Happy Hunting: A New Approach to Finding Malware Cross-Correlates Threat Intelligence Feeds to Reduce Detection Time
|
Listen to post:
Getting your Trinity Audio player ready...
|
With SOC teams inundated by thousands of security alerts every day, CISOs, SOC managers and researchers need more effective means of prioritizing security alerts. Best practices have urged us to start with alerts on the most critical resources. Such an approach, though, while valid, can leave security analysts chasing after millions of alerts, many that often turn into false positives.
We at Cato Networks Research Labs recently developed a different approach for our security team that we found to be remarkably effective. Our approach uses threat intelligence (TI) feeds to automatically identify top true-positive risks with high confidence. Here’s how we did it and some of the findings we learned along the way.
Correlating Threat Intelligence Feeds to Find Top Risk Malware
Our approach starts by identifying commonalities across TI feeds. Yes, alone, that’s nothing new. Normally, security analysts will try to eliminate false positives by looking for Indicators of Compromise (IoCs) that appear in multiple TI feeds. But how many TI feeds are enough to determine that one is valid? That’s the question and one we’ve now been able to answer.
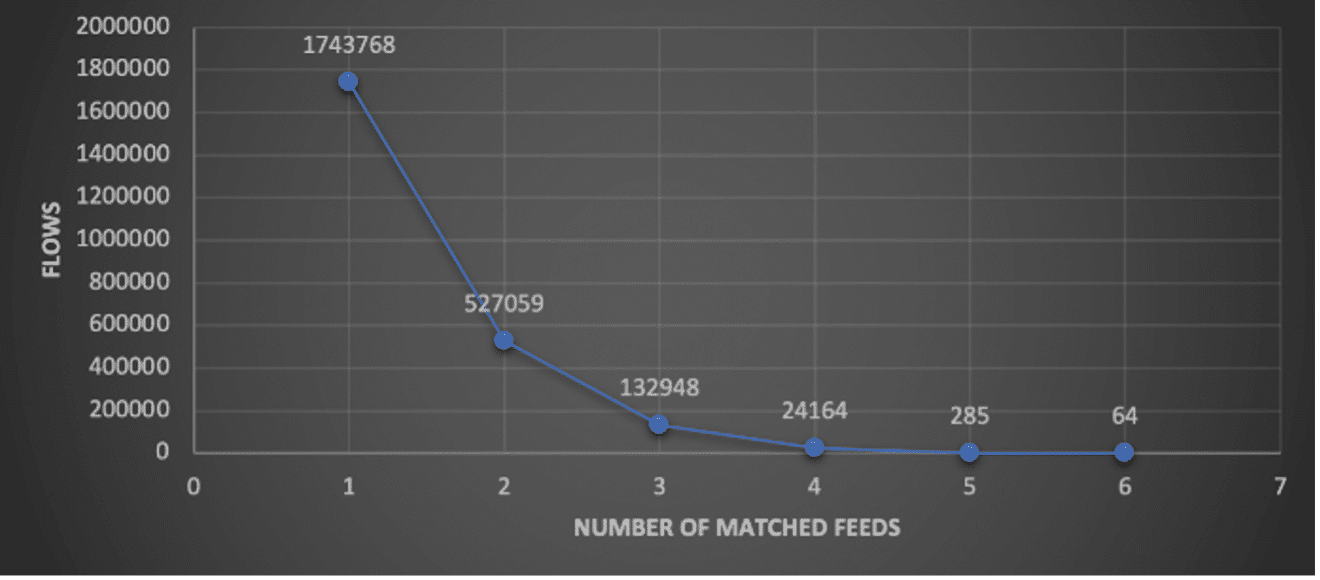
We took 525 million real network traffic flows across 45 different feeds with 1.3M malicious domain IoCs. As shown in the graph: 0.46% of the total network flows had IoCs that were hit by at least one feed.
With a simple query we cross-matched malicious domains to TI feeds. This process revealed an exponential distribution for a manageable number to evaluate, by the number of feeds (see graph). Moreover, our research identified that 66.66% of the network flows which is correlated across 5 feeds, is a malware C&C communication. For network flows that matched 6 feeds, 100% of the flows are malware C&C communication. . Bottom line, we found that while specific cases may vary (like the number of feeds, their quality etc.), IoCs identified across five feeds and more are worth investigating and would bring very good rate of malware C&C communications.
Examples of Catching Malware Faster with New Cross-Correlation Approach
Using this approach, we identified three examples of malware on our customer networks — a Worm Cryptominer, Conficker malware, and malicious Chrome extension.
PCASTLE Worm Cryptominer
The first catch is of communication with a malicious domain by PCASTLE – a Worm-Cryptominer. PCASTLE is based on Powershell and Python, infects victims by laterally moving in the network using vulnerabilities like EternalBlue, and mine cryptocurrency on the infected machines.
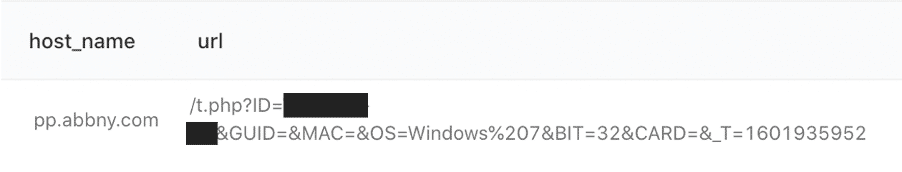
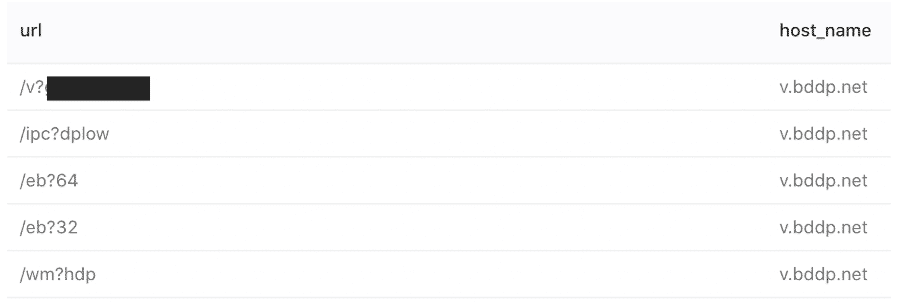
PCASTLE attempts to communicate with the pp.abbny[.]com and info.abbny[.]com domains, using the URL as the infected machine identifier and additional information:
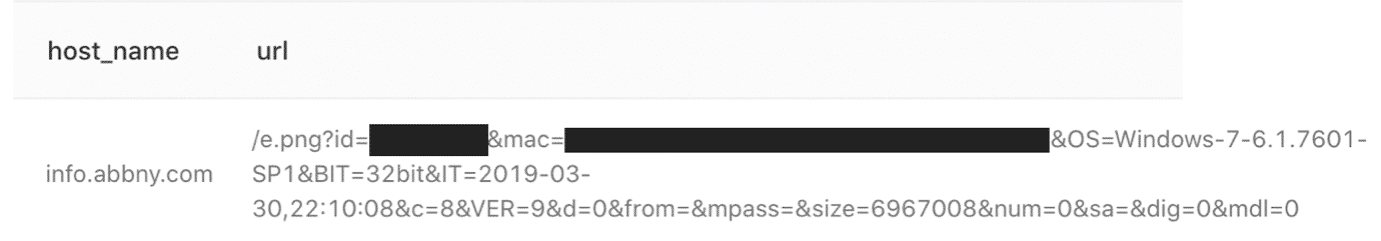
As part of this infection investigation, we could see traffic directed to download additional packages to install on the infected machine from a different domain, bddp[.]net, using different URLs:
Conficker Malware
Another fast malware discovery uncovered what seems like a newly registered domain of the famous Conficker malware. This malware exploits flaws in Windows to propagate across the network to form a botnet.
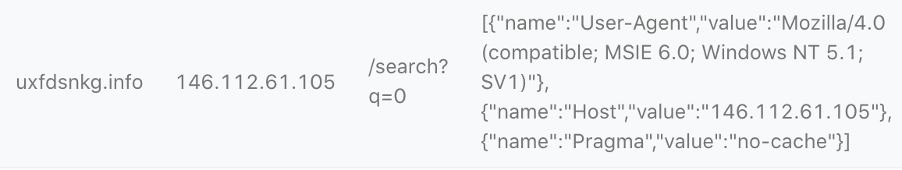
The domain uxfdsnkg[.]info, registered on the 1st October 2020, was identified on network flows of the 4th October 2020 (3 days after registered), with additional indicators (like HTTP headers and URL) which relates to Conficker malware:
Malicious Chrome Extension
Finally, we identified communication back to a C&C server at pingclock[.]net, a malicious domain identified by several TI feeds. Searching the URI parameters and domain on the web, the suspicious traffic was identified to be related to Lnkr, per this research.
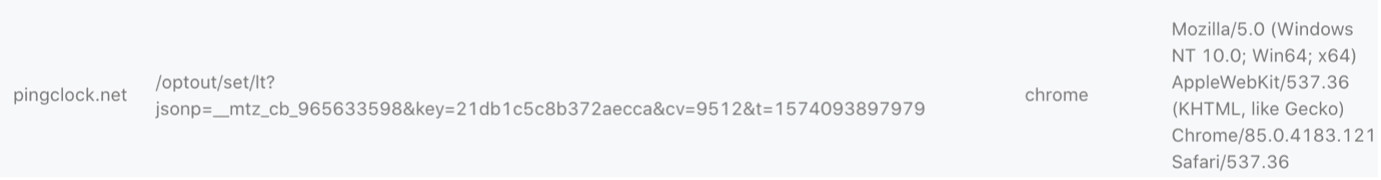
The Lnkr malware uses an installed Chrome extension to track a user’s browsing activity and overlays ads on legitimate sites. It’s a common monetizing technique on the Internet.
Prioritizing Security Alerts using TI Feeds Lowers Your Malware Hunting Risks
With this new cross-correlation approach, we automated malware hunting for prioritizing security analysis and gaining higher SOC confidence. While not every malware can be hunted using threat intelligence feeds, and not all threat intelligence alerts contain evidence of C&C communication, matched data from overlapping TI feeds is found to be a good indicator for SOC managers to focus and direct further malware analysis.
With a simple cross-matching query, SOC teams gain an important tool for high priority threat hunting of network traffic. They can evaluate and block traffic based on Threat Intelligence feeds from several different feeds. It’s highly recommended to use more than one source of Threat Intelligence to incorporate this approach in your SOC. We’d love to hear how it works for you.
SIDEBAR
IoCs To Watch Out For
Conficker C&C domain:
uxfdsnkg[.]info
LNKR Chrome Extension C&C domain:
Pingclock[.]net
PCASTLE C&C and downloader domains:
pp.abbny[.]com
info.abbny[.]com/e.png
bddp[.]net