Threat actors are testing the waters with (not so) new attacks against ICS systems
|
Listen to post:
Getting your Trinity Audio player ready...
|
Earlier this week, the city of Oldsmar, FL reported a breach of their water supply system resulting in a water poisoning attempt that was luckily detected and mitigated. ICS (Industrial Control Systems) have been the target of threat actors for years now due to their remote connectivity needs combined with the lack of security monitoring, detection and management controls modern IT infrastructures utilize. Such “low risk, high reward” targets will continue to draw adversarial attention, and unfortunately, it is not hard to find these vulnerable critical infrastructure systems.
“I told you this would happen!” While some people take joy in pointing out they were right (siblings and parents come to mind first), this sentence is said in disappointment and sadness when it comes from most cybersecurity experts. It points to a failure, an educational, procedural, or technological one —it doesn’t matter. The press conference held by the city officials of Oldsmar confirmed an attack cyber security experts have been discussing and demoing for years now – a remote access to an ICS that could result in the loss of life. City officials assured reporters that there are redundancies in place that would have prevented this attack from materializing, but the threat is clear.
Let’s start with some cold, hard facts: Operating and managing an ICS (and SCADA systems even more so) is hard work. As with any business – there are financial constraints, talent shortage, regulations and more. Add to that mix remote locations of systems and software and hardware that may be older than some of its operators and you get a volatile mix. Some of the tasks enterprises perform each week are mind boggling for me when it comes to ICS. Just thinking of how one would patch operating systems at an active working oil refinery or deploy a new security policy on a remote gas line makes me sweat. Some of these systems were designed and deployed well before any Internet connectivity was an option. Since then, the need for easy management grew and remote administration tools, usually in the form of VNC (Virtual Network Connection) and RDP (Remote Desktop Protocol) (which is based on RFB – Remote Framebuffer), have been deployed. This was also the case at Oldsmar, where TeamViewer was used for remote control of the water supply systems.
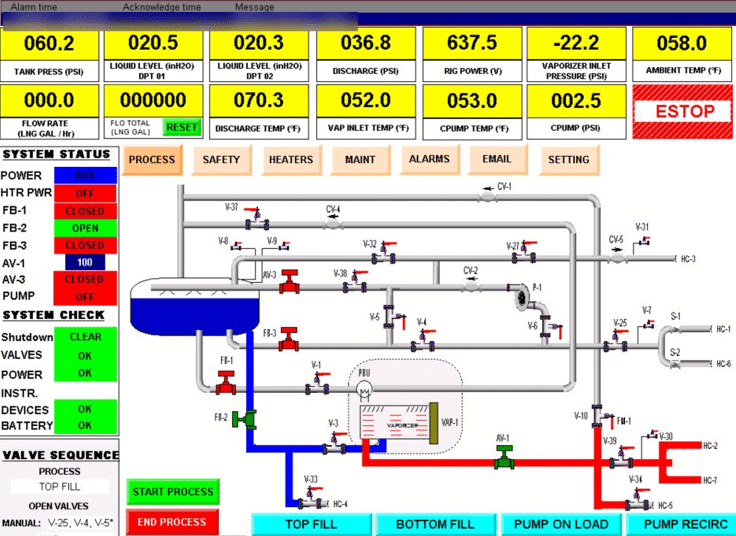
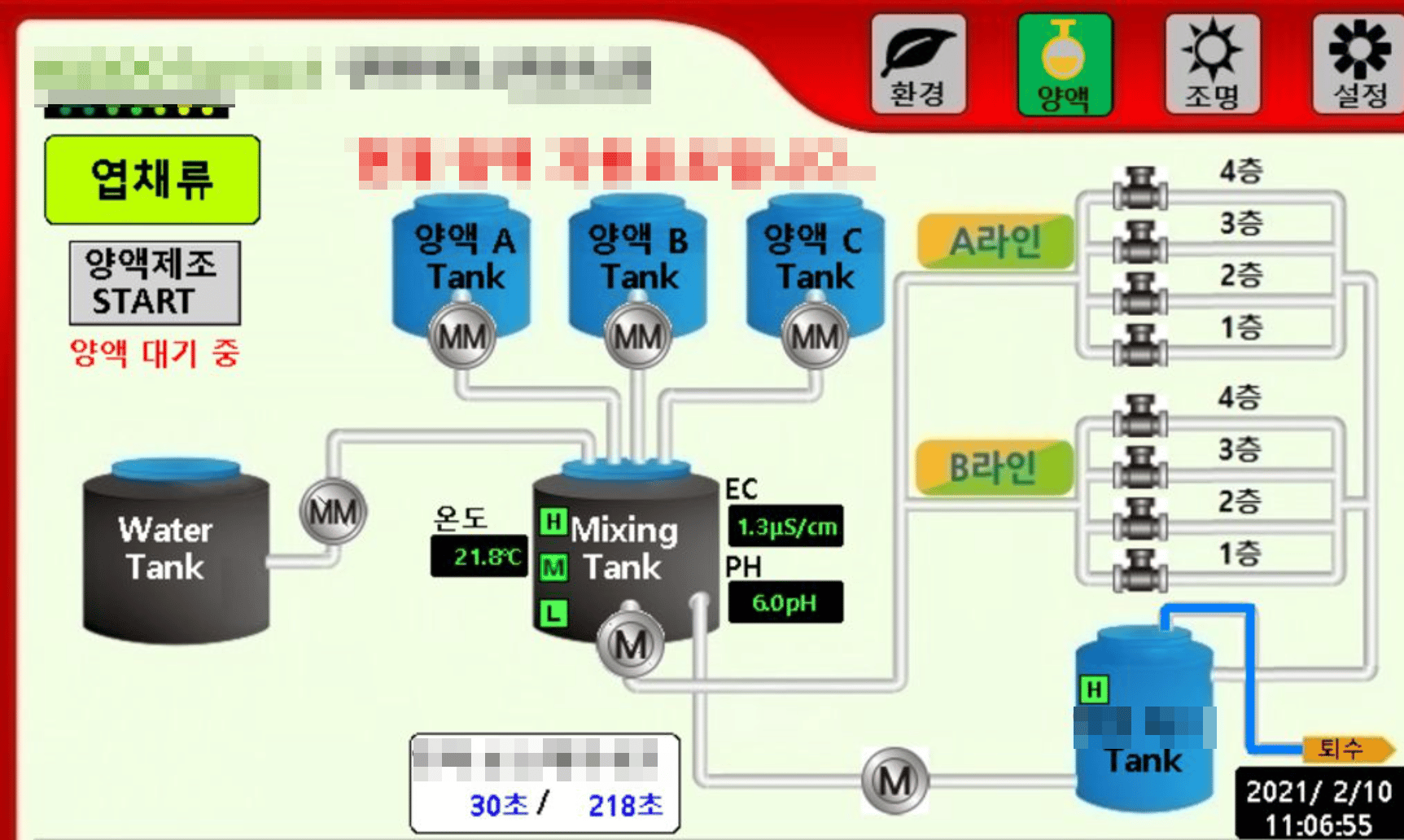
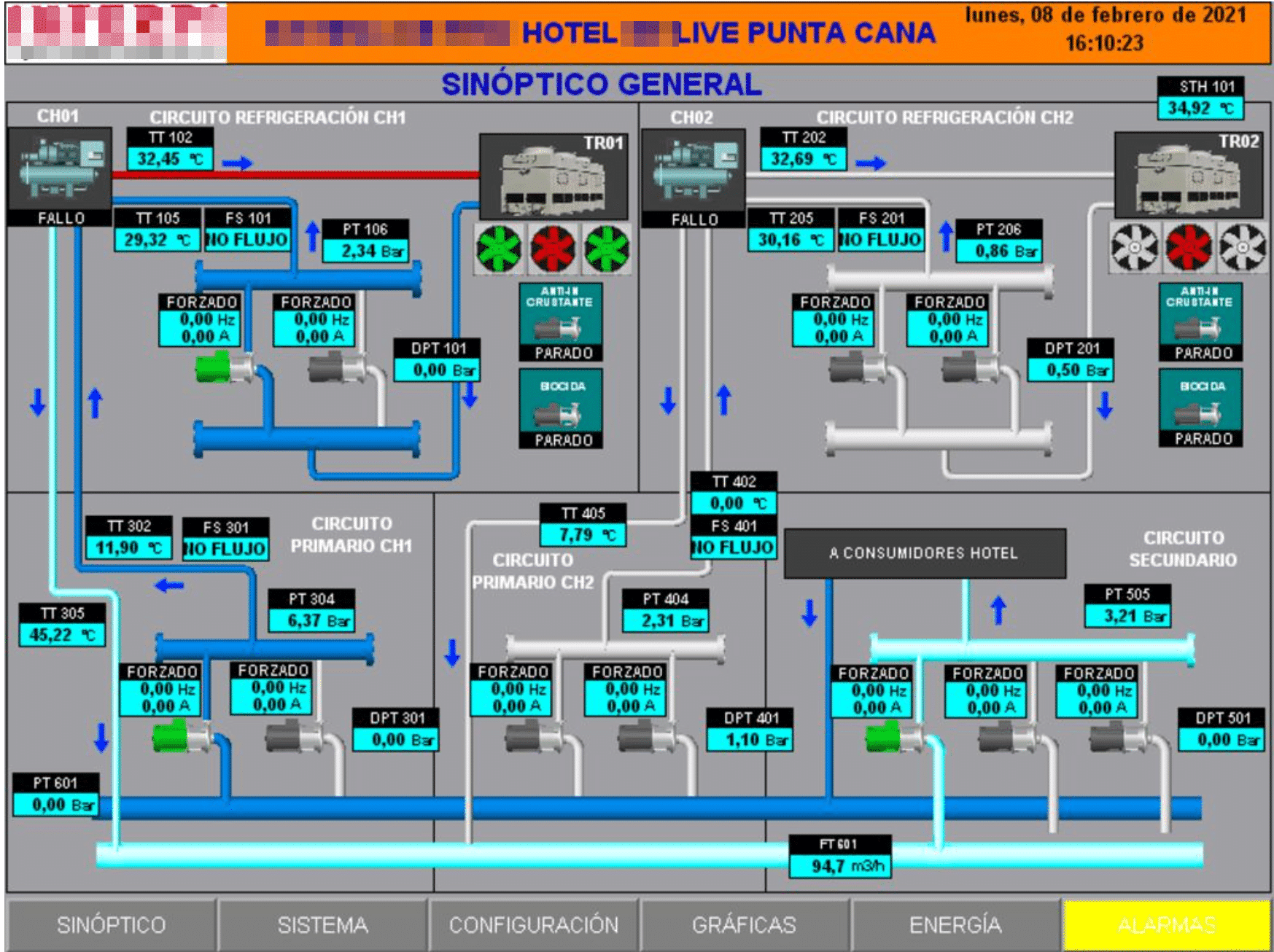
Gaining unauthorized access to resources simply by finding them exposed online, was popularized in 2005 by Johnny Long at DEFCON’s “Google Hacking for Penetration Testers.”. Since then new tools and services have been made publicly accessible. One such tool is Shodan. Shodan allows users to search for specific devices and services using a GUI and an easy querying language. For example, if a certain facility wishes to use RFB (Remote Framebuffer) for remote administration of systems but has failed to secure that access, the facility can be easily found on Shodan and other similar services. Below are just three screenshots of such systems that can currently be found on Shodan. These are just screenshots of what is currently displayed on the system’s screen, but simply pointing software that supports RFB to their IP will give anyone control over it (Needless to say, this would be deemed an unauthorized access attempt and is a punishable felony. Simply put – don’t do it).
Industrial control systems for various facilities:
Unfortunately, many of these systems have minimal, if any, security monitoring, detection and response software and services. With a growing need for remote administration, be it due to the pandemic or due to the distance between the operator and the system, more and more ICS systems become available for anyone who knows how to search for them. Such facilities may be forced to rethink remote access, not just in how to deploy and use it but also in how to monitor and alert on suspicious activities as you would with any IT infrastructure. Lives may literally depend on it.




