The Post-Quantum Journey Begins: Enforce, See, and Evolve with Quantum-Safe SASE
Table of Contents
|
Listen to post:
Getting your Trinity Audio player ready...
|
Encrypted data has a shelf life, and for many organizations it must remain secret for years. The post-quantum risk is not a dramatic collapse of encryption, but a quieter threat: attackers harvesting encrypted traffic today so they can decrypt it in the future. That is why post-quantum readiness is increasingly a board and CEO-level responsibility, with the CISO leading execution, because quantum risk threatens long-term business stability, compliance expectations, and trust.
One practical first step already exists. TLS 1.3 provides security level 4 cipher suites that use post-quantum-cryptography-ready key establishment, reducing exposure to store-now, decrypt-later attacks while standards and ecosystems evolve. The harder part is the rollout across a complex enterprise, which requires visibility into where PQC protection is needed and consistent policy enforcement across users, sites, and applications. This is why Quantum-Safe SASE matters. It provides the centralized visibility and enforcement foundation to coordinate cryptographic upgrades and apply them gradually, starting where it matters most.
Why Post-Quantum Readiness Is on Every CISO’s Radar
Quantum progress is accelerating and recent milestones make it hard for security leaders to ignore. Google’s Willow chip (we covered this in a previous post) is one such milestone, and Microsoft’s Majorana-1 announcement shows continued advances toward scalable quantum systems. Analysts like Gartner warn that PQC is a multi-year transition, not a quick fix, and the immediate danger is the store-now, decrypt-later threat where attackers harvest encrypted traffic today to decrypt later. In this environment, cryptographic agility, visibility, and policy-driven enforcement matter far more than waiting for a single “quantum-safe” moment.
Is the Recent Quantum Hype by Google Willow’s Chip a Threat to RSA Algorithm? | Read the blogThe Quantum Readiness Burden
Most enterprise environments rely heavily on RSA and elliptic-curve cryptography (ECC), which secure VPNs, TLS sessions, and digital certificates but are fundamentally vulnerable to quantum attacks based on Shor’s algorithm. At the same time, symmetric and hash-based algorithms are not immune to quantum impact. While SHA-1 is already considered insecure, quantum search techniques reduce the effective strength of algorithms such as AES-128, accelerating long-term migration toward stronger configurations like AES-256.
When leadership asks whether the organization is quantum-ready, security teams face a difficult reality check. They must inventory cryptography across network traffic in transit, credentials and certificates, remote access, cloud connectivity, and management interfaces, then align dozens of vendors with different roadmaps and timelines. Coordinating upgrades, testing hybrid deployments, and enforcing new policies often becomes a multi-year effort, with limited visibility into what is protected, what is not, and where the highest risks remain.
Post-Quantum Cryptography Is a Transition, Not a Cutover
Post-quantum cryptography has moved from academic research into formal standardization, reinforcing why preparation must begin early rather than wait for a future breaking point.
The most significant milestone came when NIST finalized its first post-quantum standards as Federal Information Processing Standards. These include FIPS 203 (ML-KEM) for key establishment, FIPS 204 (ML-DSA) for digital signatures, and FIPS 205 (SLH-DSA) for hash-based signatures. Together, these standards define the cryptographic foundation that vendors and platforms will integrate over time, as described in NIST’s official Post-Quantum Cryptography program.
Crucially, NIST emphasizes that migration will be hybrid and phased. Classical and post-quantum algorithms will coexist for years as operating systems, browsers, devices, and security platforms adopt support unevenly. Some candidate algorithms have already failed during evaluation, reinforcing why measured, adaptable adoption is essential. This reality places a premium on platforms that can enforce stronger cryptographic posture where possible, maintain compatibility where required, and provide visibility into what is protected and what is not.
The IETF is also exploring what a next-generation TLS could look like in a post-quantum world, including an early “TLS 1.4” Internet-Draft that discusses PQC-oriented design ideas. (IETF Internet-Draft).
Understanding Hybrid PQC Handshakes in a SASE Environment
At the core of post-quantum readiness is the cryptographic handshake, the process that establishes session keys, authenticates peers, and determines whether encrypted traffic will remain confidential in the long term. In traditional TLS deployments, this relies on RSA or elliptic-curve mechanisms for key establishment and signatures, both of which are vulnerable to future quantum attacks.
Post-quantum cryptography changes this model, but not all cryptographic functions evolve at the same pace. Key establishment is the most urgent concern, because it directly protects data confidentiality and is the primary target of “store-now, decrypt-later” attacks. Digital signatures, which underpin authentication and trust, follow a different adoption curve due to ecosystem dependencies such as certificate authorities, browsers, and operating systems. This asymmetry is why most real-world deployments rely on hybrid handshakes, rather than attempting a full replacement.
A hybrid PQC handshake derives session keys from both classical and post-quantum mechanisms within the same TLS session. Instead of choosing between elliptic-curve key exchange or a post-quantum algorithm, the handshake combines both, ensuring that the session remains secure as long as at least one mechanism remains uncompromised. This approach preserves compatibility with existing clients and services while significantly reducing long-term cryptographic risk.
Enforcing TLS 1.3 with security level 4 cipher suites operationalizes this hybrid model. These cipher suites prioritize post-quantum-ready key establishment alongside classical mechanisms, enabling organizations to reduce exposure to future decryption attacks without disrupting connectivity. Importantly, this is not a static configuration. Hybrid cryptography is designed for algorithm agility, allowing security teams to adapt as standards mature, implementations evolve, or new weaknesses are discovered.
In a SASE architecture, hybrid handshakes become enforceable and observable at the network layer. Rather than assuming encryption is “strong enough,” the platform evaluates how each TLS session was negotiated, including which key establishment methods and signature algorithms were used. This allows policies to require post-quantum-ready handshakes for sensitive applications or users, while permitting controlled fallback where support is not yet available.
Equally important, SASE enables continuous verification. Client connections are inspected to confirm that a post-quantum or hybrid handshake was successfully negotiated, not merely that TLS is present. This closes a critical blind spot in many enterprise environments, where encryption exists but does not meet long-term security objectives. By tying handshake analysis, policy enforcement, and visibility together, hybrid PQC moves from a theoretical cryptographic concept into a practical, manageable part of the enterprise security posture.
Introducing Quantum-Safe SASE: Enforce, See, and Evolve
To support this transition, Cato is introducing a Quantum-Safe SASE approach that combines enforcement, visibility, and gradual adoption, without requiring enterprises to change everything at once.
Enforce post-quantum-ready TLS where it matters
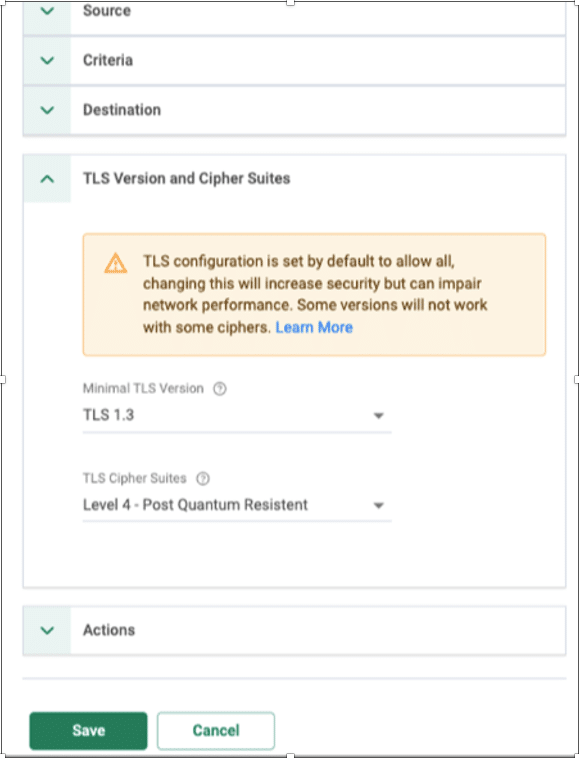
By enforcing TLS 1.3 with security level 4 as shown in Figure 1, organizations can apply post-quantum-ready hybrid cipher suites at the network level. This enables sensitive traffic paths to be protected today while maintaining interoperability with environments that are not yet PQC-capable.
Figure 1. Enforcing TLS 1.3 security level 4 for quantum readiness.
Gain visibility into quantum readiness posture
Quantum readiness is not binary. Quantum-Safe TLS Inspection (TLSi) provides visibility into the cryptographic posture of TLS connections, helping organizations understand where post-quantum protections are enforced, where hybrid cryptography is used, and where classical cryptography remains.
Adopt gradually, starting with the crown jewels
Most enterprises will not enforce post-quantum protections everywhere on day one. With SASE-based policy granularity, organizations can apply quantum-safe requirements incrementally using familiar controls such as source, destination, user, site, and application. This allows teams to start with their most sensitive assets and expand coverage as post-quantum support matures across the ecosystem.
Equally important is making sure endpoint connections actually negotiated a PQC-capable handshake. A practical SASE rollout verifies the TLS handshake on client connections, detects whether a session used a post-quantum or hybrid cipher suite, and reports or enforces policy when a client or server lacks PQC support. In other words, protection must cover the ZTNA client-to-PoP connection as well as the PoP-to-destination leg. By combining client capability detection, handshake verification, and posture visibility, teams can safely begin with crown-jewel apps and users, see where gaps remain, and widen coverage without disrupting business continuity.
A Practical Path Forward
Post-quantum readiness is not about predicting when quantum computers will break encryption. It is about recognizing that cryptographic transitions are slow, complex, and unavoidable.
By combining modern TLS enforcement, clear visibility, and policy-driven gradual adoption, a SASE-based approach allows enterprises to reduce long-term risk today while staying adaptable for what comes next. With Cato SASE, organizations gain a practical, controlled path through the post-quantum transition, focused on progress rather than panic.