Are You Protecting Your Most Valuable Asset with a Data Loss Prevention (DLP)?
|
Listen to post:
Getting your Trinity Audio player ready...
|
The Information Revolution and The Growing Importance of Data
We have all heard about the information revolution, but what does it actually mean and how profound is it? An interesting way to understand this is by looking at how it has impacted modern enterprises.
A company’s assets can be divided into two types: tangible vs intangible. Simply put, tangible assets are those with a physical form factor (or which represents something physical). Intangible assets are those which do not really exist in the conventional sense, such as a company’s Intellectual property. Research by Ocean Tomo1 covering the leading 500 companies in the US (S&P 500) shows that in 1975, intangible assets accounted for 13% of their total value. By 2015 it grew to 84% and by 2020 it reached 90%.
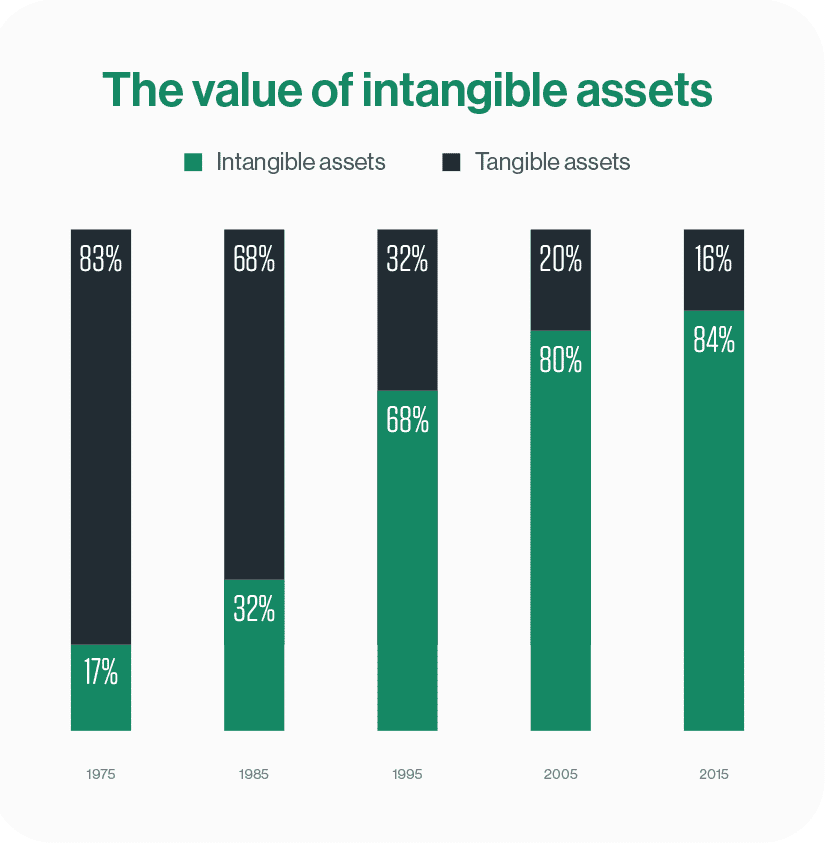
Simply put, 90% of the value of a modern-era company comes from what it knows, only 10% from what it has. When looking at how these numbers shifted over the last 45 years, we can see how information has become the single most valuable asset for the modern enterprise.
Most enterprises, however, do not have the necessary means to effectively protect their data. Let’s take a look at why this is, what protecting enterprise data means, and how to choose the right solution for your enterprise.
Protecting Your Company’s Data With DLP
Information has critical value to an enterprise. It is, however, quite difficult to protect, especially considering a great part of it typically resides in the cloud. There are numerous tools aimed at restricting access to enterprise assets, but the most efficient solution to protect the movement of information to and from enterprise assets is Data Loss Prevention (DLP).
While DLP solutions have been around for 15 years, their adoption has been limited and mostly by high-end enterprises. The complexity, prohibitive costs and expertise required to obtain and effectively manage DLP solutions has left them beyond the reach of most enterprises.
The increasing value of information, the growing adoption of cloud computing, and continued rise in cybercrime, are driving enterprises to the realization that they need to do a better job protecting their data. The need for DLP is clear and imminent, and market interest is rising.
Gartner saw a 32% rise in DLP inquiries in 2020 vs the previous year2. But how can enterprises overcome the current adoption barriers and enable DPL protection for their assets? Let us start by looking at the types of DLP solutions and their respective advantages and shortcomings.
Protect Your Sensitive Data and Ensure Regulatory Compliance with Cato’s DLP | WhitepaperDLP isn’t one thing
Gartner recognizes three types of DLP solutions2:
- Enterprise DLP (EDLP)
- Integral DLP (IDLP)
- Cloud Service Provider Native DLP (CSP-Native DLP)
The above solutions all have their pros and cons, and the acquiring decision-makers need to decide which solution attributes are more important for their use-cases, and which can be compromised. Let us take a deeper look into each one.
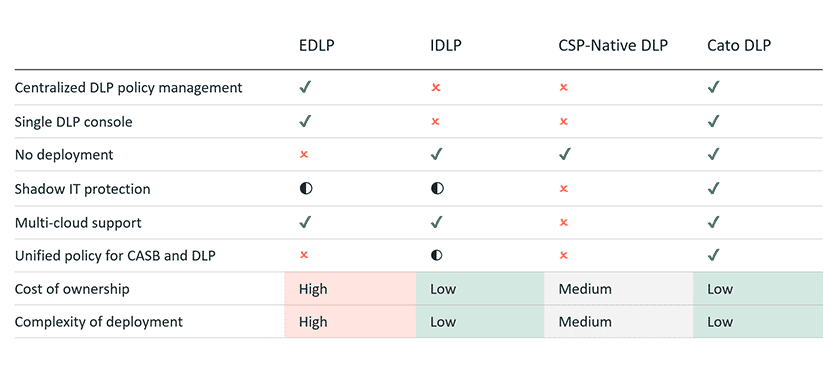
- Enterprise DLP (EDLP) – An enterprise level solution which covers all relevant traffic flows, and which is implemented as a stand-alone solution. EDLPs require adding (yet) another solution to an organization’s security toolbox. This typically requires an expansive project plan and additional expertise, adding complexity and cost to the project. While an EDLP offers a single console and policy management interface for the entire network, it is typically a separate console from the other network security tools (FW, IPS, AM, SWG, etc.). EDLPs will typically add another hop in the security service chain, and thus add latency and impact performance.
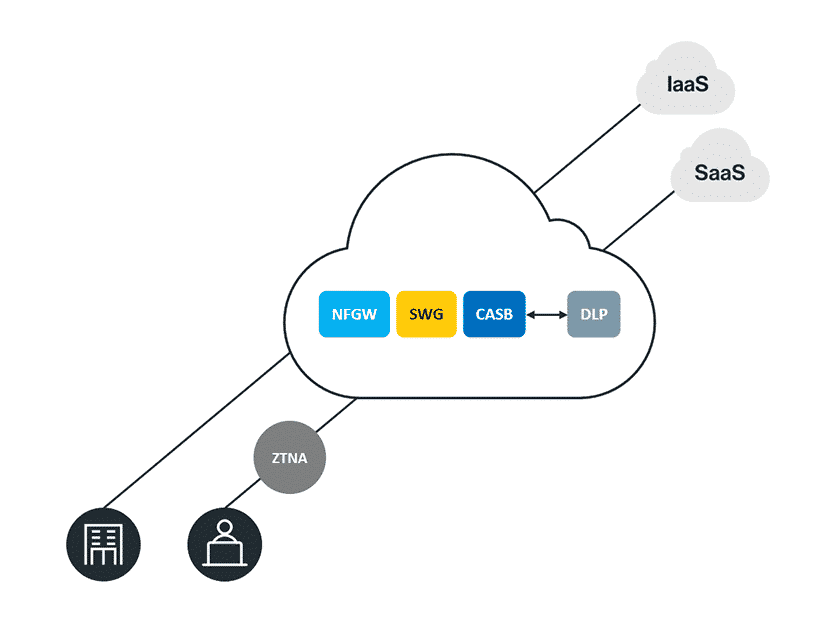
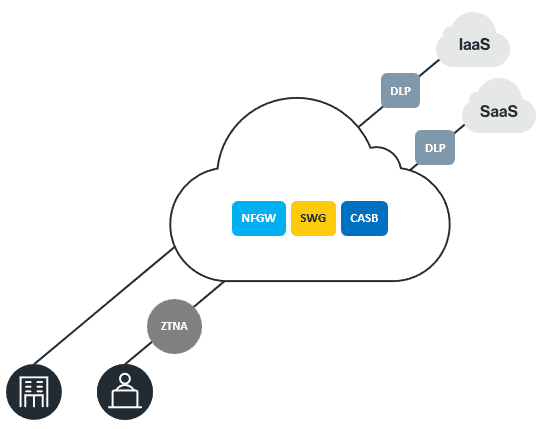
- Integrated DLP (IDLP) – DLP functionality that is added on top of a pre-existing security product such as a Secure Web Gateway (SWG). IDLPs simplify the deployment process and are regarded as a quick win to get DLP up and running quickly and at a reduced cost. IDLPs, however, are limited to the traffic and use cases the base product is intended for. Piggybacking on a SWG, for example, will cover only Internet-bound traffic and may not inspect IaaS traffic. Gaining wider coverage will require adding DLP to additional security products, which will lead to fragmented consoles and policy management.
- CSP-Native DLP – A cloud-based DLP which is deployed in, or provided by, a cloud service provider (CSP). This type of solution is also simple to adopt as it is delivered as a Software as a Service (SaaS) and doesn’t require deployment. It is, however, limited to the traffic sent to or from the specific CSP proving it. As most enterprises using cloud platforms are adopting a multi-cloud strategy, getting complete coverage will require using DLP services from several CSPs. Also, this type of solution will typically not cover all SaaS applications and is typically limited to sanctioned applications only.
Choosing The Right DLP For Your Enterprise
EDLPs typically offer better coverage and enhanced protection, however, the complexity and cost concerns drive security leaders to shy away and look for simpler and cheaper options. An IDLP offers this, but the limited coverage and disjointed consoles and policy management impact their effectiveness and level of protection. CSP-Native DLPs are also simpler to onboard but are cumbersome for multi-cloud deployments and do not cover the critical use-case of unsanctioned applications (AKA Shadow IT).
All the above DLP types come with compromises. Ideally, we would want a solution that is easy to deploy and manage, has complete coverage and optimal protection, does not impact performance, and covers unsanctioned applications.
The rise of SASE DLP
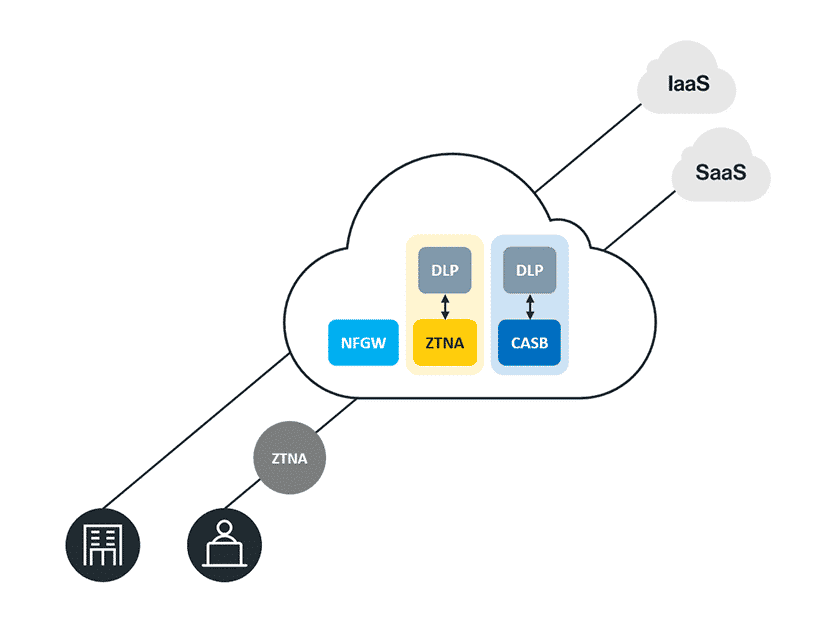
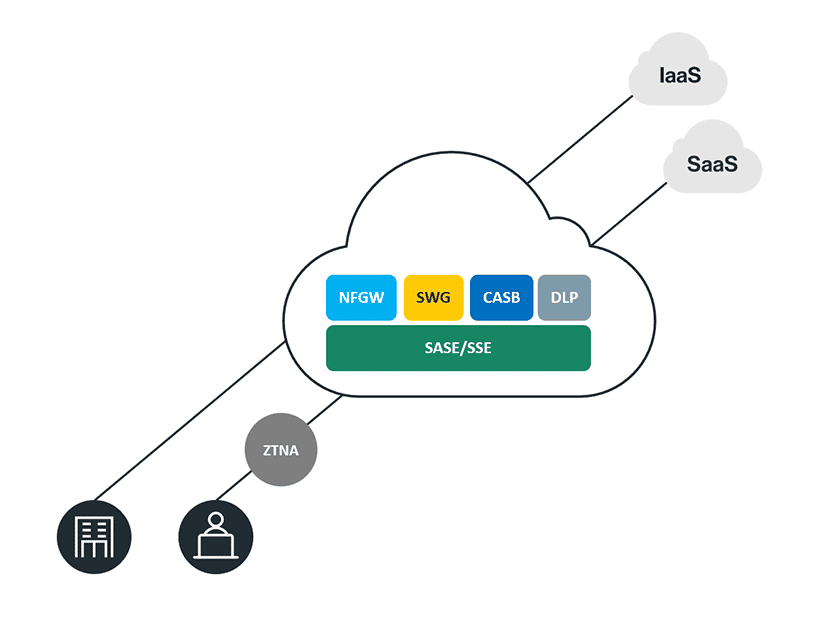
A true Secure Access Service Edge (SASE), or its Secure Service Edge (SSE) subset, offers the best of all worlds. Cato’s SASE Cloud, for example, covers all fundamental SASE requirements:
All edges – Cato SASE Cloud covers all enterprise users, on-prem or remote, and all applications and services, on-prem, IaaS and SaaS. This means that Cato’s SASE-based DLP will have complete coverage of all traffic and all use-cases.
Single pass processing – Cato SASE Cloud utilizes Cato’s proprietary Singe-Pass Cloud Engine (SPACE), which is based on a modular software platform stack that executes the networking and network security services in parallel. This enables a shared context, enhancing overall protection, and minimizes latency. Adding DLP to a Cato deployment is done by a flip of a switch and requires no additional deployment.
Cloud-native – Cato DLP is delivered fully from the cloud and offers all the benefits of a cloud-native solution, including unlimited scalability and inherent high-availability. Since it is part of the Cato SASE Cloud, it is completely CSP-agnostic and supports all leading cloud service providers, making it a true multi-cloud solution.
Converged – Cato SASE runs and manages all services as a single solution, enabling configuration, management, and visibility from a single-pane-of-glass management console.
The pros and cons of the different DLP solution types:
The DLP that’s in your reach
A true SASE solution enables enterprises to adopt a DLP solution that benefits from all the advantages mentioned above, and more. The reduced complexity and costs, lower the traditional barrier of adoption, enabling enterprises of all sizes and levels of expertise to better protect their data. It also eliminates the dilemma of what to compromise on when looking to adopt DLP within your environment. A SASE DLP requires no compromises. Protecting your enterprise’s most valuable asset is just a flip of a switch away.
To learn more about Cato DLP, read our DLP whitepaper.
1 Harvard Business Review
2 DLP market guide 2021 – Gartner