Where Cato Sits in the AI Economy
|
Listen to post:
Getting your Trinity Audio player ready...
|
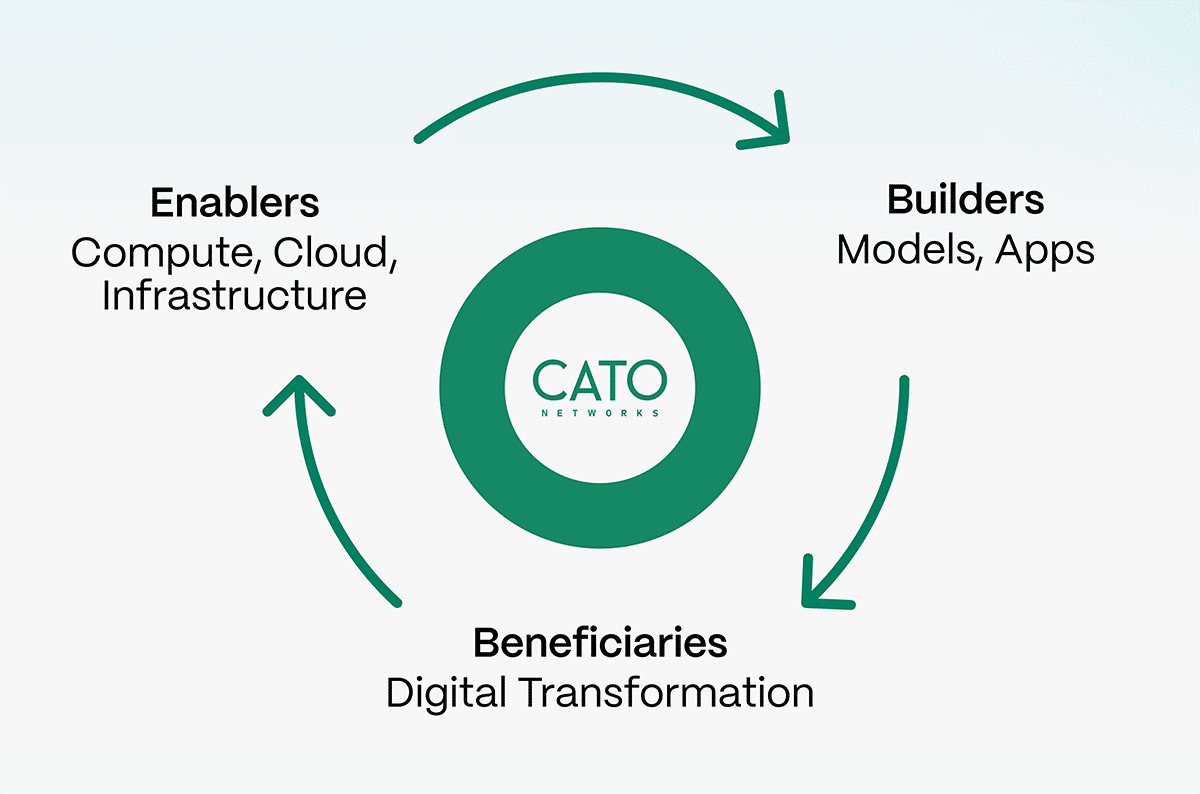
Every major technological shift reshapes the landscape, creating both winners and losers. AI will be no different. The key question is which companies are positioned to capture the value it generates, and which ones may fall behind as it unfolds.
If you look at previous technology shifts, the winners were not always the companies building the most visible products. They were often the ones that enabled the shift to happen in the first place, or those that benefited from the structural changes it created.
In the early days of the internet, most of the attention was on websites and portals. But the lasting value was created by two types of companies: those that enabled the internet to scale, like Cisco, and those that were built to take advantage of it, like Amazon. The cloud followed the same pattern. Companies like AWS enabled the shift, while others, like Snowflake and Datadog, emerged as direct beneficiaries.
AI is following the same pattern, but with one important difference: some categories span both sides. Cybersecurity is one of them.
You Cannot Have AI Without Cybersecurity
Enterprises will not deploy AI at scale without security and governance.
AI introduces a different class of risk. Data is no longer just stored or transmitted; it is actively processed through prompts, models, and agents. Sensitive information can be exposed in ways that are difficult to predict. Autonomous systems can take actions that are hard to constrain. Without governance and enforcement, AI is not something most organizations can safely use.
That makes cybersecurity a prerequisite for AI adoption. In that sense, it plays a role similar to compute or energy. It makes AI consumable for the enterprise and turns cybersecurity companies into AI enablers.
The Network Is Where This Has to Happen
Once you accept that AI requires security to be usable, the question becomes where is the best place for AI security to live.
AI interactions are continuous and dynamic. They require inspection and enforcement in real time, with full context. This cannot be done effectively after the fact, and it cannot be done reliably by stitching together multiple disconnected systems.
The only place where all traffic converges, where you have full visibility and can enforce decisions inline, is the network. Security that is not built into the network will always be limited. It will lack context, introduce latency, or depend on external processing that breaks consistency.
At Cato, we built a global private network and integrated security into it from the beginning. That means we can inspect traffic and enforce policies inline, everywhere, in real time. In the context of AI, this is more than an advantage. It is a requirement.
This also creates a clear separation from others in the market. Not every vendor owns and operates a network (backed by the Cato Commitment). And if you don’t control the network, you are fundamentally constrained in how effectively you can secure what flows through it.
Why the Delivery Model Matters: SASE in the AI Era
Owning the network is necessary, but it is not sufficient. How that network security is delivered also matters.
Enterprises are not looking to add more fragmented security tools. They are already dealing with increasing complexity, and AI will only accelerate that. As organizations adopt AI, they will need to move faster, connect more environments, analyze more traffic patterns (Human to AI, Human to agent, agent to agent) and enforce policies consistently across them. This increases the need for agility, not more point solutions.
This is where SASE becomes critical.
A true platform-based SASE delivers networking and security as a single, integrated system. This is fundamentally different from portfolio-based approaches that stitch together multiple products. In practice, those approaches increase operational complexity and cost at the exact moment enterprises need to move faster.
AI will amplify this gap.
As AI adoption grows, so will the demands on infrastructure and security budgets. CISOs will be asked to do more, not less, often within constrained or rebalanced budgets. This creates a natural tailwind for architectures that are both more efficient and more scalable.
Platform-based SASE fits this requirement. It allows enterprises to enforce security consistently, reduce complexity, and adapt more quickly to changing needs.
In the AI era, this is not just a cost or operational consideration. It becomes a strategic advantage.
AI Will Also Reshape the Threat Landscape
The second part of the equation is just as important. AI is not only something that needs to be secured. It is also changing the nature of threats. Attackers are becoming more automated, more adaptive, and more scalable. We are moving toward a world of agentic attacks, where adversaries can operate continuously and at machine speed.
This is a fundamental shift in how attacks are created and executed, and it means defenders must also harness AI, along with the infrastructure to run it at scale.
This is where cybersecurity becomes a beneficiary of AI. Demand will increase because the problem becomes more complex. But not all companies will be equally positioned to respond. Those that are already investing in AI, with the infrastructure to run it inline, and moving early will have a clear advantage.
Where Cato Fits
When you put these dynamics together, the positioning becomes clear.
Cato is an enabler of AI. We provide the security and governance enterprises need to adopt AI safely, and we do it at the network level, where it can be enforced in real time. At the same time, we are a beneficiary of AI. The threat landscape is evolving rapidly, and we are using AI, along with the necessary compute infrastructure, to address that evolution now.
This is not theoretical. It is reflected in what we are building. With capabilities like Cato Neural Edge, where we embed GPU-powered processing into our network, we are bringing AI directly into the enforcement layer. This allows us to analyze and act on traffic as it flows, rather than relying on external systems.
We are also expanding how enterprises can govern and secure their use of AI across users, applications, and agents.
These are not separate efforts. They are part of the same mission.
Execution Will Separate the Winners
It is easy to describe a favorable position in the AI economy. It is much harder to execute against it. The advantage comes from building the right architecture early and continuing to invest ahead of where the market is going.
AI will amplify differences between architectures. Approaches that rely on fragmented systems or external dependencies will become harder to sustain. Approaches that integrate networking, security, and AI into a single system will scale more naturally.
This is where first-mover advantage matters.
At Cato, we have been building toward this for some time. The current wave of AI is accelerating the need for it.
Looking Ahead
AI will create significant opportunities, but it will not do so evenly. The companies that benefit most will be those that both enable AI adoption and are positioned to respond to the changes it brings.
Cybersecurity sits at this junction.
Within cybersecurity, we believe Cato is uniquely positioned to do both and is already executing on that path.