Cato SWG (Secure Web Gateway) enhances security by providing an additional layer of protection from Internet threats, enforcing corporate standards for web site access based on their content and risk categorizations.
Cato SWG provides instant value with ready-to-use policies that align with internet security best practices. Once enabled, the policies are immediately and uniformly enforced on the entire enterprise. Cato SWG also includes 80+ categories of web site classifications that enable admins to easily adhere to enterprise compliance requirements that govern access to sensitive or inappropriate content. As needed, policies can be refined using granular attributes such as user identity, location and device posture. And, for each policy, the admin can choose the desired action such as Allow, Block and Prompt.
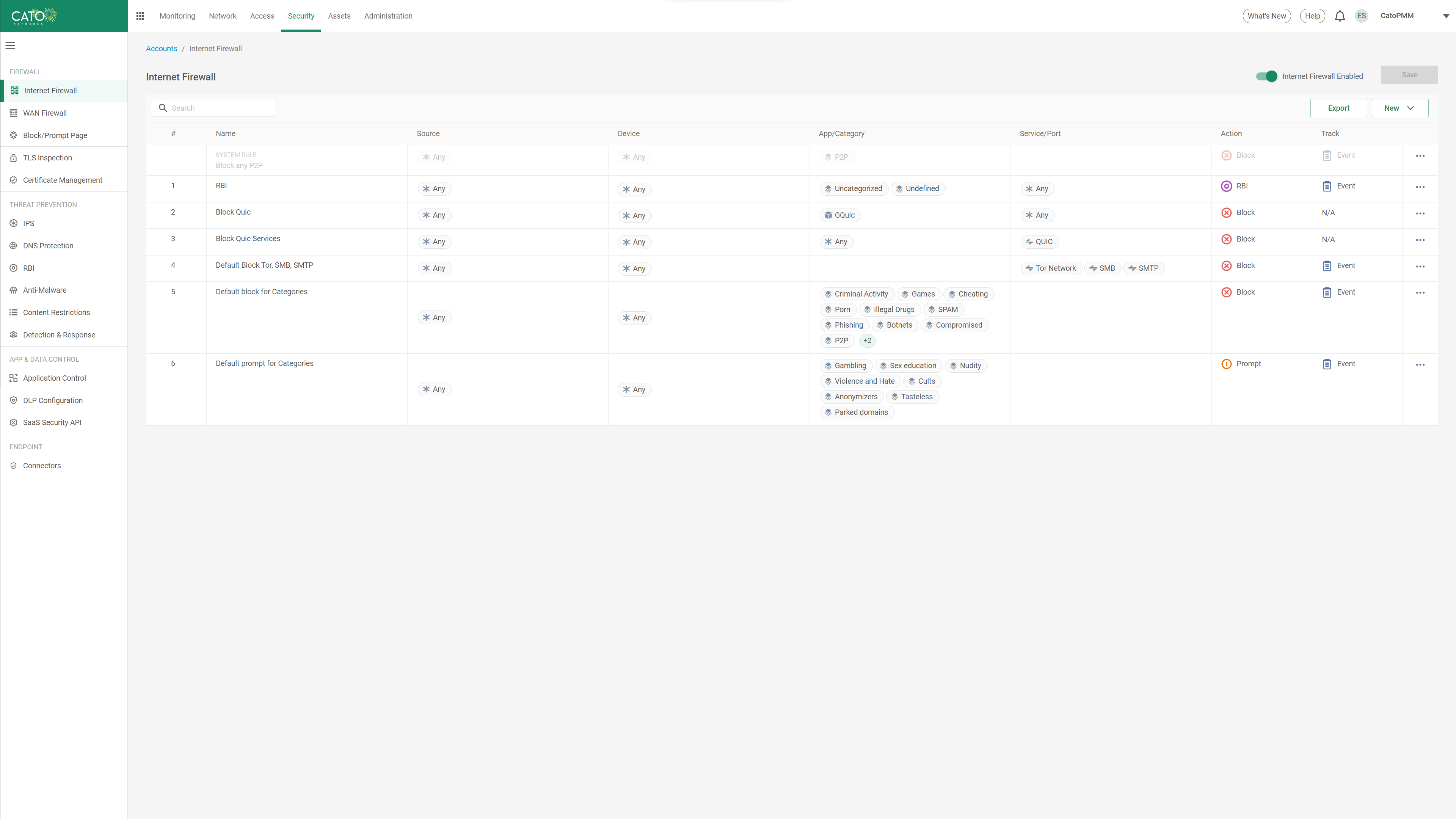
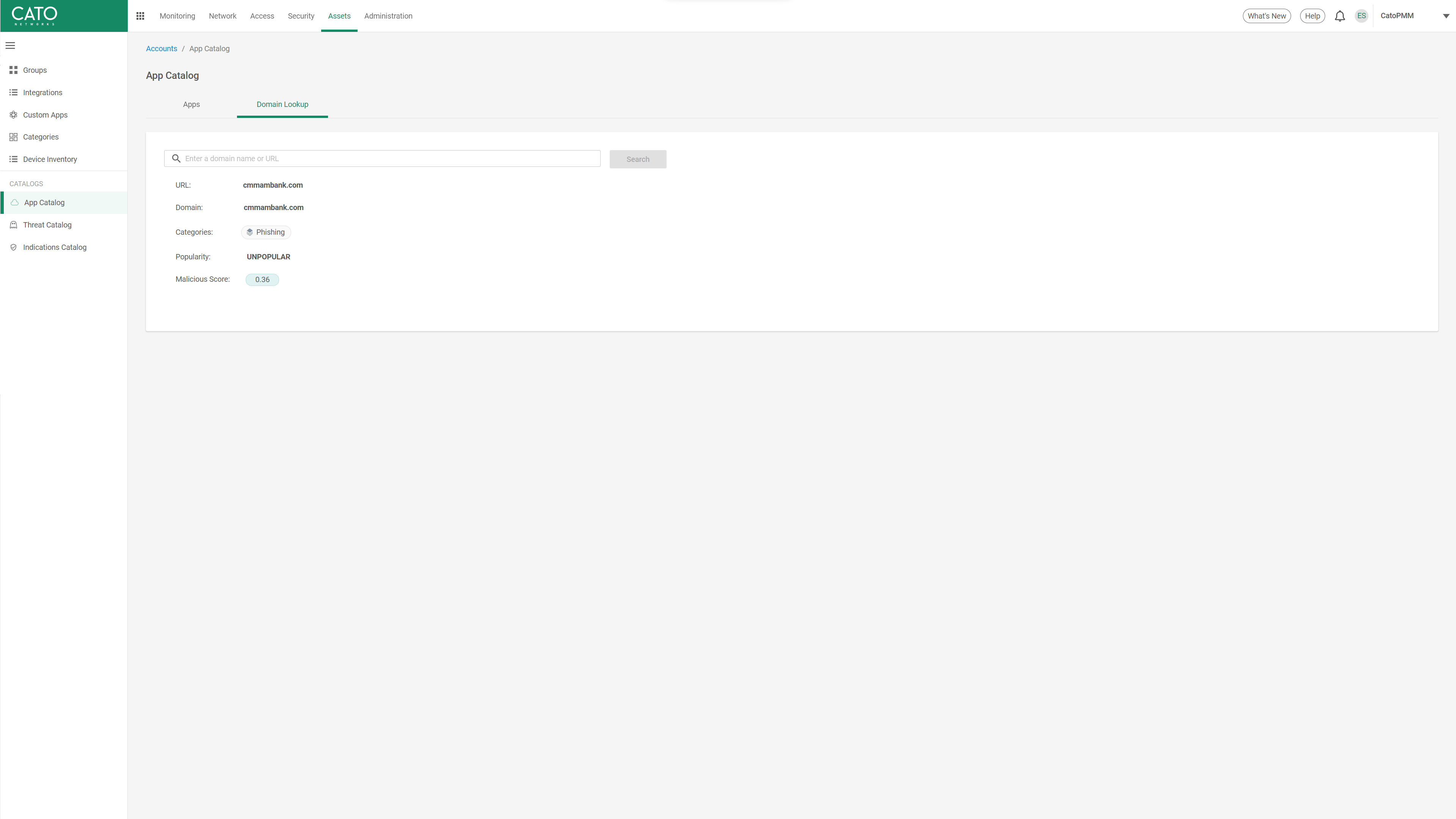
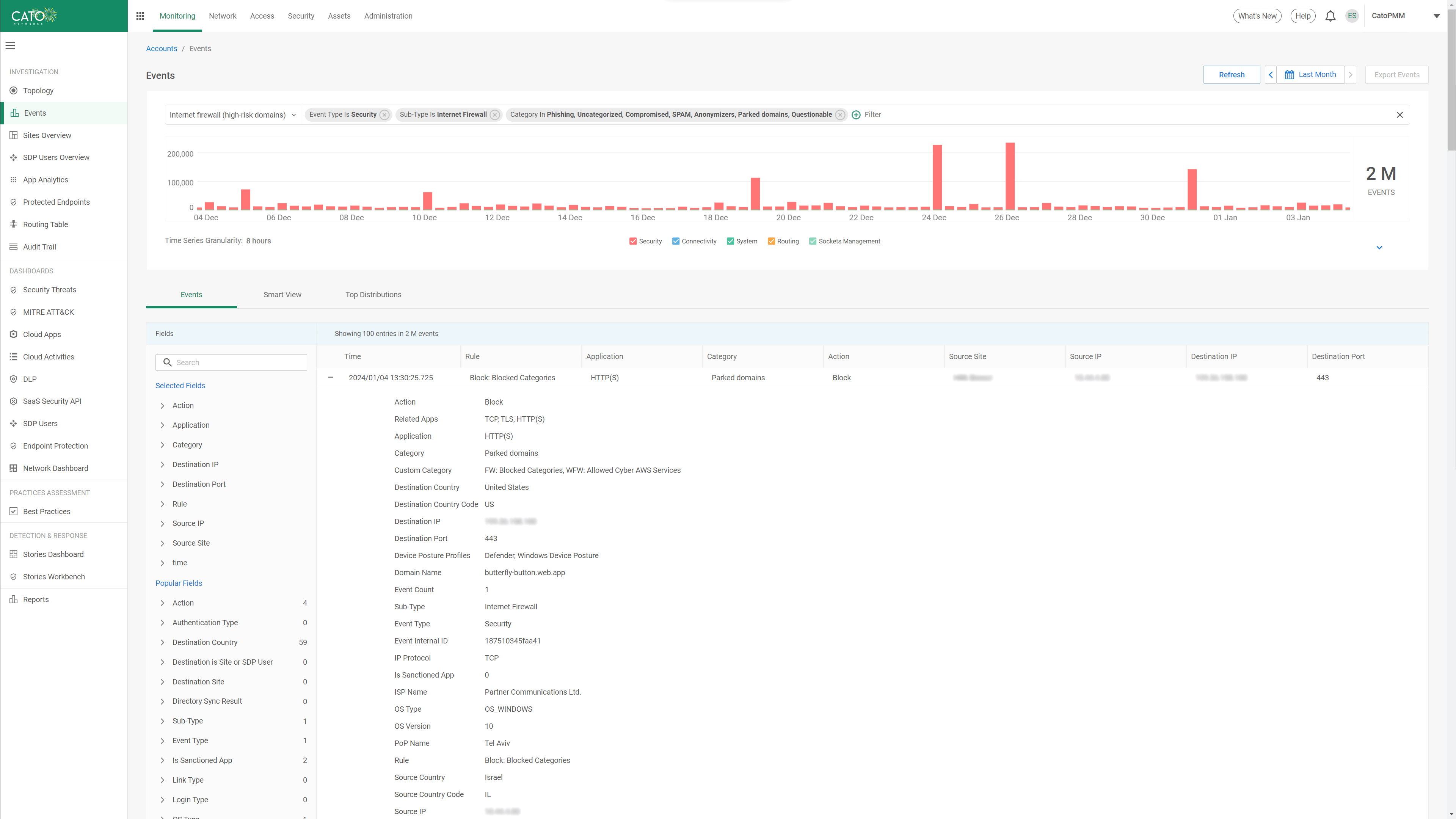
Blocking malicious, compromised, phishing, and parked domain categories reduces the overall exposure of users to web-borne threats. Cato maintains the up-to-date blacklist of malicious domains across a constantly changing domain landscape to ensure optimal security posture. Access attempts to malicious sites can be logged for record keeping, further analysis, prioritization of security training and identification of repeating offenders.
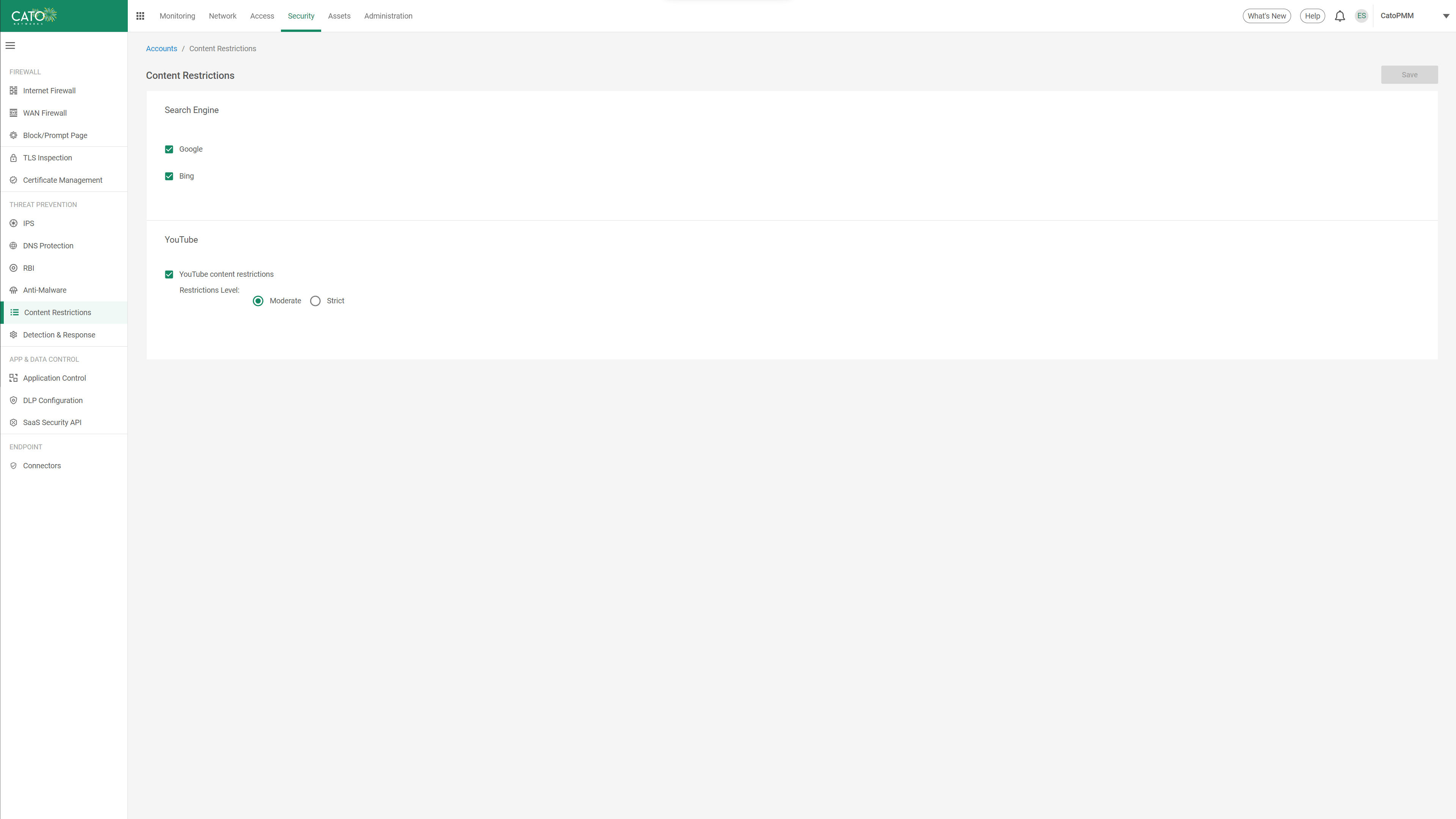
Search engines often allow users to view images and preview video content without having to leave the search engine’s domain, thus bypassing organizational compliance policies. Cato’s SWG allows admins to enforce Safe Search for popular search engines as well as content restrictions for YouTube, preventing circumvention of policy by users. This capability can be enabled in just a few clicks, providing increased protection for all users and locations with minimal effort.
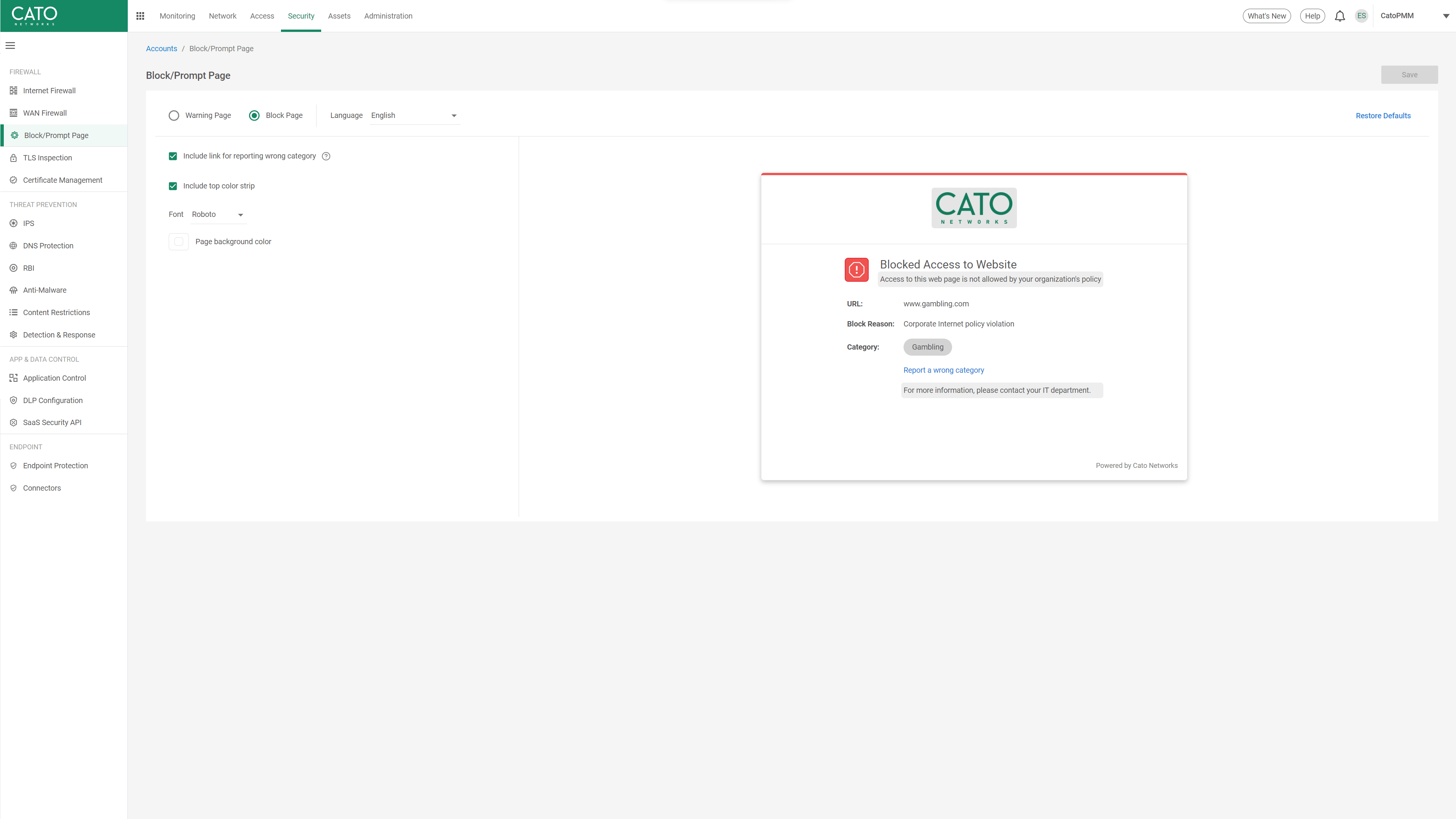
Cato SWG provides clear notification to users when they are prevented or delayed from accessing a website and allows them to request an exception or report an error. Administrators can fully customize Cato’s block and prompt pages to incorporate the enterprise brand and specific notification text provided to users including IT contact information and the process for re-categorization requests.
All event data is automatically retained and normalized into Cato’s Data Lake and can be queried using a built-in events engine with SIEM-like functionality. Administrators can select from a variety of pre-defined queries that cover common use cases or quickly build custom queries by selecting the desired filters. PDF reports can also be generated providing an easy to document for auditing or executive visibility purposes.
Customers use Cato to eliminate complex legacy architectures comprised of multiple security point solutions and costly network services. Cato’s unique SASE platform consistently and autonomously delivers secure and optimized application access everywhere and to everyone.
Cato Networks named a Leader in the 2025 Gartner® Magic Quadrant™ for SASE Platforms. Again.
Cato Networks Named a Leader and an Outperformer in the GigaOm 2025 SASE Radar
Cato Networks recognized as a Growth and Innovation Leader in SASE
Cato Networks Recognized as Global SSE Product Leader
WAN Transformation with SD-WAN: Establishing a Mature Foundation for SASE Success


“We ran a breach-and-attack simulator on Cato, Infection rates and lateral movement just dropped while detection rates soared. These were key factors in trusting Cato security.”
The Solution that IT teams have been waiting for.
Prepare to be amazed!