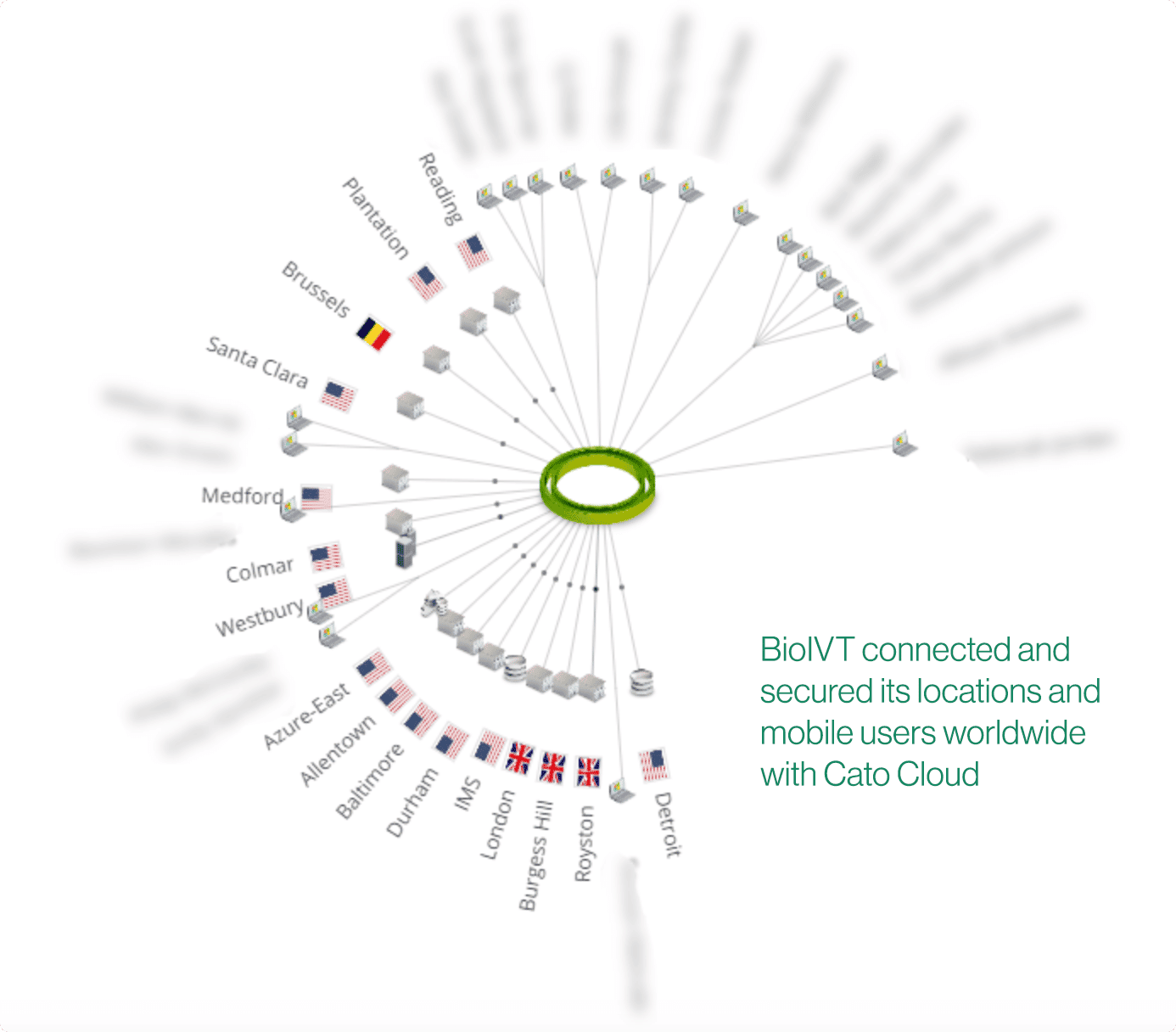
BioIVT Connects and Secures Global Network with Cato Cloud and the Cato Managed Threat Detection and Response (MDR) Service
The Challenges Facing BioIVT: Adding New Locations, SaaS Application Performance and a Security Blueprint
Like many fast-growing companies, BioIVT, a provider of biological products to life sciences and pharmaceutical companies, depends on its network being agile and secure. Mergers and acquisitions (M&A) are part of the company’s DNA, but fast integration of new company networks is challenging when running appliances. Protecting the network from Internet-borne threats was also important.
The BioIVT network was a 14-site, Internet VPN. It was an “old Cisco network,” says Andrew Thomson, director of IT systems and services, with each site running Cisco routers, interconnected by VPN tunnels.
“With every new site, we needed to build tunnels to every other location. Configuring those tunnels took time. We budgeted 90 days or so to get new locations up and running,” he says
Application performance was also a problem. The company’s New York-based ERP system and Office 365 instance were accessed by the other locations. Accessing both applications meant traversing the Internet, which became a problem particularly for users working from home or overseas.
And then there was the security issue. “We knew we’d have to look at our security strategy. Penetration testing with our Cisco routers was going to be a step. But updating our security architecture was going to require running around to different vendors, piecing together a solution, and going through all of the deployment and management pains,” he says.
Agility and Speed: Key Requirements for BioIVT’s Networking Solution
Thomson began looking around at various networking solutions for connecting his locations. Agility and speed of deployment were critical if he was to integrate new offices faster. “SD-WAN made the most sense from an ease of use perspective,” he says.
He considered an SD-WAN appliance and a telco-managed SD-WAN service. SD-WAN appliances meant he had to operate over the unpredictable Internet and both involved deploying even more infrastructure. Neither would have addressed his security issues.
Then he ran into Cato. “Cato did a lot of what we were after — which is saying a lot,” he says, “Customer service and support was fantastic. Everyone was great to work with and rollout was very easy.”
Instead of taking 90 days to configure tunnels and integrate each location, Thomson now is able to bring up new locations in as little as 30 days. “With Cato we just ship a configured device to the site. Personnel plug it in and we’re ready to go. There are no subnetting issues; no building individual tunnels. The Cato Socket connects to the Cato network itself. The whole operation is a lot less administrative and involves a lot less technique than the Cisco series routers.”
And with his locations connecting across the Cato Cloud Network not the public Internet core, performance has improved. Sage ERP has become more responsive; Active Directory synching works more effectively. As for Office 365, “It’s been fantastic,” he says, “really good speed benefit.”
Thomson has been able to deploy voice and Unified Communications as a Service (UCaaS) from 8×8 across his Cato instance. “The voice quality over Cato has been awesome,” he says.
BioIVT Protects Sites With Cato MDR
Today, BioIVT has all locations on Cato. But it’s not just networking provided by Cato that’s helped BioIVT; it’s also the security services. “When we found out that Cato not only delivered a global network but also offered built-in security services and now MDR, we were extremely excited. It was a huge help,” he says.
Thomson secures Internet connectivity and site-to-site connections with Cato firewall, protects mobile users running the Cato mobile client with Cato’s secure web gateway (SWG) capabilities, and uses Cato IPS for preventing network-based threats. More recently, he’s activated Cato Managed Threat Detection and Response (MDR) to hunt for threats on his network.
“When we found out that Cato not only delivered a global network but also offered built-in security services and now MDR, we were extremely excited. It was a huge help”
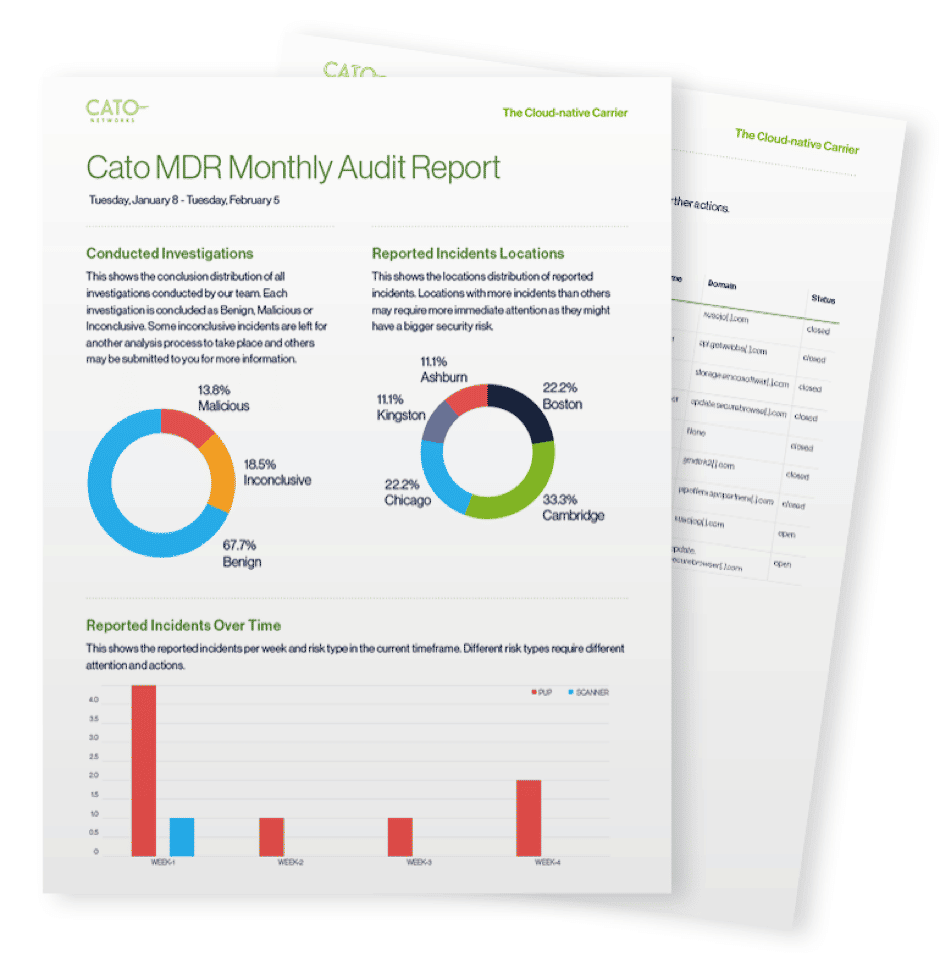
Cato MDR is a fully managed service that offloads the detection of compromised endpoints onto Cato’s security operations center (SOC) team. The service uses machine learning algorithms to look for anomalies across the billions of flows in Cato’s data warehouse and correlates them with threat intelligence sources and complex heuristics. This process produces a small number of suspicious events that Cato security researchers analyze, only alerting BioIVT on actual threats. BioIVT is relieved from handling the flood of false-positives that suck precious IT resources.
“Cato MDR has already discovered several pieces of malware missed by our antivirus system,” says Thomson, “We removed them more quickly because of Cato. Now I need to know why the antivirus system missed them.”
Remediation Without the Fuss
As part of Cato MDR, customers are notified immediately of verified live threats. Cato’s SOC advises on the risk’s threat level, recommended remediation, and follows up until the threat is eliminated “We’ve integrated Cato’s ticketing system with our own,” says Thomson, “so once the SOC discovers a threat the right IT resources are allocated.”
Cato also allows companies to automatically block C&C domains and IP addresses. Best of all? Cato MDR is built into BioIVT’s network. “Before Cato, we didn’t look at MDR. We just hadn’t gotten around to it because of the complexity. So having MDR built into the Cato platform has made all the difference in the world.”

About BioIVT
BioIVT is a provider of biological products to life sciences and pharmaceutical companies. The company has 14 locations — 10 in the US, 3 in the UK, and one in Belgium. Prior to Cato, BioIVT locations ran local firewalls interconnected by an Internet-based VPN. The company’s applications included ERP hosted at the New York site, Active Directory, and Office 365.



