Showing 0 results
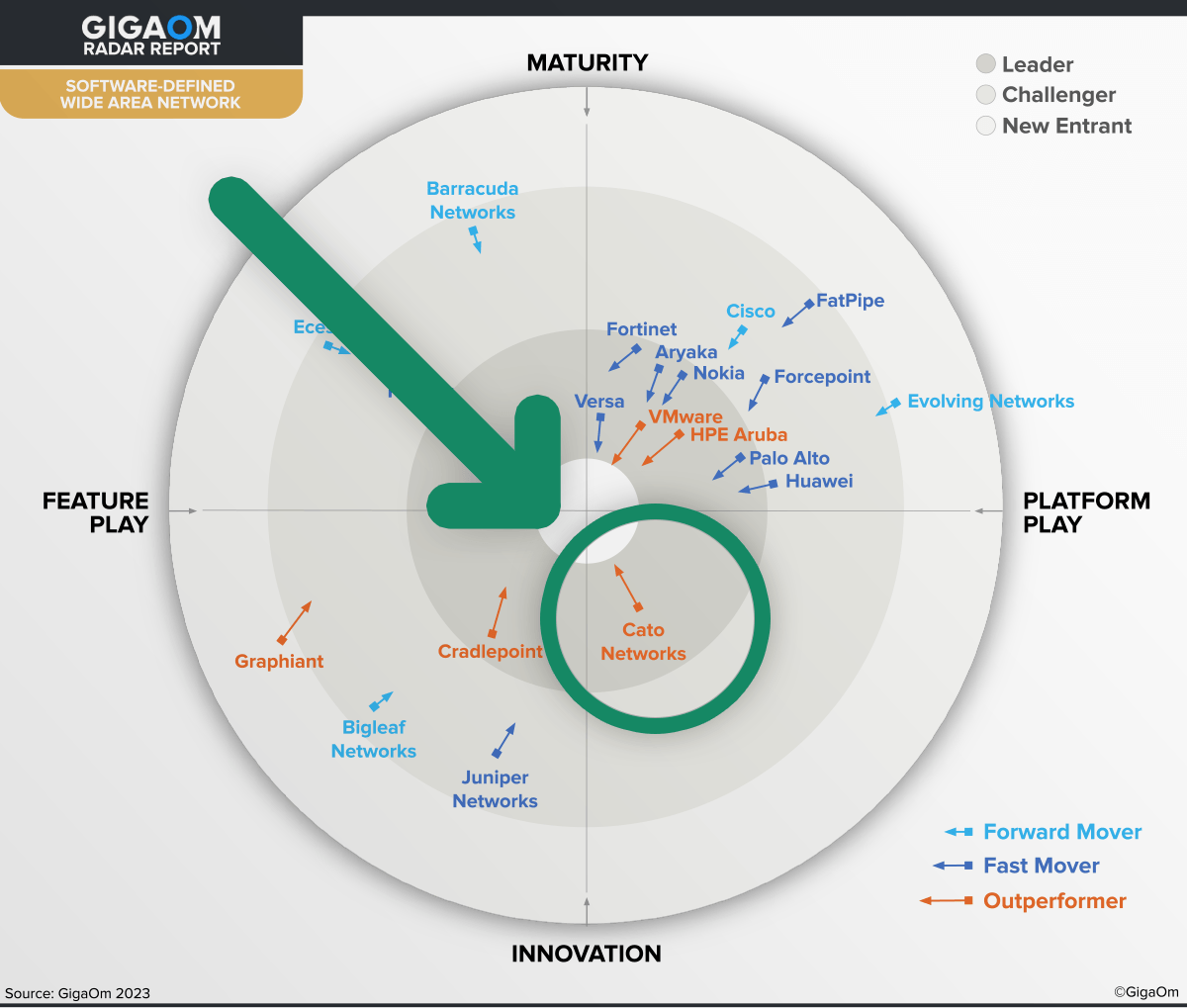
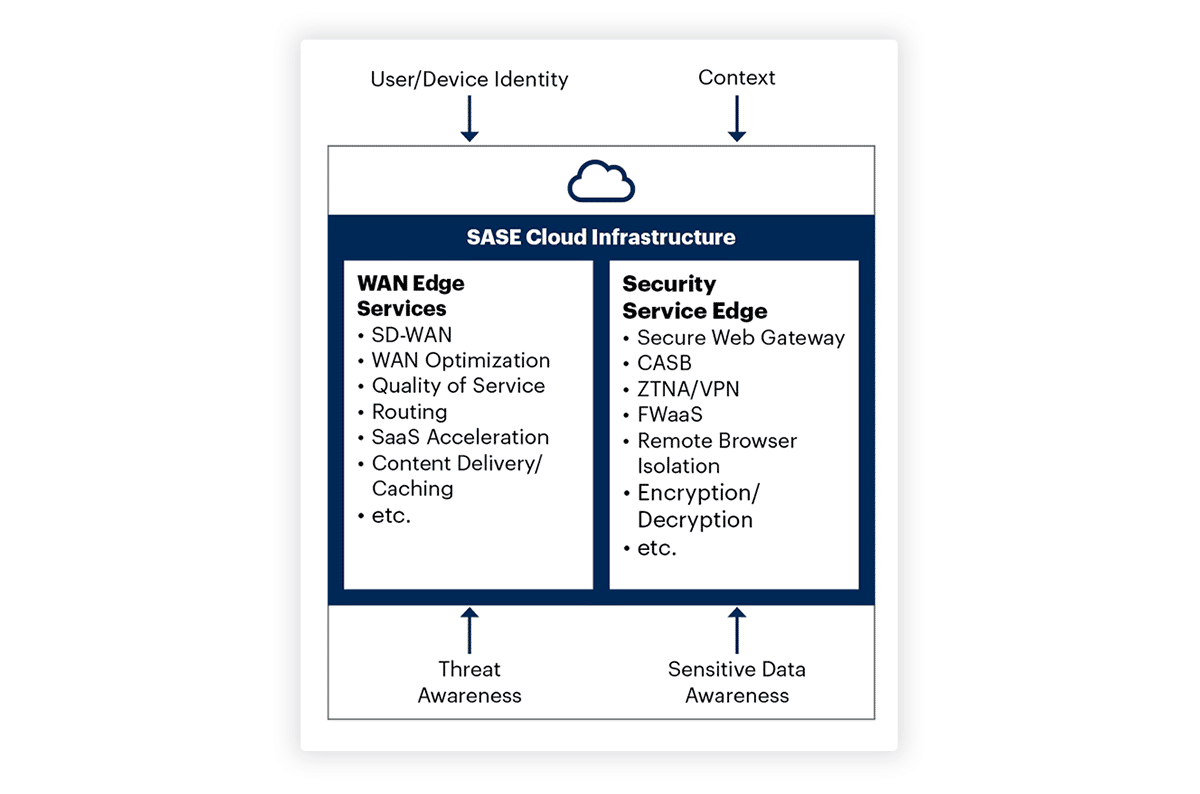
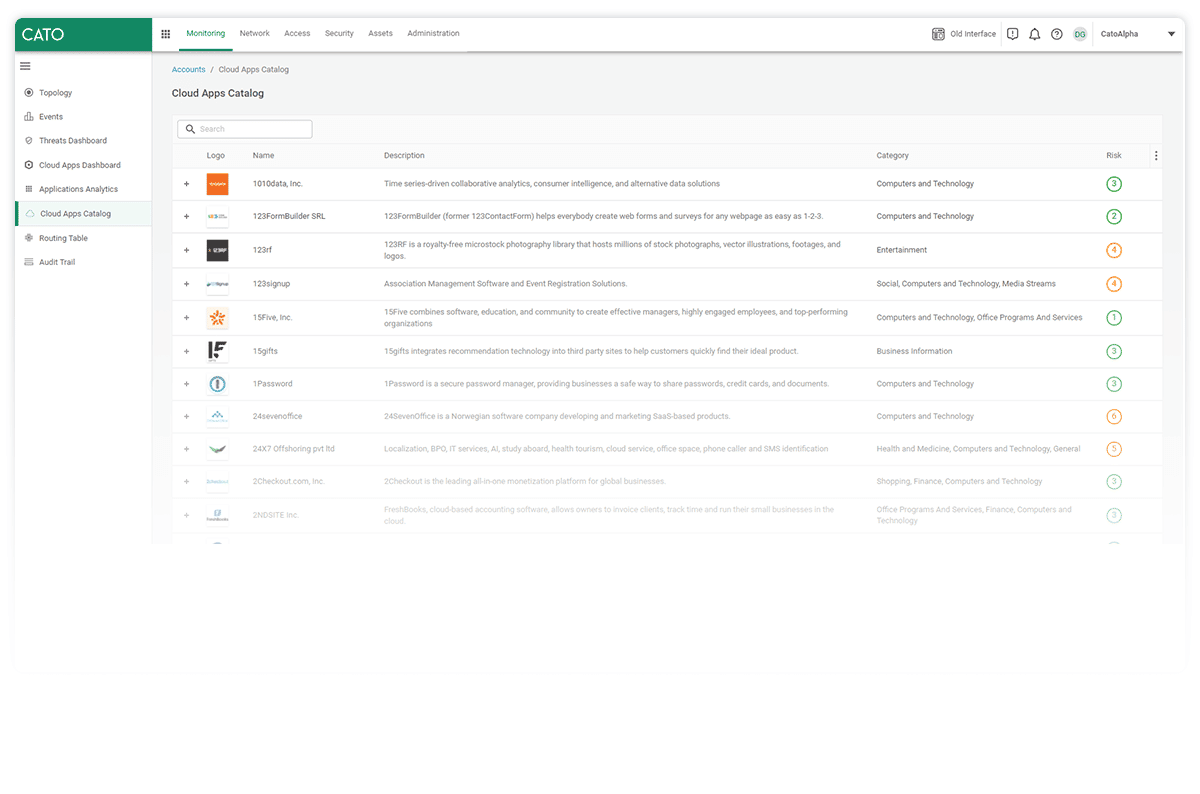
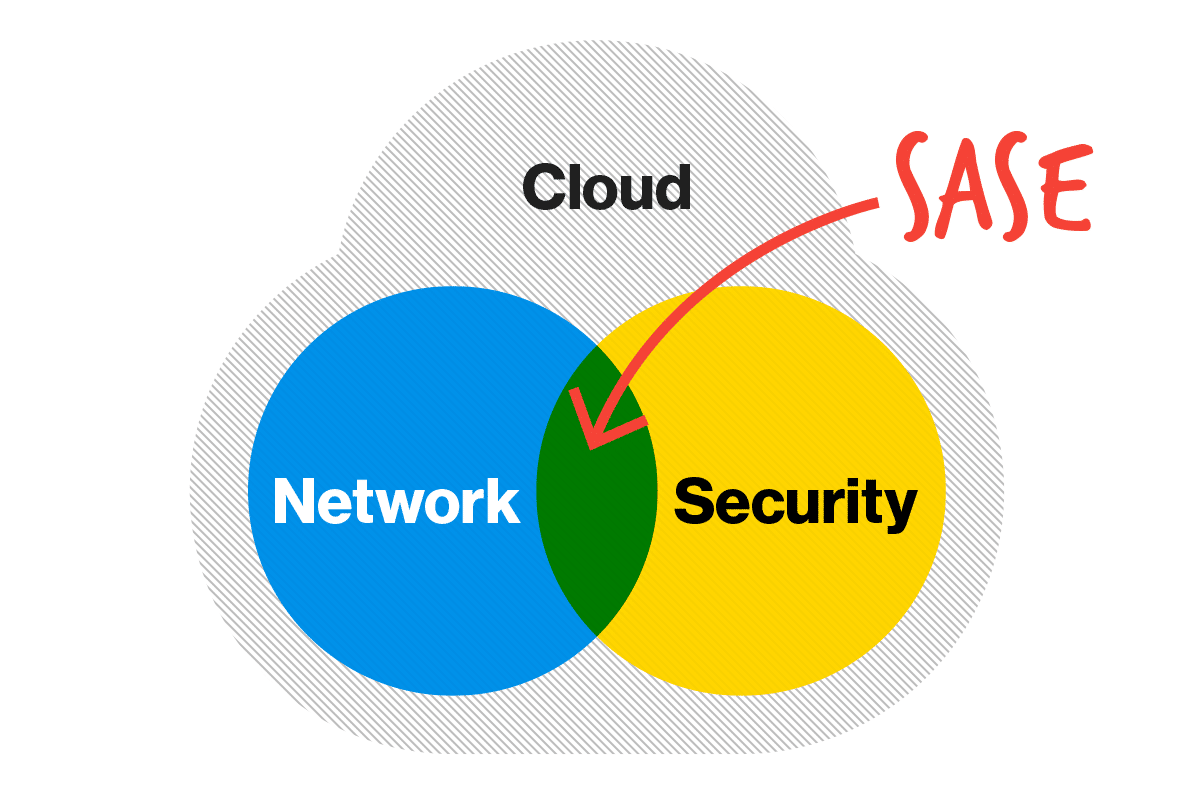
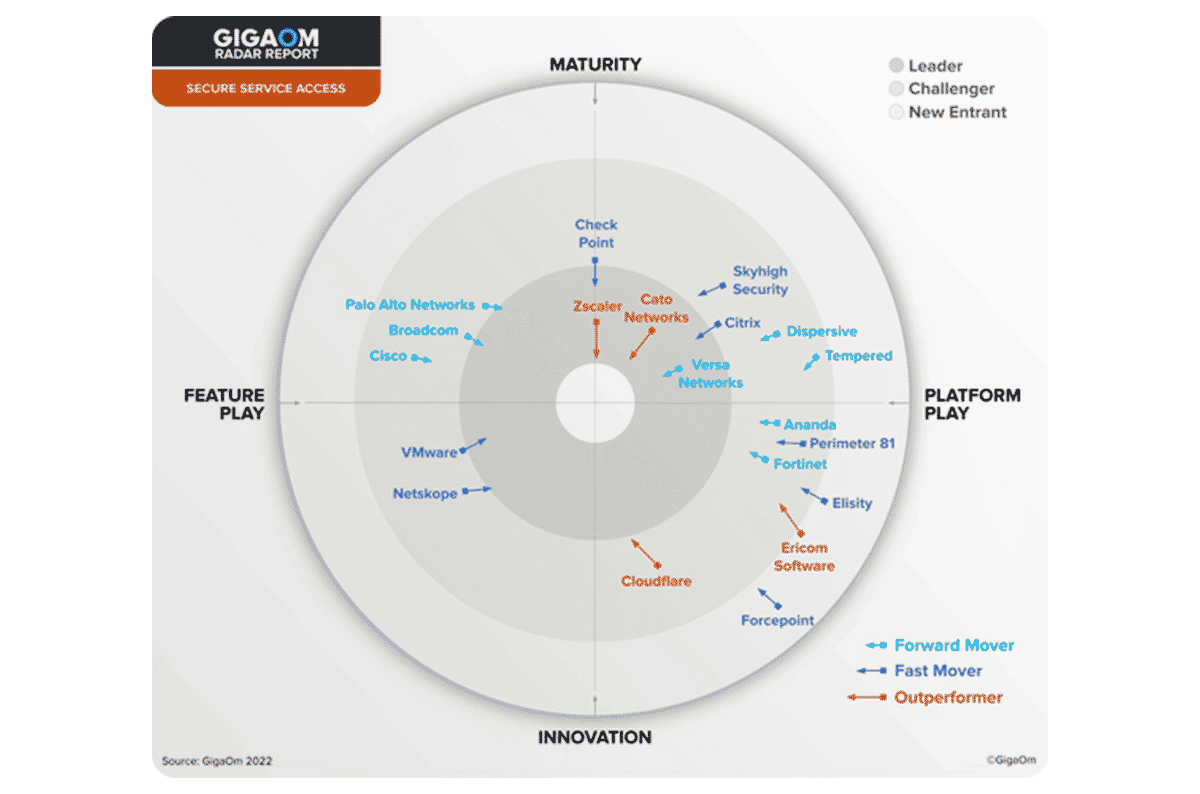
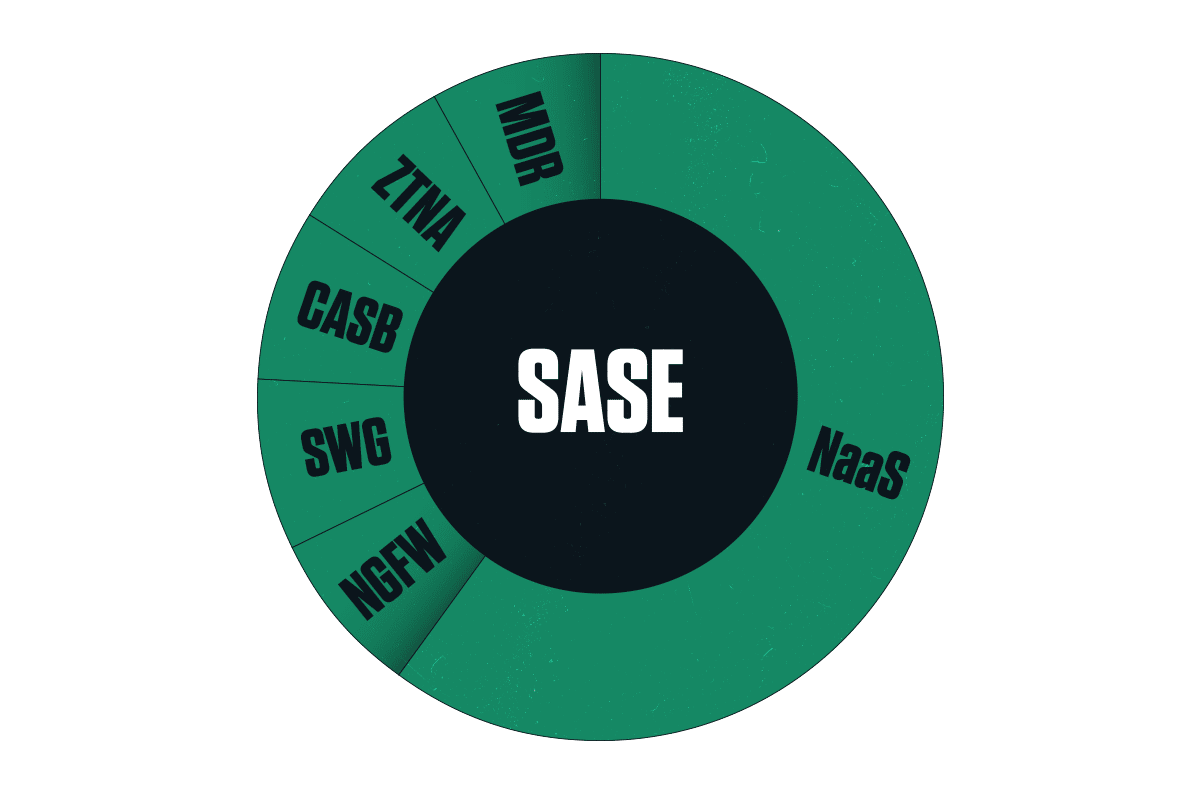
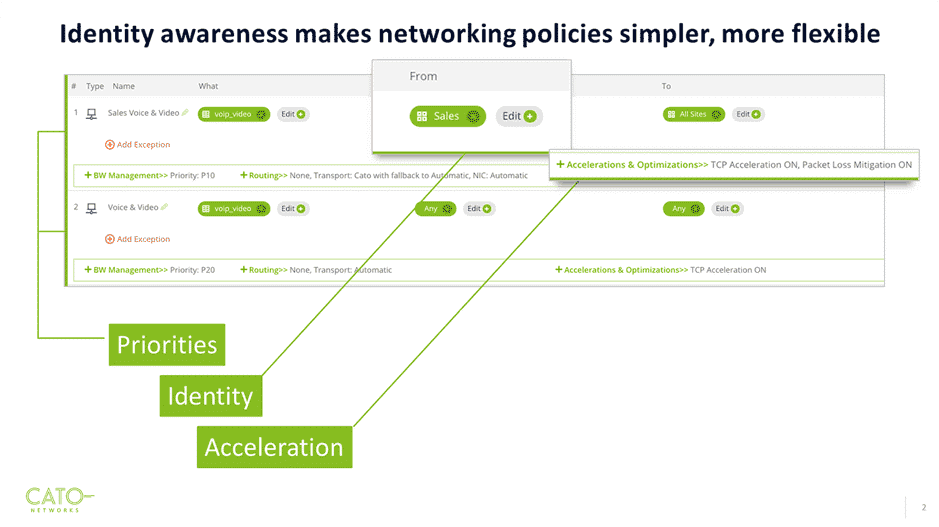
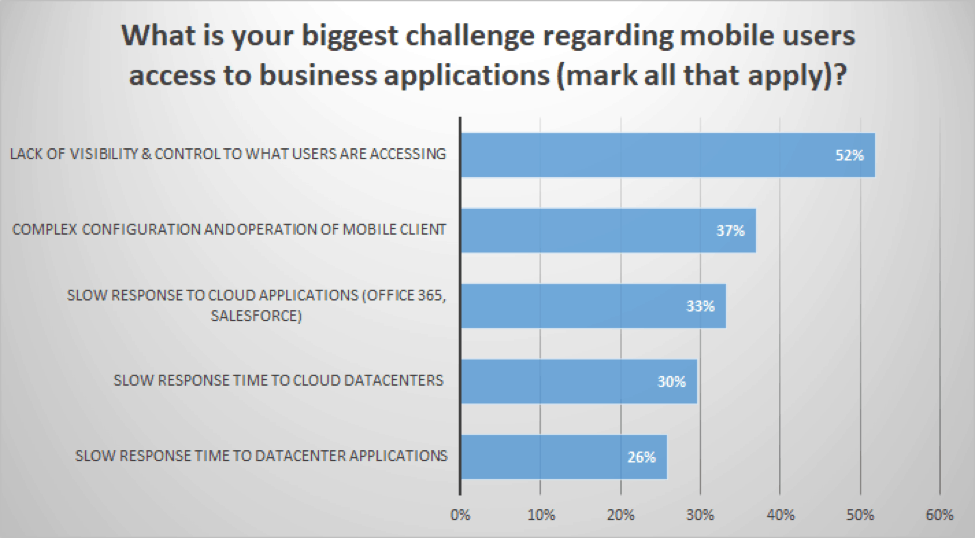
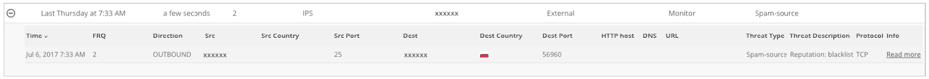
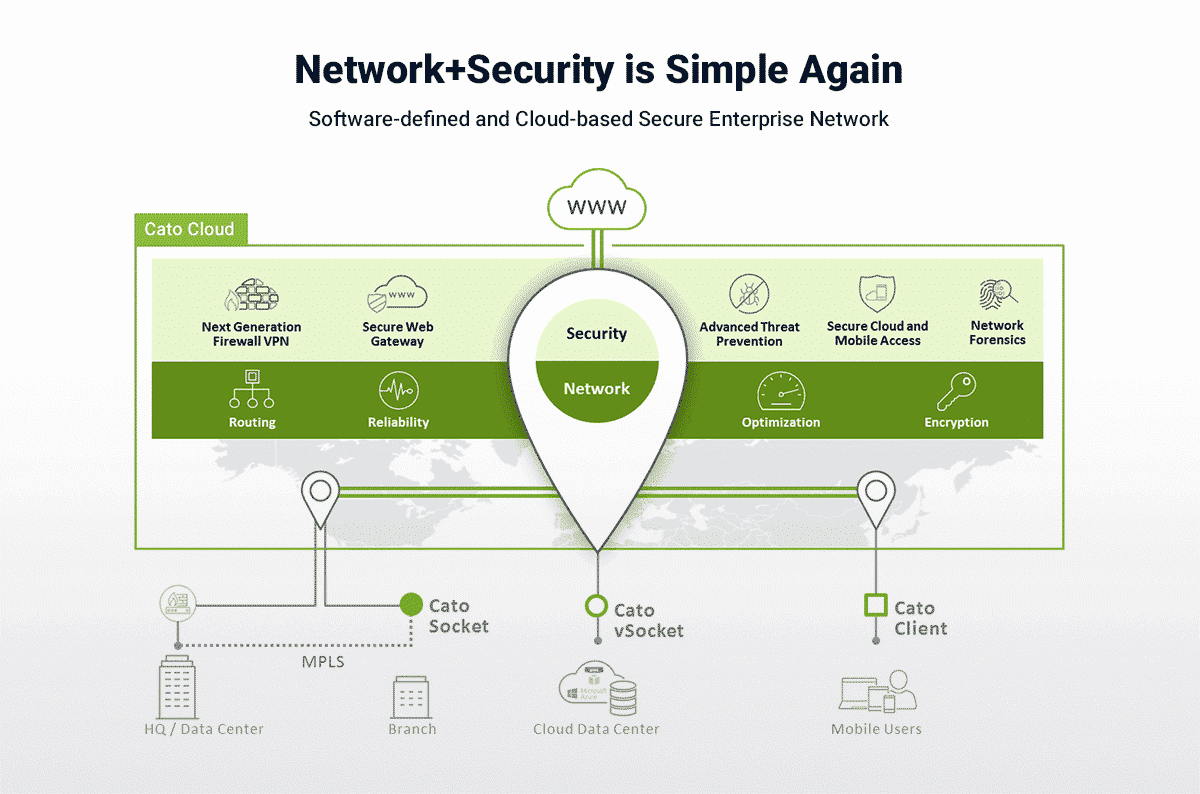
GigaOm and Frost & Sullivan Recognize Cato Networks for SASE InnovationCato Survey: Remote Access Issues and Need for Increased Visibility Continue to Drive SASE in 2024Cato Continues Expansion with New Global Headquarters Women in Tech: A Conversation with Cato’s Shay RubioCloudFactory Eliminates “Head Scratching” with Cato XDRCato XDR Proves to Be a “Timesaver” for Redner’s MarketsCato Taps Generative AI to Improve Threat CommunicationHow to Build the Perfect Network Without SLAsWith New Third-Party Integrations, Cato Improves Reach and Helps Customers Cuts CostsSSE Is a Proven Path for Getting To SASENetworking and Security Teams Are Converging, Says SASE Adoption Survey The New Network Dictionary: AvidThink Explains SASE, SD-WAN, SSE, ZTNA, MCN, and NaaS Carlsberg Selects Cato, the “Apple of Networking,” for Global SASE Deployment Key Findings From “WAN Transformation with SD-WAN: Establishing a Mature Foundation for SASE Success”Cato’s 5 Gbps SASE Speed Record is Good News for Multicloud and Hybrid Cloud DeploymentsQ&A Chat with Eyal Webber-Zvik on Cato RBI A sit down with Windstream Enterprise CTO on Security Service EdgeUnsolved Remote Access Challenges Continue to Propel SASE in 2023, Finds New Cato SurveyCato SASE Cloud’s “Innovation” and “Platform Play” Earn “Leader” and “Outperformer” Status in GigaOm SD-WAN Radar ReportGartner’s Market Guide to Single-Vendor SASE Offerings: The Closest Thing You’ll Get to a SASE Magic QuadrantThe 5-Step Action Plan to Becoming CISOThe OpenSSL Vulnerability: A Cato Networks Labs UpdateInside a Network Outage: How Cato SASE Cloud Overcame Last Week’s Fiber Optic Cable CutNew Gartner Report Identifies Four Missed Tips When Evaluating SASE Platform CapabilitiesThe Return On Investment of SD-WANThe Gnutti Carlo Group Names Cato Networks 2021 Best Supplier in the Innovation CategoryInside SASE: GigaOm Review of 20 Vendors Finds Platforms Are Far and Few15 Networking Experts To Follow on LinkedInIs SD-WAN Really Dead?Not All Backbones are Created EqualCato’s Ransomware Lab Births Network-based Ransomware PreventionAzure SD-WAN: Cloud Datacenter Integration with Cato NetworksThe Only SASE RFP Template You’ll Ever NeedCato Expands to Marseilles and Improves Resiliency Within FranceHow to Buy SASE: Cato Answers Network World’s 18 Essential QuestionsIT Managers: Read This Before Leaving Your MPLS ProviderEye-Opening Results from Forrester’s Cato SASE Total Economic Impact ReportMaking Site Support a Bit Easier. Meet the Diagnostic Toolbox in Your Cato SocketMoving Beyond Remote Access VPNsWhat is Network-as-a-Service and Why WAN Transformation Needs NaaS and SASEIndependent Compliance and Security Assessment – Two Additions to the All-New Cato Management ApplicationNew Insight Into SASE from the Recent Gartner® Report on Impact Radar: CommunicationsThe Future of the Enterprise Firewall is in The CloudPersonalized alerts straight from production environmentsSSE: It’s SASE without the “A”Horizon for SASE Adoption Shortens, Fewer Sample Vendors Identified in SASE Category of Gartner Hype Cycle for Networking, 2021Gartner’s Nat Smith Explains What Is and Is Not SASEUpdate to Cato MDR Shortens Time-to-Value, Automates 70 Security Checks5G: A Step Beyond the Last Mile?Poor VPN Scalability Hurts Productivity and SecurityWhat is a Cloud Firewall?Remote Access Security: The Dangers of VPNWhat is a UTM Firewall and What Is Beyond It?New Forrester Report: Merging Network and Security in the Age of CovidCato Offers a Free Certification Program to Help Customers and Channel Partners Learn the Fundamentals of SASERemote Access Network Architecture and Security ConsiderationsNetwork Security Solutions to Support Remote Workers and Digital TransformationWhy Large Enterprises Moved to Cato in 2020SASE vs. SD-WAN: Achieving Cloud-Native WAN SecurityWhy Remote Workforce and Legacy Security Architectures Don’t MixSD-WAN or SASE: The Power is in the PlatformTypes of Remote Access Technologies for EnterprisesCato Engineers Review Favorite SASE FeaturesThe Best Networking Memes of 2020Stopping Sunburst: The Second-Best Argument for a SASE PlatformMPLS Upgrade for the Modern Enterprise50,000 Fortinet VPNs Breached Via Vulnerability Fixed 18 Months Ago. Here’s What You Can Do.How Cato Cloud Resiliency Overcomes Regional and National OutagesTop 15 Network Security WebsitesSASE: It’s the iPhone of NetworkingRethinking Enterprise VPN Solutions: Designing Scalable VPN ConnectivityWhy SASE Must Support ALL Edges, ALL Traffic, and ALL ApplicationsWhy I Hate Multivendor SASEWhat is Zero Trust Architecture?A Modern Approach to Enterprise Remote AccessSASE Convergence or Integration? It’s Not the Same ThingThe disadvantages of VPNs for EnterprisesCloud Native, COVID-19, and True Secure Access Service Edge – What The 2020 Gartner Hype Cycles Taught UsHow to Prepare for Long-term Remote Work, Post-PandemicThe Path of a Packet in Cato’s SASE ArchitectureHow Can Organizations Improve Network Performance?Advanced Network Security TechnologiesThe WAN Accelerator and Modern Network OptimizationThe 4 Key Considerations for Extending Your Business Continuity Plan (BCP) to Home and Remote WorkersFrom MPLS to SD-WAN to SASE: An Evolution of Enterprise Networking2019: A Year of Innovation and Validation for the Cato VisionWhere is Network Security headed in 2020?SD-WAN vs Hybrid WANNetwork Optimization Techniques for the Modern WANNetwork & Firewall Security for the Modern EnterpriseWhat are VPN Tunnels and How do They WorkSD-WAN Confessions: How One Company Migrated from MPLS to SD-WANWhy is SD-WAN Considered a Top Choice Among VPN Alternatives?What is Network Visibility?Talking WAN Transformation and Managed Services with Virgin’s Network and Security Architect Frankie StroudSolving the Challenges of SD-WAN Security with Cloud-NativeThe Secure Access Service Edge (SASE) as Described in Gartner’s Hype Cycle for Enterprise Networking, 2019Cloud-based SD-WAN: The optimal approach to WAN latencyThe Way Forward: How SD-WAN Benefits the Modern EnterpriseWill cloud-based networking be your next WAN?SD WAN redundancy vs. MPLS redundancyNaaS Meets SD-WAN: What is NaaS anyway and How Will It Impact Your SaaS, PaaS, and Cloud Strategy?How to connect multiple offices quickly and affordably with Cato CloudMaking a Strategic Plan for the Future of NetworkingSD-WAN Services: Forget Burger King, Just Manage It Your WayMirai Malware Targeting the EnterpriseThe Co-Managed SD-WAN: A Managed Infrastructure with Self-Service Capabilities for AgilityNew Research Documents How Traditional Telco Services Cripple Digital TransformationHow SD-WAN Overcomes Last Mile ConstraintsNFV is Out of Sync with the Cloud-Native Movement. Here’s a SolutionHow SD-WAN Provided an Alternative to MPLS – A Case Study4 Real World Challenges in Enterprise Networking & How SD-WAN Can Solve ThemThe Cloud-Native Network: What It Means and Why It MattersStandard Insurance Transforms WAN with Cato Cloud to Win ICMG Award For Best IT Infrastructure ArchitectureHow To Best Design Your WAN for Accessing AWS, Azure, and the CloudSD-Wan Consideration Factors for Global CompaniesWhat is OTT SD-WAN?Cato MDR and Zero-Day Threat Prevention: Meet Our Two Newest Security Offerings4 Ways Cato is Perfect for UCaaSThe Pains and Problems of NFVWhat Enterprises Can Learn From The $55 Million Investment in Cato NetworksWhat You Should Know Before Choosing a Managed SD-WAN ServiceSD-WAN Success Requires A New Kind Of Managed Service ProviderStill on the Fence about SD-WAN? Gartner Says to Include It in WAN Architecture DiscussionsTop Podcasts for SD-WAN and Network ProfessionalsThe Best IT Network and SD-WAN Events for 2019How To Make A Smarter Last-Mile Management ServiceSign of the Times: Time to Eliminate Your Dependence on MPLS and Switch to SD-WANShould You Be Concerned About the Security of SD-WAN?Cato: The SD-WAN VisionaryTop WAN Issues Faced by Globally Distributed EnterprisesCato Extends Self-Healing, End-to-End for Enterprise SD-WANsWhat Enterprises Say about Cato’s SD-WANTop 5 Myths About SD-WANUnderstanding the hidden costs of virtual CPEA New Approach to SD-WAN ManagementBack to School with SD-WANThe SD-WAN Features Needed to Accelerate Global Application DeliveryBackbone Performance: Testing the Impact of Cato Cloud’s Optimized Routing on LatencyWhat is SD-WAN?The 4 Values of SD-WANCato Revolutionizes SD-WAN with Identity-Aware RoutingA Technology Horror Story: The Day the Marketing Guy Joined the HackathonTop 11 Women in Enterprise NetworkingThe Evolution of SD-WANTop SD-WAN Events to Attend in 2018 and 2019Ensuring High Uptime with SD-WANWhat You Don’t Need from an SD-WAN VendorCato Adds Threat Hunting Capabilities to Cato CloudIt’s Time To Break Down The Access Silos2018 SD-WAN Survey: What Enterprises Want From Their SD-WAN VendorSD-WAN Use Cases – Where to Start with SD-WANInside Gartner’s 10 Worst Networking PracticesSD-WAN and Cloud SecurityMulti-Segment Optimization: How Cato Cloud Modernizes WAN Optimization for Today’s SD-WANFirewall as a Service vs UTMTop Webinars on SD-WAN Technology and SolutionsWhat is Firewall as a Service (FWaaS) and Why You Need ItWAN Optimization vs. SD-WAN, or Why You Need Both3 ways Cato Cloud isn’t your father’s (or mother’s) SD-WANMPLS, VPN Internet Access, Cloud Networking or SD-WAN? Choose WiselyPaysafe Fixes Active Directory, Improves Throughput, and Reduces Costs By Converging MPLS and Internet-based VPN onto Cato CloudWhy SD-WAN is the Future of Global Connectivity10 Reasons To Choose Firewall as a Service For Your Enterprise2018 Networking Survey: The Curse of Complexity ContinuesStratoscale Boosts Throughput 8X with Cato CloudWhat To Look For in a SD-WAN VendorInside Cato’s Advanced Security ServicesArlington Orthopedics Switches to Cato Cloud Enabling Lean IT and AgilitySD-WAN vs. MPLS vs. Public InternetHumphreys Replaces SD-WAN Appliances with Cato CloudHow to improve mobile access to AWS, Office 365, and the rest of the cloudWAN Architecture Webinar: How Will You Transform Your WAN in 2018?How One IT Manager Deployed Sites in Minutes and Cut Costs by 10%What’s Really the Best Approach for Replacing MPLS Connectivity?Top 15 Enterprise Networking Experts To Follow2018: Is Your WAN Ready?The 2018 WAN Survey: Helping Us, Help YouHow to Choose the Most Suitable Network Technology for Your CompanyWhy Cloud Networking Is The Future Of Global ConnectivityFirewall Bursting: A New Approach to Scaling FirewallsAWS, Azure, or Google Cloud Platform? How Scenario Analysis Simplifies Choosing the Right Cloud ProviderThe Mobile Access Revolution: Visibility and Performance Remain a ChallengeThe business case for SD-WAN: Because MPLS is Not Fit for the CloudMobile Access: How to End Slow Mobile VPNsHow a Retailer Built an SD-WAN Across 100+ Stores: A Customer Case Study4 Ways to Secure Your Cloud DatacenterHow Alewijnse used SD-WAN Connectivity as an MPLS Alternative: A In-depth ProfileCan SD-WAN Services Meet the 6 Promises of SD-WAN?IoT Security Best PracticesIoT Security Standards and InitiativesTMC, Layer123 Recognize Cato for SD-WAN LeadershipThe 4 Drivers in the Journey to Full WAN TransformationTransitioning to SD-WANs: Problems to AvoidThe Case for Replacing MPLS with Cloud-based SD-WAN: A Customer StoryHow Secure is Your SD-WAN?Sun Rich: A Lesson in the Benefits of a Fully Converged WANWhat is SD-WAN and can it transform enterprise networking?AdRoll: How to Improve Contractor Management and Mobile Access to the CloudSimplifying your Office 365 Deployment with CatoBattle of the Global Backbones: What are Your Options?Why Global SD-WAN powered by IP Transit Backbone is Perfect for the Post-MPLS EraSD-WAN vs. MPLS: Choose the best WAN solution for youThe SD-WAN Buyer Collection: EBooks and the Guru Test for Building Tomorrow’s Backbone, TodayCato Adds IPS as a Service with Context-Aware Protection to Cato SD-WANA leopard can’t change its spots: Why physical security appliances can’t move to the cloudHow to Overcome Internet Problems with Cato’s Secure and Optimized SD-WAN ServiceThe MacGyver Experience: How Improvising with Cato Avoided DowntimeFWaaS or Managed Firewall Services: What’s the Difference?WannaCry II: How to Stop NotPetya Infections with the Cato CloudThe Internet is Broken: Here’s WhyOpening Offices in China and Asia Pacific: Are You Ready to Be a Hero?Come Meet the Cool Vendor at InfoSecurity EuropeRise of the UberNetWAN Survey: Be Wary of SD-WAN ComplexityInfoSecurity Europe: How to Build a Hybrid CloudHackerNews Finds Cato Cloud to be a “Huge Benefit” for IT ProfessionalsHow to Stop WannaCrypt Infections with the Cato CloudService Insertion and Service Chaining Defined4 Tangible Reasons for Considering SD-WANsThe WAN Survey: Learn From Your PeersWhat’s Wrong with a Digital Geneva Convention?Cato Research Decrypts the News Behind February Security EventsHow To Migrate to a Multi-Cloud DeploymentFour Questions For Life After MPLSSecurity + Network As a Service: the Better SD-WANHow SD-WANs Can Become Next Generation WAN ArchitecturesThe Promise and Peril of SD-WANsRemote Code Execution, Phishing, and More: Cato Research Labs Reviews January Security EventsTicketbleed Undermines SSL Security451 Research Reviews the Cato CloudHow MSSPs Can Drop The BoxSD-WAN and Beyond: What to Consider in a WAN Transformation?