SSE: It’s SASE without the “A”
|
Listen to post:
Getting your Trinity Audio player ready...
|
As IT leaders look to address the needs of the digital enterprise, significant changes are being pushed onto legacy networking and security teams. When those teams are in lockstep and ready to change, SASE adoption is the logical evolution. But what happens when security teams want to modernize their tools and services but networking teams remain committed to legacy SD-WAN or carrier technologies? For security teams, Gartner has defined a new category, the Security Service Edge (SSE).
What is SSE?
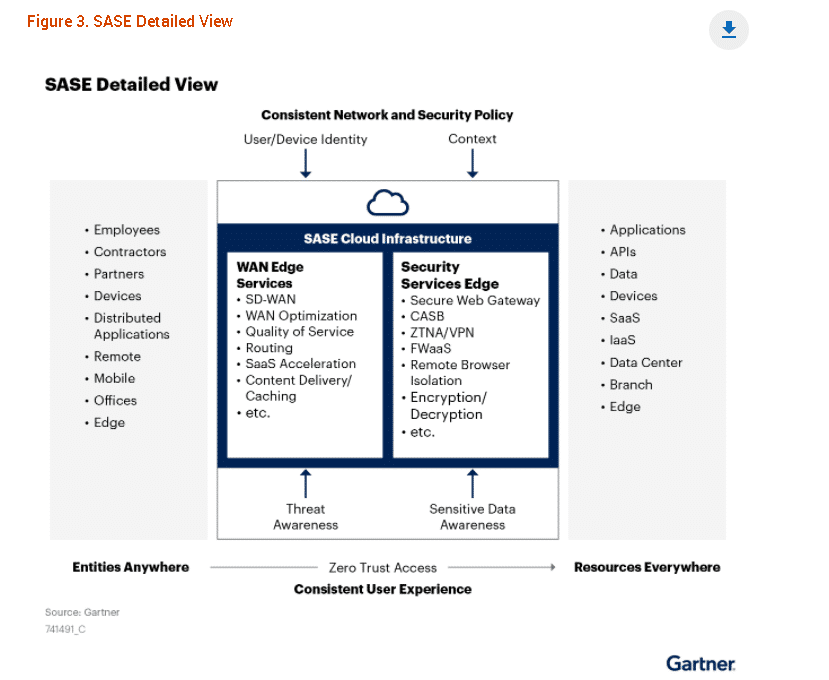
The SSE category was first introduced by Gartner in the “2021 Roadmap for SASE Convergence” report in March of 2021 (where it was named “Security Services Edge” with service in the plural) and later developed in several Hype Cycle reports issued in the summer. SSE is the half of secure access service edge (SASE) focusing on the convergence of security services; networking convergence forms the other half of SASE.
The Components of SSE
Like SASE, SSE offerings converge cloud-centric security capabilities to facilitate secure access to the web, cloud services, and private applications. SSE capabilities include access control, threat protection, data security, and security monitoring. To put that another way, SSE blends
– Zero Trust Network Access (ZTNA)
– Secure web gateway (SWG)
– Cloud access security broker (CASB)
– Firewall-as-a-service (FWaaS)
and more into a single-vendor, cloud-centric, converged service.
SASE vs SD-WAN What’s Beyond Security | Download eBookWhy Is SSE Important?
The argument of SSE is much of the same as for SASE. Legacy network security architectures were designed with the datacenter as the focal point for access needs. The cloud and shift to work-from-anywhere have inverted access requirements, putting more users, devices, and resources outside the enterprise network. Connecting and protecting those remote users and cloud resources require a wide range of security and networking capabilities. SSE offerings consolidate the security capabilities, allowing enterprises to enforce security policy with one cloud service. Like SASE, SSE will enable enterprises to reduce complexity, costs, and the number of vendors.
SSE Need To Be Cloud Services Not Just Hosted Appliances
The SSE vision brings core enterprise security technologies into a single cloud service; today’s reality will likely be very different. As we’ve seen with SASE, SSE is still in its early days, with few, if any, delivering a single, global cloud service seamlessly converging together ZTNA, SWG, RBI, CASB, and FWaaS.
And as with SASE it’s important to determine which SSE vendors are cloud-native and which are simply hosting virtual machines in the cloud. Running virtual appliances in the cloud is far different from an “as-a-service.” With cloud-hosted virtual appliances, enterprises need to think through and pay for redundancy and failover scenarios. That’s not the case with a cloud service. Costs also grow with hosted appliances in part because companies must pay for the underlying cloud resource. With a cloud service, no such costs get passed onto the user.
How Are SSE and SASE Similar?
Beyond an “A” in their names, what separates SSE from SASE? As we noted, SSE technologies form the security component of SASE, which means the security arguments for SSE are much the same as for SASE. With users and enterprise resources existing, well, everywhere, legacy datacenter-centric security architectures are inadequate. At the same time, the many security tools needed to protect the enterprise add complexity, cost, and complicate root-cause analysis.
SSE and SASE address these issues. Both are expected to converge security technologies into a single cloud service, simplifying security and reducing cost and complexity. With the primary enterprise security technologies together, security policies around resources access, data inspection, and malware inspection can be consistent for all types of access and users and at better performance than doing this separately. Both SSE and SASE should also allow enterprises to add flexible, cloud-based network security to protect users out of the office. And both are identity-driven, relying on a zero-trust model to restrict user access to permitted resources.
The most significant difference between SSE and SASE comes down to the infrastructure. With Gartner SSE, enterprises unable or unwilling to evolve their networking infrastructure have a product category describing a converged cloud security service. By contrast, SASE brings the same security benefits while converging security with networking.
SASE: Networking and SASE Better Together
But bringing networking and security together is more than a nice-to-have. It’s critical for a platform to secure office, remote users, and cloud resources without comprising the user experience.
Too often, FWaaS offerings have been hampered by poor performance. One reason for this is the limited number of PoPs running the FWaaS software, but the other issue was the underlying network. Their reliance on the global Internet, not a private backbone, to connect PoPs leaves site-to-site communications susceptible to the unpredictability and high latency of the global Internet. SSE solutions will face the same challenge If they’re to enforce site-to-site security.
Converging networking and security together also brings other operational benefits. Deployment times become much shorter as there’s only one solution to set up. Root cause analysis becomes easier as IT teams can use a single, queryable timeline to interrogate and analyze all networking and security events.
Cato is SASE
Cato pioneered the convergence of networking and security into the cloud, delivering the Cato SASE Cloud two years before Gartner defined SASE. Today, over 1,000 enterprises rely on Cato to connect their 300,000 remote users and 15,000 branches and cloud instances.
Cato SASE Cloud connects all enterprise network resources, including branch locations, the mobile workforce, and physical and cloud datacenters, into a global and secure, cloud-native network service. Cato SASE Cloud runs on a private global backbone of 65+ PoPs connected via multiple SLA-backed network providers. The backbone’s cloud-native software provides global routing optimization, self-healing capabilities, WAN optimization for maximum end-to-end throughput, and full encryption. With all WAN and Internet traffic consolidated in the cloud, Cato applies a suite of security services to protect all traffic at all times. Current security services include FWaaS, SWG, standard and next-generation anti-malware (NGAV), managed IPS-as-a-Service (IPS), and Managed Threat Detection and Response (MDR).
Deploy Cato SASE for Security, Networking, or Both – Today
Cato can be gradually deployed to replace or augment legacy network services and security point solutions:
- Transform Security Only: Companies can continue with their MPLS services, connecting the Cato Socket, Cato’s edge SD-WAN device, both to the MPLS network and the Internet. All Internet traffic is sent to the Cato Cloud for inspection and policy enforcement.
- Transform Networking Only: Companies replace their MPLS with the Cato SASE Cloud, a private global backbone of 65+ PoPs connected via multiple SLA-backed network providers. The PoPs software continuously monitors the providers for latency, packet loss, and jitter to determine, in real-time, the best route for every packet. Security enforcement can be done in the Cato SASE Cloud or existing edge firewall appliances.
And, of course, when ready, enterprises can migrate networking and security to the Cato SASE Cloud, enjoying the full benefits of network transformation. To learn more about Cato can help your organization on its SASE journey, contact us here.