ZTNA Alone is Not Enough to Secure the Enterprise Network
|
Listen to post:
Getting your Trinity Audio player ready...
|
ZTNA is a Good Start for Security
Zero trust has become the new buzzword in cybersecurity, and for good reason. Traditional, perimeter-focused security models leave the organization vulnerable to attack and are ill-suited to the modern distributed enterprise. Zero trust, which retracts the “perimeter” to a single asset, provides better security and access management for corporate IT resources regardless of their deployment location.
In many cases, zero trust network access (ZTNA) is an organization’s first step on its zero trust journey. ZTNA replaces virtual private networks (VPNs), which provide a legitimate user with unrestricted access to the enterprise network.
In contrast, ZTNA makes case-by-case access determinations based on access controls. If a user has legitimate access to a particular resource, then they are given access to that resource for the duration of the current session. However, accessing any other resources or accessing the same resource as part of a new session requires re-verification of the user’s access.
The shift from unrestricted access to case-by-case access on a limited basis provides an important first step towards implementing an effective zero trust security strategy.
Adopting ZTNA Alone Is Not Enough
The purpose of ZTNA is to prevent illegitimate access to an organization’s IT resources. If a legitimate user account attempts to access a resource for which they lack the proper permissions, then that access request is denied.
This assumes that all threats originate from outside the organization or from users attempting to access resources for which they are not authorized. However, several scenarios exist in which limiting access to authorized accounts does not prevent attacks.
Secure zero trust access to any user in minutes | ZTNA DemoCompromised or Malicious Accounts
ZTNA limits access to corporate resources to accounts that have a legitimate need for that access. However, an account with legitimate access can be abused to perform an attack.
One of the most common cyberattacks is credential stuffing attacks in which an attacker tries to use a certain individual’s compromised credentials for one account to log into another account. If successful, the attacker has access to an account with legitimate access whose requests may be accepted by a ZTNA solution. If this is the case, then an attacker can use this compromised account to steal sensitive data, plant malware, or perform other malicious actions.
Additionally, not all threats originate from outside of the organization. An employee could cause a data breach either via negligence or intentionally. For example, 29% of employees admit to taking company data with them when leaving a job. Legitimate users could also accidentally deploy malware on the corporate network. In 2021, 80% of ransomware was self-installed, meaning that the user opened or executed a malicious file that installed the malware. If this occurred on the corporate network, it would be within the context of a legitimate user account.
Infected Devices
Users access corporate resources via computers or mobile devices. While a ZTNA solution may be configured to look for a combination of a user account and a known device, this device may not be trustworthy.
Devices infected with malware may attempt to take advantage of a user’s account and assigned permissions to gain access to the corporate network or other resources. If malware is installed on a user’s device, it may spread to the corporate network via legitimate accounts.
ZTNA’s access control policies alone are not enough to protect against infected devices. Solutions also need to include device posture monitoring to provide more information about the risk posed by a particular device. Common device posture monitoring features include identifying the security tools running on the device, the current patch level, and compliance with corporate security policies. Ideally, a ZTNA solution should provide the ability to tune device posture access requirements based on the requested resources and to incorporate other valuable information, such as the device OS and location.
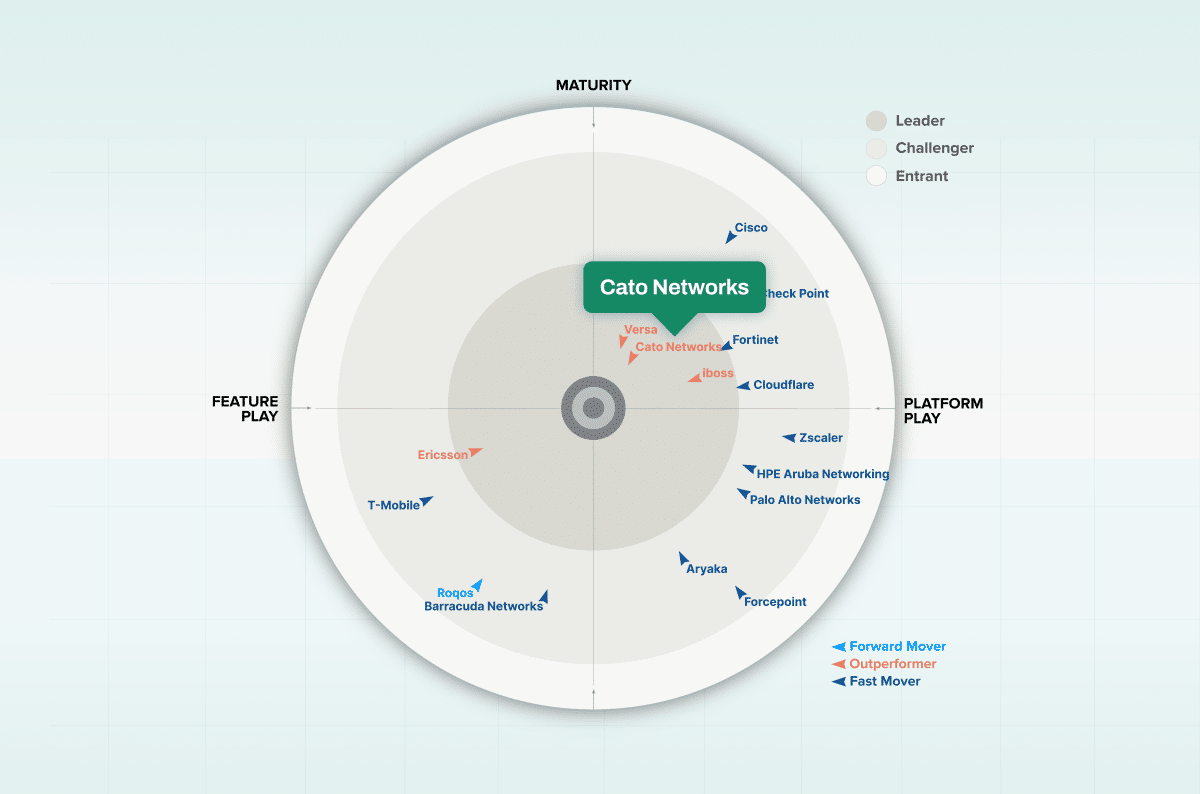
ZTNA Should Be Deployed as Part of SASE
ZTNA is an invaluable tool for providing secure remote access to corporate resources. Its integrated access controls and case-by-case grants of access offer far greater security than a VPN. However, as mentioned above, ZTNA is not enough to implement zero trust security or to effectively secure an organization’s network and resources against attack. An attacker with access to a legitimate account – via compromised credentials or an infected device – may be granted access to corporate IT assets.
Effective zero trust security requires partnering ZTNA’s access control with security solutions capable of identifying and preventing abuse of a legitimate user account. Next-generation firewalls (NGFWs), intrusion prevention systems (IPS), cloud access security brokers, and other solutions can help to address the threats that ZTNA misses.
These capabilities can be deployed as standalone solutions, but this often results in a tradeoff between performance and security. Deploying perimeter-based defenses requires routing traffic through that perimeter, which adds unacceptable latency. On the other hand, most organizations lack the resources to deploy a full security stack at all of their on-prem and cloud-based service locations.
Secure Access Service Edge (SASE) provides enterprise-grade security without sacrificing network performance. By integrating a full network security stack into a single solution, SASE enables optimized performance by ensuring that expensive operations – such as decrypting a traffic stream for analysis – are only performed once. Its integrated network optimization capabilities and cloud-based deployment ensure high network performance and reliability, especially when backed by Cato’s network of dedicated backbone links between PoPs.
ZTNA as a standalone solution doesn’t meet corporate network security goals or business requirements. Deploying ZTNA as part of a SASE solution is the right choice for organizations looking to effectively implement zero trust.