- SD-WAN: What is Software-Defined WAN?
- The Evolution of SD-WAN
- Top 5 SD-WAN benefits explained
- SD-WAN vs. MPLS: Which Is Right for You?
- MPLS Alternative
- SD-WAN redundancy vs MPLS redundancy
- SD-WAN vs VPN: How Do They Compare?
- SD-WAN security
- How to connect multiple offices
- SD-WAS as a service
- Last Mile Constraints
- A History of SD-WAN
- Gartner’s 9 Criteria For SD-WAN Selection
- What SD-WAN Vendors Won’t Tell You About SD-WAN
- Azure SD-WAN: Cloud Datacenter Integration with Cato Networks
- SD-WAN Use Cases and Success Stories
- The Return On Investment of SD-WAN
What Is SD-WAN?
The Meaning of SD-WAN
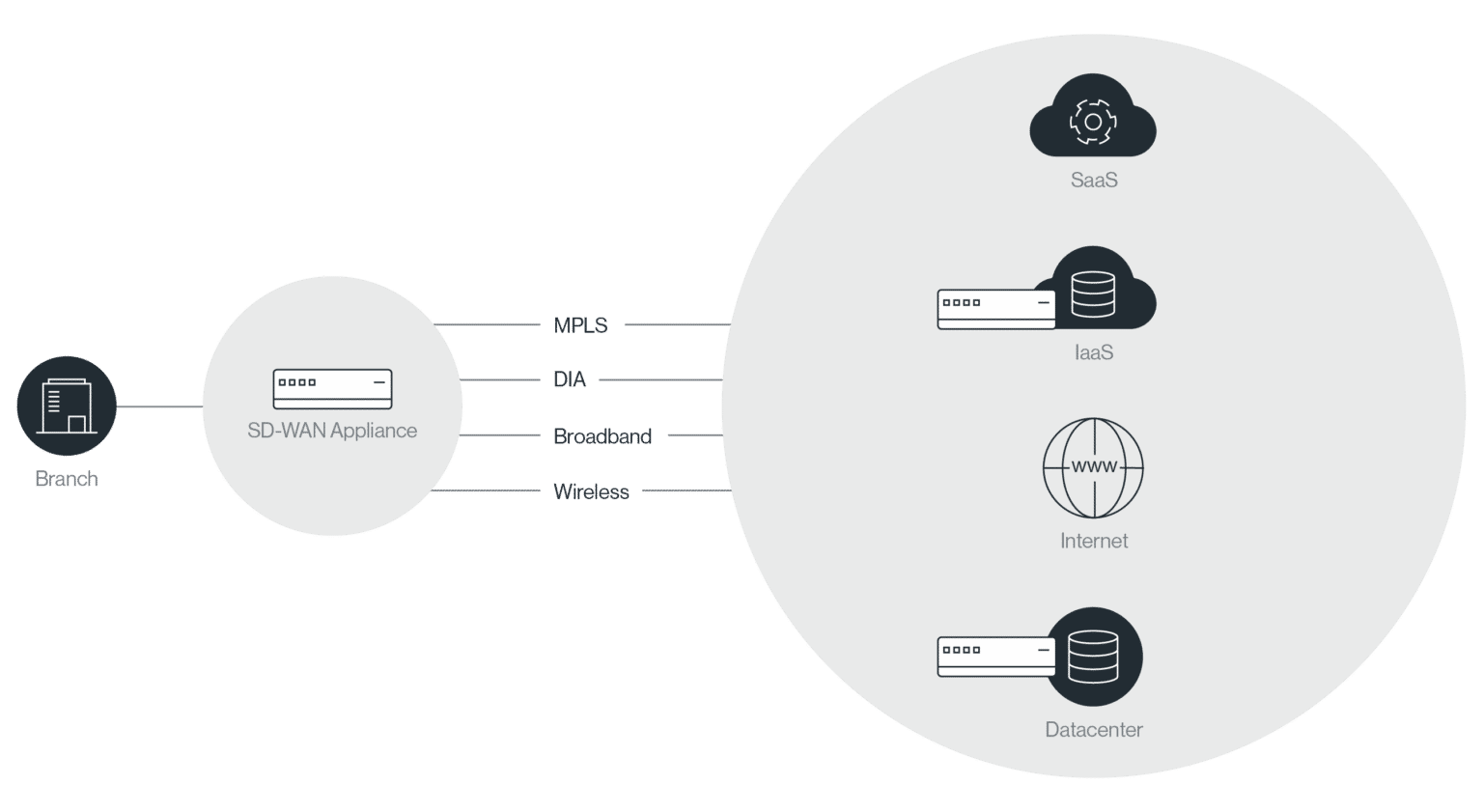
Software-Defined Wide-Area-Network (SD-WAN) is defined as a virtual WAN architecture that allows enterprises to securely and efficiently connect users to applications. This technology solution brings unparalleled agility and cost savings to networking. With SD-WAN, organizations can deliver more responsive, more predictable applications at lower cost in less time than the managed MPLS services traditionally used by the enterprise. IT becomes far more agile, deploying sites in minutes; leveraging any available data service such as MPLS, dedicated Internet access (DIA), broadband or wireless; being able to reconfigure sites instantly; and more easily supporting migration to hybrid cloud.
SD-WAN does this by separating applications from the underlying network services with a policy-based, virtual overlay. This overlay monitors the real-time performance characteristics of the underlying networks and selects the optimum network for each application based on configuration policies.
How does SD-WAN Work?
Software-defined WAN (SD-WAN) is designed to solve many of the challenges associated with traditional WAN design. SD-WAN abstracts away the details of the networking layer, allowing the WAN to use a variety of different connection types interchangeably, including LTE, MPLS, and broadband Internet. This abstraction can improve network redundancy, bandwidth, and performance and enables centralized management and orchestration.
SD-WAN works by creating a network of SD-WAN appliances connected by encrypted tunnels. Each site on the WAN has its own SD-WAN appliance, and all traffic flows through that appliance. Since all appliances are centrally managed, consistent networking policies can be enforced throughout the organization. When traffic enters an SD-WAN appliance, the appliance determines the type of application traffic and routes it to its destination based upon existing policies and the availability and performance of different network links.
Traditional SD-WAN is hardly perfect. Many SD-WANs do not include integrated security, so each branch location must deploy its own standalone security products. SD-WAN also includes the deployment of an SD-WAN appliance at each endpoint, which makes it difficult or impossible to use it for cloud and mobile traffic. Finally, SD-WAN often relies upon public Internet, which can cause reliability concerns. However, many of these problems are solved with secure access service edge (SASE) platforms.
What Problems Does SD-WAN Solve?
The cloud and high levels of mobility characterize how people use networks today. WANs, however, was designed in an era in which the focus was on linking physical locations. Using the old approach to support the new needs results in expensive global connectivity, complex topologies and widely dispersed “point products” that are difficult to maintain and secure.
The unending and cumbersome cycle of patching, updating, and upgrading requires skilled techs, an increasingly scarce commodity. That’s especially distressing because all this complexity is an inviting target for hackers, who can exploit misconfigurations, software vulnerabilities, and other attack surfaces.
There are several reasons that legacy WANs no longer are up to the job. MPLS, the focal point of the old approach, is expensive and requires long lead times for deployment to new locations. Legacy WANs only touch the Internet at secure Web portals, usually at the data center. This leads to the “trombone” effect of sending Web data back and forth across networks. The result is added latency and exhaustion of the supply of MPLS links as Internet traffic increase. Direct Internet access, which would link branch offices to the Internet, is expensive and could overwhelm rudimentary branch hardware. Finally, the WAN was designed when the emphasis was on linking physical assets such as offices and data centers. This approach isn’t ideal for this new and varied world.
The Evolution of SD-WAN
SD-WAN 1.0: Hungry for bandwidth
The first stage of SD-WAN evolution was focused on solving the issues of availability and last-mile bandwidth. New MPLS links are expensive and slow to provision, and the use of an Internet backup meant that the backup was only used in the case of an outage. Using link-bonding, an SD-WAN predecessor could combine multiple different types of connections at the link level, improving last-mile bandwidth.
SD-WAN 2.0: The rise of SD-WAN startups
The limitation of link bonding is that it only improved last-mile performance. Achieving improved performance throughout the WAN required routing awareness throughout the path. Early SD-WAN solutions offered virtualization failover/failback and application-aware routing. With application-aware routing, SD-WAN could move away from being fully reliant on MPLS links and optimally route traffic based upon the application type.
SD-WAN 3.0: Reaching out
The latest stage of SD-WAN evolution focuses on going beyond networking branch locations. As organizations increasingly move resources to the cloud, SD-WAN provides a solution for securely connecting these cloud deployments to the enterprise WAN.
Top 5 SD-WAN benefits explained
Designed to provide an alternative to traditional MPLS-based WAN, Software-defined WAN (SD-WAN) provides organizations with five major benefits when compared to MPLS.
1. Reduced WAN costs
MPLS bandwidth is expensive, and it can take weeks or months to provision a new MPLS link, compared to days with SD-WAN. Both in cost of operation and in lost business opportunity, MPLS is inferior to SD-WAN.
2. Enhanced WAN performance
MPLS is very effective at routing traffic between two static locations, but the growth of the cloud makes this less useful to businesses. SD-WAN’s policy-based routing allows traffic to be optimally sent through the network based upon the needs of the underlying application.
3. Improved WAN agility
SD-WAN also provides much more agile networking than MPLS. With SD-WAN, the network layer is abstracted away, allowing the use of a variety of different transport mechanisms throughout the WAN.
4. Simplified WAN management
With MPLS, an organization may need to deploy a variety of standalone appliances to manage WAN optimization and security. With SD-WAN, these operations can be centralized, allowing organizations to scalably manage growing networks.
5. Increased WAN availability
Finally, SD-WAN can provide dramatic redundancy and availability improvements over MPLS. With MPLS, adding redundant links can be expensive. SD-WAN, on the other hand, can route traffic over a different transport mechanism in the case of an outage.
SD-WAN vs. MPLS: The Pros and Cons?
As global organizations become more common, the need to connect geographically-distributed LANs via a WAN becomes extremely important. In order to compete effectively, organizations need access to stable, high-performance WAN at an affordable price. Three options exist for providing this: the public Internet, MPLS, and software-defined WAN (SD-WAN).
The first option for an enterprise is to route internal traffic over the public Internet. The two primary advantages of this approach are quick setup and relatively low costs since broadband Internet is widely accessible and typically affordable. However, these advantages come at the cost of unstable performance, volatile latency, and a lack of end-to-end management.
MPLS is designed to provide high-performance and reliable network connections backed by SLAs guaranteeing latency, packet delivery, and availability. However, these high-performance connections are expensive and extremely slow to deploy (taking weeks or months). MPLS connections are also ill-suited to cloud computing since traffic must be pulled back to a centralized access point before being sent out to its destination.
SD-WAN provides the best of both worlds by abstracting away the details of the network infrastructure. By choosing the optimal route from a collection of public Internet connections and MPLS links, SD-WAN can balance performance and cost on a per-application basis. Cloud-based SD-WAN provides additional benefits, including integrated security, support for mobile and cloud users, and predictable latency and packet loss.
MPLS Alternative
MPLS offers reliable network connectivity with the highest SLA for availability, packet loss, and latency. However, this technology also has significant limitations. The benefits of MPLS come with a high price tag, and new MPLS circuits can take weeks or months to deploy, limiting an organization’s ability to connect branch locations or accommodate growing bandwidth requirements.
Software-defined WAN (SD-WAN) is an MPLS alternative that uses multiple transports to connect a network of SD-WAN appliances. By abstracting away the network layer and optimally routing traffic over available links, it provides high-performance, reliable connectivity that is flexible and affordable.
However, SD-WAN is not a perfect solution. It relies on the unpredictable internet, so MPLS links may still be needed, and, often, SD-WAN lacks built-in security. SASE-based SD-WAN is necessary to overcome these issues and to also seamlessly connect remote users and clouds.
SD-WAN Redundancy vs MPLS Redundancy
Enterprise WAN requires redundancy to minimize network outages, a leading cause of downtime. Software-defined WAN (SD-WAN) is a leading MPLS alternative but must be implemented properly to ensure reliability and redundancy.
MPLS is known for its high reliability, but redundancy with MPLS is often prohibitively expensive. As a result, disruptions to MPLS connectivity can cause downtime.
SD-WAN relies on link redundancy for SLA. It abstracts away the network layer and optimally routes traffic over the available transport. With real-time availability and performance monitoring, SD-WAN can seamlessly adapt to use alternative connections in the event of a link failure. As a result, SD-WAN provides a viable alternative to MPLS.
SD-WAN vs VPN: How Do They Compare?
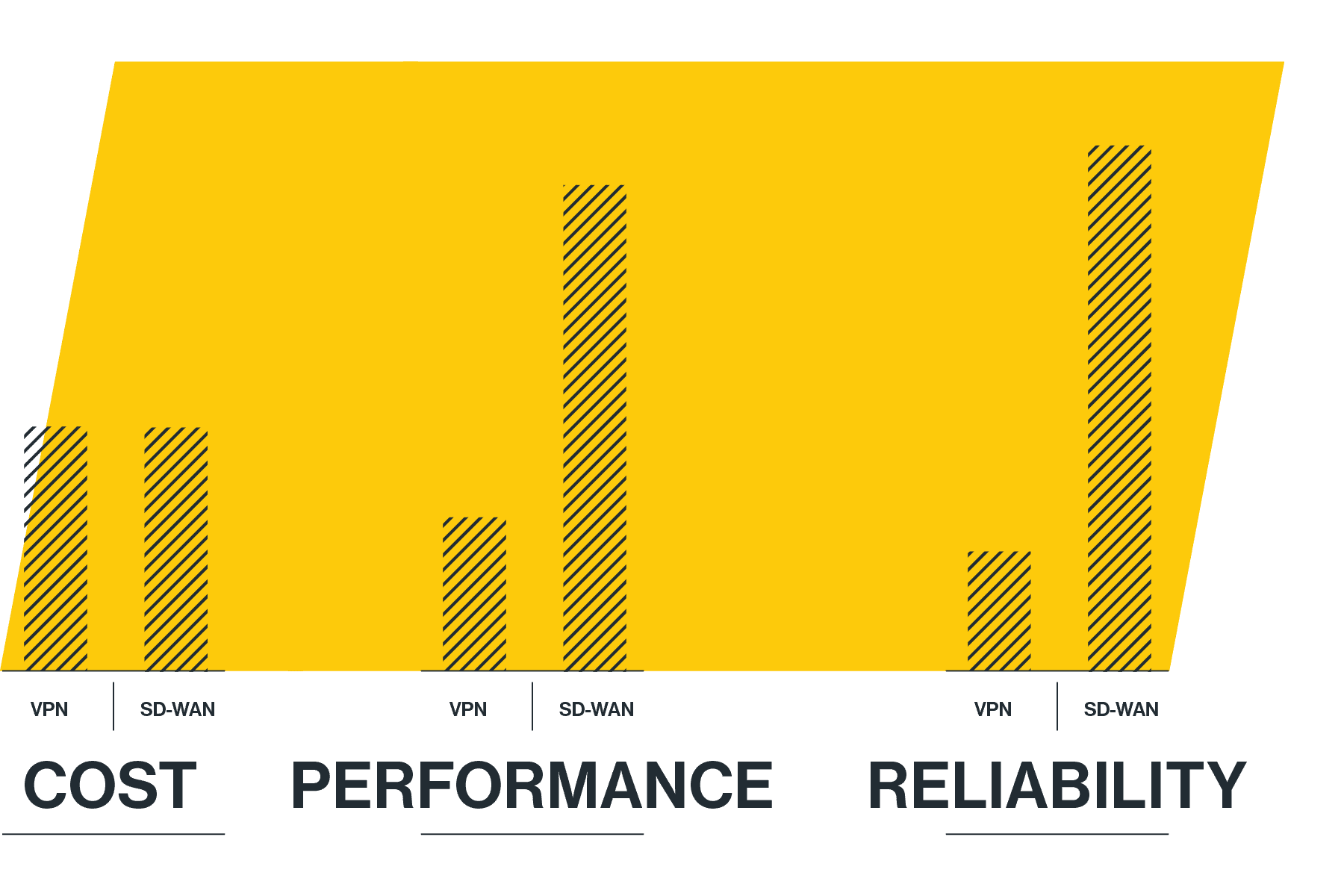
Internet-based VPNs and cloud-based software-defined WAN (SD-WAN) are two options for an enterprise WAN, both offering much lower cost and higher flexibility than MPLS. In the SD-WAN vs VPN comparison, cost, performance, reliability, and configuration & maintenance are important factors to consider.
The costs associated with the enterprise WAN boil down to the costs associated with acquiring the necessary hardware or software and the costs of deploying, configuring, maintaining, and monitoring it. Acquiring SD-WAN hardware incurs some costs, but the costs of operating and maintaining it are relatively low. With VPN, software can be cheap or even free, but the complexity of maintaining a VPN-based WAN can be significant.
The performance of a VPN is limited by the public Internet that it runs on, which can create significant latency for long-distance connections. A cloud-based SD-WAN running over a private backbone, on the other hand, has high performance regardless of connection distance. The reliance of VPNs upon the public Internet also hurt them in terms of reliability, where links can go down unexpectedly. An SLA-backed cloud-based SD-WAN running on Tier-1 private links has much higher reliability.
Finally, VPN-based WANs can have significant configuration and maintenance costs due to the complexity of creating different encrypted tunnels for each point-to-point connection. These connections also lack centralized visibility and monitoring, making them more complex to secure. A cloud-based SD-WAN can be easily deployed to a site and is centrally managed, minimizing configuration and maintenance costs.
SD-WAN vs. SDN: What is the Difference?
SD-WANs implement software-defined networking (SDN) principles to connect locations. SDNs first were introduced in the data center with the goal of increasing network by separating the data plane from the control plane. The policies and routing intelligence would run in one or more servers (“controllers”), which would instruct the networking elements forwarding the packets (switches and routers).
SDN created an overlay across the local network, opening up a world of possibilities in efficiency and agility. SD-WAN creates an overlay across the wide-area network also bringing incredible efficiency and agility gains.
How Does SD-WAN Improve Security?
MPLS and appliance-based software-defined WAN (SD-WAN) can both provide an organization with the networking capabilities needed for a WAN. However, they often have significant security shortcomings. MPLS lacks any encryption of its circuits, and both MPLS and appliance-based SD-WAN may have no built-in security. As a result, many organizations using these systems deploy standalone security appliances at each location to provide the necessary cybersecurity protections.
However, this approach to WAN security can be complex, unscalable, and expensive since each new location requires another set of security appliances. Each of these appliances must be individually purchased, configured, monitored, and managed, which creates significant costs throughout their lifetimes. This approach also does not work for the cloud and mobile, where security appliances cannot be deployed on-site.
Cloud-based SD-WAN provides a solution to this problem. By placing points-of-presence (PoPs) in the cloud, they can achieve global coverage, allowing users to connect via a nearby PoP and use the SD-WAN with minimal latency impacts. These PoPs can also have integrated security functionality, removing the need to deploy standalone appliances at each location and enabling centralized networking and security visibility across the enterprise WAN. Networking and security integration can also improve performance since networking and security appliances can be optimized to interoperate with one another.
What are the Limitations of SD-WANs?
SD-WAN brings significant benefits but also some challenges. For example, SD-WAN deployments in the cloud require virtual appliances in each cloud instance, and SD-WAN does not support mobile users.
SD-WAN also creates challenges for securing branch locations. Branches with access to the public Internet are at risk of various threats, and protecting against these threats can create significant costs associated with purchasing, sizing, maintaining, and scaling firewalls and UTMs alongside the SD-WAN. When using separate solutions for security and networking, troubleshooting becomes harder due to the need to work with separate network and security consoles.
How Do SASE-based SD-WAN Address Those Challenges?
SD-WAN, as part of SASE, addresses these issues by converging security and networking functions in cloud-native software running on the SASE provider’s points of presence (PoPs). These PoPs, which are connected by a dedicated private global backbone, also provide superior network performance compared to the public Internet.
This approach alleviates the branch offices’ challenges of running both networking and security stacks by creating a “thin edge”. These SASE SD-WAN devices primarily route traffic to the SASE cloud, where security inspection can be performed at line speed regardless of volume or enabled features.
What are SD-WAN Managed Services?
Some SD-WAN providers offer to manage SD-WAN deployments for their customers. A SASE-based SD-WAN would usually offer several management options: self-management, co-management, and full management. Customers should choose the option which suits their needs best, and keep the ability to transition between options if needed in the future.
How to Connect Multiple Offices?
WAN connections to branch offices must be secure, reliable, affordable, and offer enterprise-level network performance. Many available WAN solutions have their issues.
IP-VPNs that route traffic over the public Internet are a common solution for the corporate WAN. However, these solutions can be difficult to configure, offer limited or no support for remote users, and cannot provide the network performance and reliability guarantees that the enterprise needs.
MPLS offers better reliability and simplicity than IP-VPNs but is expensive and takes a longer time to deploy. MPLS also lacks cloud and remote work support and offers no built-in security.
SASE-based SD-WAN offers a superior branch networking solution. Cloud-based points-of-presence (PoPs) connected by dedicated tier-1 network links offer SLA-backed high-performance, reliable, and affordable networking. These PoPs are also accessible from anywhere and include a full and converged security stack.
What is SD-WAN as a Service?
SD-WAN as a Service extends the core capabilities of traditional SD-WAN. It converges the WAN edge, a global backbone and a full network security stack into a unified cloud-native platform. Known as SASE (or the Secure Access Service Edge) it is built to optimally connect and secure all enterprise resources; physical locations, cloud datacenters, and the mobile workforce. By integrating SD-WAN into SASE, enterprises can gradually transform their WAN to address the full WAN transformation journey, without deploying multiple point solutions.
What Are MPLS and SD-WAN Constraints?
Minimizing downtime and outages requires end-to-end reliability and redundancy. While MPLS is known for its reliability, the cost of MPLS links often makes MPLS redundancy cost-prohibitive.
These constraints have led organizations to seek alternative solutions, such as using a backup Internet connection and link bonding. However, the active-passive setup of backup connections causes slow failovers and dropped connections. Link bonding’s aggregation of multiple internet links helps overcome that.
The remaining issue is global connectivity, which SD-WAN alone can’t solve due to a lack of control over routing between states, countries, and continents, and MPLS can’t scale because of high cost.
The solution is a SASE-based SD-WAN coupled with a global private backbone that can use multiple local internet links to reliably connect a branch to the nearest SASE PoP, and from there leverage the global private backbone for high speed, redundant, and reliable connectivity to anywhere else in the world.








