A CISO’s Guide: Avoiding the Common Pitfalls of Zero Trust Deployments

|
Listen to post:
Getting your Trinity Audio player ready...
|
The Role of the CISO Post-Pandemic
The world has evolved and the on-going momentum of Cloud and Work-From-Anywhere (WFA) has become unstoppable. CISOs have realized their traditional security architectures, specifically VPNs, are no longer adequate to ensure only authorized users have access to critical resources.
This has made the role of CISO ever more important because we now have applications everywhere and people everywhere, leading to increased cyber threats everywhere. CISOs have an unenviable mandate: master the IT Security game to effectively map out the company’s security priorities and strategy. They must flawlessly execute on this to ensure the strongest possible security posture to protect access to critical data.
Zero Trust Is Just a Starting Point
Zero Trust has been around for more than a decade and is now top-of-mind for all CISOs. Zero Trust mandates that access to all critical corporate data be authenticated, authorized and validated before granting or maintaining access. In short, Zero Trust is a framework for building holistic security for the modern digital. Considering the attack surface continues to expand, Zero Trust is uniquely equipped to address the modern digital business architecture: WFA workers, supply chains, hybrid cloud, and evolving threats.
It must be noted that Zero Trust is not a single product solution, and CISOs would be well advised to consult the three main standards (Forrester ZTX, Gartner Carta, NIST SP-800-207) as guidance for developing their Zero Trust strategy. Of the three, NIST SP-800-207 as pictured below, is the most widely adopted framework.
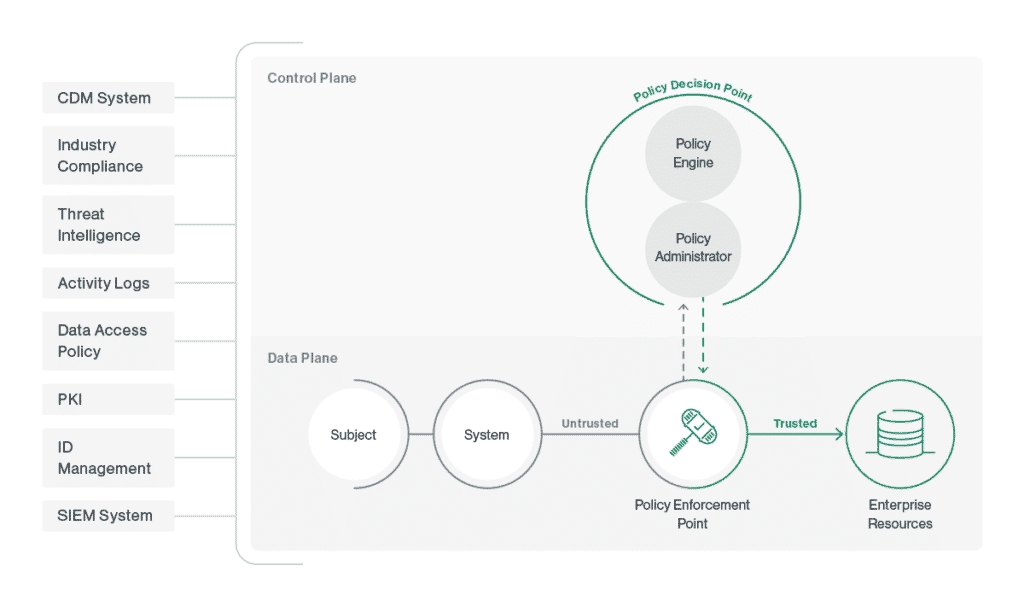
The NIST model is a discussion of 2 key functions:
- Data plane – this is the collector of data from numerous sources. These sources can be application data, user device information, user identity information, etc.
- Control plane – this is the brains of the model as this is responsible for making decisions upon what is considered good, bad, or requiring further clarification.
Together, they collaborate to determine whether to grant or deny access to critical business resources. For this to be viable, effective, and scalable, context must inform decisions to be made around access and security. As each business varies in its data flows and security concerns, this context consists of numerous data feeds, as depicted in figure 1. This includes compliance data, log data, threat intelligence feeds and user and application data captured across the network. The more context you have, the better decisions your Zero Trust deployment will make.
The 5 Most Common Pitfalls in Zero Trust Projects

Zero Trust is often misunderstood, potentially resulting in misaligned strategies that don’t meet the organization’s needs. Gartner defines Zero Trust as a ‘mindset that defines key security objectives’ while removing implicit trust in IT architectures. This implies that today’s CISOs would be well-advised to pursue their Zero Trust strategy thoughtfully, to ensure they avoid common pitfalls that impede most security initiatives.
Pitfall 1: Failing to Apply the Key Tenants of Zero Trust
Zero Trust came to life as a resolution for overly permissive access rights that created broad security risks throughout networks. The concept of implicit deny is perceived as the catch all terminology for a better security architecture, assuming it to be the fix-all for all things security. Considering this, it may be easy for CISOs to inadvertently disregard the core purpose of Zero Trust and overlook some key architectural tenants that influence Zero Trust architectures.
While each Zero Trust framework highlight several architectural attributes, for the purpose of this section, we will highlight a few that we feel should not be overlooked.
- Dynamic policy determines access to resources – dynamic polices focus on the behavioral characteristics of both the user and devices when determining whether access will be granted or denied. A subset of these characteristics can include location, device posture, data analytics and usage patterns. For example, is the user in a restricted location, or are user and device credentials being used correctly? Any of these should determine whether access should be granted and at what level.
- Continuous monitoring and evaluation – no user or device should blindly be trusted for access to network or application resources. Zero Trust dictates that the state of both the resource and the entity requesting access to be continually monitored and evaluated. Those deemed to be risky should be treated accordingly, whether it is limited access or no access.
- Segmentation & Least Privileges – Zero Trust should eliminate blind trust and by extension, blanket access to targeted resources from all employees, contractors, supply chain partners, etc. and from all locations. And when access is granted, only the minimal amount of access required to ensure productivity should be granted. This ensures the damage is limited should there be a breach of some kind.
- Context Automation – For Zero Trust to deliver the desired impact, organizations need to collect lot of data and contextualize this. This context is the key as without context, well-informed decisions for user or device access cannot be made. The more context, the better the decisions being made.
Cato SASE Cloud Approach: The Cato SASE Cloud takes a risk-based approach to Zero Trust, combining Client Connectivity & Device Posture capabilities with more holistic threat prevention techniques. Because we have full visibility of all data flows across the network, we utilize this, as well as threat intelligence feeds and user and device behavioral attributes to pre-assess all users and devices prior granting access onto the network. This in-depth level of context allows us to determine their client connectivity criteria and device suitability for network access, as well as continually monitor and assess both the user and device throughout their life on the network. Additionally, we use AI & Machine Learning algorithms to continually scan the network for indications of malware or other advanced threats and will proactively block these threats to minimize the potential damage inflicted upon the network.
The Hybrid Workforce: Planning for the New Working Reality | EBOOKPitfall 2: Treating Zero Trust a Like a Traditional VPN
When deploying Zero Trust, many organizations tend to rely on legacy security processes that are no longer applicable or select the shiny new toy that equates to a less viable solution. In 2021, Gartner noted that some organizations reported initially configuring their Zero Trust deployments to grant full access to all applications, which ironically, mirrored their VPN configuration. One of the intrinsic shortcomings of traditional VPNs, beyond the connectivity issue, is the challenge of least privilege user access to critical applications once a user has been authenticated to the network. Traditional VPNs cannot provide partial or specific access to selected applications or resources. So, deploying Zero Trust like their old VPN leaves us to wonder what problems they are truly solving, if any.
CISOs must remember that existing security architectures are based on the concept of implicit trust, which leads to unknown, yet ever-increasing risk to modern enterprise environments. The goal of Zero Trust is to ensure that users and their devices prove they can be trusted with access to critical resources. Hence, the goal for any CISO in creating a Zero Trust strategy is to reduce the risk posed by users and devices, and in the event of a successful breach, limit the spread and impact of the attack.
Cato SASE Cloud Approach: Cato Networks realizes that existing VPN architectures are too inadequate to provide the depth of access protections for critical enterprise resources. The Cato approach to Zero Trust invokes consistent policy enforcement everywhere to ensures least privilege access to all enterprise & cloud resources, while also taking a holistic approach to preventing cyber threats. We consume terabytes of data across our entire SASE Cloud backbone, and this informs how we apply additional protections once users and devices are on the network.
Pitfall 3: Not understanding the true impact on the user, IT and Security
Unfortunately for many CISOs, IT and Security departments do not always operate with aligned priorities and desired outcomes. IT departments may have critical projects they deem to have a higher priority than Security. Security teams, being tasked with strengthening the organization’s security posture may view Zero Trust as the only priority. In such cases of mis-aligned priorities, Zero Trust efforts may result in incomplete or mis-configured deployments, expanding security gaps and increasing blind spots. And let’s not forget the end user. When IT organizations finally make significant changes to networks, security, or other systems, if priorities aren’t aligned, the end results will produce adverse user outcomes.
When it comes to Zero Trust, CISOs must ensure they are mapping out the journey. In doing so, IT and Security teams should establish a “Hippocratic Oath” of “first, do no harm”. This could make it easier to map the journey to Zero Trust where the solution is simple to deploy, easy to manage, easily scales at the speed of the business, and provides positive outcomes for all parties impacted. Critical to this is the user – Zero Trust must not impede their ability to get things done.
Cato SASE Cloud Approach: At Cato Networks, our entire approach to Zero Trust is to ensure the most holistic user experience with zero impact on productivity. Often when deploying or upgrading to new security technologies, security teams will inadvertently have policy mismatches that result in inconsistent policy enforcement in certain segments of the network. Zero Trust, if not implemented correctly, increases the risk level for negative user experiences, which will reflect poorly upon the CISO and their teams. With the Cato SASE Cloud, Zero Trust & Client Access policies are applied once and enforced everywhere. This ensures specific and consistent policy treatment for all users and devices based upon identity and user and devices access criteria.
“The hallmark of Zero Trust is Simplicity“
John Kindervag
Pitfall 4: Inadequately Scoping Common Use Cases
CISOs are so inundated with everyday security concerns that identifying all possible use cases for their Zero Trust initiative, while seemingly straight-forward, could be easily overlooked. It is easy to drill down into the core requirements of Zero Trust, approaching from a broad enterprise perspective, yet neglect smaller details that might derail their project. While there are numerous use cases and each would depend on the individual organization, this document calls out (3) use cases that, if not properly planned for, will impact all non-HQ based or non-company users.
- Multi-branch facilities – It is common that today’s enterprises will comprise of a single headquarter with multiple global locations. More commonly, these global locations exist in a shared space arrangement whereby the physical network and connectivity is independent of the company. In such cases, these employees still require access to enterprise applications or other resources at the HQ or company data center. In other cases, a user may be a road warrior, using unmanaged personal devices, or be located in restricted locations. Given this, great care and consideration must be given in determining if, when and how to grant access to necessary resources while denying access or restricting actions to more sensitive resources.
- Multi-cloud environments – More enterprises are utilizing multi-cloud providers to host their applications and data. There are occasions whereby the application and data source exist in different clouds. Ideally, these cloud environments should connect directly to each other to ensure the best performance.
- Contractors and 3rd party partners – Contractors and 3rd party supply chain partners requiring access to your network and enterprise resources is very common these days. Often these entities will use unmanaged devices and/or connect from untrusted locations. Access can be granted on a limited basis, allowing these users and devices only to non-critical services.
CISOs must factor in these and other company specific use cases to ensure their Zero Trust project does not inadvertently alienate important non-company individuals.
Cato SASE Cloud Approach: At Cato Networks, we acknowledge that use cases are customer, industry, and sometimes, location dependent. And when Zero Trust is introduced, the risk of inadvertently neglecting one or more critical use cases is magnified. For this reason, we built our architecture to accommodate, not only the most common use cases, but also obscure and evolving use cases as well. The combination of our converged architecture, global private backbone, single policy management, and virtual cloud sockets ensure we provide customers with the most accommodating, yet most robust and complete Zero Trust platform possible.
Pitfall 5: Not having realistic ROI expectations
ROI, for many IT-related initiatives is rather difficult to measure, and many CISOs often find themselves twisted on how to demonstrate this to ensure company-wide acceptance. Three questions around ROI that are traditionally difficult to answer are:
- What should we expect?
- When should we expect it?
- How would we know?
Like many things technology-related, CISOs are hesitant to link security investments to financial metrics. However, delaying a Zero Trust deployment can yield increased costs, or negative ROI over time that can be measured in increased data breaches, persistent security blind spots, inappropriate access to critical resources, and misuse of user and resource privileges, just to name a few.
CISOs can address these ROI concerns through several strategies that extend beyond simple acquisition costs and into the broader operational costs. With the right strategy and solution approach, a CISO can uncover the broader strategic benefits of Zero Trust on financial performance to realize it as an ROI-enabler.
Cato SASE Cloud Approach: It is easy to appreciate the challenge of achieving ROI from Security projects. As mentioned, CISOs like CIOs are hesitant to link security investments to financial metrics. However, with an appropriate Zero Trust strategy, organizations will assure themselves enormous savings in IT effort and vendor support. Organizations deploying a Zero Trust solution based off a converged, cloud-native, global backboned SASE Cloud like Cato can expect more efficient cost structures while achieving greater performance. By converging critical security functions, including Zero Trust, into a single software stack within the Cato SASE Cloud, organizations can immediately retire expensive, non-scalable, maintenance-intensive VPN equipment. This approach delivers ease of deployment and simplistic management, while drastically reducing maintenance overhead and IT support costs.
Achieving Your Organization’s Zero Trust Goals with Cato SASE Cloud
Justifying a security transformation from implicit trust to Zero Trust is becoming easier and easier. However, determining the right approach to achieving an organization’s Zero Trust goals can be daunting. It is challenging when factoring in the broad paradigm shift in how we view user and device access, as well as numerous use case considerations with unique characteristics. Zero Trust Network Access is an identity-driven default-deny approach to security that greatly improves your security posture. Even if a malicious user compromises a network asset, ZTNA can limit the potential damage. Furthermore, the Cato SASE Cloud’s security services can establish an immediate baseline of normal network behavior, which enables a more proactive approach to network security in general and threat detection in particular. With a solid baseline, malicious behavior is easier to detect, contain, and prevent.
“The Zero Trust is a security model based on the principle of maintaining strict access controls and not trusting anyone by default; a holistic approach to network security, that incorporates a number of different principles and technologies.”
Ludmila Morozova-Buss
The Cato SASE Cloud was designed for the modern digital enterprise. Our cloud-native architecture converges security features such as Zero Trust Network Access (ZTNA), SWG, NGFW, IPS, CASB, and DLP, as well as networking services such as SD-WAN and WAN Optimization across a global private backbone with a 99.999% uptime SLA. As a result, Cato is the only vendor currently capable of delivering seamless ZTNA on a true SASE platform for optimized performance, security, and scalability.
Zero Trust is a small part of SASE. The Cato SASE Cloud controls access to critical business data in accordance with Zero Trust principles. Click here to understand more about Cato Networks’ approach to Zero Trust.