Cato IoT/OT Security extends protection to IoT and OT environments, providing real-time device discovery and classification, granular policy enforcement, and comprehensive threat prevention. As a native feature of the Cato SASE Cloud Platform, Cato IoT/OT Security eliminates complex integration and simplifies management.
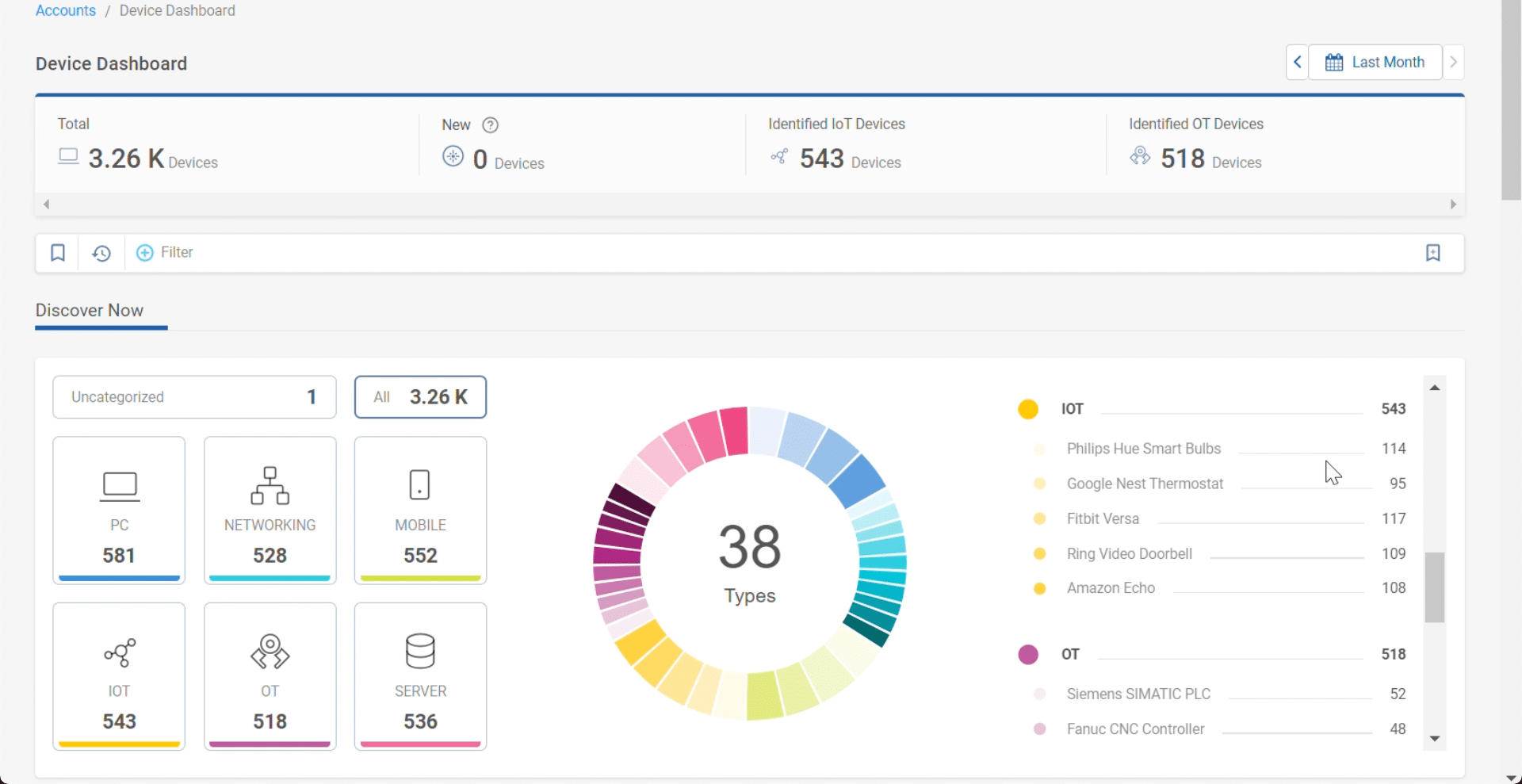
Cato IoT/OT Security, natively built into the Cato SASE Cloud platform, delivers instant, effortless visibility across IT, IoT, and OT environments with no integration required. Purpose-built and trained AI and ML fingerprint devices on the network, mapping their type, manufacturer, and version. Eliminating IoT/OT blind spots enables a complete understanding of this critical attack surface and serves as a foundation for a robust IoT/OT security strategy.

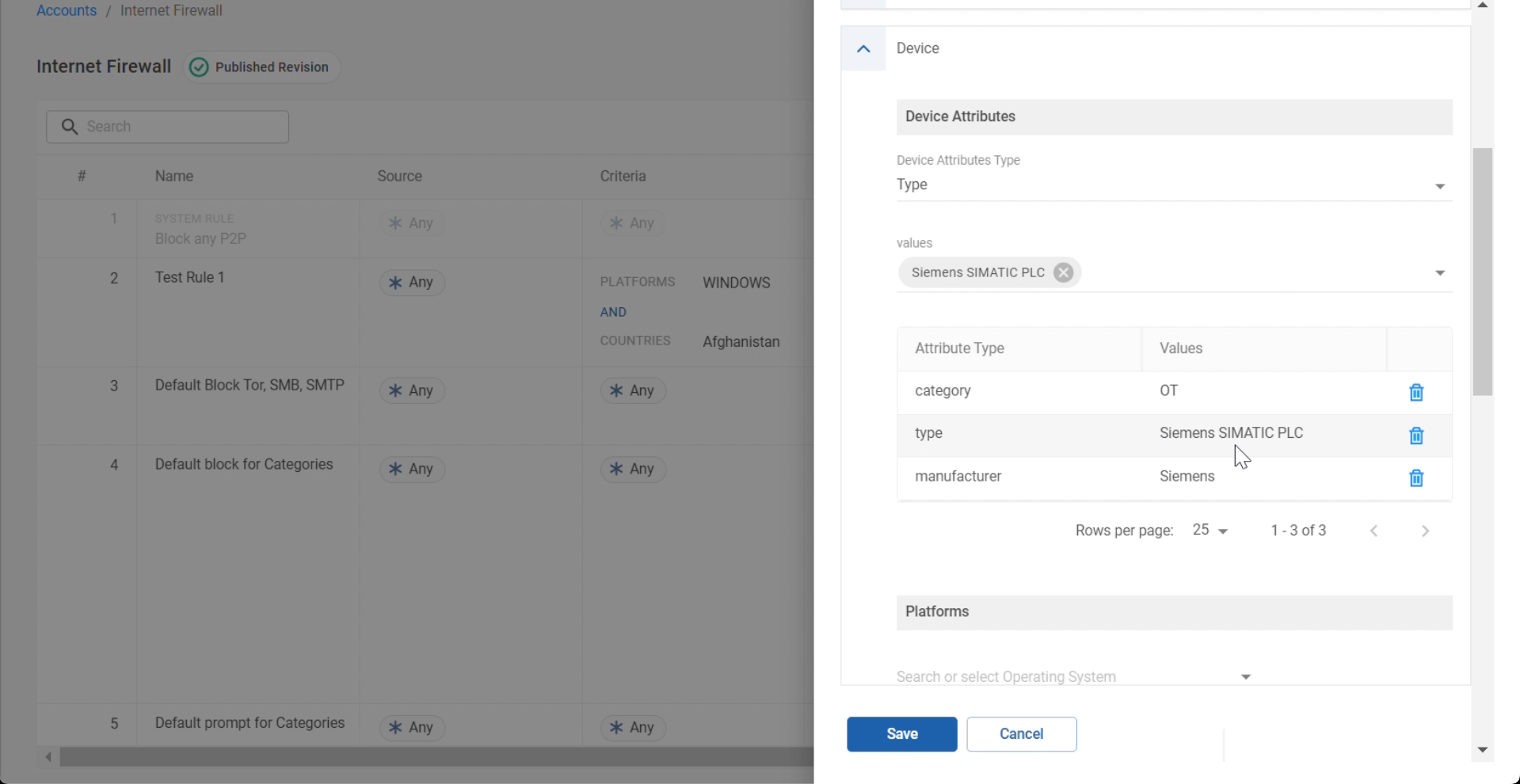
A complete IoT/OT Security strategy requires more than visibility, and IT teams need the ability to efficiently control IoT/OT device access to internal and external resources. Cato IoT/OT Security empowers IT teams to achieve this. Access policies can be set based on specific device characteristics or, for efficiency, based on grouping by type, manufacturer, or model. Controlling IoT/OT network access helps secure the enterprise network and dramatically reduce the attack surface.
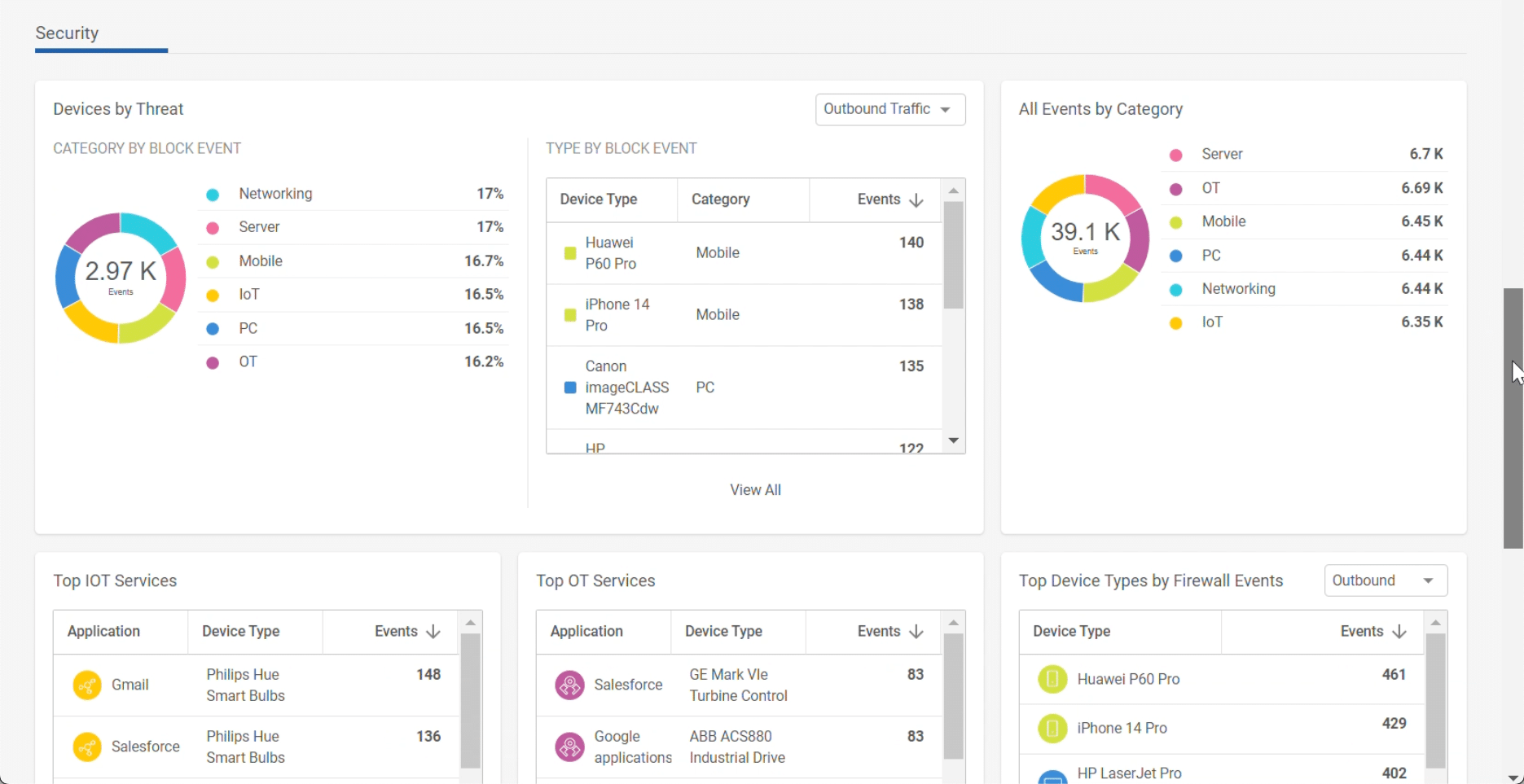
Beyond policy enforcement, Cato IoT/OT Security benefits from the threat prevention capabilities of the Cato SASE Cloud platform. Cato’s Threat Prevention leverages multiple advanced security engines, such as IPS, NGAM, DNS security and inline AI/ML, to safeguard IoT/OT devices against known and zero-day threats. Enterprises benefit from advanced prevention that help reduce their risk.

Cato IoT/OT Security is a native feature of the Cato Management Application (CMA). All dashboards and reports are consistent with other capabilities in the CMA and the Cato SASE Cloud Platform, eliminating learning a new interface and accelerating time-to-value. Policies, logs, events and objects such as devices, manufacturers, models, users, and sites are consistently presented throughout the CMA. This consistency enables IT teams to easily identify and understand IoT/OT incidents without the need to move between different dashboards across multiple solutions.
Enhance Protection with Extended Insights and Threat Control
客戶透過 Cato,取代繁瑣的多重安全點解決方案和高成本網路服務,簡化傳統解決方案架構。Cato 獨特的 SASE 平台能自動化地一致提供全球所有用戶安全且高效的應用程式存取服務。
Cato Networks 榮登 Gartner® 單一廠商 SASE 2024 Magic Quadrant™ 領導者位置
「Cato Networks 是 ZTE 和 SASE 領域的最佳典範。」
Cato Networks 被評選為 SASE 領域的成長與創新領導者
Cato SASE 在 GigaOm Radar 報告中被評為「領導者」
Cato Networks 被評選為全球 SSE 領域的產品領導者
透過 SD-WAN 實現廣域網路轉型 為 SASE 的成功奠定穩健基礎


「我們在 Cato 上進行了攻防模擬測試,結果顯示感染率和橫向移動明顯降低,而偵測率則大幅提升。這些因素是信任 Cato 安全性的關鍵所在。」
IT 團隊一直期待的解決方案。
準備好被驚艷了嗎!