Meet the Industry’s First GPU-Powered SASE Platform with Native AI Security
|
Listen to post:
Getting your Trinity Audio player ready...
|
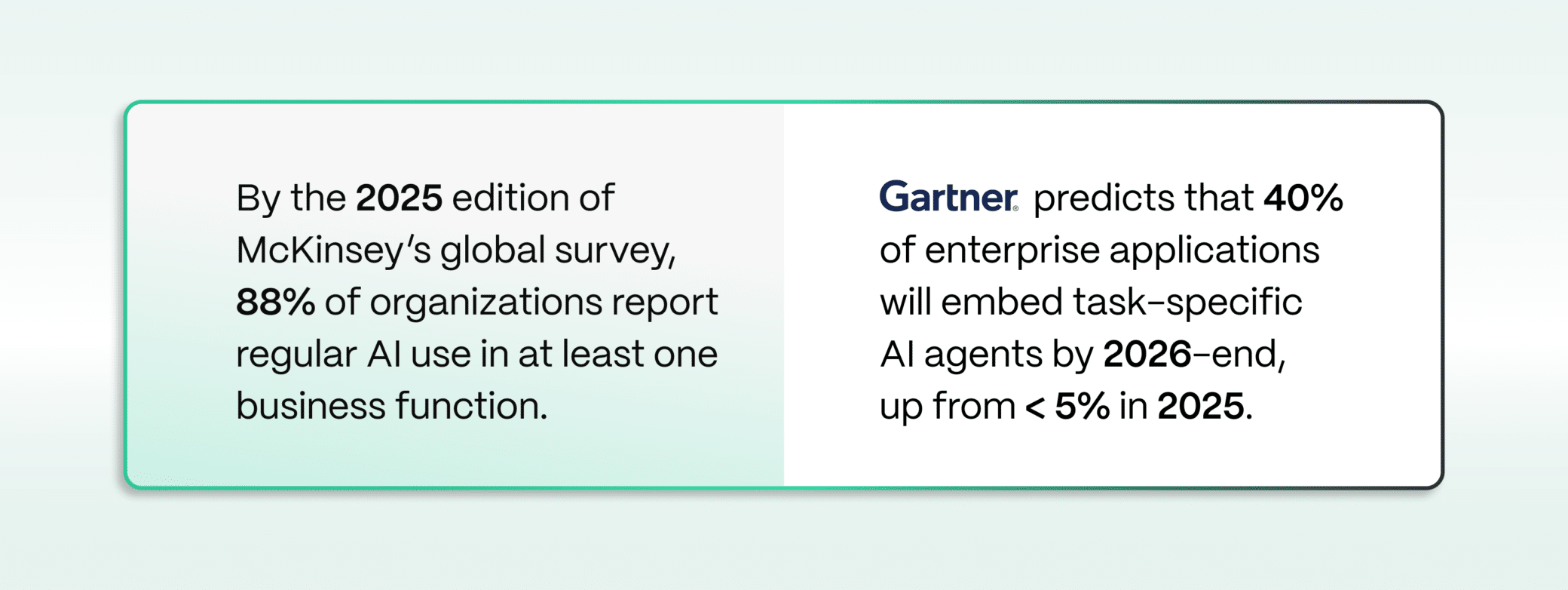
AI has moved from experimentation to a strategic enterprise imperative. It’s no longer about whether organizations will adopt AI, but whether their security architecture can govern it at the speed and scale at which it is being embedded into the business.
This is not a future concern. It is today’s operational mandate to:
- Secure all AI usage.
- Secure homegrown AI applications.
- Govern autonomous AI agents.
Securing AI is not limited to software applications and agents. It requires hardware infrastructure capable of sustaining its scale, performance, and AI-grade compute intensity. Cato solves for both.
Introducing Cato Neural Edge
NVIDIA GPUs are now deployed across the Cato SASE Platform, spanning 85+ PoP worldwide. The GPU-powered Cato Neural Edge provides the compute foundation to run advanced SML models at scale, enabling deeper semantic inspection, large-scale pattern analysis, and real-time adaptive intelligence inline across Cato’s global private backbone.
Traditional SASE architectures route AI workloads to separate hyperscaler GPU locations, introducing round-trip inference latency that degrades performance and limits AI traffic scalability.
Cato Neural Edge converges inspection, compute, and enforcement within the same PoP. This eliminates architectural separation and reduces latency variability. Intelligence runs where enforcement runs.
AI transformation is not only about securing AI. It is about using AI to deliver better security outcomes. GPUs in the Cato cloud enable:
- Faster AI-driven threat detection,
- More accurate semantic data classification, and
- Scalable inspection aligned with enterprise performance expectations.
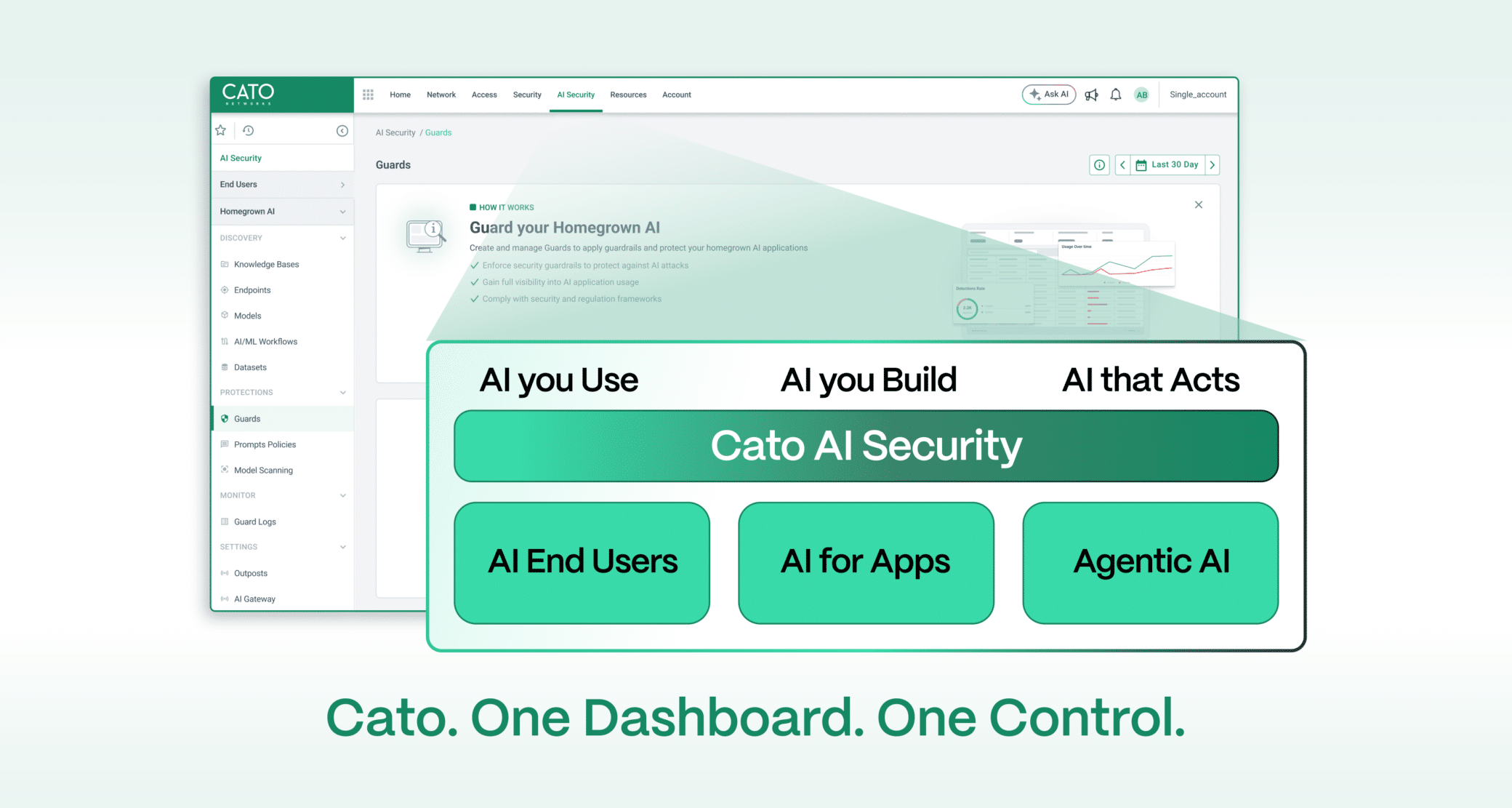
Cato AI Security, Native in the Cato SASE Platform
Cato is proud to offer the industry’s first SASE platform with native AI Security.
Cato’s single architecture now includes the full breadth of AI security and governance:
- A single management application for One Control.
- A unified policy engine for One Security.
- A shared data lake for One Context.
As boards mandate AI adoption and governance, AI security cannot be treated as a standalone control point. It must be embedded into the enterprise security architecture. Cato delivers unified visibility and enforcement across network, access, security, and AI governance within a single architectural framework.
Cato AI Security as a Stand-alone Solution
Importantly, Cato AI Security is available as a standalone solution. Organizations can secure their AI transformation with any combination of use cases: AI usage, homegrown AI applications, or agentic workflows.
The power of the Cato platform lies in its modularity, giving customers the flexibility to start where needed and evolve on their own terms, all with seamless, CapEx-free cloud agility.
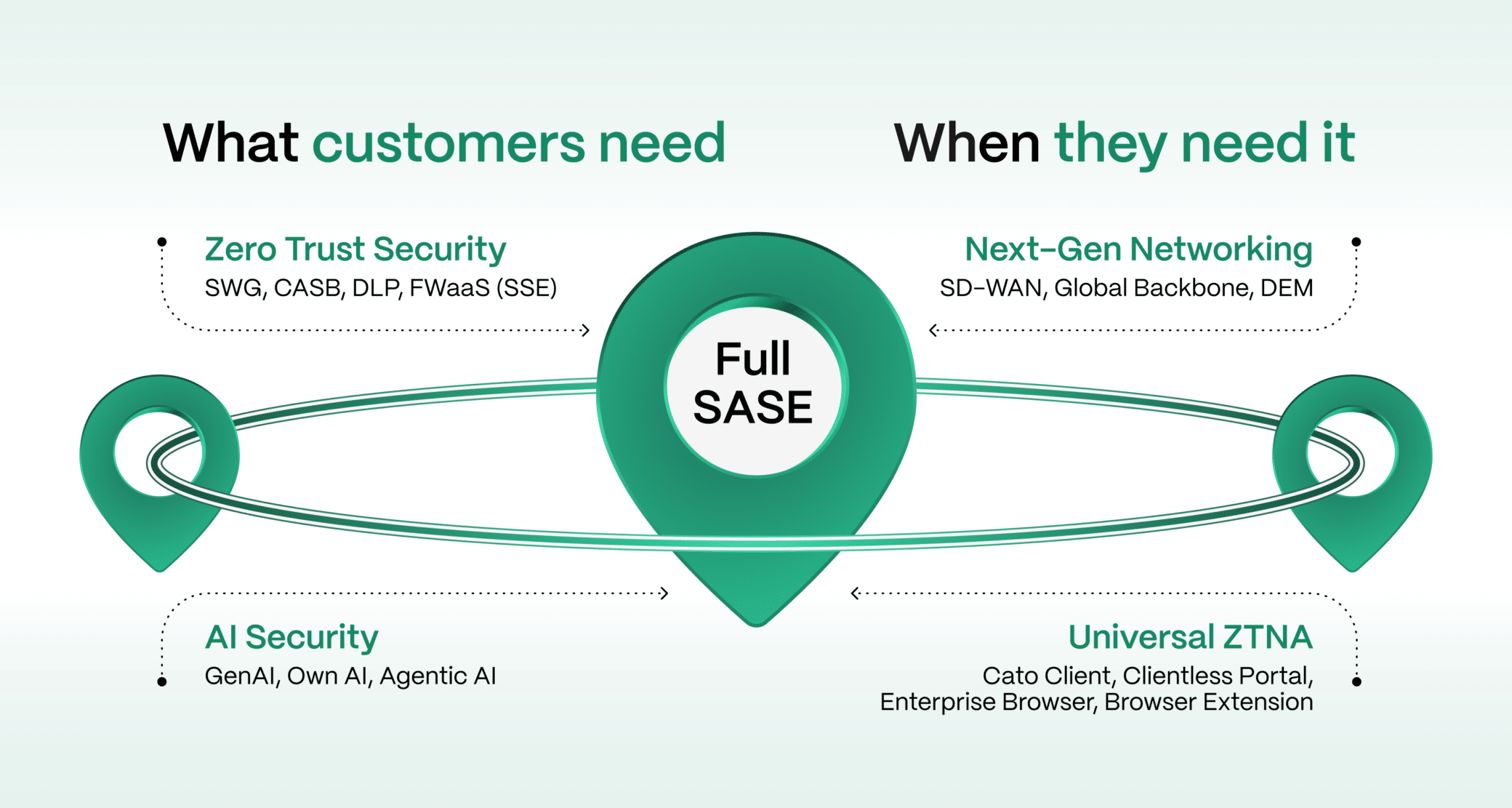
Even as a standalone solution, Cato AI Security runs on the same global private backbone and resilient architecture that deliver enterprise-grade 99.999% SLA-backed availability. It also establishes a foundation to expand seamlessly into Zero Trust security and next-generation networking without re-architecture.
What This Means at the Executive Level
Why is the AI Security Problem Different?
AI introduces an entirely new security dimension. Traditional controls were built to inspect files, user behavior, and application access. AI risk is conversational and contextual. Enterprise security must evolve accordingly.
With AI, security teams are no longer protecting only data objects and application sessions. They are protecting intent expressed in natural language, instructions embedded in prompts, and chained actions executed by agents.
Organizations must contain Shadow AI before sensitive information is exposed. They must prevent prompt injection and jailbreak techniques that override model safeguards. They must correlate multi-stage agent actions across APIs and enterprise systems to understand cumulative impact.
To realize the full value of AI transformation, organizations must embed AI Security across the business, not bolt it on. A point-product approach creates visibility gaps and inconsistent enforcement that attackers can exploit. AI Security, that is self-standing, and yet built into a holistic enterprise network security architecture with centralized policy and full visibility delivers consistent protection across users, data, applications, and AI interactions.
Secure Your AI Transformation Webinar | Save your seat.From Breakthrough Research to World-Class AI Security
Effective AI security requires deep understanding of emerging AI attack techniques.
Cato AI Security is built on groundbreaking AI security research from our world-class research team (formerly Aim Labs) who uncovered EchoLeak, the first Zero-Click AI vulnerability and CurXecute, a remote-code execution vulnerability via Cursor MCP. This deep expertise of prompt injection exploitation, model manipulation, and AI-driven attack chains is translated into product innovation that delivers best-in-class AI guardrails.
Setting the Right Foundation for the AI Security Era
AI adoption and AI risk are now C-level and board-level mandates. They cannot be addressed through siloed tooling or disconnected point solutions.
Cato is the first to natively deliver AI Security as part of a converged security architecture, from a single console and policy engine to a GPU-powered global cloud platform. Enterprises can deploy AI Security as a standalone solution or alongside SSE, Universal ZTNA, or SD-WAN, while leveraging the power of a global cloud platform that maintains unified policy, consistent enforcement, and platform-wide visibility without sacrificing architectural integrity.
Backed by dedicated AI security research, Cato continuously discovers emerging AI threats and translates that intelligence directly into platform-wide protections, ensuring enterprises stay ahead of rapidly evolving risks.
The result: enterprises can accelerate AI innovation with unified visibility, proactive protection, and consistent control, without introducing new security gaps, new management consoles, or siloed point products for every emerging AI risk.
It’s time to secure your AI transformation with AI security that’s built-in, not bolted on.