Solving Real-World Challenges – Your Pathway to SASE

Table of Contents
- 1. Real-world Challenges Breeds New Networking and Security Considerations
- 2. The Cato SASE Approach to Rapid Digital Transformation
- 3. What is SASE and its Core Requirements?
- 4. 7 Questions You Must Ask Before Selecting Your Next Solution
- 5. Mapping Your SASE Journey in 4 Easy Steps
- 6. Does Your Solution Allow You to Plan for the Future?
|
Listen to post:
Getting your Trinity Audio player ready...
|
We are witnessing a tremendous shift in mindset regarding technology’s relationship to the business. As IT leaders learned during Covid, business challenges are IT challenges, and IT challenges are business challenges. As digitization continues to advance, these leaders continue to face an array of challenges, and the solutions they choose will determine their success or failure.
This article provides IT and security professionals with actionable ideas for selecting a robust platform for digital transformation to address the network and security challenges that adversely impact their business.
We cover:
- Real-world challenges in need of solutions
- The Cato SASE Approach
- SASE Comparisons
- Key questions to ask yourself when looking for a solution
- Mapping Your Journey
Real-world Challenges Breeds New Networking and Security Considerations
Global Business Expansion Creates New Connectivity Requirements

We are a global business society that is constantly expanding, whether organically into new markets or through mergers and acquisitions into new business lines. Whatever the impetus, there are real challenges these organizations will face. Adding new locations, for example, requires planning for global and local connectivity, which could be very inconsistent, depending upon the region.
In the case of mergers, we must deal with inconsistent or incompatible networks architectures, while factoring in the unreliable nature of global connectivity over a public internet. And let’s not forget inconsistent security policies that add to your headaches.
And finally, we must consider how all this affects migrating new users and apps onto your core network, as well as ensuring access and security policies are correct. Not impossible, but this could take weeks or months to achieve.
All this results in unexpected consequences.
Core Challenges:
- Rapid site deployment
- Inconsistent connectivity
- Public Internet Transport
On-premise to Cloud Migration Spurs Capacity Constraints
Most obstacles in cloud adoption are related to basic performance aspects, such as availability, capacity, latency and scalability. Many organizations neglect to consider bandwidth and capacity requirements of cloud applications. These applications should deliver similar or better performance as legacy on-premise. However, with the rush to adapt to the new Covid-normal, many are finding this is far from reality.
Scalability is also an issue with cloud deployments. As businesses continue to grow and expand, the greater the need for a cloud network that scales at the speed of their business, and doesn’t restrict the business with its technical limitations.
All together, these are real issues IT teams continue to face today, and until now, saw little to no relief in sight.
Core Challenges:
- Capacity planning and cost management
- Poor app performance
- Scalability
Expanding Cyber Threat Landscape
Every year, like clockwork, we witness numerous global companies attacked by cyber criminals at least once per day. Many have had sensitive data stolen and publicly leaked. The pandemic only exacerbated this, pushing more employees further from the enterprise security perimeter. The growth in Work-From-Anywhere (WFA) introduced more remote worker security challenges than many expected, and not many were truly prepared.
Additionally, as more organizations move their apps to cloud, providing security for these apps, as well as safe use of 3rd party SaaS apps, became an even stickier point for today’s enterprises. This, along with securing remote workers, is pushing IT leaders to face the harsh reality of their current cyber defense short-comings.
As these businesses attempt some form of return to normal, it’s clear we may never make it back to traditional full-time office setup. WFA, as well as increased cloud usage, is here to stay, meaning the threats to the business will only increase. This means the potential costs of cyber breaches will follow suit.
Core Challenges:
- Expanding cyber threat landscape
- Securing Work-from-anywhere (WFA)
- Improper employee usage
The Cato SASE Approach to Rapid Digital Transformation
It’s easy for most organizations to take a traditional approach to these challenges by looking for point solutions or creative chaining of technologies to create a bundled solution. While this provides an initial “feel-good” moment, this complex approach, invariably, creates more problems than it solves.
Cato addresses these challenges through simplicity, and accomplish this through our converged, cloud-native approach. The Cato SASE (Secure Access Service Edge) Cloud converges core capabilities of networking, security and access management into a single software stack that delivers optimized cloud access, predictable performance, and unified policy management. Our SASE Cloud also provides complete visibility to inspect all traffic flows and provide advanced, holistic threat protection and consistent policy enforcement across a global private backbone.
Cato addresses the challenges of global connectivity with our global private backbone, providing resiliency and performance SLA guarantees. Our cloud acceleration and optimization address the performance challenges faced when migrating enterprise apps to a cloud data center. And we address the security challenges with advanced, holistic security tools like NGFW, SWG, NextGen Anti-Malware, IPS, CASB and DLP.
The Cato SASE Cloud enables enterprises to more rapidly and securely deliver new products and services to market, and more quickly respond to changes in business and technology dynamics that impacts their competitiveness.
What is SASE and its Core Requirements?
When deciding on SASE solutions, it is helpful to understand the core requirements as specified by Gartner and compare the various vendors in the market. For SASE to deliver on the promise of infrastructure simplicity, end-end optimization and limitless scalability, it must adhere to certain requirements: Converged, Cloud-native, Global, All Edges and Unified Management.
- Converged – A single software stack that combines network, security, and access management as one. This eliminates multiple layers of complexity. There is no need to stitch together bundles of disparate technologies. No need for multiple configuration tools to configure these different technologies. Convergence leads to simplistic architecture, easier management, and lower overall costs to the business.
- Cloud-Native – Built in the cloud for the cloud. Unlike appliances and virtualized solutions based upon appliances, being cloud-native enables vendor to deliver more flexibility in deployment and scale easier and faster when customers require more capacity.
- Global – Having a global presence means a network of PoPs everywhere, connected via a global private backbone. This means the network is everywhere the customer business is, delivering guaranteed performance and optimization for all traffic, consistent policy enforcement globally, network resilience to keep the business running.
- All Edges – Consistently and seamlessly delivering services to all edges (branch, endpoint, data center, cloud) without complex configuration or integration.
- Unified – A single, unified management console to provision and manage all services. No need to build dashboards to communicate with multiple technologies to manage the deployment .
These are non-negotiable requirements that only a true Cloud-Native SASE solution can deliver. Appendix A highlights how the Cato SASE Cloud compares to appliance-based solutions.
7 Questions You Must Ask Before Selecting Your Next Solution

To solve these issues, here are some key questions to ask yourself and your team. This will help you find the right solution to alleviate these challenges.
1. What real problems are we trying to solve?
Identify what technical challenges are inhibiting you from delivering the best app, networking, and security experience for the business. Discover which projects are on hold because your infrastructure can’t accommodate them. The answers will provide you with insights into the actual problems you need to solve.
2. Which solution solves this, while scaling at the speed of our business?
The natural response when encountering point-problems, is to find a point-solution. When doing so, ask yourself which solution delivers a more holistic approach to all your concerns (from question 1) while also providing a platform that scales at the speed of your business.
3. How can we ensure cost-effective, business continuity?
Business continuity is non-negotiable, so when searching for a solution, ensure you find one that provides a resilient architecture that keeps your business running, no matter what happens.
4. With limited resources, how fast can we deploy new sites?
Your solution shouldn’t just look good on paper, it needs to work well in practice. You can’t wait two, three or six months to launch new branches. Find a solution that enables rapid, zero-touch deployment, with minimal impact on your teams.
5. How can we build and maintain a consistent policy structure?
Multiple configuration tools can create policy mismatches, which in turns, creates gaps and puts your critical applications at risk. To reduce this risk, find a solution that addresses configuration inconsistencies.
6. What’s the right amount of security?
Security is an imperative, so most businesses try to implement multiple solutions with lots of cool-sounding features to make themselves feel secure. Unfortunately, multiple point solutions create security blind spots. Additionally, about 80%-90% of “cool” security features are never used. Achieve more with less by finding a solution that improves your security posture, independent from the size of your corporation or the size of your IT team
7. What’s our best option for global connectivity?
Connectivity can make or break your business. Find a solution that provides increased capacity, guaranteed performance, and a global private backbone. Don’t settle for less.
Mapping Your SASE Journey in 4 Easy Steps
Now that you understand the networking and security challenges adversely affecting your business and their proposed solutions, now it’s time to map out your SASE journey. Doing this can be easier than you might think.
1. Prioritize:
After you’ve answered the above questions, it’s now time to prioritize and create your migration plan. You may have one problem to solve, and in this case it’s easy. But most will have several, so once determined and prioritized, it’s time to plan and put it into action. Of course, Cato and our partners can assist, and even recommend a migration plan.
2. Solve the problem:
This is wholly up to the organization. Some may prefer to tackle low-hanging fruit projects to build confidence in the teams. In this case, easy problems may go first. But others believe in “Go Big or Go Home”, so they may start with the most critical problems first. It’s basically up to the organization to define.
3. Observe:
Observe the “wow” moments of that problem being solved. Whether performance, enhanced security, global connectivity, and so on – observe and enjoy. Then move onto the next problem or project.
4. Repeat and observe.
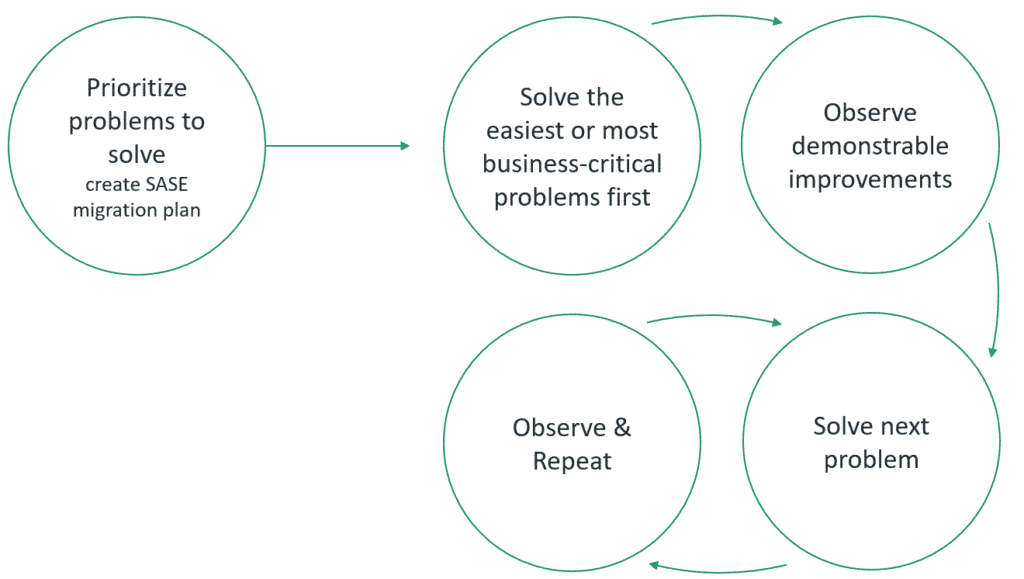
It’s a straight-forward journey, and a well-defined plan makes it all flow smoothly.
Does Your Solution Allow You to Plan for the Future?
Solving problems the legacy way is how we acquired the complexity beast we have today. So, it’s time we change the game and become more strategic about addressing our IT challenges.
The Cato SASE Cloud does this by converging all the capabilities organizations need today into a single platform, while future-proofing their businesses for whatever is next. In contrast, a non-SASE approach forces you to spend time and resources evaluating, acquiring, and integrating multiple technologies to address each requirement.
Taking a platform approach to your transformation journey will address the challenges of today and prepare you for the opportunities of tomorrow. Taking a Cato SASE approach will enable your network to scale at the speed of your business.
Appendix A – SASE Core Requirements Comparison Chart
| Gartner SASE Requirements | Cato | Appliance Solutions | Cato SASE Advantage for Customers |
| Converged | Yes One single software stack with the network and security as one | NO A mixed collection of appliances that are stitched together. | Network and security simplicity and uniformity in policy enforcement can only be achieved through convergence. |
| Cloud-Native | Yes Built as a distributed cloud-native service from scratch, with no appliance baggage | NO Use virtualized hardware placed in the cloud | Easy and inexpensive to scale when increased capacity is required. Customers can scale and grow at the speed of their business, and not be limited by the complexity of a stale network. |
| Global | Yes 75+ PoPs available located near every major business center. Each has an independent expansion plan. | Limited Relying on IaaS for hosting PoPs limits availability and degrades performance. Growth depends on IaaS plans, not the SASE vendor’s | Cato’s global private backbone delivers performance guarantees, resiliency and policy consistency between sites across the WAN and cloud. |
| All Edges | Yes Designed with light edge connectors (SD-WAN, SDP, Cloud) with a cloud first architecture to deliver same service to all edges | Limited Delivering services to different edges requires a different portfolio solution. So, this is only achieved by stitching together portfolio products | Connecting and servicing all edges (branch, endpoint, data center, cloud) does not require complex configuration or integration |
| Management | Unified One console to control all SD-WAN, security, remote access, and networking policies with full analytics and visibility. Self-service or managed service | No Multiple configuration interfaces to navigate | A single policy management app eliminates configuration gaps by ensuring consistent policy configurations & enforcement across the entire network. |
About Cato Networks
Cato is the world’s first SASE platform, converging SD-WAN and network security into a global cloud-native service. Cato optimizes and secures application access for all users and locations. Using Cato SASE Cloud, customers easily migrate from MPLS to SD-WAN, improve connectivity to on-premises and cloud applications, enable secure brach Internet access everywhere, and seamlessly integrate cloud data centers and remote users into the network with a zero-trust architecture. With Cato, your network and business are ready for whatever’s next.
For any questions about the ideas suggested in this article, and if you have some more of your own, feel free to contact us at: catonetworks.com/contact-us/