How to Buy SASE: Cato Answers Network World’s 18 Essential Questions
Table of Contents
|
Listen to post:
Getting your Trinity Audio player ready...
|
Last December, Network World published a thoughtful guide outlining the questions IT organizations should be asking when evaluating SASE platforms. It was an essential list that should be included in any SASE evaluation.
Too often, SASE is a marketing term applied to legacy point solutions, which is why we suspect these questions are even needed. By contrast, The Cato SASE Cloud is the world’s first cloud-native SASE platform, converging SD-WAN and network security in the cloud. Cato Cloud connects all enterprise network resources including branch locations, the mobile workforce, and physical and cloud data centers, into a global and secure, cloud-native network service. With all WAN and Internet traffic consolidated in the cloud, Cato applies a suite of security services to protect all traffic at all times. In short, Cato provides all of the core SASE capabilities identified by NWW.
We are pleased to respond point-by-point to every issue raised. You should also check out our SASE RFP template to help with the valuation.
1. Does the vendor offer all of the capabilities that are included in the definition of SASE? If not, where are the gaps? If the vendor does claim to offer all of the features, what are the strengths and weaknesses? How does the maturity of the vendor offerings mesh or clash with your own strengths, weaknesses, and priorities? In other words, if your biggest need is Zero Trust, and the vendor’s strength is SD-WAN, then the fit might not be right.
Yes, Cato provides all of the core capabilities NWW defines for SASE – and more. On the networking side, the Cato Global Private backbone connects 70+ PoPs worldwide. Locations automatically connect to the nearest PoP with our edge SD-WAN device, the Cato Socket. Cloud datacenters are connected via an agentless configuration, and cloud applications are connected through our cloud-optimized routing. Remote users connect in by using the Cato Mobile Client or clientless browser access.On the security side, Cato Security as a Service is a fully managed suite of enterprise-grade and agile network security capabilities, directly built into the Cato Global Private Backbone. Current security services include firewall-as-a-Service (FWaaS), secure web gateway with URL filtering (SWG), standard and next-generation anti-malware (NGAM), IPS-as-a-Service (IPS), and Cloud Access Security Broker (CASB), and a Managed Threat Detection and Response (MDR) service.
2. How well integrated are the multiple components that make up the SASE? Is the integration seamless?
The Cato SASE Cloud is completely converged. The Cato SPACE architecture is a single software stack running in our PoPs. Enterprises manage and monitor networking, security, and access through a single application. All capabilities are available in context via a shared user interface. Objects created in one domain (such as security) are available in other domains (such as networking or remote access). (To see what we mean by seamless, check out this detailed walkthrough of the Cato Management Application.)
5 Questions to Ask Your SASE Provider | eBook3. Assuming the vendor is still building out its SASE, what does the vendor roadmap look like? What is the vendor’s approach in terms of building capabilities internally or through acquisition? What is the vendor’s track record integrating past acquisitions? If building internally, what is the vendor’s track record of hitting its product release deadlines?
Cato has demonstrated its ability to develop and bring capabilities to market. Since its founding in 2015, Cato has successfully developed and delivered the global SASE cloud, which is used today by more than 1000 enterprises. We regularly add new services and capabilities to our platform, such as December’s announcement of more than 103 frontend improvements and updates to our backend event architecture. (Other additions included a Cloud Application catalog, a Threats dashboard, an Application Analytics dashboard, CASB launch, and updates to our managed detection and response (MDR) service that automated security assessments.)
4. Whose cloud is it anyway? Does the vendor have its own global cloud, or are they partnering with someone? If so, how does that relationship work in terms of accountability, management, SLAs, troubleshooting?
Cato owns and maintains the Cato SASE Cloud. The PoPs are on our hardware hosted in tier-3 datacenters, running Cato’s cloud-native software stack. Every PoP is connected by at least two and many by four tier-1 carriers, who provide SLA-backed capacity. Cato’s custom routing software constantly evaluates these paths identifying the shortest path for each packet.
Question for MSPs
Network World also included a series of questions specific to managed service providers (MSPs) that we’d like to address as well. Cato in addition to building a SASE platform is also a service provider so we took the liberty of responding to these questions as well.
1. How many PoPs do they have and where are they located? Does the vendor cloud footprint align with the location of your branch offices?
The Cato Global Private backbone currently serves 140 countries worldwide from more than 70 PoPs that we continue to expand each quarter.
2. Does the vendor have the scale, bandwidth, and technical know-how to deliver line-rate traffic inspection?
Thanks to our highly scalable cloud-native architectures, the Cato Cloud delivers line-rate performance regardless of whether traffic is encrypted or unencrypted or the number of security operations performed. PoPs have enough spare capacity to accommodate traffic surges. Case in point was how our Manchester PoP accommodated additional traffic during the Interxion outage.
3. For the cloud-native vendors: How can you demonstrate that your homegrown SASE tools stack up against, say, the firewall functionality from a name-brand firewall vendor?
Cato can fully replace branch office firewalls and, usually, datacenter firewalls. Moreover, the convergence of capabilities allows us to deliver security capabilities and visibility impossible with legacy point solutions. For example, we can use data science and machine learning algorithms on networking data to spot security threats before they can exfiltrate data. The company was founded by security luminary Shlomo Kramer, co-founder of Checkpoint Software. It taps some of the brightest minds in cybersecurity that Israel has to offer. You’re welcome to try out our platform and see for yourself.
4. Is there a risk that the vendor might be an acquisition target? As the market continues to heat up, further acquisitions seem likely, with the bigger players possibly gobbling up the cloud-native newcomers.
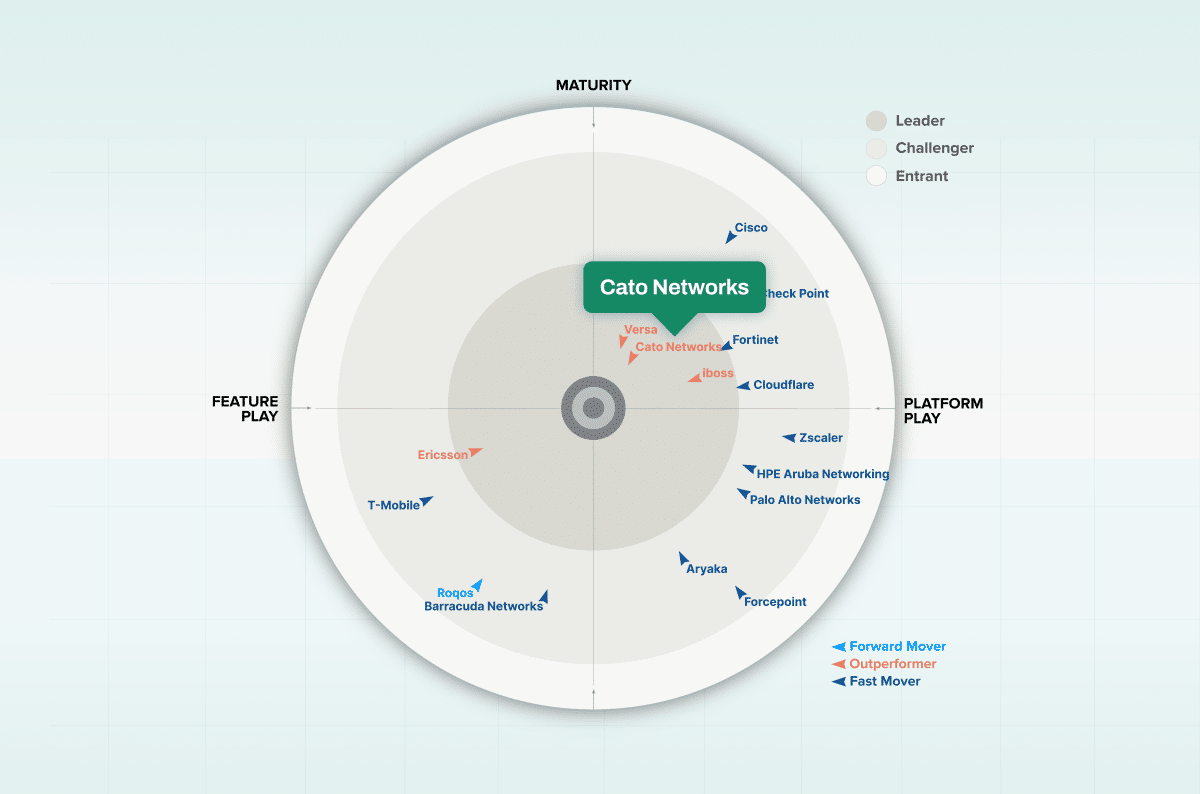
Cato is a well-established company with well over 1,100 enterprise customers committed to serving the needs of those customers for the long term. We’ve raised over $500 million in venture capital resulting in a private $2.5 billion valuation.
5. For the traditional managed services powerhouses like AT&T and Verizon, do they have all the SASE capabilities, where did they get them, and how well are they integrated? What is the process for troubleshooting, SLAs, and support? Is there a single management dashboard?
Cato just like any cloud service provider enables organizations to co-manage their own Cato implementation while Cato maintains the underlying infrastructure. IT teams can opt to manage infrastructure themselves, outsource a subset of responsibilities to a Cato partner, or have a Cato partner fully manage the infrastructure. There’s always 24×7 support available.
6. Is there flexibility in terms of policy enforcement? In other words, can a consistent SASE security policy be applied across the entire global enterprise, and can that policy also be enforced locally depending on business policy and compliance requirements?
Yes, customers apply a consistent security policy across the enterprise. In fact, enterprises have full control over their security policies. We instantiate the most commonly used security policies at startup, so most customers require little or no changes. The policy set is instantly applied across the global enterprise or to a specific site or user depending on requirements. Enterprises can, of course, add/change policies as necessary.
7. Even if enforcement nodes are localized, is there a SASE management control plane that enables centralized administration? This administrative interface should allow security and network policy to be managed from a single console and applied regardless of the location of the user, the application, or the data.
Cato provides centralized administration via our management application. Both security and network policies are managed from the same interface for all Cato-connected users and resources, whether they exist in the office, on the road, at home, or in the cloud.
8. How is sensitive data handled? What are the capabilities in terms of visibility, control and extra protection?
Cato encrypts and protects all data in transit and at rest within the Cato network. Designated applications or data flows that contain sensitive information can also remain encrypted if required in a way that bypasses Cato inspection engines.
9. Is policy enforced consistently across all types of remote access to enterprise resources, whether those resources live in the public internet, in a SaaS application, or in an enterprise app that lives on-premises or in an IaaS setting?
Part of what makes Cato unique is that all inspection engines and network capabilities operate on both northbound traffic to the Internet or east-west traffic to other Cato-connected resources. Our CASB, for example, inspects all Internet and cloud-based traffic. Security capabilities continue to perform well on East-West traffic regardless of the user’s location due to the Cato global private backbone and our distributed cloud architecture.
10. Is policy enforced consistently for all possible access scenarios–individual end users accessing resources from a home office or a remote location, groups of users at a branch office, as well as edge devices, both managed and unmanaged?
Cato uses a single policy set for all access scenarios.
11. Is the network able to conduct single-pass inspection of encrypted traffic at line rate? Since the promise of SASE is that it combines multiple security and policy enforcement processes, including special treatment of sensitive data, all of that traffic inspection has to be conducted at line speed in a single pass in order to provide the user experience that customers demand.
Cato uses a single-pass inspection engine that can operate at line rate even on encrypted traffic. Thousands of Cato SPACEs enable the Cato SASE Cloud to deliver the full set of networking and security capabilities to any user or application, anywhere in the world at cloud scale using a service that is both self-healing and self-maintaining.
12. Is the SASE service scalable, elastic, resilient, and available across multiple PoPs? Be sure to pin the service provider down on contractually enforced SLAs.
The Cato SASE Cloud is a fully distributed, self-healing service, that includes many tiers of redundancies. If the core processing a flow fails, the flow will be handled by one of the other cores in the compute node. Should a compute node fail, other compute nodes in the Cato PoP assume the operation. Should the PoP become inaccessible, Cato has 70+ other PoPs available that enable users to automatically reconnect to the next best available PoP. Enterprises do not need to do any high availability (HA) planning that is typically required when relying on virtual appliances to deliver SASE services.
We have 99.999% uptime SLAs with our carriers. Should one of the tier-1 carriers connecting our PoPs experience an outage or slowdown, Cato’s routing software detects the change and automatically selects the next best path from one of two other carriers connecting our PoPs. Should the entire Cato backbone — that’s right all 70+ PoPs somehow disappear, one day — Cato Sockets will automatically bring up a peer-to-peer network.
13. One of the key concepts of zero trust is that end-user behavior should be monitored throughout the session and actions taken to limit or deny access if the end user engages in behavior that violates policy. Can the SASE enforce those types of actions in real time?
Cato inspects device posture first upon connecting to the network, ensuring the device meets predefined policy requirements and then continues to monitor the device once connected.
Should a key variable change, such as an anti-malware engine expire, the device can be blocked from the network or provided limited access depending on corporate requirements. As users connect to cloud application resources, Cato inspects traffic flows. Dozens of actions within applications can be blocked, enabled, or otherwise monitored and reported, such as uploading files or giving write access to key applications.
14. Will the SASE deliver a transparent and simplified end user experience that is the same regardless of location, device, OS, browser, etc.?
The Cato experience remains consistent regardless of operating system. Mobile users can be given clientless access or client-based access with the Cato Mobile Client. The Cato Mobile Client is available for all major enterprise platforms including Windows, macOS, Android (also supported for ChromeOS), iOS, and Linux. Users within the locations connected by Cato Sockets, Cato’s edge SD-WAN device, log into their network as usual with no change.
Once connected to the Cato SASE Cloud, all security inspection is done locally at the connected PoP, eliminating the traffic backhaul that so often degrades the performance of mobile users situated far from their offices. The Cato Global Private Backbone uses optimized routing to minimize latency and WAN optimization to maximize throughput. The result is a remote user experience that’s as close as possible to being inside the office.
Other Questions to Explore
We applaud Network World for raising these issues. Some other questions we might encourage IT teams to ask MSPs include:
- High Availability (HA): Take a close look at how HA is delivered by the vendor. What’s the additional cost involved with deploying the secondary appliance? How are the SD-WAN devices configured and deployed? With most enteprises, HA has become the defacto edge configuration to ensure the high uptime they’re looking for particularly when replacing MPLS.
- What happens when there is a lockup rather than just an outage, will the system failover properly?
- What about the underlying memory, storage, and server system underpinning what are often virtual appliances?
- What happens if the PoP itself becomes inaccessible?
The list goes on. The secure Cato SASE platform is based on a fully distributed self-healing network built for the cloud era that we manage 24/7 on behalf of our customers. Anything less than that from our perspective simply isn’t SASE.