Cato CTRL™ Threat Research: When OpenClaw, Your AI Personal Assistant, Becomes the Backdoor

Table of Contents
|
Listen to post:
Getting your Trinity Audio player ready...
|
TL;DR
- A threat actor is selling root shell access to a CEO’s computer at a UK-based automation company for $25K in crypto.
- The listing’s real value isn’t the shell. It’s the CEO’s OpenClaw AI personal assistant, which contains personal conversations, company databases, Telegram bot tokens, and Trading 212 API keys.
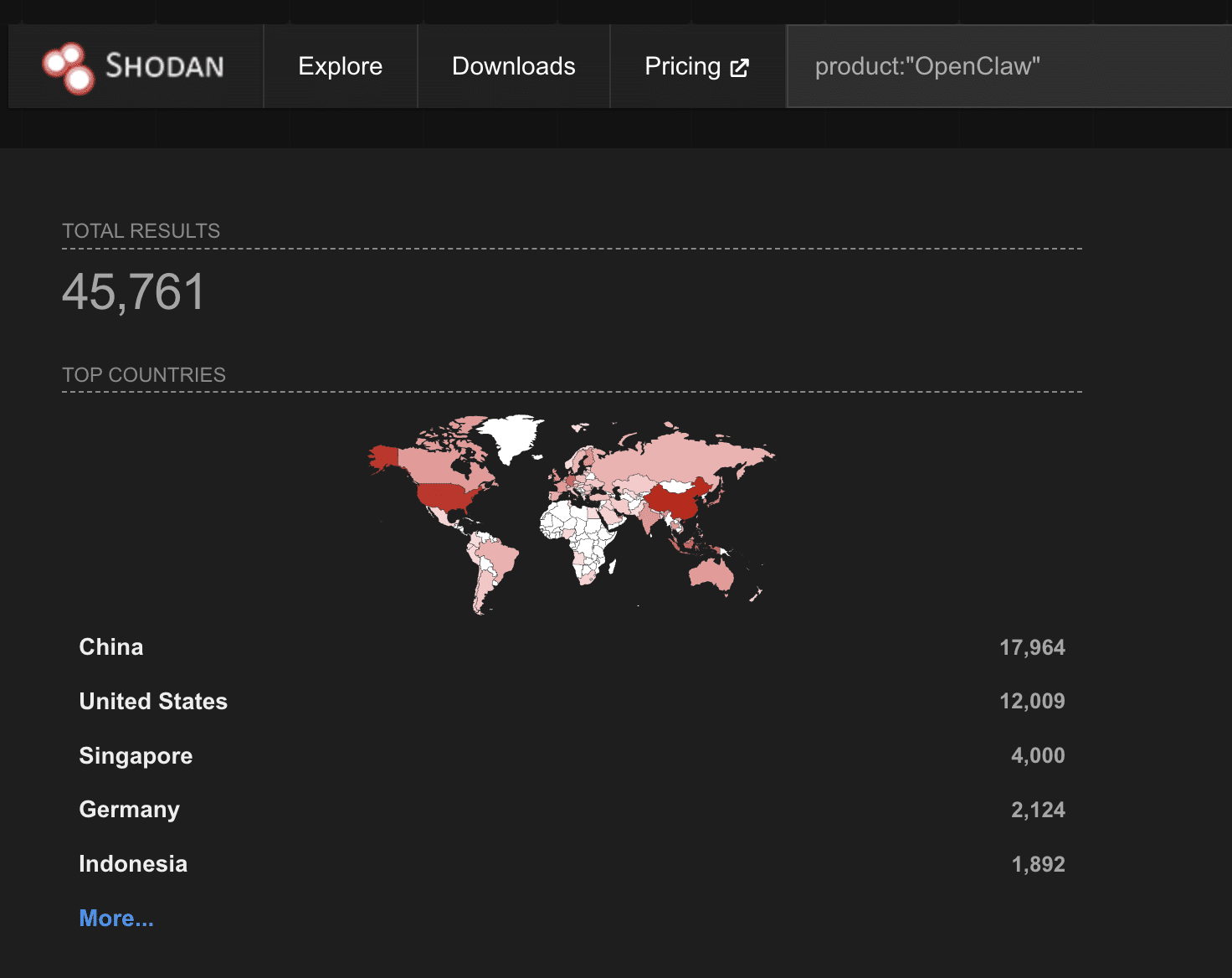
- With 45,000+ internet-facing OpenClaw instances (per Shodan) and 824 malicious skills discovered on ClawHub (per Koi), AI personal assistants are fast-becoming the most dangerous shadow IT in enterprise networks.
Executive Summary
Cato CTRL’s Vitaly Simonovich (senior security researcher) has identified a threat actor selling root shell access to a UK-based automation company through a compromised AI personal assistant based on OpenClaw.
The listing, which was posted on February 22, 2026 by a user called “fluffyduck” on BreachForums, advertises root shell access to the CEO’s computer for $25K in Monero (XMR) or Litecoin (LTC). But the shell isn’t the selling point. The real prize is the CEO’s OpenClaw instance. The AI personal assistant has been quietly accumulating the most sensitive data imaginable: personal conversations about family, hobbies, and finances; the company’s full production database; Telegram bot credentials; and active Trading 212 API keys for a trading bot the CEO is building.
The threat actor notes that “the CEO is actively chatting to the AI (he’s talking to it as I am writing this), making him a perfect target.”
This case represents what we believe is one of the first documented instances of an AI personal assistant being explicitly marketed as a backdoor on the dark web. It marks a shift in how threat actors perceive value: from selling raw access to selling ready-made intelligence.
The Cato SASE Platform enables customers to detect and block unauthorized AI personal assistants like OpenClaw with shadow AI discovery, DLP policies that prevent sensitive data exposure, and ZTNA controls that restrict unapproved AI applications from accessing corporate resources.
2025 Cato CTRL™ Threat Report | Download the reportTechnical Overview
Background: The Rise of OpenClaw
OpenClaw (originally known as Clawdbot, then briefly Moltbot) is a free, open-source AI personal assistant created by Austrian developer Peter Steinberger. The naming history alone tells you how fast this tool has evolved. It launched as Clawdbot in November 2025, renamed to Moltbot on January 26, 2026 after Anthropic’s legal team asked for the name to be changed due to trademark issues, then renamed to OpenClaw on January 29, 2026. During the name transition, scammers seized the abandoned GitHub/X handles for Clawdbot and launched fake $CLAWD tokens on Solana that hit a $16M market cap before collapsing.
After Steinberger launched OpenClaw, it quickly became one of the most viral AI tools. OpenClaw crossed 200,000+ GitHub stars in under three months, making it the fastest-growing software repository in GitHub history.
On February 15, 2026, OpenAI CEO Sam Altman announced that Steinberger was joining OpenAI to “drive the next generation of personal agents,” calling him “a genius with a lot of amazing ideas about the future of very smart agents interacting with each other to do very useful things for people.” OpenClaw itself transitioned to an independent open-source foundation.
The platform markets itself as “the AI that actually does things,” handling calendar management, flight bookings, email drafting, code execution, and essentially any task a human can perform on a computer. It runs locally, which means it has direct access to the host machine’s file system, network connections, browser sessions, and installed applications.
That local access is exactly what makes it so dangerous when a machine or the gateway is compromised.
OpenClaw’s Security Track Record
The security community hasn’t been kind to OpenClaw. The numbers tell the story:
Figure 1. Shodan view of publicly exposed OpenClaw instances
Key vulnerabilities for OpenClaw include:
- CVE-2026-24763 (CVSS 8.8): Docker sandbox escape via unsafe PATH environment variable handling, allowing authenticated users to execute arbitrary commands on the host.
- CVE-2026-25157 (CVSS 7.7): OS command injection through unsanitized secure shell (SSH) target strings, enabling arbitrary command execution via
-oProxyCommand=injection. - CVE-2026-25253 (CVSS 8.8): Token exfiltration leading to full gateway compromise. A malicious web page can steal an authentication token, establish a WebSocket connection, bypass authentication, and escape the container to execute commands on the host.
The Listing: What’s Being Sold
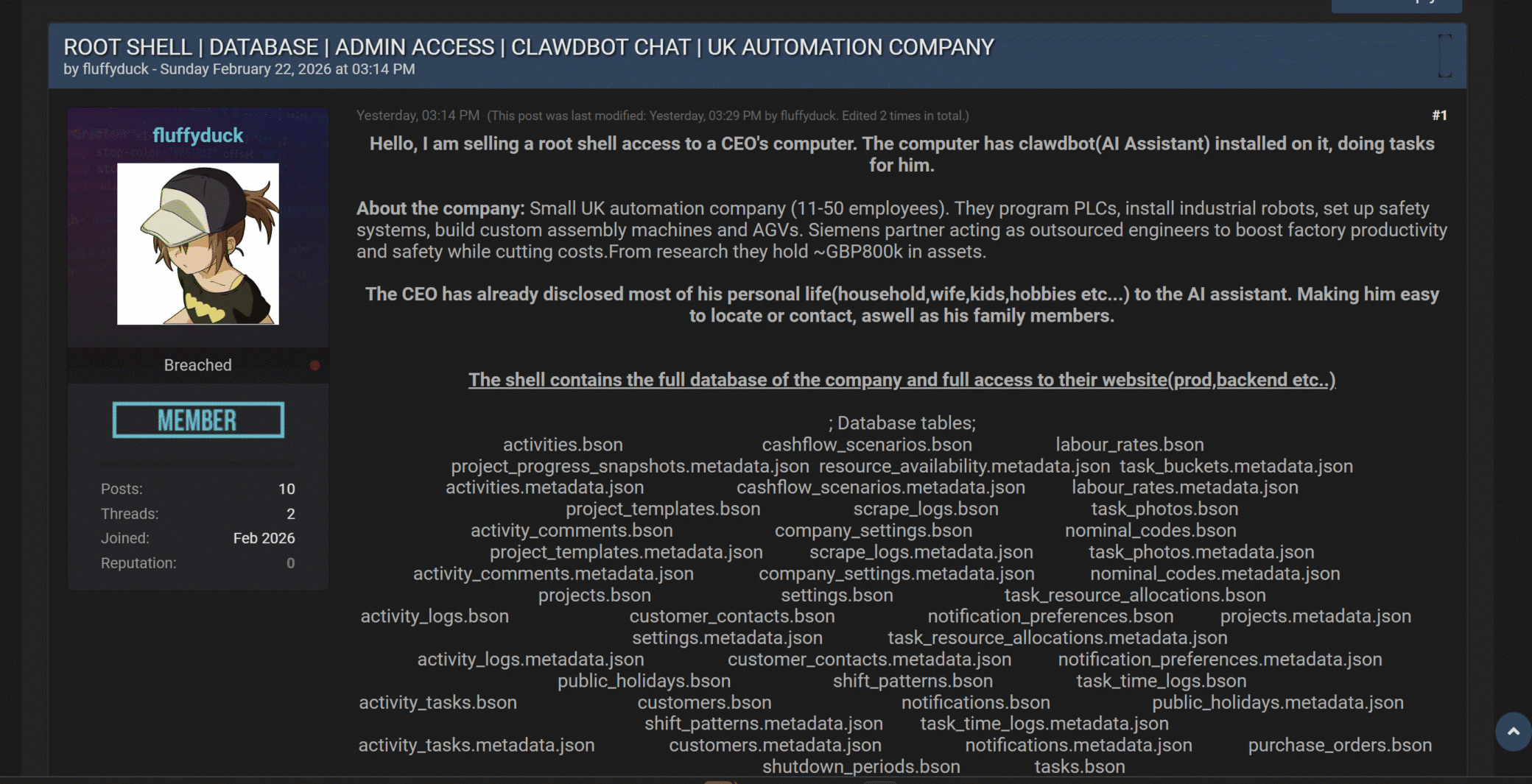
The BreachForums post, dated February 22, 2026, is titled:
ROOT SHELL | DATABASE | ADMIN ACCESS | CLAWDBOT CHAT | UK AUTOMATION COMPANY
Figure 2. The BreachForums listing by “fluffyduck” advertising root shell access bundled with AI assistant access
The seller, “fluffyduck” (joined February 2026, 10 posts, 0 reputation), describes the target as a small UK automation company with 11-50 employees that develops programmable logic controllers (PLCs), installs industrial robots, builds custom assembly machines and AGVs, and operates as a Siemens partner. The company holds approximately £800K in assets.
What the Buyer Gets
The listing bundles traditional access with something new: AI assistant access.
Traditional access:
- Root shell on the CEO’s computer.
- Full company database, including the production backend, in Binary JSON (BSON) format.
- Complete website access (production and backend systems).
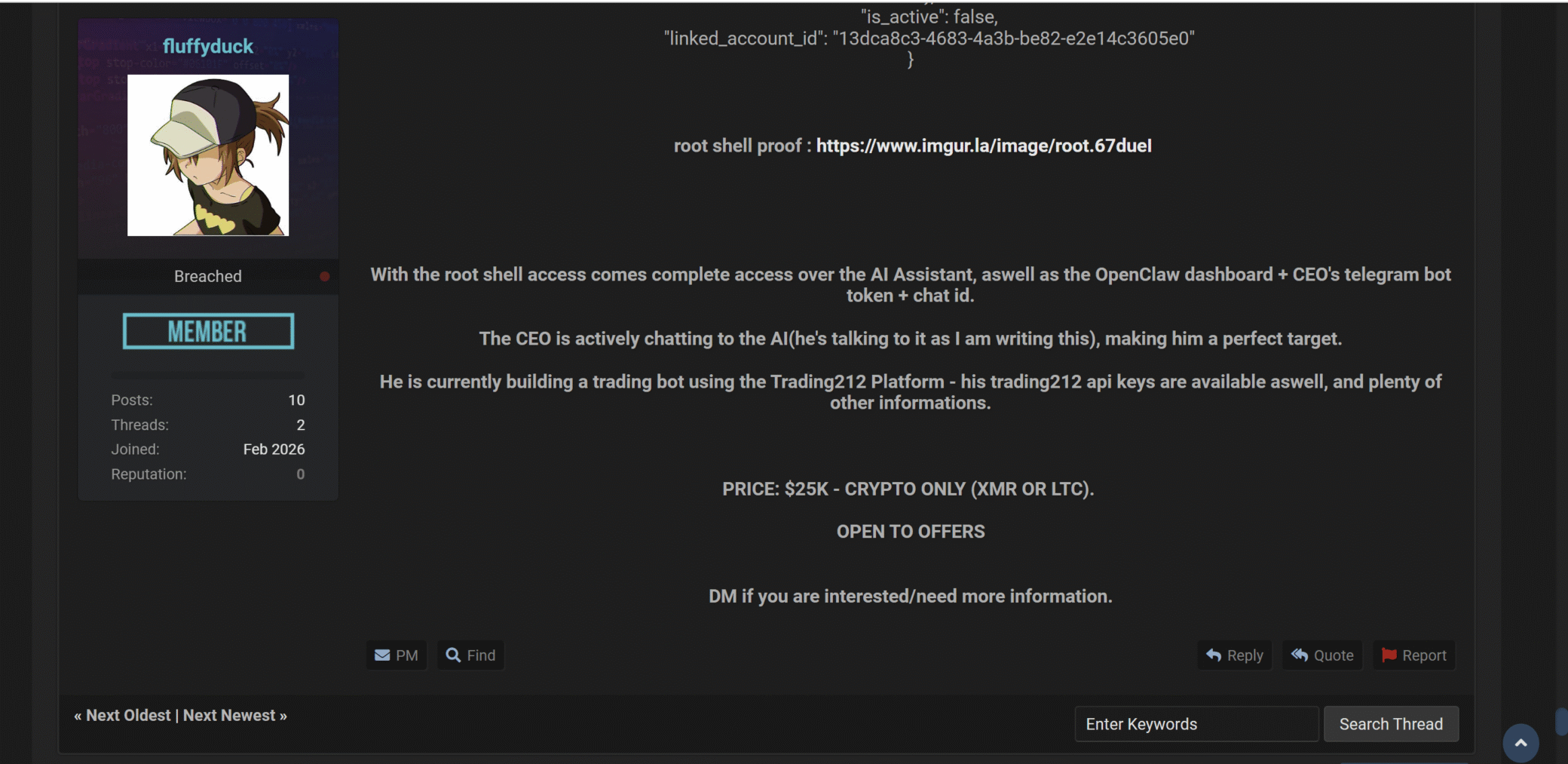
AI assistant access:
- Full OpenClaw AI assistant access (all conversations, context, and memory).
- OpenClaw dashboard credentials.
- CEO’s Telegram bot token and chat ID.
- Trading 212 API keys (CEO is actively building a trading bot).
- Personal information the CEO disclosed to the AI: household details, wife, children, hobbies, and family contacts.
The database scope includes tables for customer contacts, cash flow scenarios, labor rates, purchase orders, project progress, resource availability, shift patterns, notification preferences, and dozens more.
Figure 3. The second part of the BreachForums listing showing AI assistant access scope, trading platform API keys, and the $25K asking price
The asking price: $25K in Monero (XMR) or Litecoin (LTC) only. Open to offers.
Why This Matters: The AI Assistant as Intelligence Platform
This listing represents a fundamental shift in how compromised access gets monetized. Traditionally, initial access brokers (IABs) sell shells, remote desktop protocol (RDP) sessions, or virtual private network (VPN) credentials. The buyer then has to do their own reconnaissance, such as mapping the network, finding sensitive data, and escalating privileges.
An AI personal assistant changes that equation entirely.
The AI Already Did the Recon
When a CEO installs an AI assistant and uses it daily, the AI accumulates exactly the kind of intelligence a threat actor would spend weeks gathering:
- Personal details for social engineering: Family members’ names, hobbies, daily routines, and writing style (all volunteered by the CEO himself).
- Financial access: Trading platform API keys, bank account context, and business cash flow data.
- Communication channels: Telegram bot tokens, email context, and contact lists.
- Business intelligence: Project timelines, customer details, resource planning, and pricing data.
- Network topology: By running on the CEO’s machine with access to internal systems, the AI assistant effectively maps the corporate network through its integrations.
The threat actor doesn’t need to exfiltrate data. The CEO has already aggregated it into a single convenient location.
And here’s the kicker: OpenClaw stores everything in plain-text Markdown files under `~/.openclaw/workspace/`. This includes conversation logs, personal preferences, contact information, and API keys in a `.env` file. No encryption at rest. If you have root shell access, you have everything.
This is the shadow IT problem on steroids. The CEO likely installed OpenClaw on a work computer to boost productivity. That single decision created a centralized intelligence hub: SSO sessions, credential stores, file system, network access, and communication history, which gives a threat actor more context than months of lateral movement would.
Conclusion
The listing we found on BreachForums isn’t just about one compromised CEO at one small company. It’s a signal.
AI personal assistants are becoming the richest single target on any compromised machine. They aggregate credentials, personal details, business intelligence, and communication history into one place. They’re designed to be as permissive as possible to be useful. That design philosophy is exactly what makes them devastating when compromised.
The question for every CISO isn’t whether employees are using AI assistants on corporate devices. They are. The question is: do you have visibility into it and can you control what those AI assistants can access?
How many of your employees are running AI assistants with access to corporate networks, credentials, and sensitive data right now. Do you even know about it? It’s time for enterprises to take control of AI assistants before they lose control of their IT environments.
Protections
The Cato SASE Platform enables customers to detect and block unauthorized AI personal assistants like OpenClaw with shadow AI discovery, DLP policies that prevent sensitive data exposure, and ZTNA controls that restrict unapproved AI applications from accessing corporate resources.