CASB provides IT managers with comprehensive insight into their organization’s cloud application usage, covering both sanctioned and unsanctioned (Shadow IT and Shadow AI) applications. Cato’s CASB enables the assessment of each cloud application to evaluate its potential risk, and the definition of highly granular and flexible access rules to ensure least-privilege access and minimal exposure.
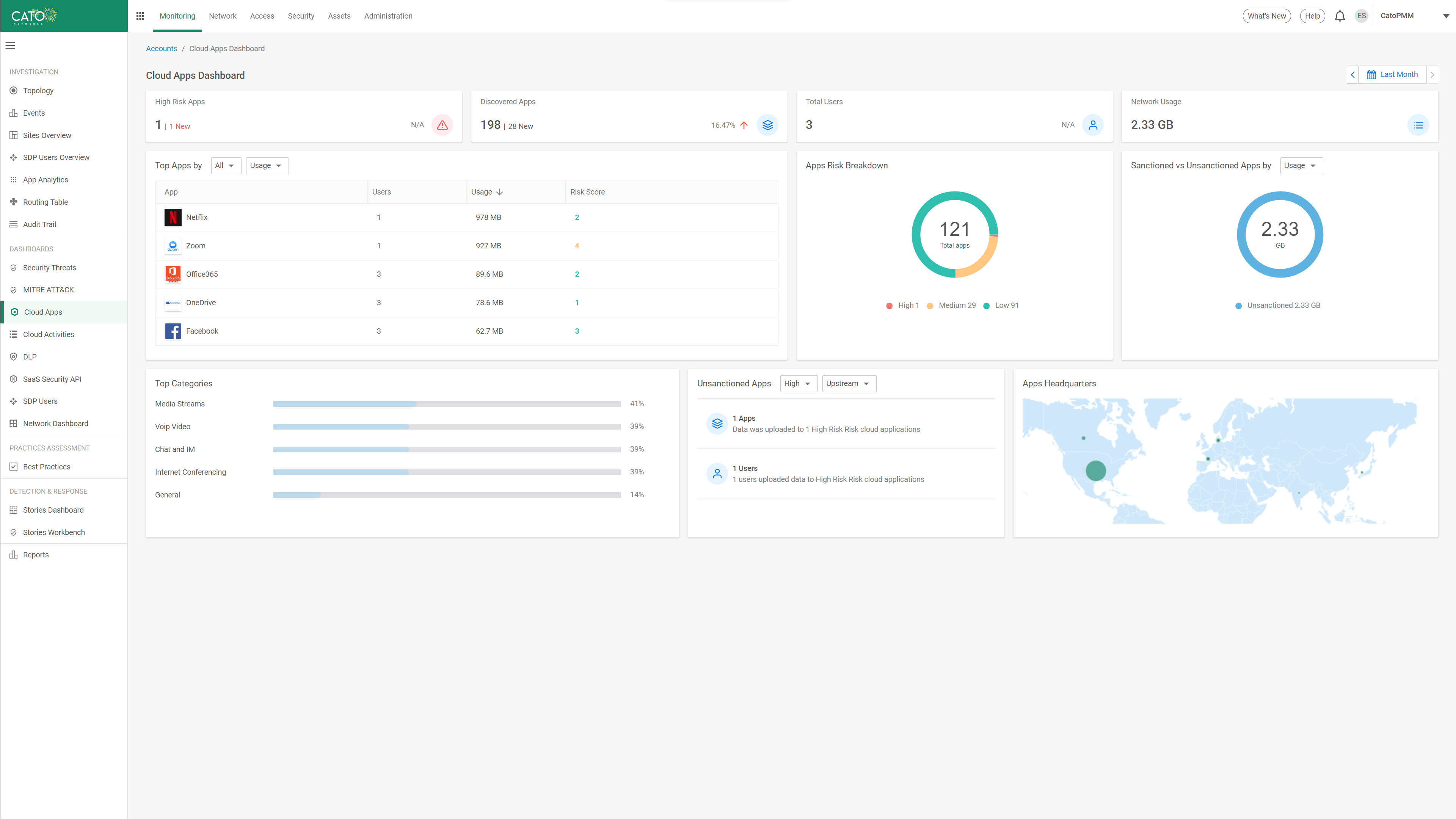
With infinite cloud apps available, IT teams need visibility and control. Cato’s CASB monitors the enterprise’s internet traffic, reporting all cloud applications in a detailed dashboard—including high-risk apps, user activity, usage volume, and app categories. IT can easily tag apps as sanctioned or unsanctioned, streamlining cloud usage management and control.
The rapid adoption of Generative AI (GenAI) tools presents new risks to organizations, often known as Shadow AI. Cato’s CASB enables organizations to harness GenAI securely without compromising data security, integrity or regulatory adherence. With complete visibility and control into GenAI application usage, IT teams can assess risks, enforce granular access controls, and detect sensitive data violations in real-time.
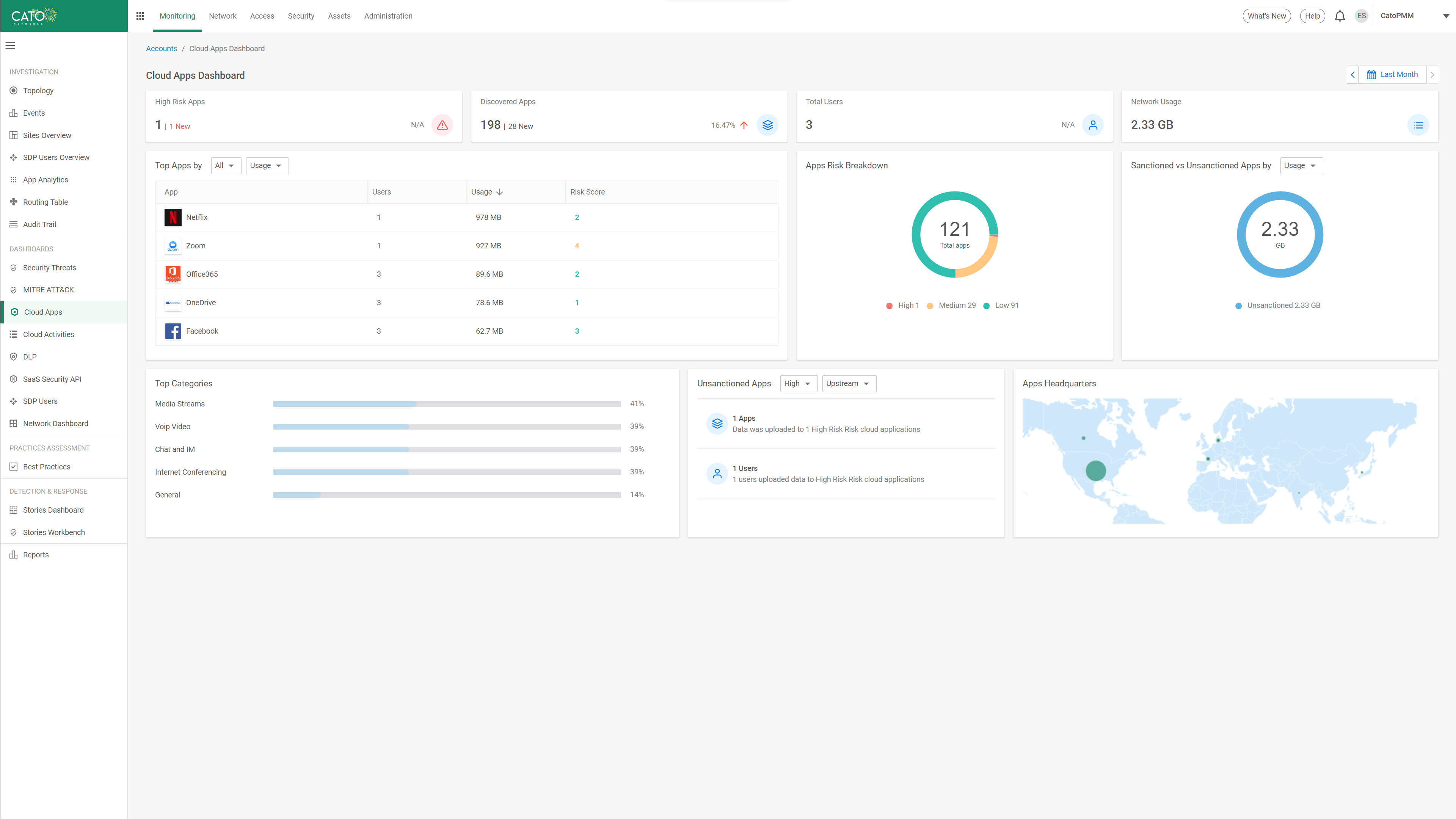
Manually validating the compliance of every cloud application is highly impractical for IT teams tasked with minimizing enterprise risk. As Cato’s CASB automatically discovers all cloud applications, it uses automated data collection and ML-based analysis to provide a calculated risk score for each application. Presented in a Cloud App catalog, each profile includes a description, compliance insights, and security controls. This gives IT the context they need to block high-risk apps, such as those lacking proper MFA/SSO or those failing to meet certain compliance requirements.
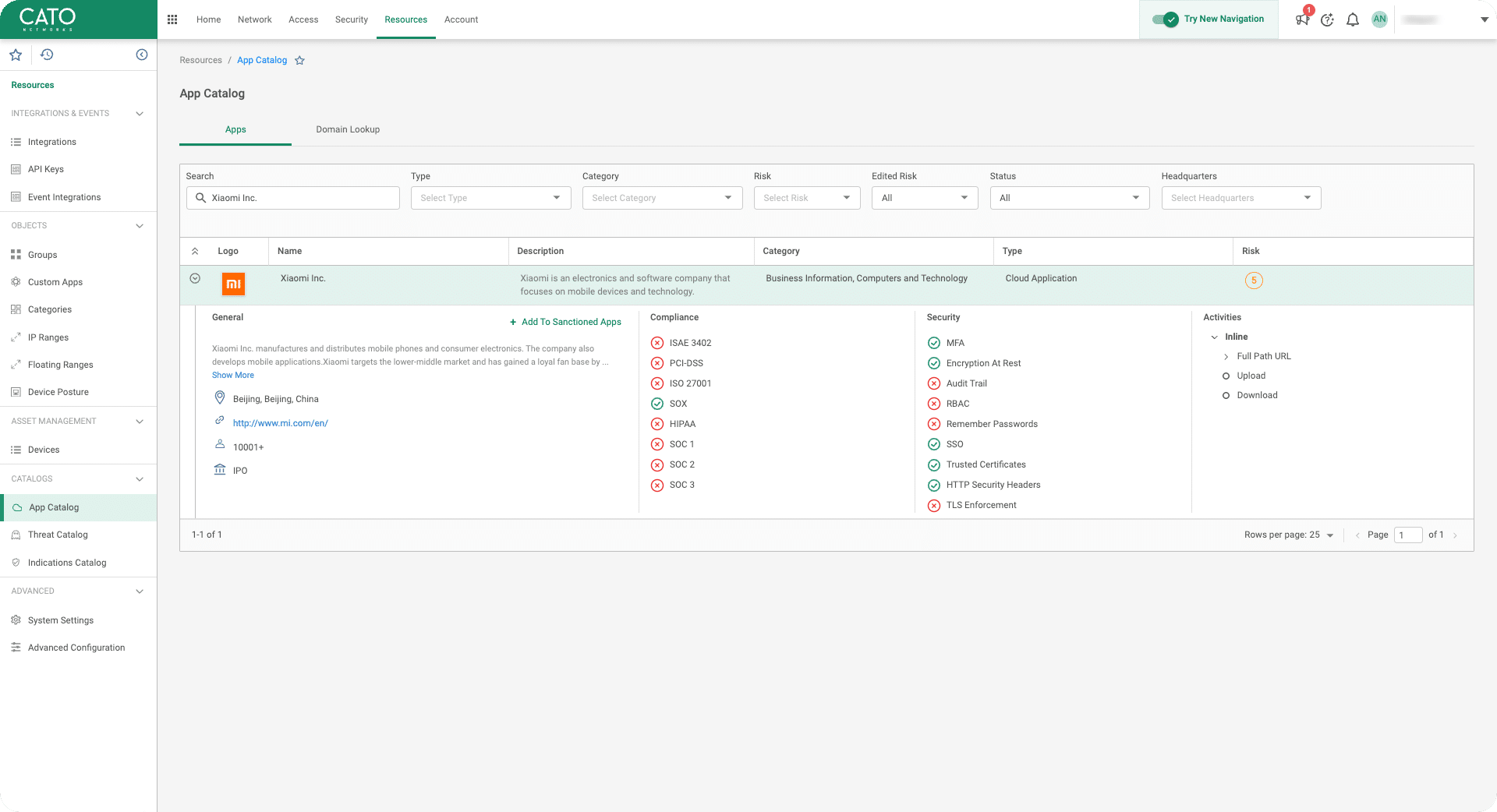
Cato’s CASB offers detailed inline monitoring of user actions (login, upload, download, view, etc.) within cloud apps via HTTP/S and API inspection. It enables IT teams to create granular policies that balance productivity and security. For example, permitting downloads while blocking uploads to unsanctioned file-sharing apps—ensuring secure yet flexible data exchange with external entities.
The same SaaS applications that are sanctioned and permitted by the enterprise may also be in private use by employees, posing a risk of sensitive data leakage. Following industry best practices, Cato CASB can limit access down to sanctioned tenants within sanctioned applications to ensure enterprise intellectual property doesn’t leak outside the enterprise without explicit permission.
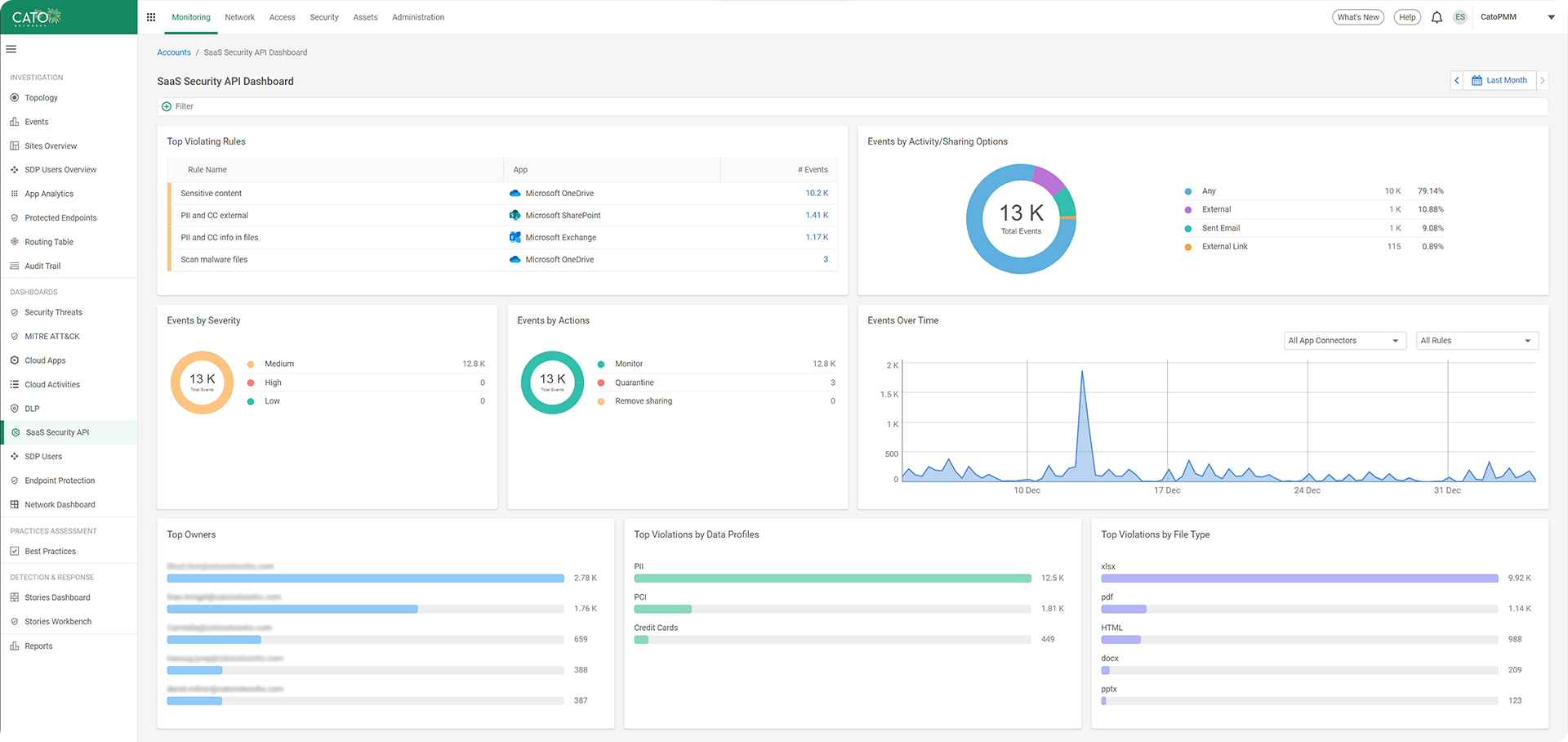
Cato’s CASB delivers real-time visibility and control of user actions across both managed and unmanaged devices. By combining inline inspection and API integrations, it identifies actions, data leaks, misconfigurations, and malware. The context-aware policy enforcement engine enables granular control that considers the source device and posture – ensuring safe, compliant access across all scenarios.
Cato’s CASB gives IT teams full visibility into all cloud apps—including Shadow IT and Shadow AI—so they can rate each app’s risk and enforce fine-grained, least-privilege access.
Customers use Cato to eliminate complex legacy architectures comprised of multiple security point solutions and costly network services. Cato’s unique SASE platform consistently and autonomously delivers secure and optimized application access everywhere and to everyone.
Cato Networks named a Leader in the 2025 Gartner® Magic Quadrant™ for SASE Platforms. Again.
Cato Networks Named a Leader and an Outperformer in the GigaOm 2025 SASE Radar
Cato Networks recognized as a Growth and Innovation Leader in SASE
Cato Networks Recognized as Global SSE Product Leader
WAN Transformation with SD-WAN: Establishing a Mature Foundation for SASE Success


“We ran a breach-and-attack simulator on Cato, Infection rates and lateral movement just dropped while detection rates soared. These were key factors in trusting Cato security.”
The Solution that IT teams have been waiting for.
Prepare to be amazed!