Firewall-as-a-Service (FWaaS) is a new and revolutionary way of delivering firewall and other network security capabilities as a cloud service. It eliminates the constraints and complexities of legacy physical and virtual firewalls, and make network security consistently available everywhere.
Cato FWaaS eliminates security gaps by inspecting all traffic—across the internet (north-south), WAN (east-west), and LAN—without limitations on ports, protocols, or encryption. Unlike legacy firewalls, which create blind spots and complexity, Cato delivers unified security from the cloud with multi-gig throughput, replacing branch, data center, and LAN firewalls. By consolidating security into a single cloud-native architecture, Cato ensures there are no configuration gaps or inspection blind spots, reducing the risk of breaches and simplifying security management.
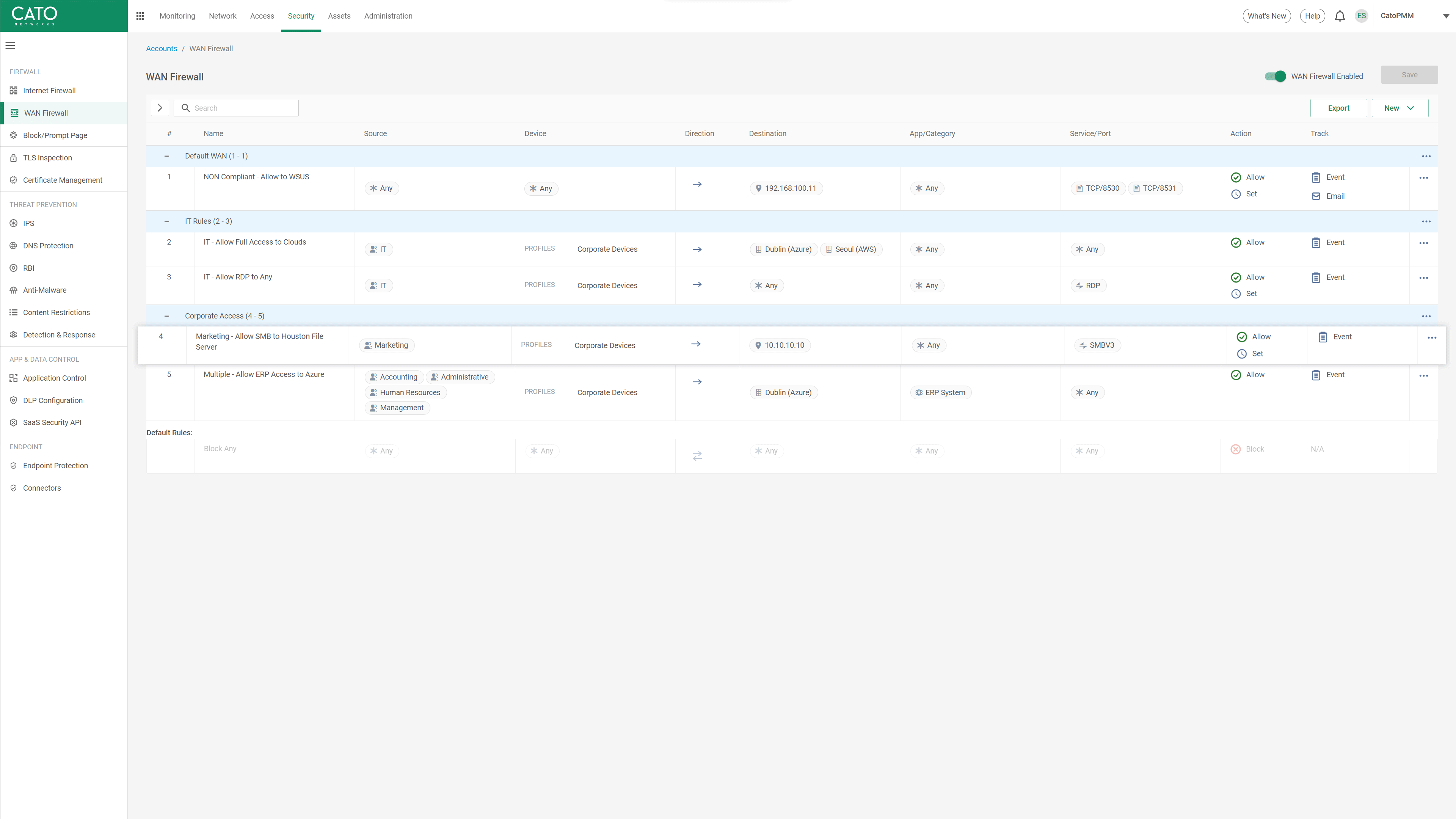
Cato FWaaS provides enterprise-grade access control for WAN, Internet and LAN. It supports a rich set of objects (user identity, organization unit, device, host, application, protocol, location, network, VLAN, and more) that can be used in the rules, and the ability to manage them in logical groups that can combine multiple object types.
AI-based autonomous policies further enhance ruleset management with continuous analysis and optimization, identification of misconfigurations and zero trust enforcement in real time. This results in fewer errors, sustained compliance, and consistent enforcement across all environments.
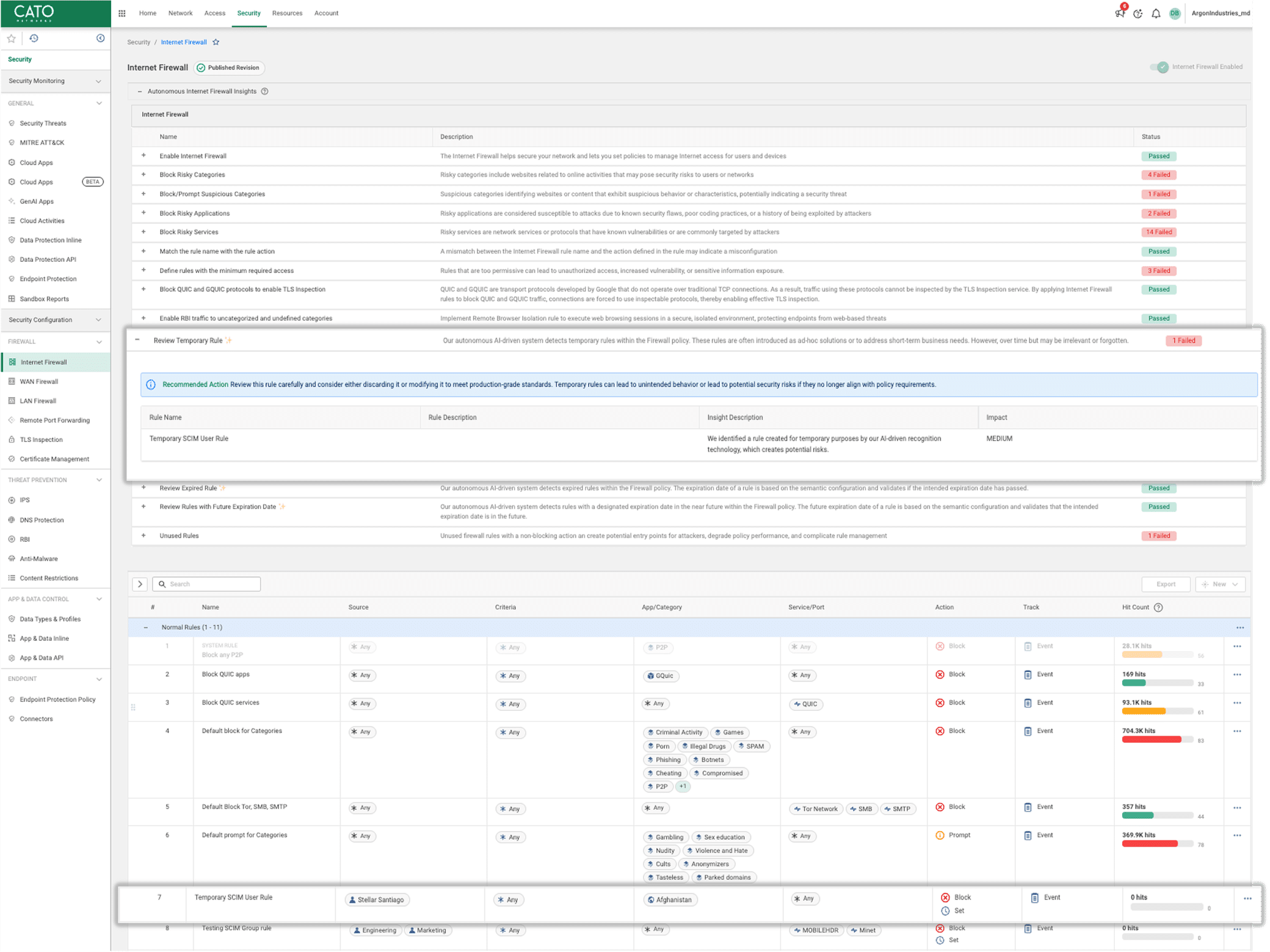
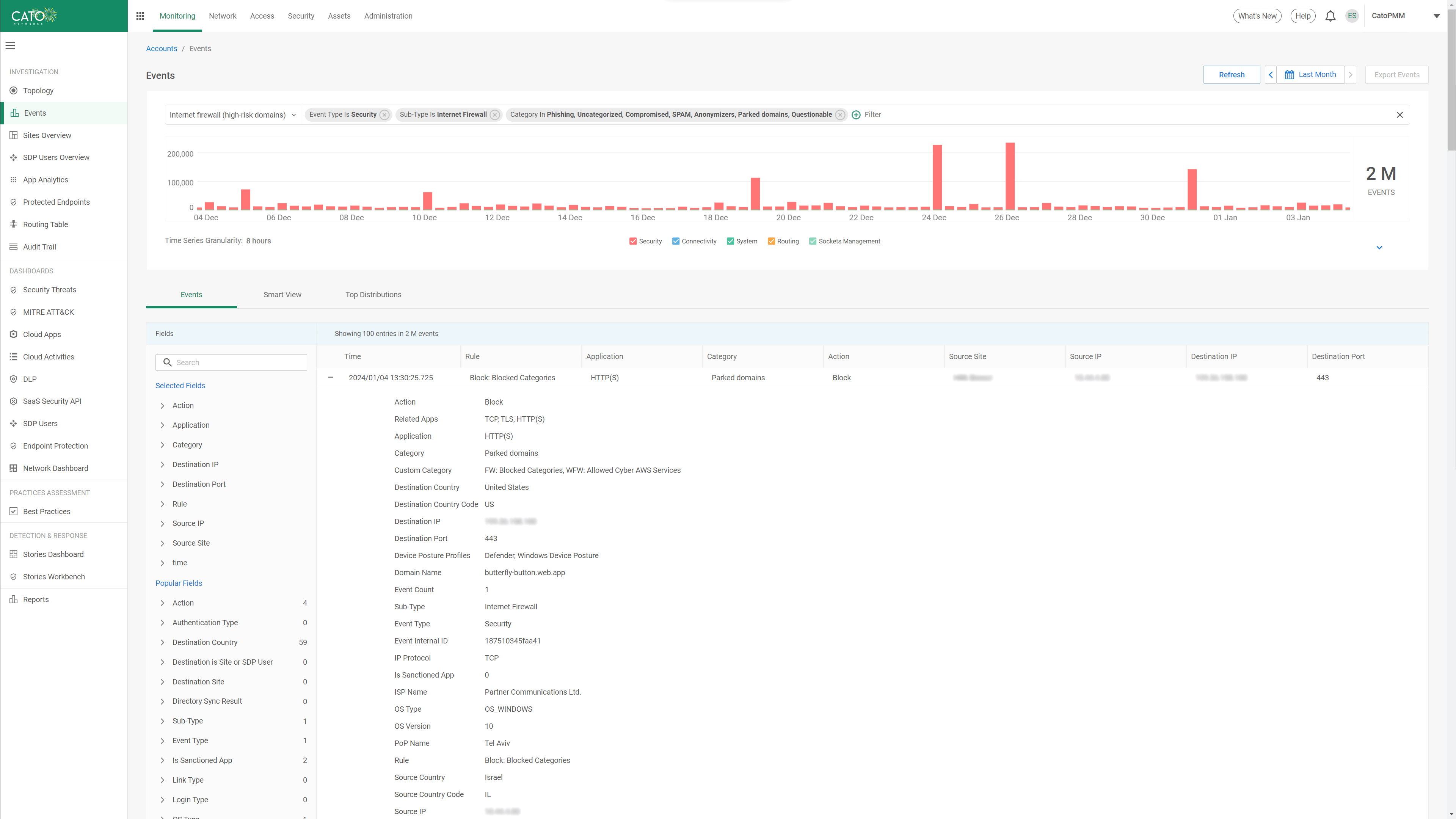
All rules and actions in the Cato FWaaS can be set to record an event and store it on the Cato SASE Cloud Platform for an agreed upon retention period.
Email notifications can be configured to alert on selected event that repeat during a defined period and at a defined urgency.
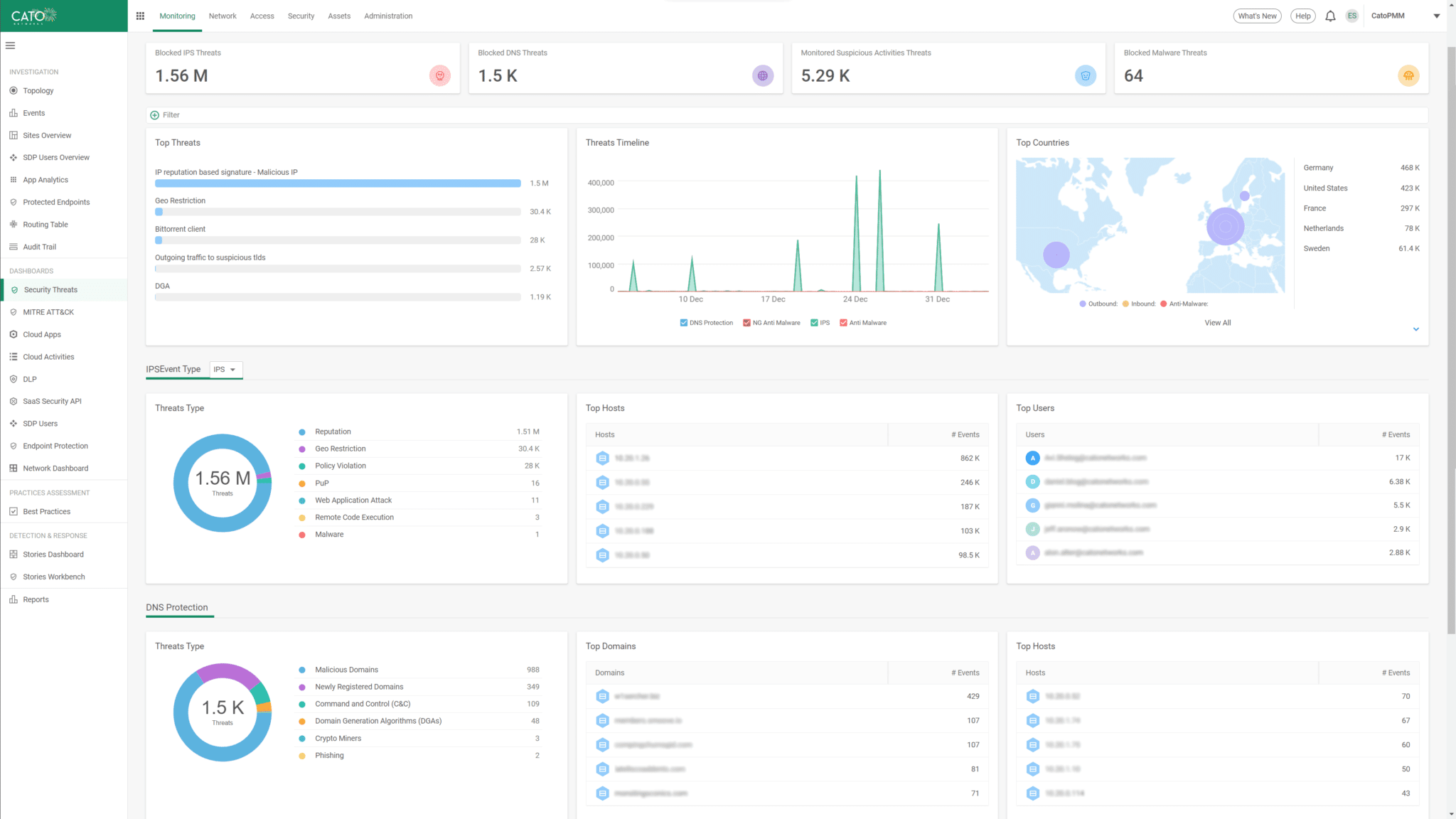
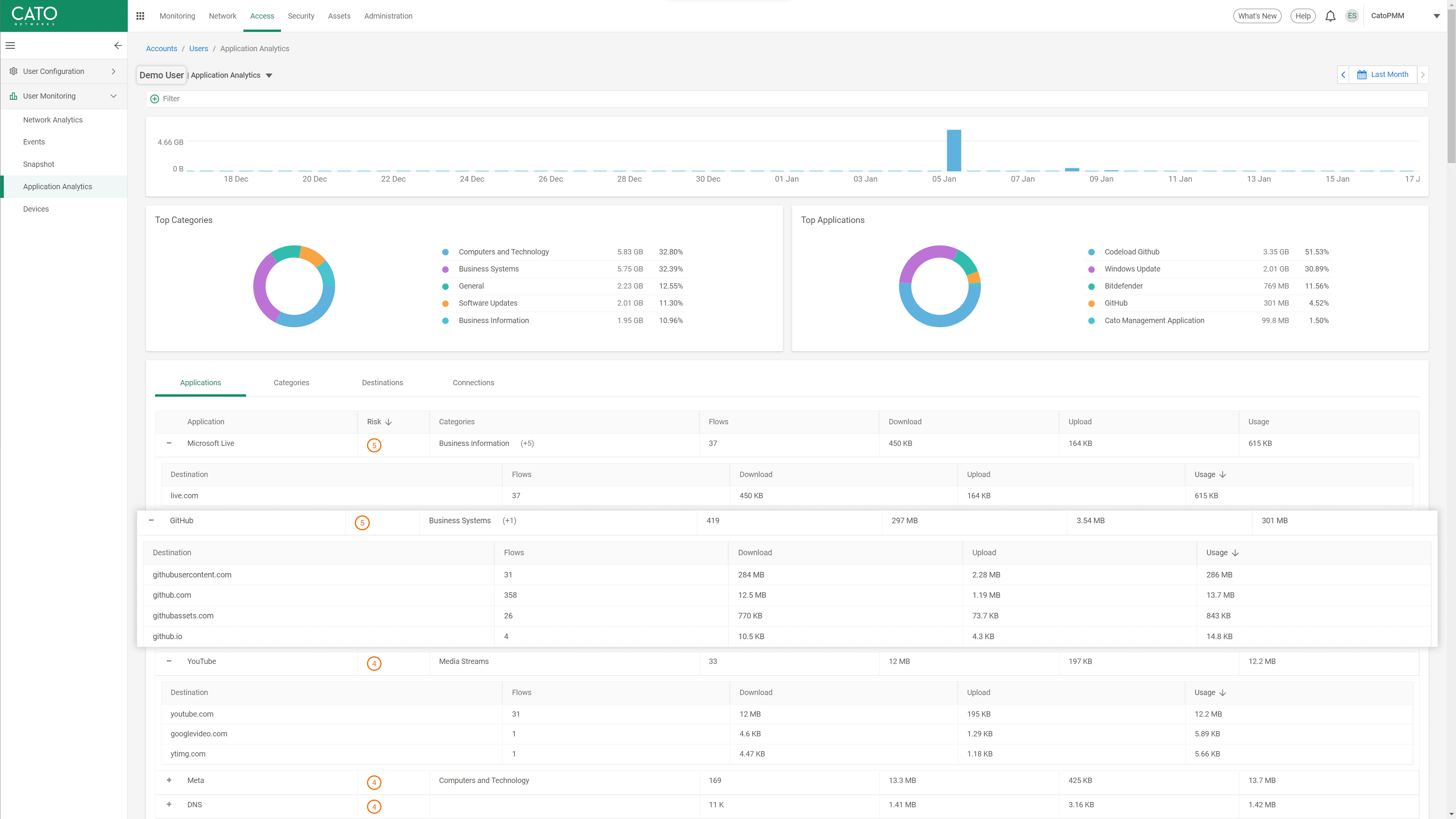
Event monitoring and analysis is available through dedicated dashboards and through the event monitoring interface which provides easy-to-use searching and filtering.
An audit trail records all admin activities for tracking, monitoring and auditing.
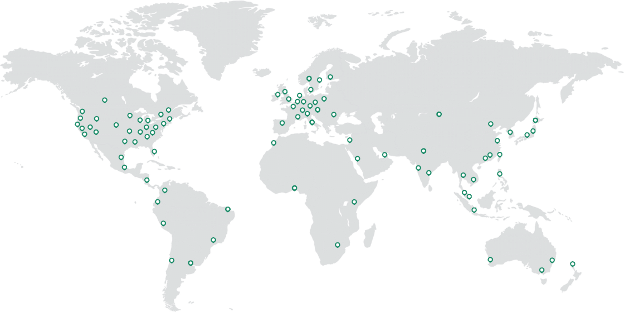
Cato FWaaS is a cloud service that benefits from a cloud-native software architecture. Features and capabilities are not limited by the underlying hardware, and autonomous and elastic scaling and self-healing ensures high performance and service resiliency.
Cato allow admins to enable all features, including TLS inspection, and use any type and number of objects, groups and rules without worrying about performance or availability.
Cato’s cloud-native software architecture eliminates concerns of increased latency due to CPU load, packet drops, or device failure. Similarly, risk of mid-term appliance replacement due to insufficient compute power is avoided.
Microsegmentation can be easily configured to restrict access to sensitive resources. Policies can be set based on groups, networks, VLANs and individual objects such as hosts , users and devices to govern granular access that meets business requirements. For zero trust, Cato allows admin to set identity-to-identity, identity-to-app, and app-to-app access policies that factor in not only the identity of a user, but also their geo location, method of connectivity, security posture and more. Were compliance to regulations require, enforcement can be executed locally at the LAN.
Cato FWaaS includes built-in awareness to thousands of applications across all ports and protocols and the ability to define custom applications. A DPI engine identifies the application or service as early as the first packet and without having to decrypt the payload.
Cato allows policy configuration and enforcement that factors the identity of the users and the organization units they belong to. By synchronizing with the user directory, and using the identity agent in the Cato Client, a user identity is associated with every network flow.
Watch how Cato automates policy management and delivers consistent enforcement everywhere, with zero patching
Customers use Cato to eliminate complex legacy architectures comprised of multiple security point solutions and costly network services. Cato’s unique SASE platform consistently and autonomously delivers secure and optimized application access everywhere and to everyone.
Cato Networks named a Leader in the 2025 Gartner® Magic Quadrant™ for SASE Platforms. Again.
Cato Networks Named a Leader and an Outperformer in the GigaOm 2025 SASE Radar
Cato Networks recognized as a Growth and Innovation Leader in SASE
Cato Networks Recognized as Global SSE Product Leader
WAN Transformation with SD-WAN: Establishing a Mature Foundation for SASE Success


“Cato future-proofs Swissport’s IT infrastructure. The platform constantly evolves, adapts to new technologies, and provides the visibility and security we need to support our business today and tomorrow.”
The Solution that IT teams have been waiting for.
Prepare to be amazed!