Global Campaign Discovered with Modbus PLCs Targeted and China-Geolocated Infrastructure Observed

Table of Contents
|
Listen to post:
Getting your Trinity Audio player ready...
|
Executive Summary
From September – November 2025, Cato Networks threat researchers observed a global campaign involving suspicious Modbus/TCP (transmission control protocol) activity against internet-exposed PLCs (programmable logic controllers). The targeted footprint spanned 70 countries and 14,426 distinct targeted IPs, with the largest share of activity in the United States. The activity blended large-scale automated probing with more selective patterns that suggest deeper device fingerprinting, disruption attempts, and potential manipulation paths when PLCs are reachable from the public internet.
Across the three months, we saw thousands of requests sourced from a broad and frequently low-reputation infrastructure set, alongside a small subset of higher-intent infrastructure of interest including sources geolocated to China. While it’s unclear who the threat actors are, these findings reinforce a simple takeaway: exposing Modbus to the internet materially increases both operational risk and the likelihood of follow-on attack activity.
Technical Overview
When Modbus Writes Affect the Physical World
Modbus was built for trusted industrial networks, not the public internet. When a Modbus-enabled PLC is exposed externally, a remote threat actor can move quickly from discovery to action: fingerprint the device, read controller data, and if writes are reachable, change register values that influence physical processes.
To demonstrate how quickly exposed Modbus access can translate into real-world impact, we built a proof of concept (PoC) based on MITRE’s Wildcat Dam simulation. In the video below, a threat actor first fingerprints the PLC to confirm it controls the dam, then issues Modbus write requests that manipulate the water-level thresholds used by the control logic. As a result, the water level rises abnormally fast and reaches the third threshold at 255%, while the threat actor also forces dam door states to change (shifting doors between open and closed in ways that could defeat normal operator expectations). We show how against the same techniques, with the Cato SASE Platform, we were able to fingerprint and block such write attempts.
Modbus Register Fundamentals and Why 0x03 and 0x10 Matter
From a Modbus perspective, PLC memory is accessed via coils and registers. Registers commonly represent 16-bit values and are split into Input Registers (read-only) and Holding Registers (read/write).The Modbus PDU (protocol data unit) specification outlines the functions in detail.
In this report, the critical functions are:
- 0x03 Read Holding Registers: Reads values from read/write register space, often configuration or controller data.
- 0x2B/0x0E Read Device Identification: Returns vendor, product, and version metadata that is useful for inventory and valuable for attacker targeting.
- 0x10 Write Multiple Registers: Writes to holding registers. When exposed, this can directly change device behavior.
Method
We reviewed inbound Modbus/TCP telemetry observed over three months, focusing on:
- Function code frequency and sequencing.
- Consistency versus variability of PDU arguments, where static patterns strongly indicate automation.
- Bulk-read lengths near protocol limits and repeated high-rate request patterns.
- Single-source, single-target behaviors.
- Enrichment using AbuseIPDB, VirusTotal, and internal correlation such as multiple IPS triggers per source.
Results and Analysis
Across three months of inbound Modbus/TCP telemetry, we observed a progression of suspicious activity patterns, from broad automated reconnaissance to higher-risk behaviors that can degrade availability or manipulate device state. Table 1 summarizes the key behaviors, what we observed, and the suspected technique behind each pattern.
Notably, a large portion of the infrastructure behind this activity appears “unknown” in public reputation services at the time of observation, with many source IPs carrying low or zero AbuseIPDB scores and only limited VirusTotal vendor flags. This is consistent with scanning operations that rely on fresh or rotating infrastructure, where reputation signals often lag behind active probing.
We interpret the behavioral analysis column based on protocol patterns and repetition. Infrastructure location and geolocation are not attribution because threat actors may route through proxies, VPS (virtual private server) providers, or compromised hosts.
Below, we dive into a more detailed technical breakdown of the suspicious Modbus traffic in the wild that we observed.
- Recon at scale: Read Holding Registers dominates: Read Holding Registers (0x03) overwhelmingly dominated inbound Modbus traffic, with ~235.5K requests from 233 source IPs. This discovery reflects active attempts to read holding-register space from exposed PLCs. In our telemetry, nearly half of these sources correlated with multiple IPS detections, suggesting many scanners are part of broader suspicious activity rather than benign measurement.
- Fingerprint then targeted read: scripted PLC identification and data pull: We observed a consistent two-step sequence: basic device identification (0x2B/0x0E, payload 0100) paired with a fixed 0x03 register read (e.g., start 0xB414, quantity 8). The parameters were rigid, which is characteristic of automation. This pattern aligns with a practical workflow: confirm the PLC type, then retrieve a specific register range that is likely meaningful for that vendor or model.
- Bulk reads near the limit: behavior consistent with disruption: A notable portion of requests attempted near-maximum bulk reads, often 124 registers out of 125. One source executed a high-rate sequence that resulted in ~158.1K reads against a single target in rapid succession. While we cannot validate device-side impact without access to the PLC, the request size and rate are consistent with resource exhaustion attempts intended to degrade responsiveness or availability.
- Expanded device identification – small set, higher intent: Basic device identification (0100) was common, but the expanded identification payload (0200) was rare and concentrated: 175 requests from six IPs. Most of these sources geolocated to China and had strong reputation signals. We treat this as higher-intent reconnaissance infrastructure of interest, while noting again that geolocation does not establish operator identity.
- Write Multiple Registers: systematic write attempts: All inbound write activity originated from a single source IP and totaled 3,240 requests. The writes followed a consistent structure, starting at 0x0BB8 and writing 27 to 122 registers. This regularity is strongly consistent with automation and represents the highest-risk category we observed, since write access can directly influence PLC state and physical outcomes.
Sector Distribution of Observed Targets
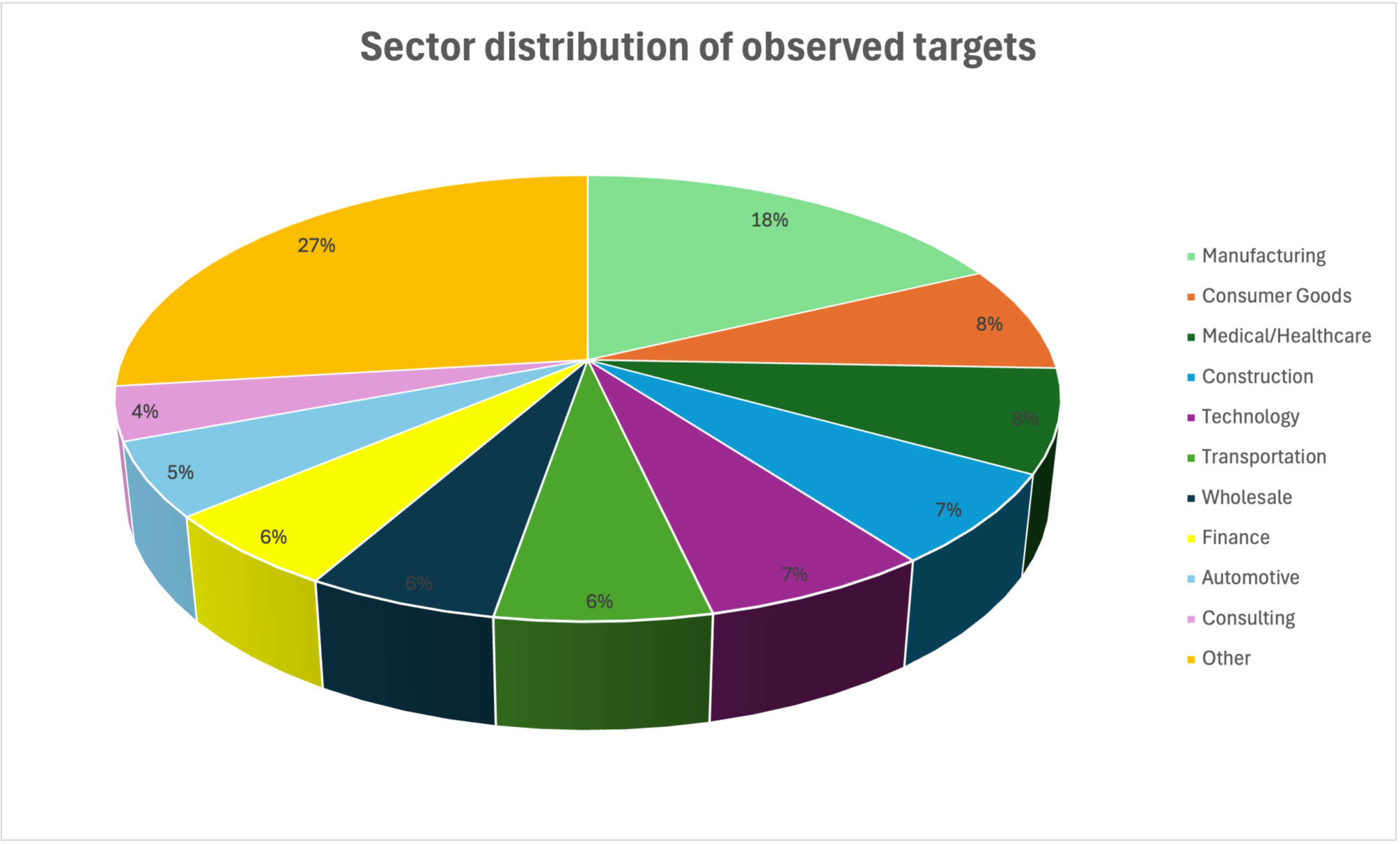
Figure 1 summarizes the type of organizations whose internet-exposed Modbus endpoints were targeted by the suspicious inbound activity. The distribution is broad and appears opportunistic. Manufacturing (18%) is the top sector targeted, followed by smaller shares across healthcare, construction, technology, transportation, finance, and a long tail of additional sectors grouped under Other (27%). The manufacturing concentration is consistent with where Modbus-enabled PLCs are most commonly deployed, particularly in OT-reliant environments, which increases the likelihood of exposure and subsequent probing. We also saw a small representation of government organizations, mainly municipalities.
Figure 1. Sector distribution of observed targets associated with suspicious Modbus probing
Geographic Distribution of Observed Targets
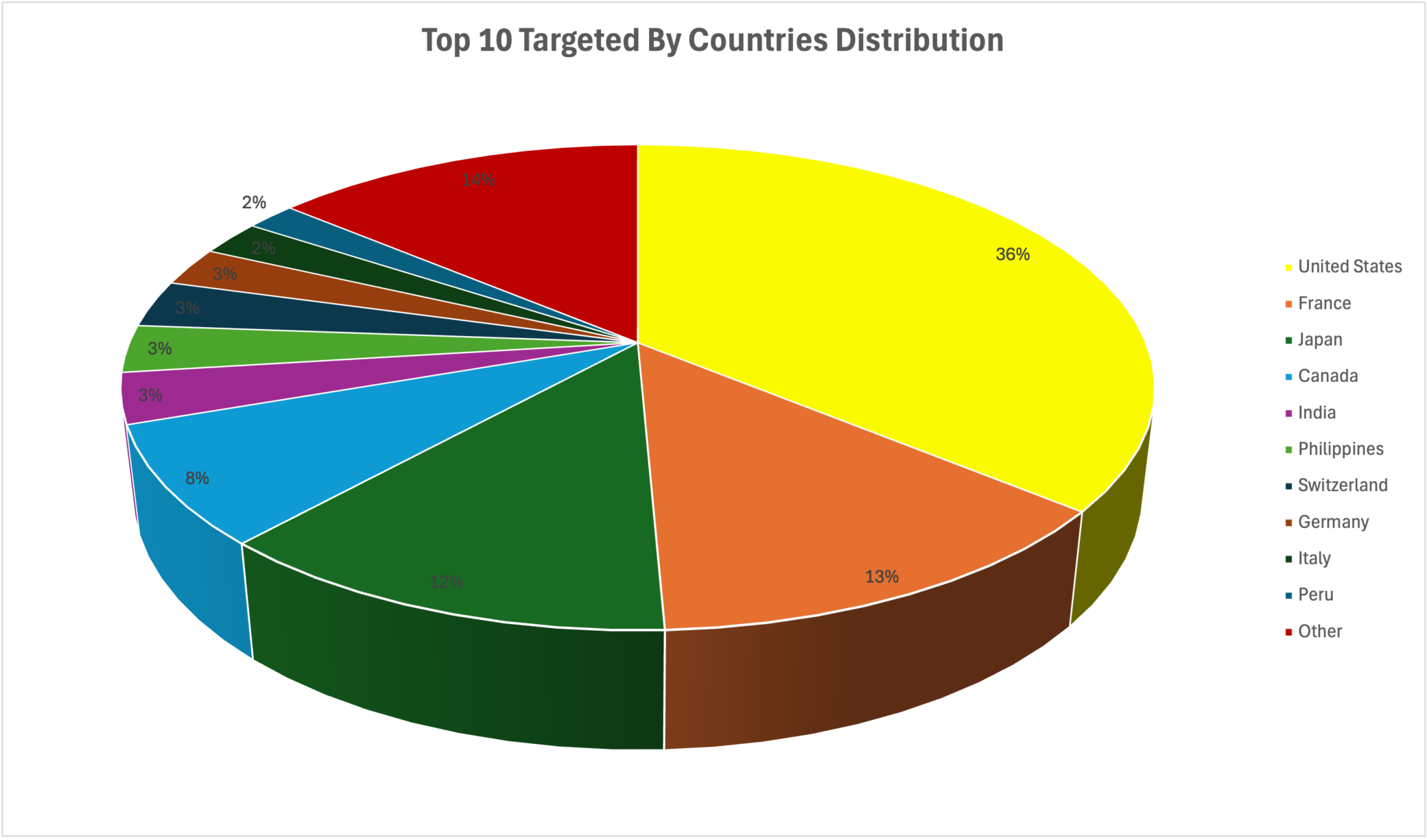
Geographically, the suspicious inbound Modbus activity spans 14,426 distinct targeted IPs across 70 countries, but it is heavily concentrated. Figure 2 shows that the Top 10 countries account for 86% of targeted IPs, and the top three alone (US, France, and Japan) represent 61% of targeted IPs combined.
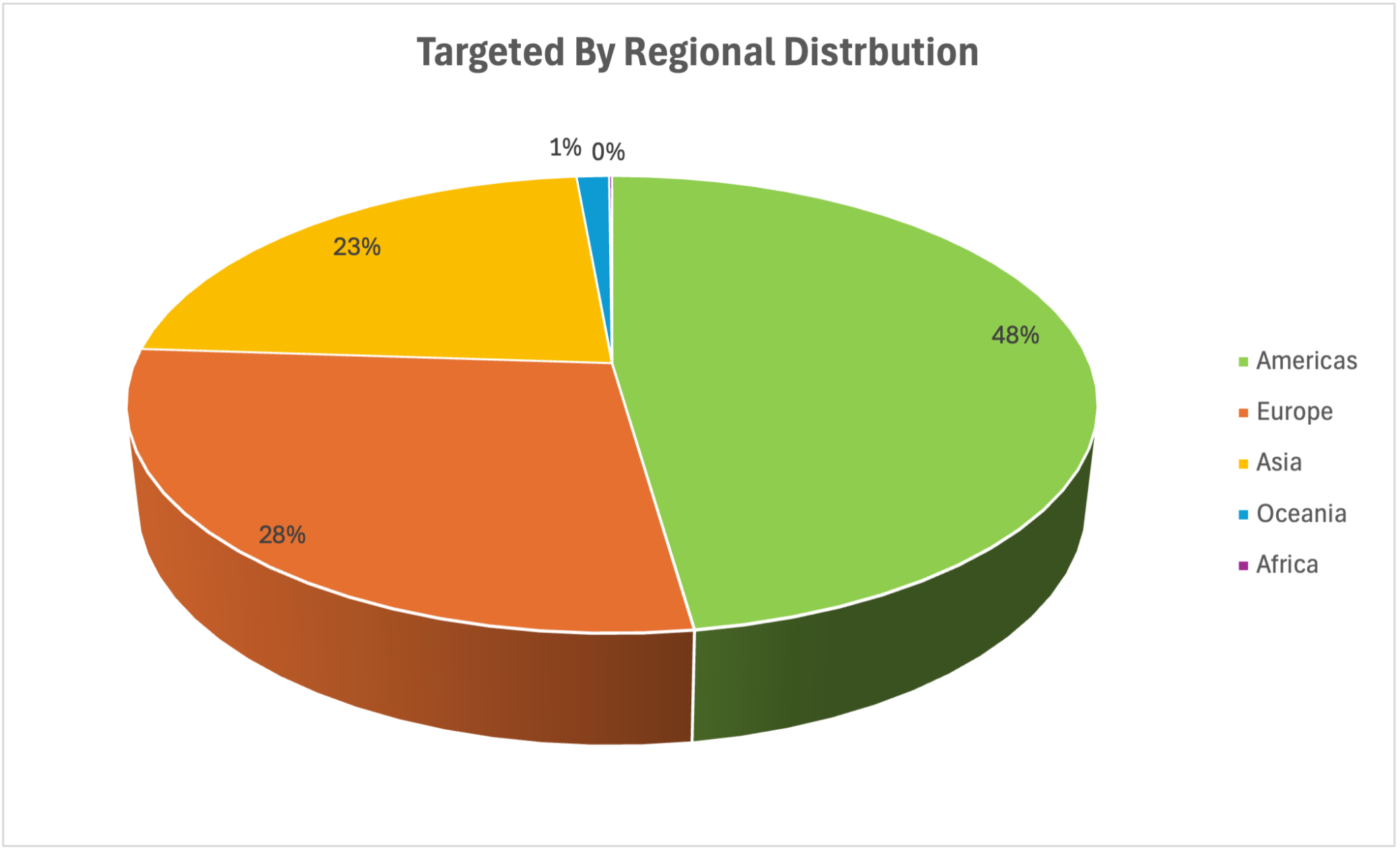
At the regional level (Figure 2), the Americas leads (48%), followed by Europe (28%) and Asia (23%).
Figure 2. Top 10 targeted countries observed
Figure 3. Targeted regions observed
Key Findings Over Three Months of Observation (September – November 2025)
- Recon at scale: 233 source IPs generated ~235.5K inbound requests dominated by Read Holding Registers (0x03).
- New and low-reputation infrastructure: Many source IPs had low or zero public reputation scores, consistent with fresh or rotating scanning hosts.
- Identifying then probing: Read Device Identification (0x2B/0x0E) followed by a fixed register read, consistent with scripted targeting.
- Disruption and impact attempts: DoS-like bulk reads near the maximum request size, plus 3,240 Write Multiple Registers (0x10) requests from a single source.
- Higher-intent infrastructure of interest: Only six IPs used the rare expanded device identification (0200) technique.
- Geographic spread: 70 countries targeted, led by the U.S. (36%).
Conclusion
Our findings show that internet-exposed Modbus devices face repeated hostile interest that ranges from broad discovery and device profiling to attempts at disruption and direct manipulation. While the threat actors are unknown, we know that this activity spans multiple industries, with manufacturing most represented, and is geographically widespread across dozens of countries.
The core recommendation remains the same: do not expose Modbus to the public internet. Where exposure exists, enforce segmentation by isolating OT from IT and the public internet, strict access controls to limit Modbus reachability, and pair that with threat prevention to stop both early-stage probing and higher-impact actions.
Protections
In the Wildcat Dam demo previously shown, Cato Threat Protection is capable of blocking the threat actor’s Modbus fingerprinting and write attempts, preventing access to PLC control logic.
Additionally, Cato Threat Protection helps reduce risk from the specific behaviors observed in this report, including:
- Device fingerprinting using Read Device Identification (0x2B/0x0E).
- Scripted fingerprint-then-read sequences, such as basic identification followed by a fixed register read.
- DoS-like bulk reads that request near-maximum register ranges at high rate.
- Inbound write activity (0x10), which we monitor, and which can be blocked by policy to prevent unsolicited register writes from the internet.
We recommend blocking unsolicited inbound Modbus writes by default and allowing Modbus access only from explicitly trusted sources.
Resources
- For a deeper look at how Cato Threat Protection detects and blocks OT-focused threats in practice, read this blog.
- For the full list of Indicators of Compromise (IoCs) related to this research, please contact the Cato MDR team for additional details and context.