Eliminating Shadow IT
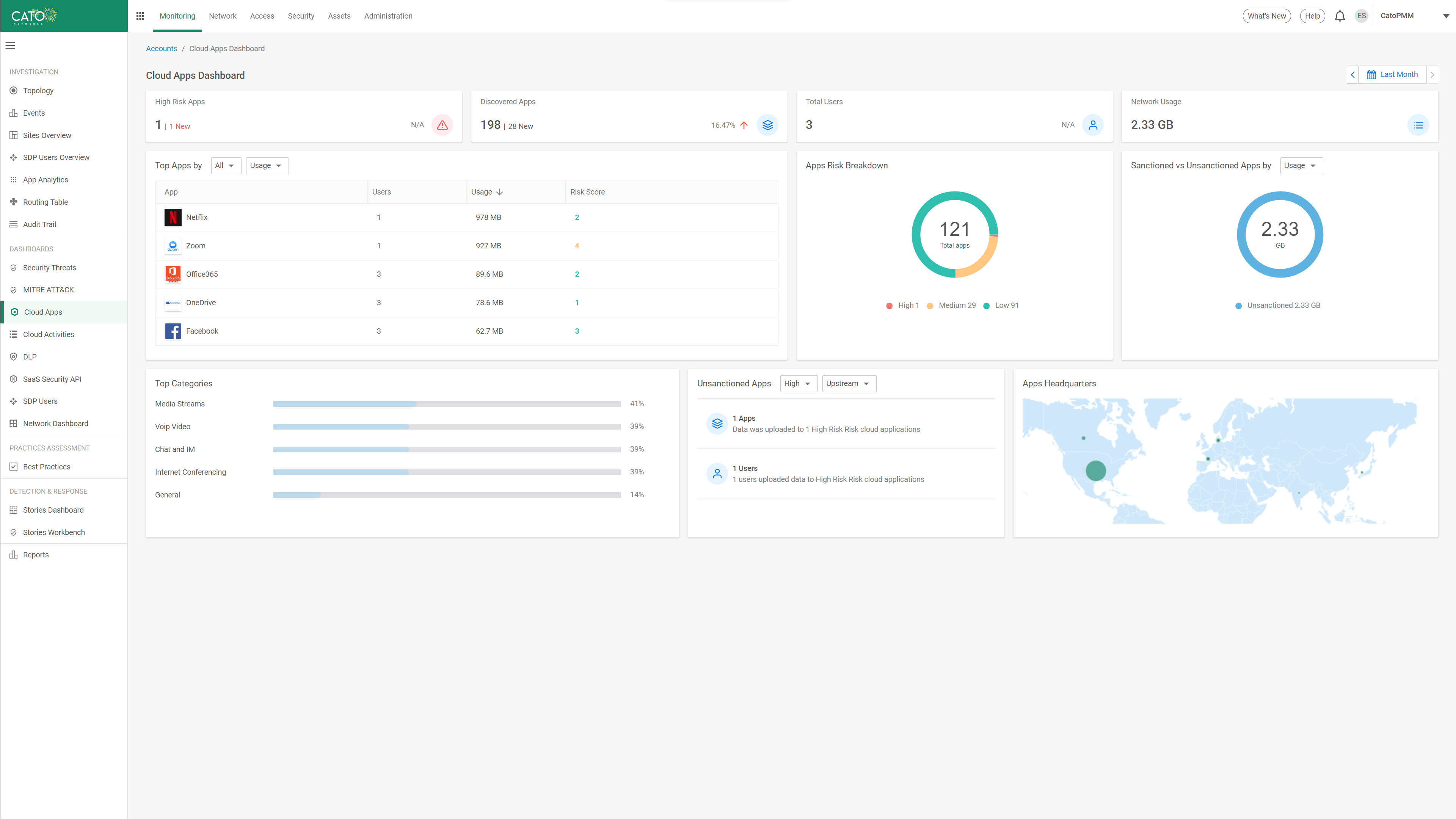
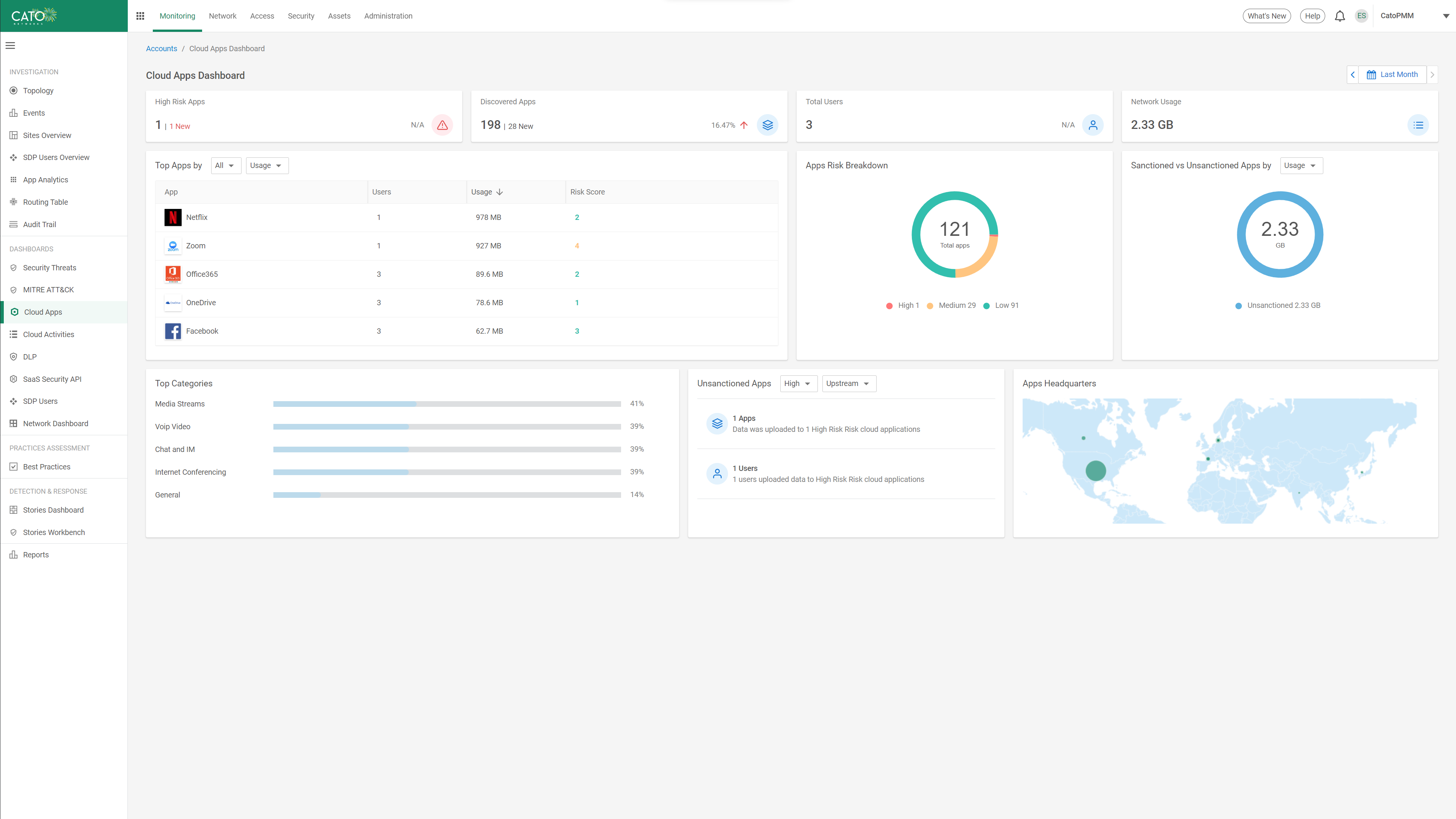
Full Cloud Application Visibility and Shadow IT Control
Admins responsible for controlling enterprise exposure to risks are often unable to manually validate each cloud application compliance. Using automated data collection and ML-based analysis, Cato CASB provides a calculated risk score for every cloud application. Presented in a Cloud App Catalog, each application profile is enriched with a description, compliance adherence, and security controls of the application. Admins can view all the information required to make informed decisions regarding application usage and define policies that limit risk and exposure. For example, preventing access to applications above a certain risk score, applications without MFA and SSO, apps that don’t comply with security standards, etc.
AI/ML-based Application Risk and Access Control
Admins responsible for controlling enterprise exposure to risks are often unable to manually validate each cloud application compliance. Using automated data collection and ML-based analysis, Cato CASB provides a calculated risk score for every cloud application. Presented in a Cloud App Catalog, each application profile is enriched with a description, compliance adherence, and security controls of the application. Admins can view all the information required to make informed decisions regarding application usage and define policies that limit risk and exposure. For example, preventing access to applications above a certain risk score, applications without MFA and SSO, apps that don’t comply with security standards, etc.
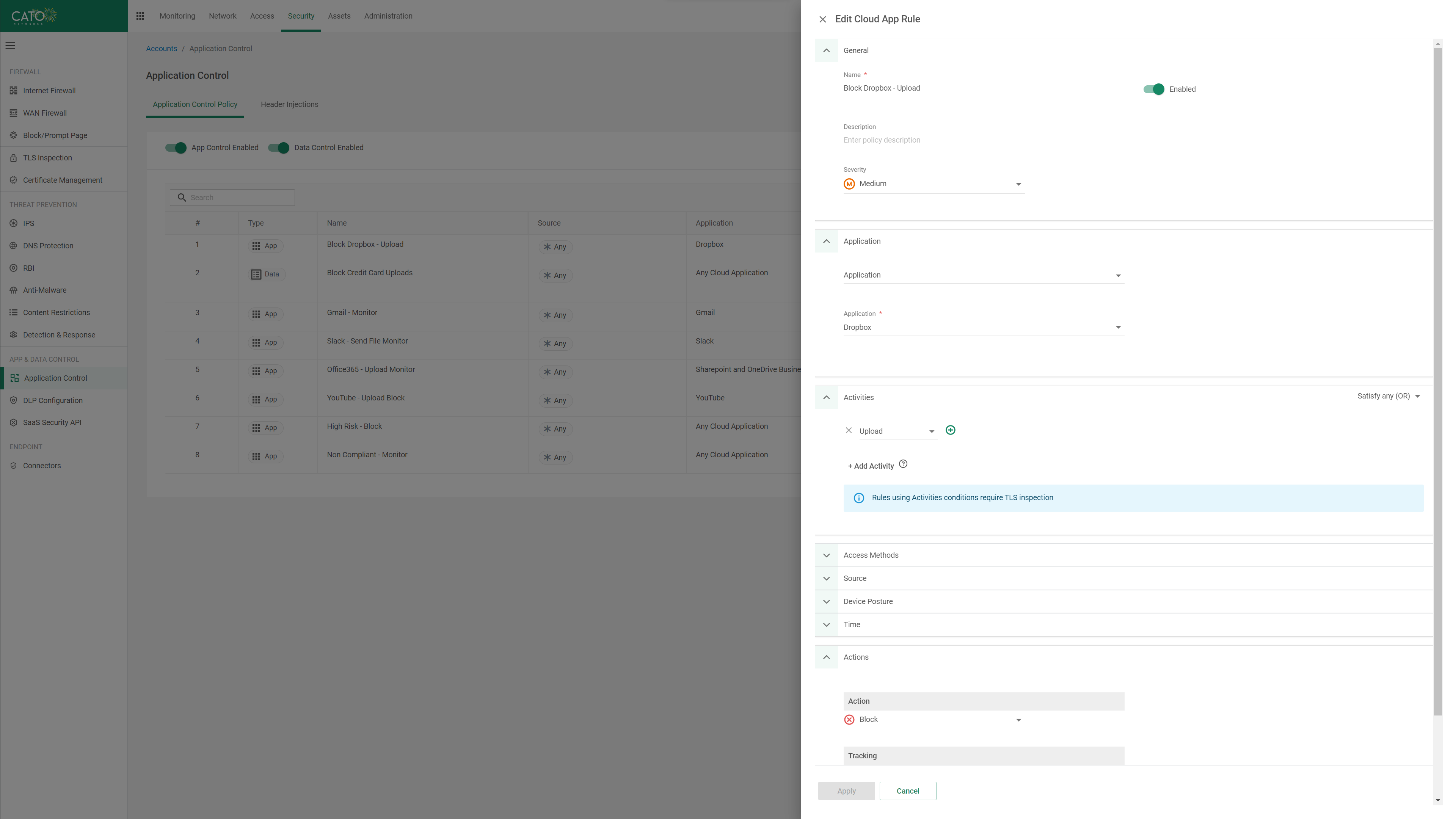
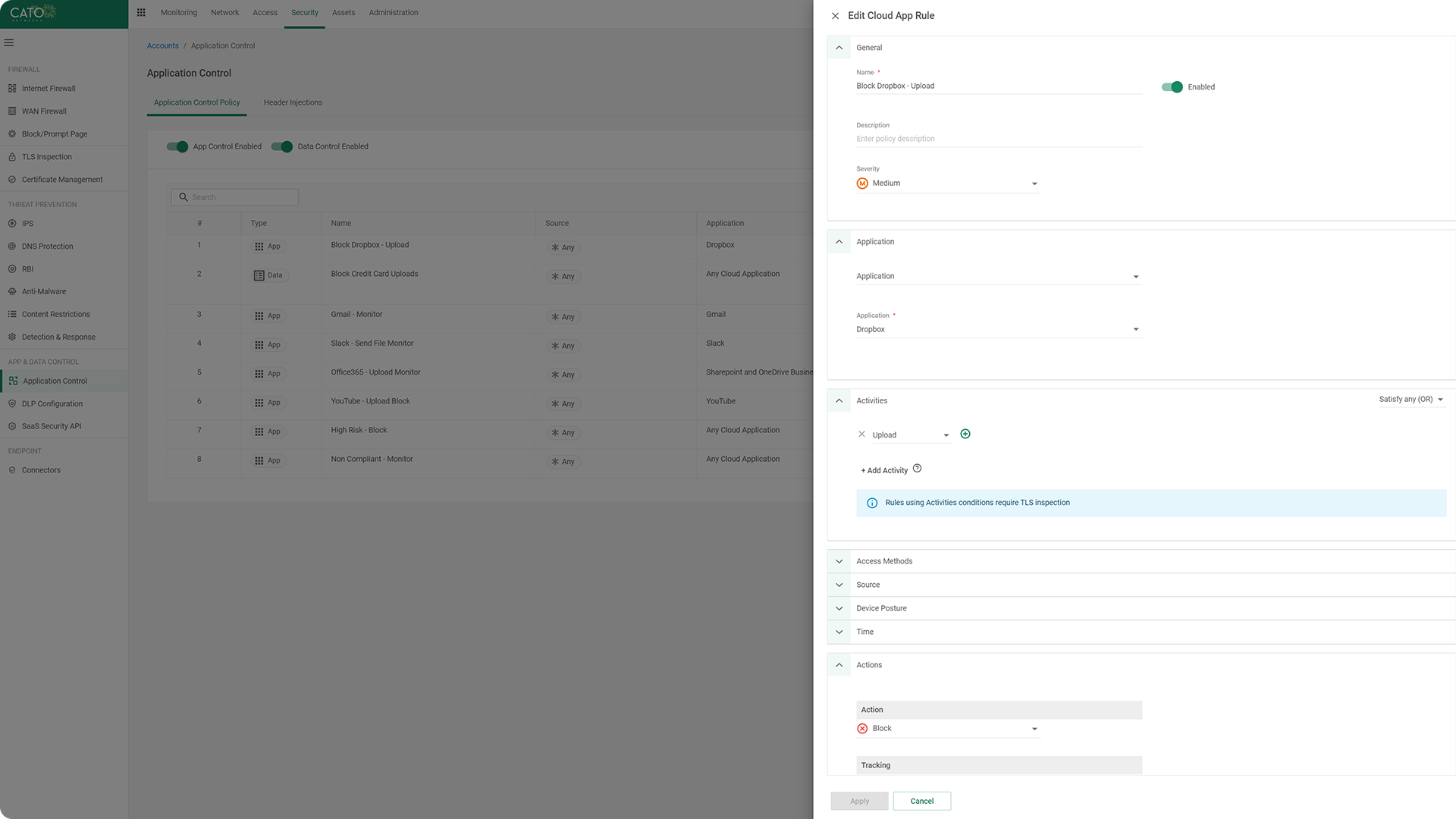
Controlling What Users Do Within Cloud Applications
Beyond the broader risk and compliance-based controls, Cato CASB also provides granular inline monitoring and control of the specific actions a user can take within an application. By inspecting the commands sent over HTTP/S and through APIs, granular user actions such as login, download, upload, view are identified. Admins can create policies to control action permissions to balance user productivity with data security in real-world situations such as blocking uploads from to unsanctioned file-sharing app but allowing downloads for data exchange with external organizations.
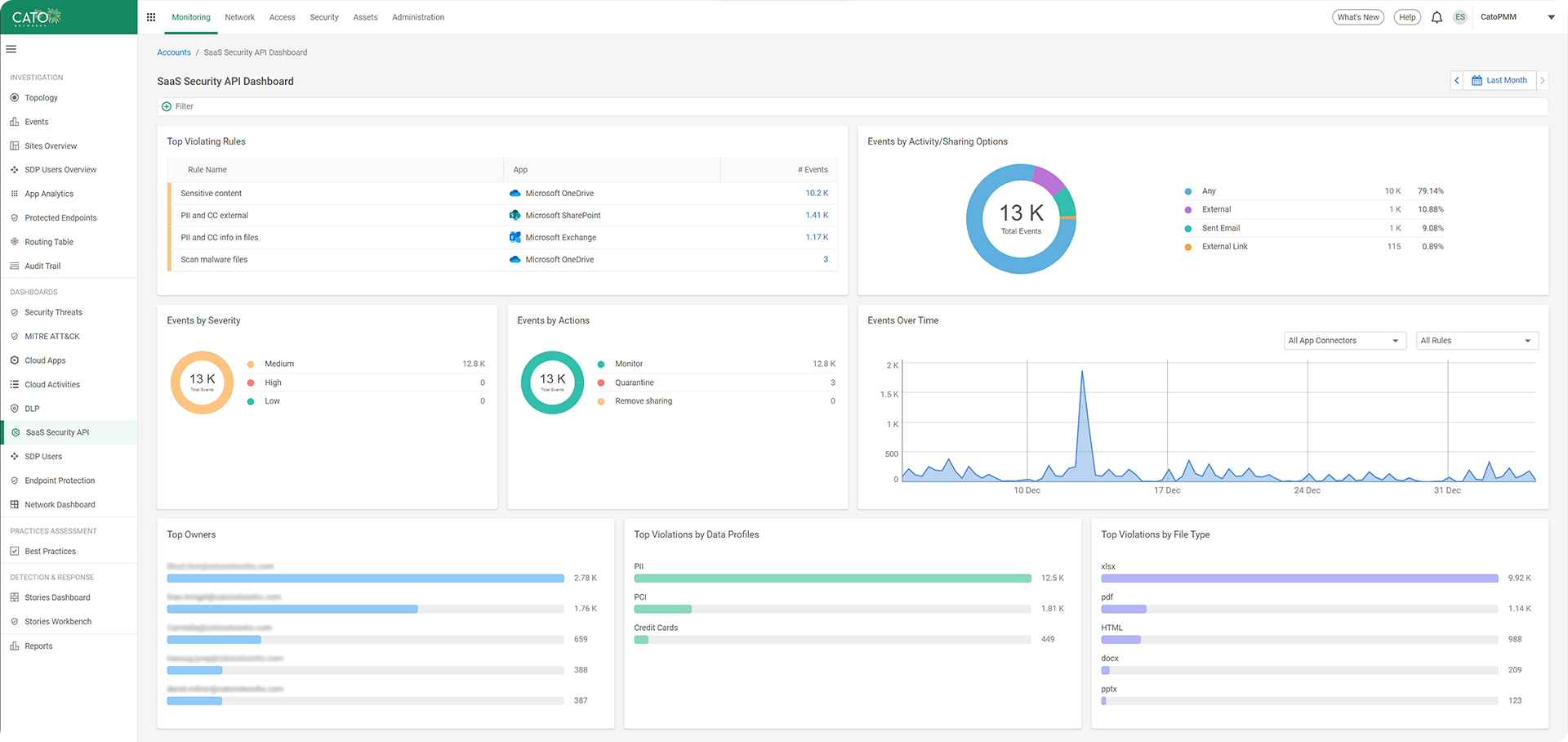
Inline and Out-of-Band Application Access Controls
Users access cloud applications both in the office and remotely, and from corporate devices and BYOD, requiring out-of-band control inline controls. In addition to its inherent visibility and control of inline traffic, Cato CASB provides API connectors for common enterprise cloud applications. The API connectors allow near real-time monitoring of application access to protect from data leakage, data sharing misconfiguration, and malware propagation. With Cato CASB operating both inline and out-of-band, the admin’s visibility, and control of cloud app usage is comprehensive and complete, enabling consistent control in all application access scenarios.
Stop Data Leaks with Enterprise SaaS Tenant Restriction
The same SaaS applications that are sanctioned and permitted by the enterprise may also be in private use by employees, posing a risk of sensitive data leakage. Following industry best practices, Cato CASB can limit access down to sanctioned tenants within sanctioned applications to ensure enterprise intellectual property doesn’t leak outside the enterprise without explicit permission.