Essential steps to evaluate the Risk Profile of a Secure Services Edge (SSE) Provider
|
Listen to post:
Getting your Trinity Audio player ready...
|
Introduction
Businesses have increasingly turned to Secure Services Edge (SSE) to secure their digital assets and data, as they undergo digital transformation.
SSE secures the network edge to ensure data privacy and protect against cyber threats, using a cloud-delivered SaaS infrastructure from a third-party cybersecurity provider.
SSE has brought numerous advantages to companies who needed to strengthen their cyber security after undergoing a digital transformation. However, it has introduced new risks that traditional risk management methods can fail to identify at the initial onboarding stage.
When companies consider a third party to run their critical infrastructure, it is important to seek functionality and performance, but it is essential to identify and manage risks. Would you let someone you barely know race your shiny Porsche along a winding clifftop road, without first assessing his driving skills and safety record?
Ensuring Success with SSE: Your Helpful SSE RFP/RFI Template | Download the TemplateWhen assessing a Secure Services Edge (SSE) vendor, it is therefore essential to consider the risk profile alongside the capabilities.
In this post, we will guide you through the key steps to evaluate SSE vendors, this time not based on their features, but on their risk profile.
Why does this matter?
Gartner defines a third-party risk “miss” as an incident resulting in at least one of the outcomes in Figure 1.
Its 2022 survey of Executive Risk Committee members shows how these third-party risk “misses” are hurting organizations: 84% of respondents said that they had resulted in operations disruption at least once in the last 12 months.
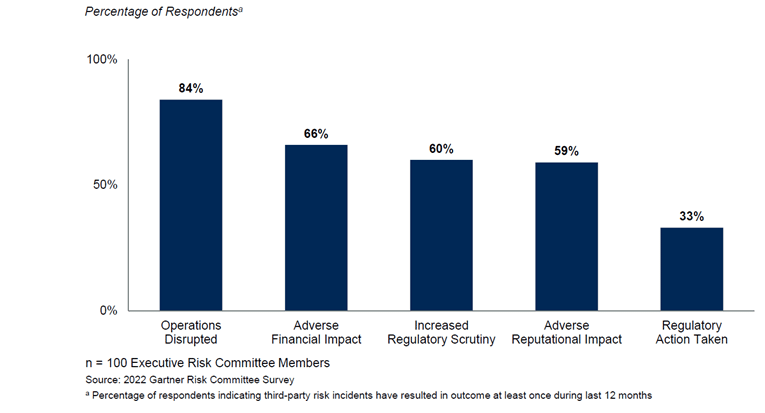
Courtesy of Gartner
Essential steps to evaluate the Risk Profile of a potential SSE provider
- Step 1: Assess Reputation and Experience
Start your evaluation by researching the provider’s reputation and experience in the cybersecurity industry. Look for established vendors with a proven track record of successfully securing organizations from cyber threats. Client testimonials and case studies can offer valuable insights into their effectiveness in handling diverse security challenges.
- Step 2: Certifications and Compliance
Check if the cybersecurity vendor holds relevant certifications, such as ISO 27001, NIST Cybersecurity Framework, SOC 2, or others. These demonstrate their commitment to maintaining high standards of information security. Compliance with industry-specific regulations (e.g., GDPR, HIPAA) is equally important, especially if your organization deals with sensitive data.
- Step 3: Incident Response and Support
Ask about the vendor’s incident response capabilities and the support they provide during and after a cyber incident. A reliable vendor should have a well-defined incident response plan and a team of skilled professionals ready to assist you in the event of a security breach.
- Step 4: Third-party Audits and Assessments
Look for vendors who regularly undergo third-party security audits and assessments. These independent evaluations provide an objective view of the vendor’s security practices and can validate their claims regarding their InfoSec capabilities.
- Step 5: Data Protection Measures
Ensure that the vendor employs robust data protection measures, including encryption, access controls, and data backup protocols. This is vital if your organization handles sensitive customer information or intellectual property.
- Step 6: Transparency and Communication
A trustworthy vendor will be transparent about their security practices, policies, and potential limitations. Evaluate how well they communicate their security measures and how responsive they are to your queries during the evaluation process.
- Step 7: Research Security Incidents and Breaches
Conduct research on any past security incidents or data breaches that the vendor might have experienced. Analyze how they handled the situation, what lessons they learned, and the improvements they made to prevent similar incidents in the future.
Gartner has recently released a Third Party Risk platform to help organizations navigate through the risk profiles of Third Party providers, including of course, cybersecurity vendors.
The Gartner definition of Third-Party Risk is: “the risk an organization is exposed to by its external third parties such as vendors, contractors, and suppliers who may have access to company data, customer data, or other privileged information.”
The information provided by vendors on Gartner’s Third-Party Risk Platform is primarily self-disclosed. While Gartner relies on vendors to accurately report their details, they also offer the option for vendors to upload attestations of third-party audits as evidence to support their claims. This additional layer of validation helps increase the reliability and credibility of the information presented. However, it is ultimately the responsibility of users to perform their due diligence when evaluating vendor information.
Conclusion
Selecting the right SSE provider is a critical decision that can significantly impact your organization’s security posture. By evaluating vendors based on their Risk profile, not just their features, and leveraging the Gartner Third Party Risk Platform, you can make an informed choice and gain a reliable cybersecurity provider. Remember: investing time and effort in the evaluation process now, can prevent potential security headaches in the future, ensuring your organization remains protected from evolving cyber threats and compliant to local regulations.