David Heinemeier Hansson lays out the economic case for why application providers should leave the cloud in a recently published blog post. It’s a powerful... Read ›
SASE Evaluation Tips: The Risk of Public Cloud’s High Costs on SASE Delivery David Heinemeier Hansson lays out the economic case for why application providers should leave the cloud in a recently published blog post. It's a powerful argument that needs to be heard by IT vendors and IT buyers, whether they are purchasing cloud applications or SASE services.
Hansson is the co-owner and CTO of 37Signals, which makes Basecamp, the project management software platform, and Hey, an email service. His "back of the napkin" analysis shows how 37Signals will save $1.5 million per year by moving from running its large-scale cloud software in the public cloud to running its cloud software on bare-metal hardware. If you haven't done so, I encourage you to read the analysis yourself.
Those numbers might seem incredible for those who've bought into the cloud hype. After all, the cloud was supposed to make things easier and save money. How's it possible that it would do just the opposite?
The cloud doesn't so much as reduce vendor costs as it allows vendors to get to market faster. They avoid the planning, deployment time, and investment associated with purchasing, shipping, and installing the hardware components, creating the redundancy plans, and the rest of what goes into building data centers worldwide. The cloud gives vendors the infrastructure from day one. Its elasticity relaxes rigorous compute planning, letting vendors overcome demand surges by spinning up more compute as necessary.
All of which, though, comes at a cost -- a rather large cost. Hansson realized that with planning, an experienced team could overcome the time to market and elements and elasticity requirements without the expenditures necessary for the cloud:
"…The main difference here is the lag time between needing new servers and seeing them online. It truly is incredible that you can spin up 100 powerful machines in the cloud in just a few minutes, but you also pay dearly for the privilege. And we just don't have such an unpredictable business as to warrant this premium. Given how much money we're saving owning our own hardware, we can afford to dramatically over-provision our server needs, and then when we need more, it still only takes a couple of weeks to show up.
The result: enormous capital savings (and other benefits).
From Productivity Software to Productive SASE Services
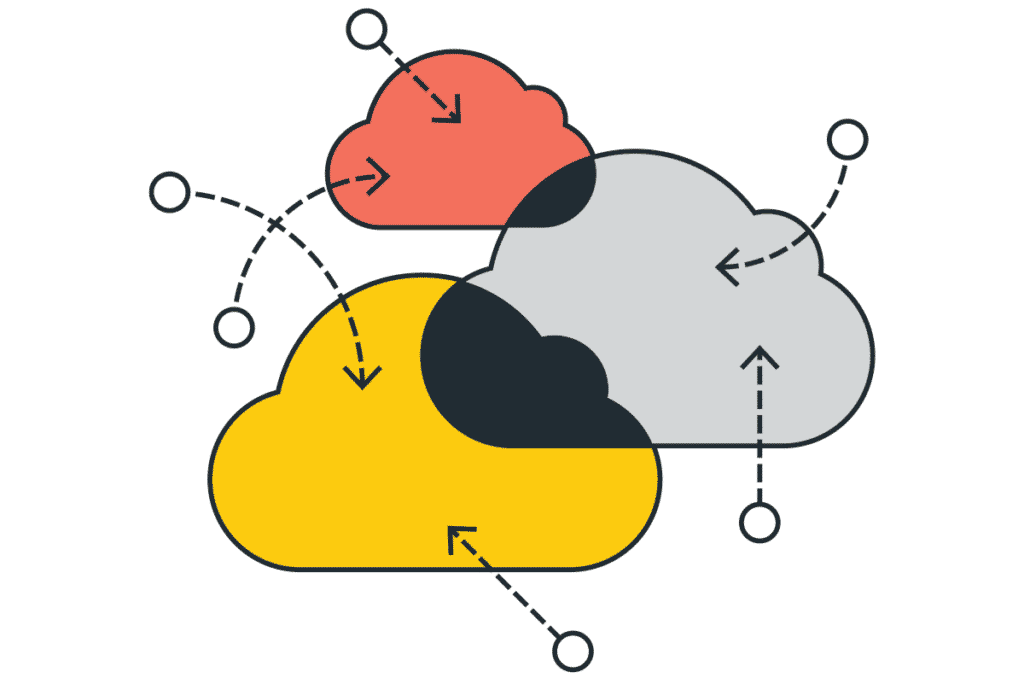
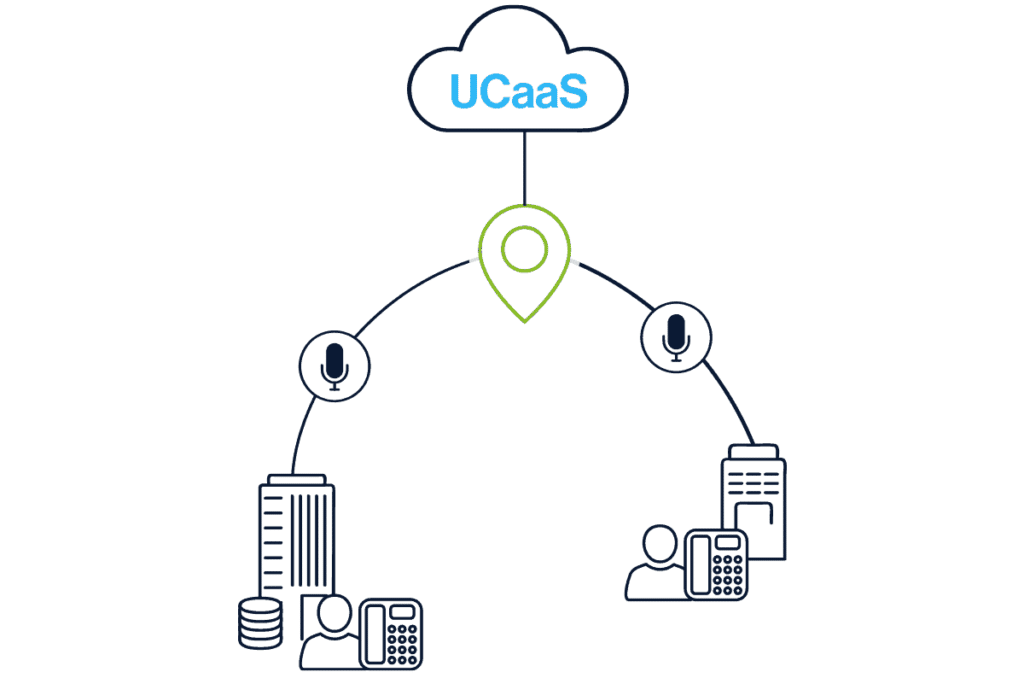
What Hansson says about application software holds for SASE platforms. A SASE platform requires PoPs worldwide. Those PoPs need servers with enough compute to work 24x7 under ordinary occasions and additional compute needed to accommodate spikes, failover, and other conditions.
It's a massive undertaking that takes time and planning. In the rush to meet the demand for SASE, though, many SASE players haven't had that time. They had no choice but to build out their SASE PoPs on public cloud infrastructure precisely because they were responding to the SASE market. Palo Alto Networks, for example, publicly announced their partnership with Google Cloud in 2022 for their ZTNA offering. Cisco announced its partnership with Google for global SD-WAN service. And they're not alone. With the purchasing of cloud infrastructure, those companies incur all the costs Hansson details.
[boxlink link="https://www.catonetworks.com/resources/inside-cato-networks-advanced-security-services/"] Inside Cato Networks Advanced Security Services | Download the White Paper [/boxlink]
Which brings us to Cato. Our founders started Cato in 2015, four years before SASE was even defined. We didn't respond to the SASE market; we invented it.
At the time, the leadership team, which I was fortunate enough to be part of, evaluated and deliberately avoided public cloud infrastructure as the basis for the Cato SASE Cloud. We understood the long-term economic problem of building our PoP infrastructure in the cloud. The team also realized that owning our infrastructure would bring other benefits, such as delivering Cato SASE Cloud into regions unserved by the public cloud providers.
Instead, we invested in building our PoPs on Cato-owned and operated infrastructure in tier-4 data centers across 80+ countries. Today, we continue with that philosophy and rely on our experienced operations team to ensure server supply to overcome supply chain problems.
High Costs Mean a Choice of Three Rotten Outcomes for Customers
Now, customers don't usually care about their vendors' cost structures. Well, at least not initially. But when a service isn't profitable because the COGS (cost of goods sold) is too high, there's only one of three outcomes, and none are particularly well-liked by customers. A company will go bankrupt, prices will grow to compensate for the loss, or service quality will drop.
Those outcomes are improbable if a vendor sells a service or product at a profit. The vendor may adjust prices to align with macroeconomics and inflation rates or decrease prices over time, sharing the economic benefit of large-scale operations with your customers. Or the vendor may evolve service capabilities and quality to meet customer needs better. Regardless, the vendor will likely be the long-term solution enterprise IT requires for networking or security solutions.
The Bottom Line Should Be Your Red Line
Using public clouds for large-scale cloud services allowed legacy vendors to jump into the then new SASE market and seemingly offer what any enterprise IT buyer wants – the established reputation of a large company with innovation that is SASE. It's a nice comforting story. It's also not true.
Building a SASE or application service on a cloud platform brings an excessively high COGS, as Hansson has pointed out. Eventually, that sort of deficit comes back to bite the company. Sure, a company may be able to hide its losses for a while. And, yes, if the company is large enough, like a Palo Alto Networks or Cisco, it's not likely to go out of business any time soon.
But if the service is too expensive to deliver, any vendor will try to make the service profitable – whether by increasing prices or decreasing service quality – and always at the customer's expense. Ignoring such a glaring risk when buying infrastructure and purchasing from a large vendor isn't "playing it safe." It's more like sticking your head in the lion's mouth. And we know how well that goes.
History taught us that whistleblowers can expose the darkest secrets and wrongdoing of global enterprises, governments and public services; even prime ministers and presidents. Whistleblowers... Read ›
Whistleblowers of a Fake SASE are IT’s Best Friends History taught us that whistleblowers can expose the darkest secrets and wrongdoing of global enterprises, governments and public services; even prime ministers and presidents. Whistleblowers usually have a deep sense of justice and responsibility that drives them to favor the good of the many over their own. Often, their contribution is really appreciated only in hindsight.
In an era where industry buzz around new technologies such as SASE is exploding, vendors who are playing catch-up can be tempted to take shortcuts, delivering solutions that look like the real thing but really aren’t. With SASE, it is becoming very hard for IT teams to filter through the noise to understand what is real SASE and what is fake. What can deliver the desired outcomes and what might lead to a great disappointment.
Helpfully for IT teams, the whistleblowers of fake SASE solutions have already blown their whistles loud and clear. All we need to do is listen to their warnings, to the red flags they are waiving in our faces, and carefully examine every SASE (true or fake) solution to identify its’ real essence.
The Fragmented Data Lake Whistleblower
As more and more legacy products such as firewalls, SWG, CASB, DLP, SD-WAN and others are converging into one SASE platform, it can only be expected that all the events they generate will converge as well, forming one unified data lake that can be easily searched through and filtered. This is still not the case with many vendor’s offerings.
Without a ready-made, unified data lake, enterprises need a SIEM solution, into which all the events from the different portfolio products will be ingested. This makes the work of SIEM integration and data normalization a task for the IT team, rather than a readily available functionality of the SASE platform.
Beyond the additional work and complexity, event data normalization almost always means data reduction, leading to less visibility about what is really happening on the enterprise network and security. Conversely, the unified data lake from a true single-vendor SASE solution will be populated with native data that gives rich visibility and a real boost to advanced tools such as XDR.
Think carefully if an absence of a ready-made unified data lake is something you are willing to compromise on, or should this red flag, forcefully waved by the data lake whistleblower, be one of your key decision factors.
The Multiple Management Apps Whistleblower
One of the most frustrating and time-consuming situations in the day-to-day life of IT teams is jumping between oh so many management applications to understand what is happening, what needs attention, troubleshooting issues, policy configuration and even periodic auditing.
SASE is meant to dramatically reduce the number of management applications for the enterprise. It should be a direct result of vendor consolidation and product convergence. It really should.
But some vendors (even big, established ones) offer a SASE built with multiple products and (you guessed it) multiple management applications, rather than a single-platform SASE with one management application.
With these vendors, it’s bad enough having to jump between management applications, but it can also mean having to implement policies separately in multiple applications.
The management whistleblower is now exhausting the air in her lungs, drawing your attention to what might not be the time saving and ease of use you may be led to expect. Some might like the overflow of management applications in their job, but most don’t.
Multiple managements applications can be hidden by a ‘management-of-managements’ layer. It might be a good solution in theory, but in practice – it means that every change, bug fix, and new feature needs to be implemented and reflected in all the management applications. Are you sure your vendor can commit to that?
[boxlink link="https://catonetworks.easywebinar.live/registration-making-sure-sase-projects-are-a-success"] Making Sure SASE Projects Are a Success | Watch the Webinar [/boxlink]
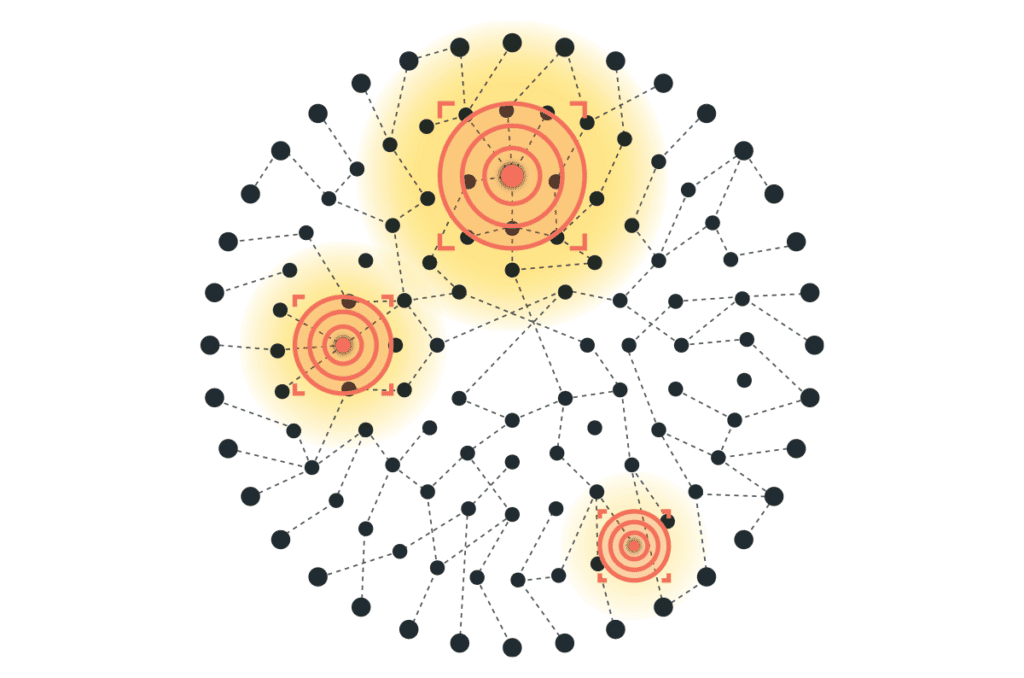
The Asymmetric PoPs Whistleblower
This one is probably the hardest one to expose, but once seen – it cannot be unseen.
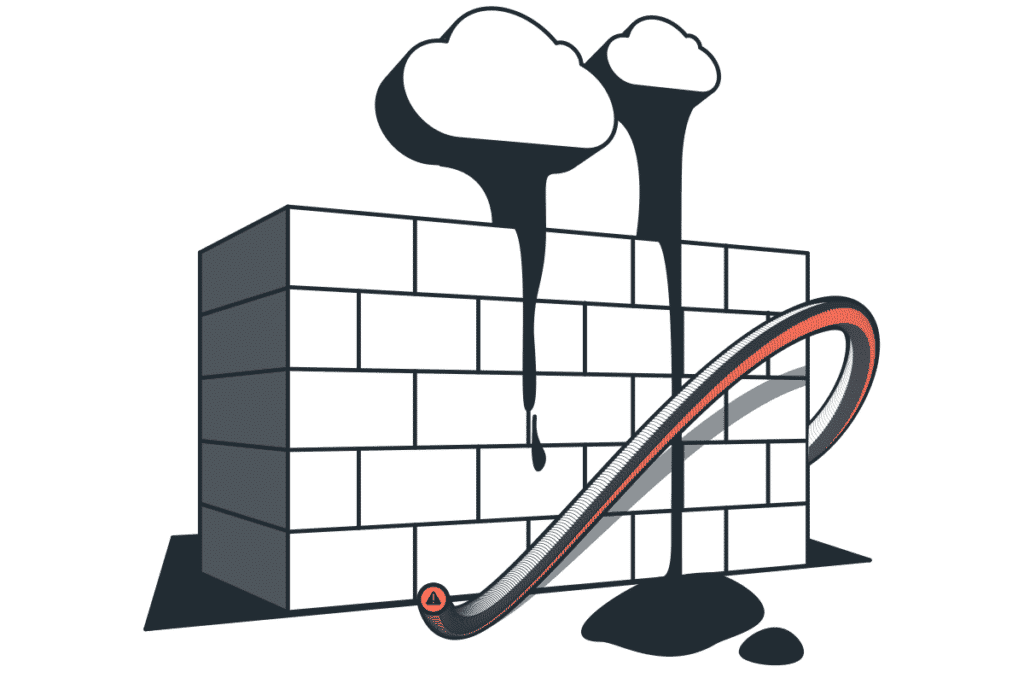
Vendors who did not build their SASE from the ground up as a cloud-native software often take shortcuts in the race to market. They create service PoPs (Points of Presence) by deploying their legacy point products as virtual machines on a public cloud like GCP, AWS or Azure. This is an expensive strategy to take on, and an extremely complex operation to build and maintain with an SLA that fits critical IT infrastructure requirements.
Some may think this is meaningless, and that as long as the customer is getting the service they paid for, why should they care. Well, here is why.
To reduce the high IaaS costs and the operational complexity, such vendors will intentionally avoid offering all their SASE capabilities from all of their PoPs. The result of this asymmetric PoP architecture is degraded application performance and user experience, due to the need to route some or all traffic to a distant PoP for processing and inspection. So, when users come in complaining, do you think that saying you are supporting the cost saving of the SASE vendor will be a reasonable explanation?
The asymmetric PoPs whistleblower recommends that you double check with every SASE vendor that all their PoPs are symmetric, and that wherever your users and applications are, all the SASE services will be delivered from the nearest one PoP.
Epilogue
Whistleblowers are usually not fun to listen to. They challenge and undermine our believes and perception, taking us out of our comfort zone.
The three whistleblowers here mean no harm, only wanting to help minimize the risk of failure and disappointment. They blow their whistles and wave their red flags to warn you to proceed with caution, educate yourself, and select your strategic SASE vendor with eyes wide open.
Enterprises in the private sector look to the US federal government for cybersecurity best practices. The US CISA (Cybersecurity & Infrastructure Security Agency) issues orders... Read ›
How Long Before Governments Ban Use of Security Appliances? Enterprises in the private sector look to the US federal government for cybersecurity best practices. The US CISA (Cybersecurity & Infrastructure Security Agency) issues orders and directives to patch existing products or avoid use of others. The US NIST (National Institute of Standards and Technology) publishes important documents providing detailed guidance on various security topics such as its Cybersecurity Framework (CSF).
CISA and NIST, like their peer government agencies in the world, have dedicated teams of experts tasked with quantifying the risks of obsolete security solutions and discovered vulnerabilities, and the urgency of safeguarding against their exploitation. Such agencies do not exist in the private sector. If you are not a well-funded organization with an established team of cyber experts, following the government’s guidance is both logical and effective.
What you should do vs what you can do
Being aware of government agencies guidance on cyber security is extremely important. Awareness, however, is just one part of the challenge. The second part, usually the much bigger part, is following their guidance. Instructions, also referred to as ‘orders’ or ‘directives,’ to update operating systems and patch hardware products arise on a weekly basis, and most enterprises, both public and private, struggle to keep up.
Operating systems like Windows and macOS have come a long way in making software updates automatic and simple to deploy. Many enterprises have their computers centrally managed and can roll out a critical software update in a matter of hours or days.
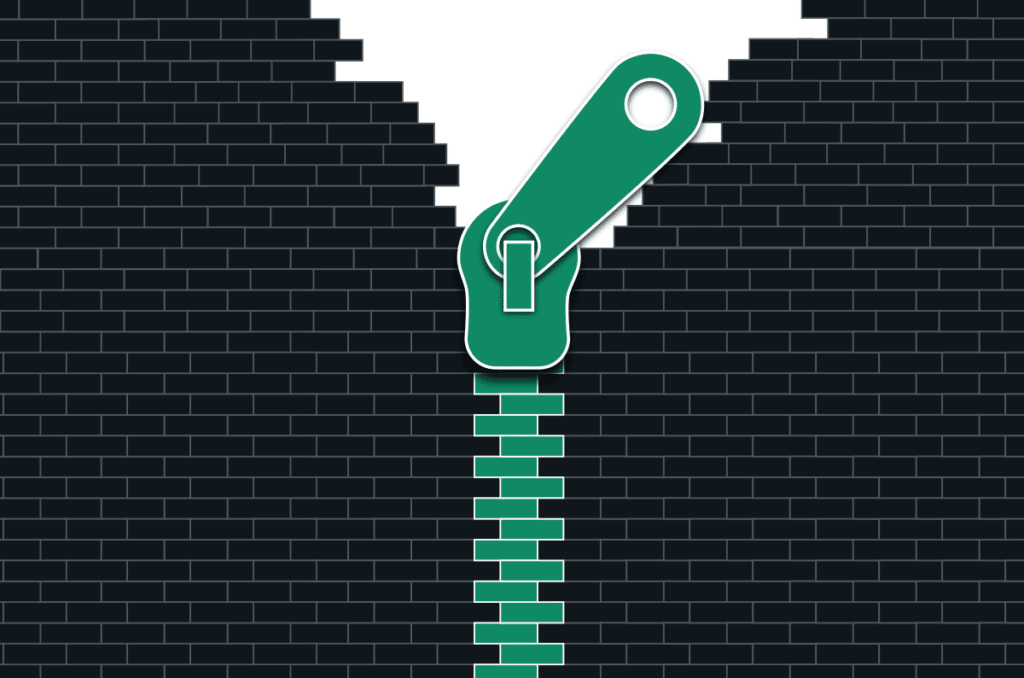
Hardware appliances, on the other hand, are not so simple to patch. They often serve as critical infrastructure so IT must be careful about disrupting their operation, often delaying until a weekend or holiday. Appliances such as routers, firewalls, secure web gateways (SWG) and intrusion prevention systems (IPS) have well-earned reputations of being extremely ‘sensitive’ to updates. Historically, they do not continue to operate the same after a patch or fix, leading to lengthy and frustrating troubleshooting, loss of productivity and heightened risk of attack. The challenge in rapidly patching appliances is known to governments as it is known to cyber attackers. Those appliances, often (mis)trusted as the enterprise perimeter security, are effectively the easy and preferred way for attackers to enter an enterprise.
[boxlink link="https://www.catonetworks.com/resources/cato-networks-sase-threat-research-report/"] Cato Networks SASE Threat Research Report H2/2022 | Get the Report [/boxlink]
The CISA KEV Catalog – Focus on what’s important
Prioritization has become a necessity as most enterprises can’t really spend their resources in continuous patching cycles. The US CISA’s Known Exploited Vulnerability (KEV) catalog which mandates the most critical patches for government organizations, helps enterprises in the private sector know where to focus their efforts.
The KEV catalog also exposes some important insights worth paying attention to. Cloud-native security vendors such as Imperva Incapsula, Okta, Cloudflare, Cato Networks and Zscaler don’t have a single record in the database. This is because their solution architecture allows them to patch and fix vulnerabilities in their ongoing service, so enterprises are always secured.
Hardware vendors, on the other hand, show a different picture. As of September of 2023, Cisco has 65 records, VMware has 22 records, Fortinet has 11 records, and Palo Alto Networks has 4 records.
Cyber risk analysis and the inevitable conclusion
CISA’s KEV is just the tip of the iceberg. Going into the full CVE (Common Vulnerabilities and Exposures) database shows a much more concerning picture.
FortiOS, the operating system used across all of Fortinet’s NGFWs has over 130 vulnerabilities associated with it, 31 of which disclosed in 2022, and 14 in the first 9 months of 2023. PAN-OS, the operating system in Palo Alto Networks’ NGFWs has over 150 vulnerabilities listed. Cisco ASA, by the way, is nearing 400. For comparison, Okta, Zscaler and Netskope are all in the single-digit range, and as cloud services, are able to address any CVE in near-zero time, and without any dependency on end customers.
Since most enterprises lack the teams and expertise to assess the risk of so many vulnerabilities and the resources to continuously patch them, they are forced by reality to leave their enterprises exposed to cyber-attacks.
The risk of trusting in appliance-based security vs. cloud-based security is clear and unquestionable. It is clear when you look at CISA’s KEV and even clearer when you look at the entire CVE database.
All of this leads to the inevitable conclusion that at some point, perhaps not too far ahead in the future, government agencies such as the US NIST and CISA will recommend against or even ban appliance-based security solutions.
Some practical advice
If you think the above is a stretch, just take a look at Fortinet’s own analysis of a recent vulnerability, explicitly stating it is targeted at governments and critical infrastructure: https://www.fortinet.com/blog/psirt-blogs/analysis-of-cve-2023-27997-and-clarifications-on-volt-typhoon-campaign.
Security appliances have been around for decades, and yet, the dream of a seamless, frictionless, automatic and risk-free patching for these products never came true. It can only be achieved with a cloud-native security solution.
If your current security infrastructure is under contract and appliance-based, start planning how you are going to migrate from it to a cloud-native security at the coming refresh cycle.
If you are refreshing now or about to soon, thoroughly consider the ever-increasing risk in appliances.
Picture this: A rock band embarking on a world tour, rocking stages in different cities with thousands of adoring fans. But wait, behind the scenes,... Read ›
Rocking IT Success: The TAG Heuer Porsche Formula E Team’s City-Hopping Tour with SASE TAG Heuer Porsche Formula E Team Picture this: A rock band embarking on a world tour, rocking stages in different cities with thousands of adoring fans. But wait, behind the scenes, there's an unsung hero—the crew. They're the roadies, the ones responsible for building the infrastructure that supports the band's electrifying performances in each new location. Now, let's take that same analogy and apply it to the TAG Heuer Porsche Formula E Team.
We invited Friedemann Kurz, Head of IT at Porsche Motorsport, to a special webinar where we discussed how technology drives these races and IT’s key role.
Join us as we dive into the IT requirements faced by this cutting-edge racing team and how SASE (Secure Access Service Edge) rises to the occasion, ensuring a flawless journey from one city to another.
Top IT Requirements
The TAG Heuer Porsche Formula E Team’s IT team faces a number of networking challenges. Surprisingly (or not) these challenges are not that different from the challenges faced by IT teams across all organizations. From battery energy to braking points, and time lost for Attack Mode, the IT support team at the Porsche test and development center in Weissach and trackside will work in parallel to process approximately 300 GB of data on one Cato Networks dashboard to make time critical decisions. Some of these challenges include:
Finding the Right Products
The TAG Heuer Porsche Formula E Team’s IT provides services in a high-pressure environment -- and expectations are high. On-track, the IT team is limited in size, so each person needs to be able to operate all IT-related aspects, from network to storage to layers one to five to end-to-end monitoring. This makes choosing the right products and technologies key to their success.
Operational Efficiency
With so many actions happening simultaneously during the race, IT needs to be able to focus on the issues that matter most. This requires in-depth monitoring that is easy-to-use and the ability to fix issues instantly.
Security
Security needs to be built-in to the solution to ensure it doesn’t require additional effort from the team. Security is a key success factor, meaning all IT team members focus on security, rather than having a dedicated security person.
Easy Deployment
The TAG Heuer Porsche Formula E Team operates worldwide, but they only spend a few days at each global site. Every time they arrive at a new city, IT needs to quickly deploy networking and security from scratch (with no existing infrastructure) and pack it up after the race. This whole process only takes a few days, so it has to be efficient and quick. In addition, the rest of the team arrives on site at the same time as the IT team, demanding connectivity immediately.
[boxlink link="https://catonetworks.easywebinar.live/registration-simplicity-at-speed"] Simplicity at Speed: How Cato’s SASE Drives the TAG Heuer Porsche Formula E Team’s Racing | Watch the Webinar [/boxlink]
IT Capabilities Required to Win Races
Why is the IT team a key component in the TAG Heuer Porsche Formula E Team’s success? Here are a few of the networking and security capabilities they rely on:
Data Analysis
Races are a data-driven and data-intensive event, with large amounts of data being transmitted back and forth across the global network. For example, the TAG Heuer Porsche Formula E Team downloads the car and racetrack data after the races. Then, the engineers in the operations room at the team’s headquarters analyze the data for improving the team’s setup and strategy.
Real-Time Communication
During the races, the team relies on global real-time communication. It is the most critical way of communication between the driver, the support engineers and the operations room. This means that real-time packages that are transmitted across the WAN need to be optimized to ensure quality of services.
Driver in the Loop
The TAG Heuer Porsche Formula E Team’s success relies on large-scale mathematical models that use the data to find better racing setups and strategies. Their focus is on the energy use formula, since, ideally, drivers complete the races with zero battery left. Zero battery means it was the most efficient race. The ability to calculate these formulas is based on data that is transferred back and forth between the track and the headquarters.
Ransomware Protection
The sports industry has been targeted by cyber attackers in the past with ransomware and other types of attacks. To protect their ability to make decisions during races, the TAG Heuer Porsche Formula E Team needs a security solution that protects them and their ability to access their data from ransomware attacks. Since data is the cornerstone of their strategy and key for their decision-making, safeguarding access to the data is top priority.
How Cato’s SASE Changed the Game
To answer these needs, the TAG Heuer Porsche Formula E Team partnered with Cato Networks. Cato Networks was chosen as the team’s official SASE partner. Cato Networks helps transmit large volumes of data in real-time from 20 global sites.
Before working with Cato Networks, the TAG Heuer Porsche Formula E Team used VPNs. This introduced security, configuration and maintenance challenges. Now, maintenance and effort have significantly decreased. One IT member on-site can oversee, manage and monitor the entire network during the races independently and flexibly.
In addition, Cato delivered:
Fast implementation - from 0 to 100% in two weeks.
Simplified and efficient operations.
Quick response times.
Personal and open-minded support.
To hear more from Friedemann Kurz, Head of IT at Porsche Motorsport, watch the webinar here.
In November 2022, the TAG Heuer Porsche Formula E Team announced its partnership with Cato Networks, declaring Cato the team’s official SASE partner. Cato Networks... Read ›
The TAG Heuer Porsche Formula E Team & Cato Networks: The Story Behind the Partnership In November 2022, the TAG Heuer Porsche Formula E Team announced its partnership with Cato Networks, declaring Cato the team’s official SASE partner. Cato Networks provides the TAG Heuer Porsche Formula E Team with the connectivity and security they need to deliver superior on-track performance during the races.
According to Thomas Eue, Lead IT Product Manager of the TAG Heuer Porsche Formula E Team, “Cato is a real game changer for us. I would absolutely recommend Cato to other enterprises because it’s really simple to set up and the network is really getting faster now.”
In this blog post, we examine the challenges the TAG Heuer Porsche Formula E Team was dealing with before using SASE, why they chose Cato and how Cato’s SASE solution helps the TAG Heuer Porsche Formula E Team win races. You can read the entire case study this blog post is based on here.
The Challenge: Real-Time Data Transmission at Scale
During the ABB FIA Formula E World Championship races, the TAG Heuer Porsche Formula E Team relies on insights and instructions delivered in real-time to drivers from the team’s headquarters in Germany. These instructions are derived from live racing data, like tire temperature, battery depletion, timing data and videos of the driver. The accuracy and reliability of this process is critical to the team’s success.
However, it was challenging for the TAG Heuer Porsche Formula E Team to transmit live TV feeds, live intercom services and live communication across several different channels, since they were only provided 50Mbps of bandwidth.
In addition, the nature of the races requires the team to travel to each new racing site before each competition and set up the network. According to Friedemann Kurz, Head of IT at Porsche Motorsport, this is challenging because “Technologically we are not a hundred percent sure on what’s awaiting us in the different countries. So especially the latency of course by the pure physics, it’s changing a lot between countries.”
[boxlink link="https://catonetworks.easywebinar.live/registration-simplicity-at-speed"] Simplicity at Speed: How Cato’s SASE Drives the TAG Heuer Porsche Formula E Team’s Racing | Watch the Webinar [/boxlink]
The TAG Heuer Porsche Formula E Team’s Choice: Cato Networks’ SASE
The TAG Heuer Porsche Formula E Team chose Cato’s SASE, turning it into a cornerstone of their racing strategy. Cato’s global and optimized SASE solution connects the drivers, the garage and the HQ with a high-performing infrastructure. During the races, vital data is transmitted across Cato’s global private backbone for real-time analysis at the HQ and back to the drivers and on-site teams to boost driving performance.
According to Friedemann Kurz, Head of IT at Porsche Motorsport, “Cato Networks will allow us to focus on the critical decisions that make a difference on-track by lessening the administrative work to set up and manage our IT network infrastructure. Using the Cato SASE Cloud, we’re able to have the reliable and secure connectivity we need to have anywhere around the world, whether at a racetrack, during travel or at the research and development center in Weissach, the home of Porsche Motorsport.”
Cato Networks also ensures the connection is secure. “We have the most secure connection wherever we are – between all the racetracks, cloud applications and Porsche Motorsport in Weissach,” says Carlo Wiggers, Director of Team Management and Business Relations at Porsche Motorsport
To answer the deployment challenges, Cato Networks enables setting up a site in a mere five hours. “We are very well prepared and confident, as soon as the engineers arrive the services are ready to run,” comments Friedemann Kurz, Head of IT at Porsche Motorsport.
A Streamlined and High-Performing Solution
With Cato Networks’ technology, the team’s IT engineers and the Motorsport IT department, are reliably transmitting data in real-time. The HQ team, in turn, is able to analyze the data and make informed decisions instantly.
In the first week of usage, the team transferred more than 1.2 TB of data.
In the Cape Town race, for example:
1.45 TB of data were transmitted.
The round-trip-time from the race track to the HQ was stable at 80-100 milliseconds.
Packet loss was only 0.23% over the whole event.
“Every enterprise that has any similarity with what we are doing, acting worldwide, having various branches around the world can definitely benefit on all the solutions that Cato is providing,” concludes Friedemann Kurz, Head of IT at Porsche Motorsport
Learn more about the ABB FIA Formula E World Championship, how the TAG Heuer Porsche Formula E Team leverages Cato’s SASE and the joint values the two teams share by reading the complete case study, here.
Security leaders today are facing a number of challenges, including a rise in the number of breaches, a need to accommodate remote work and networking... Read ›
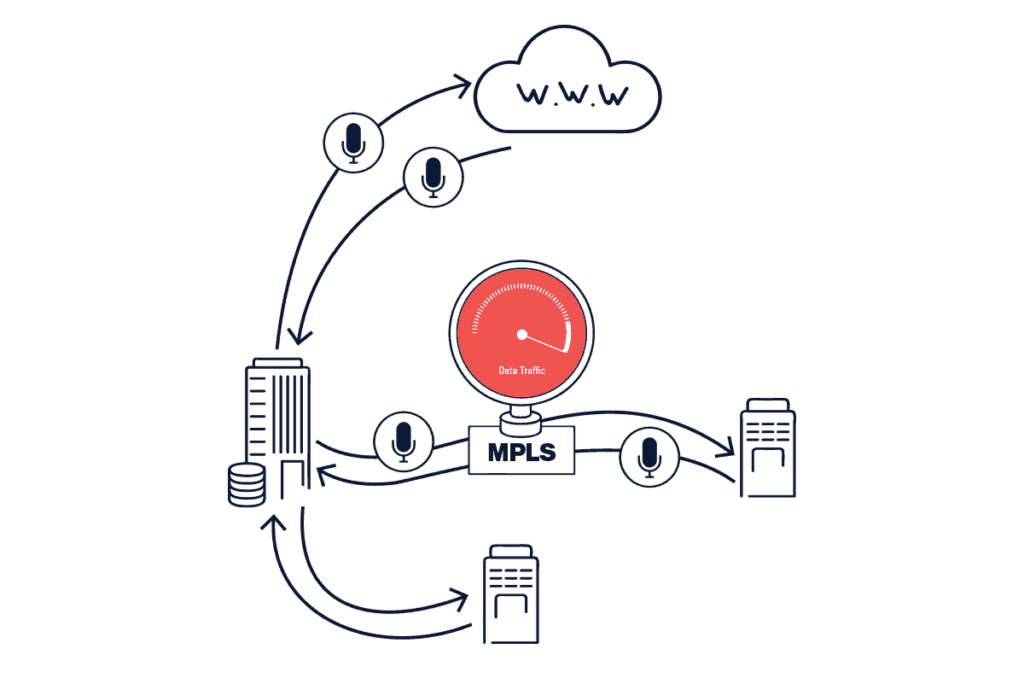
How to Be a Bold and Effective Security Leader Security leaders today are facing a number of challenges, including a rise in the number of breaches, a need to accommodate remote work and networking requirements to replace MPLS networks. In this new blog post, we share insights about this new reality by David Holmes, Senior Analyst at Forrester, as well as an in-depth explanation about the security stack that can help. You can watch the webinar this blog post is based on here.
3 Trends Impacting Networking and Security
Forrester identified three converging trends that are influencing the network and security industries: A growing number of cybersecurity breaches complemented by a security skills shortage, remote work as the new reality and MPLS connections being replaced by SD-WAN. Let’s delve into each one.
1A. Cybersecurity Breaches are on the Rise
According to Forrester, the number of cybersecurity breaches has grown significantly. In 2019, 52% of organizations they surveyed were breached at least once over a 12-month period. In 2020, the percentage jumped to 59%. In 2021 it was 63% and in 2022 it was a whopping 74%. Unfortunately, the actual percentage is probably higher since these numbers do not include organizations that do not know they were breached or have not admitted it.
1B. Security Skills Shortage has Real Impact
In addition, Forrester found that companies whose IT security challenges included finding employees with the right security skills tended to have more breaches annually. Nearly a quarter (23%) of organizations who pinpointed security skills shortage as one of their biggest IT challenges, were breached more than six times in the past 12 months.
2. Remote Work is Here to Stay
Forrester’s research concluded that the concept of working anywhere has been embraced by security leaders. Nowadays, 30% of a CSO’s time during working hours is spent working from home, compared to 2% before the COVID-19 pandemic. The percentage of work taking place at the corporate headquarters has been reduced from 49% to 21%. Non-security employees probably spent more work time at home than the surveyed CSOs.
Remote working means employees work from anywhere and their company data can also be anywhere, especially in the cloud. For architects, CSOs and CTOs, this means they have to build an architecture that take these new conditions into account. This requires adjustments in terms of security, the user experience, and more.
3. SD-WAN Adoption
Finally, according to Forrester, 74% of organizations are adopting or have already adopted SD-WAN, while only 10% have no plans at all. SD-WAN allows organizations to replace their private lines and eliminate the overhead and maintenance of connecting through local ISPs.
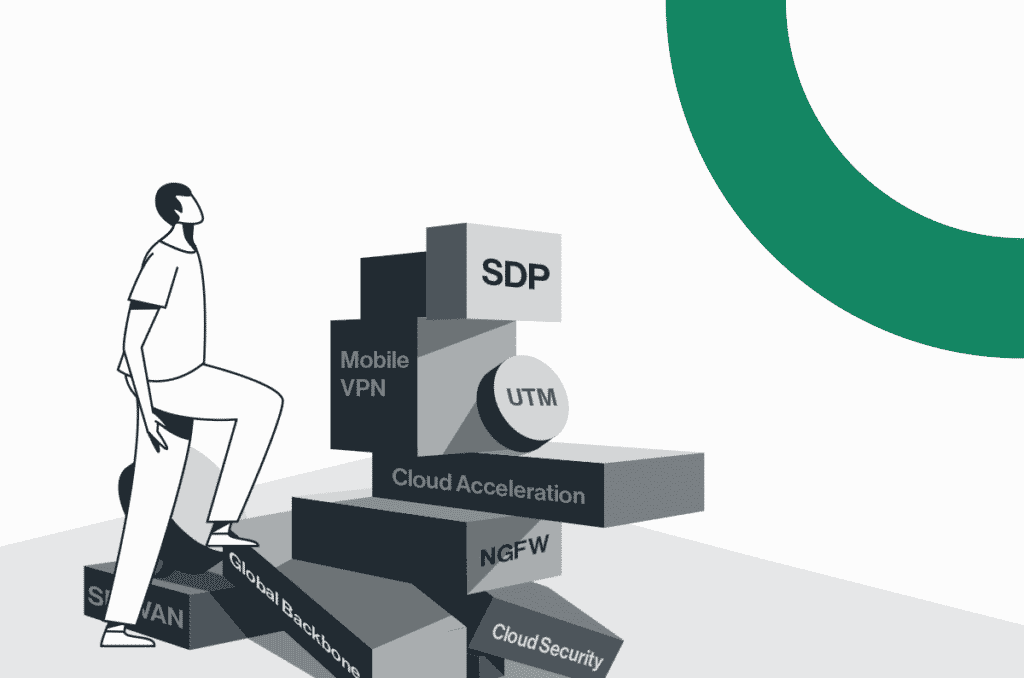
Point Solutions are Incompatible with the Hybrid Enterprise
This new reality requires new networking architectures. In legacy architectures, most users were in the office,using on-premises applications, remote user traffic was backhauled through the data center, where security policies were enforced through point solutions. This was a good solution at the time, but today with applications and users everywhere, this approach is no longer practical or productive.
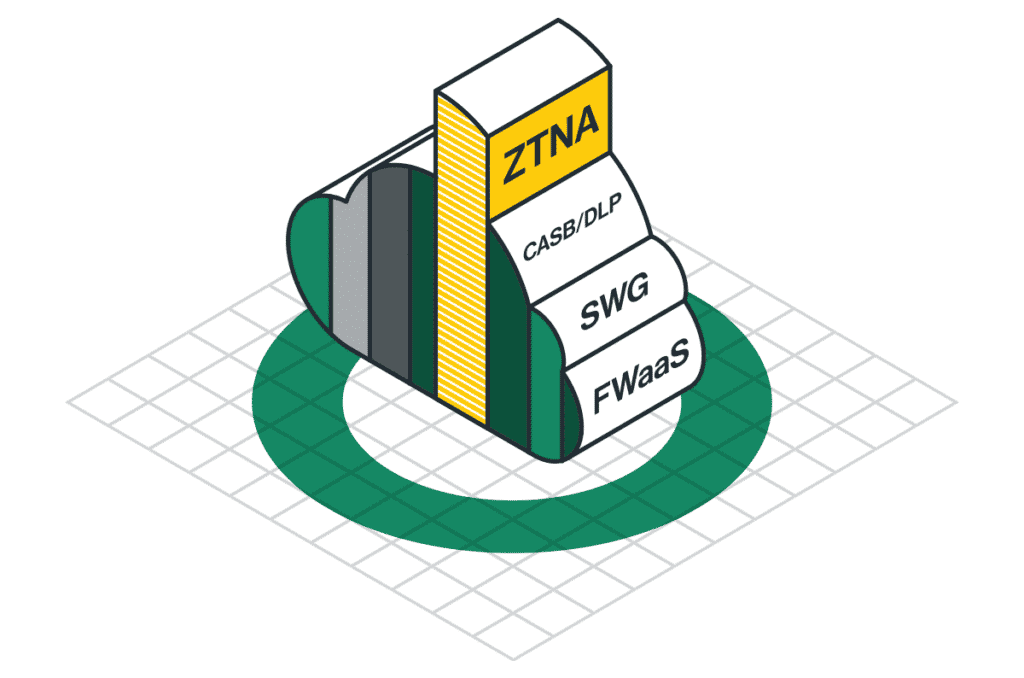
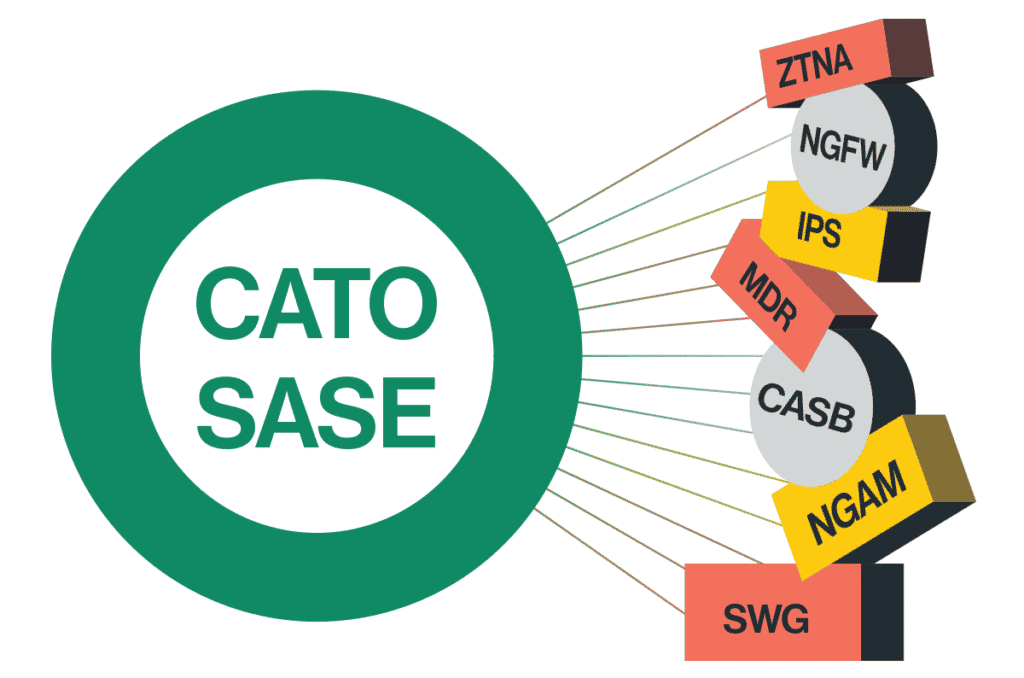
But moving all point solutions to the cloud isn’t a good approach either. Let’s take a look at a typical organization’s security stack for the cloud:
SWG and CASB solutions secure user access to the internet and to cloud applications. They are usually provided through a built-in web proxy architecture, i.e they examine HTTP and HTTPS traffic.
ZTNA provides access to private applications. It is commonly delivered through a separate pre-app connector architecture, which is a type of virtual overlay.
NGFW and UTM solutions identify malicious traffic coming from non-users.
This stack constitutes a fragmented architecture that creates inconsistent policy engines, limited visibility for WAN security and unoptimized access to the Internet and Cloud Resources. The result is blind spots and complexity.
The Right Way: One Architecture for Total Visibility, Optimization and Control
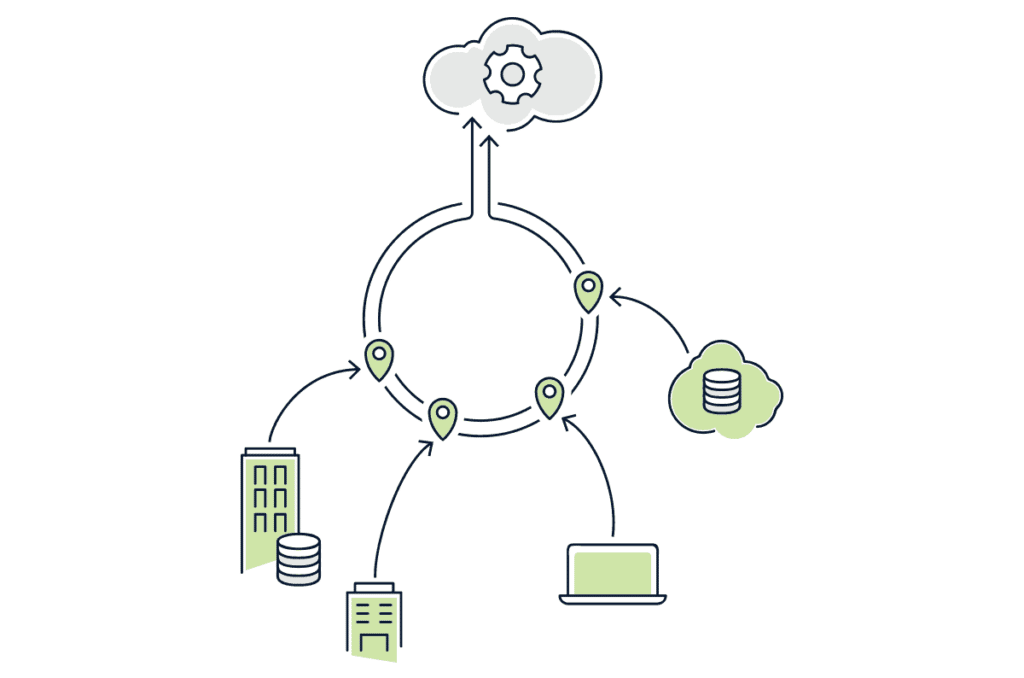
The solution is to converge the entire security stack into one cloud function. Such a cloud security service will provide total visibility, optimization and control of all the traffic. It will ensure all traffic goes through the same security controls in a single, converged architecture for all edges, giving organizations the ability to enforce policies with one policy engine and one rule base.
A converged solution enables doing this in a holistic manner that covers all traffic (ports, protocols, IPs, sources and destinations), applications (Private, Public, Cloud and Web), security capabilities (FWaaS, IPS, NGFW, ZTNA, CASB, DLP) and directions (WAN, Internet, Cloud) for all users, IoT, apps and devices. In addition, traffic is optimized for global routing and acceleration across a global private backbone.
Cato SSE 360: Security Transformation in the Cloud
Cato SSE 360 is built from the ground up to behave that way. Cato SSE 360 is the security pillar of Cato’s SASE cloud, providing total visibility, optimization and control. Cato’s SSE 360 converges all SSE components into a global cloud service that includes SWG, CASB, DLP, FWaaS, while providing a global backbone for traffic optimization and acceleration.
The global reach of Cato SSE 360 (and SASE, see below) spans over more than 80 Pop locations across North America, Europe, Asia, Latin America, the Middle East and Africa. Each PoP location runs Cato's full security stack and network optimization capabilities. This ensures a short distance of under 25 milliseconds round trip time from any user and any business location. In addition, Cato is continuously adding more PoPs every quarter to expand coverage.
[boxlink link="https://catonetworks.easywebinar.live/registration-how-to-be-a-bold-and-effective-security-leader-during-times-of-economic-downturn"] How to Be A Bold and Effective Security Leader During Times of Economic Downturn | Watch the Webinar [/boxlink]
Cato SASE Cloud
SASE (Secure Access Service Edge) is the convergence of security and networking capabilities into a single cloud-native platform. Cato’s SASE cloud is the convergence of SSE 360 and SD-WAN across a private cloud network of PoPs. All PoPs are interconnected by a global private backbone that is built with redundant tier one providers, and this guarantees consistent and predictable global latency, jitter and packet loss, creating a reliable network.
All traffic runs through Cato’s Single Pass Cloud Engine (SPACE) that performs all networking and security processing in the cloud. SPACE consists of two parts:
A multi-gig packet processing engine
A real-time policy enforcement engine
SPACE is natively built to process multi-gig traffic flows from all enterprise edges, including branches, users devices and applications. It supports all ports and protocols and automatically extracts rich context from each flow, including the user identity, device posture, target applications and data files. Then, it finds the best route for the traffic and applies network optimization and acceleration to minimize round trip times. TLS decryption is applied as needed without any impact on the user experience.
Multiple security engines simultaneously and consistently enforce policies through SPACE. FWaaS, IPS, NGAM and SWG clooaborate to protect users against WAN and Internet-based advanced threats. In addition, ZTNA provides secure remote access, while CASB and DLP control access to risky cloud applications and prevent sensitive data loss. All these capabilities run on all the traffic at the same time to minimize security overhead and leverage the rich context of every packet.
Connectivity takes place through an IPSec tunnel and a Cato vSocket, turning the cloud data centers into an integral part of the network, and with no need to deploy virtual firewalls. Cato provides full visibility and control over all the incoming and outgoing traffic from cloud data centers.
For public cloud applications, no integration is required. Optimization, inspection and enforcement are inherently applied from any edge. Traffic is forwarded over the private backbone to the PoP that is closest to the cloud instance that is serving the business. This smart egress capability optimizes the user experience. Remote users can use the Cato client or a browser to securely connect to any application on-premise or in the cloud, from laptops, tablets and smartphones.
Cato offers full visibility and control via a single pane of glass and a flexible management model. Customers can opt for a fully managed service, co-management, or complete self-management of their deployments.
Best of all, transitioning from an SSE to full SASE only requires replacing the edges with Cato’s SD-WAN sockets.
How Cato SSE 360 Addresses 3 Common Use Cases
1. Securing the Hybrid Workforce
As Forrester identified, enterprises today need to seamlessly and securely connect the hybrid workforce wherever they are.
Cato SSE 360 seamlessly and securely connects the hybrid workforce no matter where they are, and ensures all policies are consistently enforced everywhere. This eliminates the need to backhaul the user’s traffic across the world to a data center VPN appliance. There is also no need to deploy global instances to achieve the same goal. This provides zero trust security with continuous verification, access control, threat prevention and sensitive data protection, wherever the users are.
2. Beyond User-to-Application Access
Security is required beyond users and applications. It must address all edges, including IoT devices and unmanaged endpoints. This is the difference between proxy architectures and network architectures.
The Cato SPACE architecture enables Cato to provide complete visibility and full traffic inspection. This includes:
End-to-end visibility across all edges: branches, data centers, users, and apps.
End to end threat prevention and sensitive data protection.
3. IT Infrastructure Consolidation
End-to-end visibility and control provides last mile resiliency and a single pane of glass for networking and security management. Cato also eliminates solution sprawl by eliminating point solutions and the need for patching, fixing and upgrading. Finally, Cato SASE Cloud is designed to provide a resilient, self-healing architecture that ensures connectivity and security.
Learn more about solutions for security leaders by watching the entire webinar, here.
Introduction Since Gartner introduced the Secure Access Service Edge (SASE) category in 2019, interest from enterprises has grown substantially. SASE transforms enterprise IT through the... Read ›
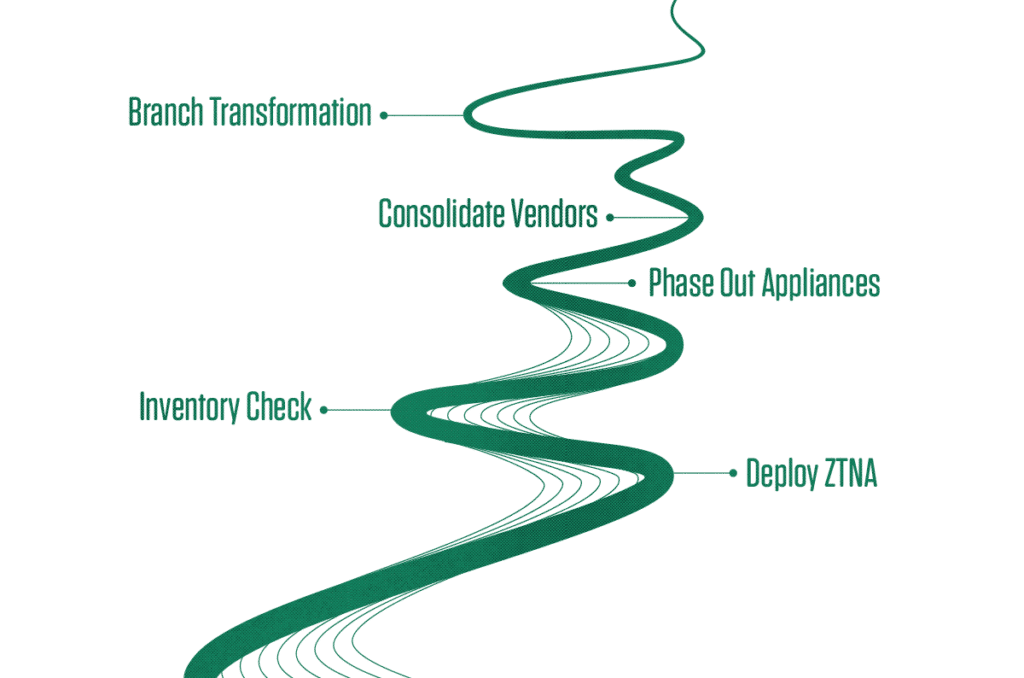
Strategic Roadmap to SASE Introduction
Since Gartner introduced the Secure Access Service Edge (SASE) category in 2019, interest from enterprises has grown substantially. SASE transforms enterprise IT through the convergence of enterprise networking and network security into a single, cloud-native, service. It aims to optimize security posture, enable zero-trust access from anywhere, and reduce costs and complexity. Given its potential impact, SASE is becoming a strategic project for many organizations.
However, the widespread availability of SASE offering from different vendors and managed services providers is causing a great deal of confusion. Organizations are challenged to compare SASE feature sets and solutions and combine offering from multiple vendors - resulting in complex architectures that lead to incomplete service offerings that don’t meet needs and expectations.
Adopting SASE is an IT strategy targeted to accompany and enable rapid growth and digital transformation, not a tactic selection of a point product. As such, making the right selection is more critical than ever.
During the “2022 Strategic Roadmap to SASE” webinar, Gartner Research Vice President Neil Macdonald and Cato Networks CMO Yishay Yovel, discussed multiple aspects of SASE but most importantly reiterated the fundamental principles and expected benefits that are the basis of why SASE was introduced back in 2019.
[boxlink link="https://www.catonetworks.com/resources/inside-look-life-before-and-after-deploying-sase/?utm_medium=blog_top_cta&utm_campaign=before_and_after_sase"] An Inside Look: Life Before and After Deploying a SASE Service | Whitepaper [/boxlink]
Several questions were raised during the webinar; the most interesting and relevant ones are answered below. They cover the following areas:
What business and technical benefits does SASE provide?
When and how should you initiate your SASE project?
How can you deploy SASE gradually into your existing infrastructure?
How do different SASE architectures impact the expected business outcomes?
We hope these Q&A will be able to clear up some of the confusion around SASE and SSE and help organizations make the right decisions when selecting a SASE provider.
Questions
SASE market overview
1. Will SSE be replacing SASE in the short term?
No, SSE is just a stop in the journey to SASE. Today, some organizations are not yet ready to fully transition to SASE for various reasons, but they are ready to adopt SSE because they recognize the benefits in adopting cloud-delivered security services such as SWG, CASB, and ZTNA to protect their offices and remote users when accessing the public Internet. The final step in the journey will be to combine the SSE capabilities with the cloud-delivered connectivity and control services such as SD-WAN and FWaaS to complement Internet security and provide the best performances and protection when accessing corporate assets.
2. Why is the security industry generally so fragmented, and will it consolidate or splinter more in the next 5 years?
The trend is clearly towards vendor consolidation. Organizations of all sizes are looking to simplify their infrastructure and operations to become more agile. They are favoring vendors that can combine multiple security and networking functionalities in a single platform, rather than best of breed solutions. This is confirmed by a recent Gartner survey that showed that 75% of organizations are pursuing security vendor consolidation and rising to 90% by Year End 2022. That’s a stunning increase if we compare to just 29% back in 2020.
3. What are the upcoming changes in SASE that experts foresee?
SASE is calling for vendor consolidation. Gartner, in its latest report "Market Guide for Single-Vendor SASE", has explicitly restated the need to unify all SASE capabilities into ideally one single vendor or at best into two vendors that must be fully integrated. We expect a limited list of vendors to stand out in the SASE market leadership and we expect companies to accelerate their initiatives towards network and security cloud-based services to reduce infrastructure complexity, optimize their CAPEX and OPEX and better control security across all their data, users and applications.
4. What techniques work best on informing senior leadership; assisting them with understanding, approving, and adopting a SASE technology?
When talking to senior leadsership about the value of SASE, put the emphasis on the benefits that a SASE approach brings to companies in their digital transformation journey:
Simplicity - by reducing infrastructure complexity
Productivity - by providing an improved and consistent user experience
Efficiency - by reducing the overall infrastructure budget
Agility - shifting network and security skills from managing boxes to policies supporting the digital workplace
SASE Migration and adoption
5. What pre-requisites and steps are needed to transition successfully to a sustainable SASE?
Break down the organizational silos – network and security teams must work in concert in the name of speed, agility and reduction of complexity
Choose a SASE vendor that meets the SASE architectural requirements (cloud-native, converged, global & support for all edges)
Map future HW and SW refresh to the SASE vendor capabilities
Plan the transition project to start with low-risk areas to minimize friction
6. What components of SASE will be important in the SMB market now and in the next 5 years? ZTNA? CASB? SD-WAN? SMB?
Aside from the specific SASE features (which of course are important and depend on the specific business case), SMBs, probably more than any other organization, will look to adopt SASE solutions that provide the following characteristics and benefits:
Operational simplicity
High automation
Flexibility
Reliability
These characteristics are typically delivered by cloud-native SASE vendors that offer an "As-a-Service" approach to networking and security.
7. Do you have a blueprint or reference architecture for an 80% cloud, 20% on-prem environment with multiple SaaS applications?
Regarding the 80/20 split, this is just marketing. Every enterprise is different, and so is every vendor. At Cato, we believe we should deliver as much as we can from the cloud and as little as we can from on-prem. Our 1500+ customers agree with us.
Cato SASE vs other SASE solutions
8. Which are the main benefits of the Cato SASE solution compared to a managed SASE offered by a Telco?
A Telco managed SASE service is normally a conglomeration of point solutions wrapped around a telco managed blanket. Some customers may consider this "black-box" approach but be wary of the following:
They can't move as fast as a modern digital business requires. Everything is managed through tickets, and involves multiple staff members due to the complexity of the underlying solutions architecture
They can't offer a future-proof solution. They are dependent on their vendors' roadmap, and usually are last to apply updates and enhancements due to the complexity and risk of downtime.
The bottom line is that, unless they manage a real SASE architecture underneath, they are simply not the right fit for the needs of modern, digital enterprises.
9. How is Cato SASE a better value than Netskope SASE?
Enterprises today are looking to consolidate services as much as possible realizing it will improve simplicity, agility, efficiency, and productivity. Netskope offers one point product (SWG+CASB) focused on internet and cloud security, another point product (NPA) focused on ZTNA, and they recently acquired a very small SD-WAN company (Infiot) for their SD-WAN technology.
While Cato and Netskope share the common vision of a SASE solution delivered as a Service from the cloud, the main difference is in the architecture design. While the Cato architecture has been built from the ground up with a converged approach with networking and security services delivered from a single home-grown software stack, Netskope started as a CASB/DLP solution and has later expanded its services portfolio by integrating multiple point solutions together because of several acquisitions, the last one being a small SDWAN provider called Infiot acquired in August 2022. Stitching point solutions together, even if done in the cloud, still poses questions on how these services can seamlessly scale and how much time it will take, for example, to get the SD-WAN technology fully integrated in the Netskope product suite, or to lift their FWaaS engine to an acceptable level to protect the East-West traffic.
In essence, whilst Netskope has a strong SSE proposition, their complete SASE offering is still not fully baked.
If you are looking for simplicity, agility, efficiency, and productivity today, and not in 2-3 years, Cato is the best solution.
10. What incentive would a business have to switch from Fortinet to SASE via Cato?
Improved productivity - Cato can help you optimize application performance and user experience. The Cato SASE Cloud has a global private backbone which minimizes the exposure of network traffic to the unpredictable and unreliable internet
Improved efficiency - By moving from on-premise appliances to a cloud-native solution, procurement, management, and maintenance cost are dramatically reduced. Team members are freed to focus on business needs and outcomes instead of maintenance and support.
Improved agility - Whether tomorrow’s need will be additional security capabilities, business expansion, cloud migration or a new balance between office and remote work, a cloud-native network and security infrastructure allows you to meet new business requirements much faster than appliance-based infrastructure that mandates complex planning, sizing, procurement, deployment, integration, and maintenance.
Cato SASE business value
11. How will SASE have an impact on our existing infrastructure?
SASE has many capabilities that can augment your existing infrastructure today and replace it tomorrow to make your infrastructure more agile, secure, and efficient. For example, you can use a global private backbone to augment SD-WAN with a reliable global transport. You can offload internet security from your resource-constrained on-prem firewalls to an unlimited cloud-delivered security. You can also enable more users to work from remote without adding more VPN servers and without compromising on security or productivity.
12. Are you able to advise on any effort that Cato may have invested in reassuring potential Financial Service customers that the solution meets regulatory requirements?
Cato customers, including those from the financial services sector, all rely on us for their mission critical network and network security. To get their trust, we work continuously to make sure our enterprise network and our cloud service adhere to the highest security standards such as ISO, SOC, GDPR and others. Please see here for more details.
13. Are there any statistics or case studies that show typical cost savings achieved through migration from legacy networks and security to the Cato SASE solution?
Cato commissioned Forrester to run a survey across Cato Networks customers to quantify the benefits these customers have achieved in adopting the Cato SASE solution. The Total Economic Impact (TEI) report shows a stunning ROI of more than 240% when looking at the following benefits:
Reduced operation and maintenance
Reduced time to configure
Retired legacy systems (on-prem FW, SD-WAN)
The TEI document can be downloaded from here.
Cato SASE capabilities
14. Is it possible to implement the SASE architecture in countries such as: Spain, Italy, Colombia, Chile, Mexico and Venezuela?
If the SASE architecture is cloud-native, there are no limits to where it can be implemented. The implementation and availability are the responsibility of the SASE vendor. As a customer, you should focus on making sure there are SASE PoPs available withing 25ms round trip time from your users, branches, and datacenters. Cato’s SASE backbone consists of more than 75 POPs around the world with presence in all five continents, including China. New POPs are added on a quarterly basis to guarantee our customers a guaranteed minimum latency. More information can be found here.
15. Is Cato able to connect to other Next-gen firewalls through an IPsec / VPN tunnel?
Cato allows third party devices to connect to the Cato SASE cloud by means of an IPsec tunnel. A potential use case could be to leverage an existing NGFW for East-West traffic in the local premises and use the Cato Cloud to provide secure internet connectivity and East-West traffic protection for geographical sites.
16. Is it possible to interconnect two components of SASE from different vendors (e.g., Cato SASE to Cisco Viptela SD-WAN)?
Cato allows third party devices to connect to the Cato SASE cloud by means of an IPsec tunnel. Third party SDWAN devices will provide reliable connectivity to the Cato SASE cloud, once the traffic lands into one of our POPs, Cato handles security and middle-mile connectivity via the Cato private backbone.
17. How is security as a service, which is part of SASE, received by customers who have stringent compliance requirements like PCI-DSS / HIPPA etc.?
Organizations that are planning to migrate their network and security stack to the cloud must ensure they’re partnering with trusted providers who maintain the necessary levels of safeguarding and discipline of their own service security. The enterprise must evaluate the SASE vendor and make sure they adhere to the highest industry standards. Cato SASE services have received ISO27000, GDPR, SOC1, SOC2, SOC3 certifications. And with the Cato CASB solution, enterprises can configure their application control policies so that only applications which are compliant with PCI-DSS and/or HIPAA are authorized.
The face of the modern corporate network is changing rapidly. Digital transformation initiatives, cloud adoption, remote work, and other factors all have a significant impact... Read ›
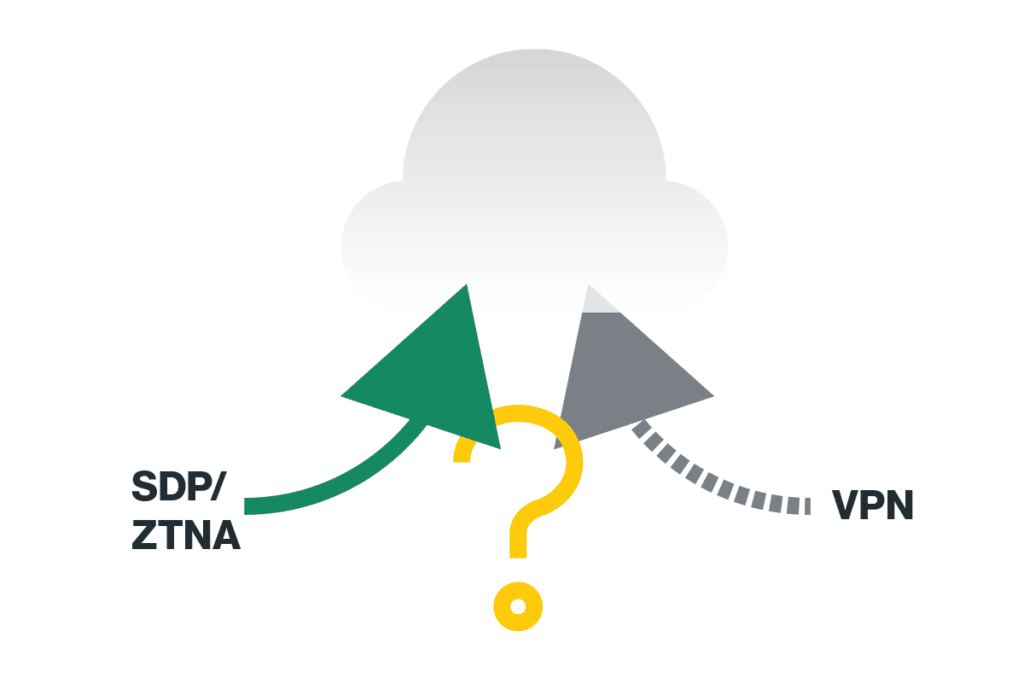
Remote Access VPNs are a Short-Term Solution The face of the modern corporate network is changing rapidly. Digital transformation initiatives, cloud adoption, remote work, and other factors all have a significant impact on where corporate IT assets are located and how corporate networks are used.
Companies looking to provide secure remote access to their off-site employees have largely chosen to expand their existing virtual private network (VPN) deployments. However, this is a short-term solution to the problems of the increasingly distributed enterprise. VPNs are ill-suited to meeting modern business needs and will only become less so in the future. It’s time for a change.
Secure Remote Access Has Become Business-Critical
Until a few years ago, most or all of an organization’s employees worked almost exclusively from the office. As a result, many corporate security infrastructures were perimeter-focused, working to protect employees and systems inside the office from external threats.
However, remote work has become normalized in recent years. Companies have been slowly shifting toward supporting remote work for some time now, and the pandemic accelerated this shift. Even as some companies try to pull workers back to the office, a higher percentage of employees are working remotely, at least part-time, than before the pandemic.
The ability to support remote work has become a critical capability for modern business. The popularity of remote work has made remote or hybrid work programs important for attracting and retaining talent. Additionally, a remote work program can also be a key component of a business continuity and disaster recovery (BC/DR) strategy as employees can work remotely in response to power or Internet outages, extreme weather, or public health crises.
[boxlink link="https://www.catonetworks.com/resources/why-remote-access-should-be-a-collaboration-between-network-security/"] Why remote access should be a collaboration between network & security | White Paper [/boxlink]
A Remote Access VPN Doesn’t Meet the Needs of the Modern Enterprise
A central component of an organization’s remote work program is secure remote network access. Employees need to be able to access corporate networks, resources, and data without fear of eavesdropping or other cyber threats. Historically, many organizations have relied upon VPNs to provide secure remote access. VPNs provide an encrypted connection between two points, securing traffic between a remote user’s computer and the VPN server on the corporate network. The problem is, however, that VPNs don’t meet the business needs of the modern enterprise.
Some of their shortcomings include:
Lack of Scalability: In general, corporate VPN deployments were designed for occasional usage by a small percentage of an organization’s workforce. Continuous usage by a larger group — as many organizations experienced during the height of the pandemic — results in significantly degraded performance and can render VPN deployments unusable for employees.
Performance Degradation: VPNs are point-to-point solutions, meaning that they are often designed to connect remote employees to the headquarters network. With the growth of cloud computing and the distributed enterprise, this can result in inefficient network routing and increased latency.
Nothing but Basic Security: VPNs are designed solely to provide an encrypted connection between a remote employee and the headquarters network. They offer no access control or other security functions to ensure that the traffic they carry is benign or to implement zero-trust access controls.
VPNs are intended to allow employees to securely do their jobs from outside the office. Yet their limitations mean that they offer neither productivity nor security.
VPNs struggle to meet the needs of the modern enterprise, and corporate IT architectures and business needs are rapidly evolving. As a result, the impact of VPNs on business operations will only grow more pronounced in the future.
Some key business operations that will be inhibited by VPNs include:
Regulatory Compliance: Companies are subject to various regulations, and these regulations are periodically updated to reflect updates to the cyber threat landscape and available security solutions. When zero trust and more robust threat monitoring and prevention capabilities become required by law, VPNs will be unable to provide them.
Mobile Support: The use of mobile devices for business purposes has grown dramatically in recent years. VPN deployments designed for desktops and laptops often have lower usability and performance for mobile users.
Cyber Risk Management: The remote workforce is an easy target compared to applications secured behind advanced firewalls and threat prevention tools. Enterprises cannot rely on VPNs to secure remote users, and are required to apply means to minimize risk and exposure to advanced attacks originating from remote user’s devices.
Moving Beyond the VPN
A remote access VPN is a thing of the past. It is a tool designed to implement a connectivity model that no longer works for the modern organization. While VPNs have significant limitations and challenges today, these issues will only be exacerbated over time as networks, threats, and compliance requirements evolve. Switching away from legacy technology today will improve an organization’s security posture in the future.
Secure Access Service Edge (SASE) and Security Service Edge (SSE) solutions with integrated zero trust network access (ZTNA) provide all of the secure remote access capabilities VPN lacks. It is a solution designed for the modern, distributed enterprise that converges a full stack of enterprise network security capabilities. SASE/SSE offers all of the benefits of a VPN and more with none of the drawbacks. Learn more about how Cato SASE Cloud — the world’s first SASE platform — can help you modernize your organization’s secure remote access capabilities by signing up for a free demo today.
Properly implemented, a zero trust architecture provides much more granular and effective security than legacy security models. However, this is only true if a zero... Read ›
You’ll Need Zero Trust, But You Won’t Get It with a VPN Properly implemented, a zero trust architecture provides much more granular and effective security than legacy security models. However, this is only true if a zero trust initiative is supported with the right tools. Legacy solutions, such as virtual private networks (VPNs), lack the capabilities necessary to implement a zero trust security strategy.
Zero Trust Security is the Future
Castle-and-moat security models were common in the past, but they are ineffective at protecting the modern network. Some of the primary limitations of perimeter-focused security models include:
Dissolving Perimeters: Legacy security models attempt to secure a perimeter that encapsulates all of an organization’s IT assets. However, with growing cloud adoption, this perimeter would need to enclose the entire Internet, making it ineffective for security.
Insider Threats: A perimeter-focused security model lacks visibility into anything inside of the corporate network perimeter. Insider threats — such as attackers that breach an organization’s defenses, supply chain vulnerabilities, and malicious users — are all invisible to perimeter-based defenses.
Trusted Outsiders: Castle-and-moat security assumes that everyone inside the perimeter is trusted, while outsiders are untrusted. However, the growth of remote work means that companies need to find ways to account for trusted users outside of the perimeter, forcing the use of insecure and unscalable VPNs.
The zero trust security model was designed to address the limitations of these legacy security models. Under the zero trust model, all access requests are evaluated independently against least privilege access controls. If a user successfully authenticates, their session is monitored for suspicious or risky activity, enabling potential threats to be shut down early.
94% of companies are in the process of implementing zero trust, making it one of the most common cybersecurity initiatives. Some of the drivers of zero-trust include:
Corporate Security: Data breaches and ransomware infections are common, and, in many cases, are enabled by the remote access solutions (VPNs, RDP, etc.) used to implement perimeter-based security. Zero trust promises to reduce the probability and impact of these security incidents, decreasing enterprise security risk.
Regulatory Compliance: The zero trust security model aligns well with regulators’ goals to protect sensitive information. Implementing zero trust is best practice for compliance now and may be mandatory in future updates of regulations.
Incident Investigation: A zero trust security system tracks all access requests on the corporate network. This audit trail is invaluable when investigating a security incident or demonstrating regulatory compliance.
Greater Visibility: Zero trust’s stronger access control provides granular visibility into access requests. In addition to security applications, this data can also provide insight into how corporate IT assets are being used and inform infrastructure design and investment.
Zero trust overcomes the problems of legacy, perimeter-focused security models. As corporate IT environments expand, cyber threats mature, and regulatory requirements become stricter, it will be a vital part of a mature security policy.
[boxlink link="https://www.catonetworks.com/resources/why-remote-access-should-be-a-collaboration-between-network-security/?utm_medium=blog_top_cta&utm_campaign=remote_access_whitepaper"] Why remote access should be a collaboration between network & security | White Paper [/boxlink]
A VPN Can’t Provide Zero Trust
The rise of remote and hybrid work has made secure remote access a vital capability for many organizations. VPNs are a well-established remote access solution, and many organizations turned to them to support their remote employees.
However, while VPNs offer employees secure remote access to the corporate network, they fail to provide crucial capabilities for a zero trust deployment. Some of the ways in which VPNs fall short include:
Access Management: VPNs are designed to provide an authenticated user with full access to the corporate network, simply creating an encrypted tunnel from the user’s machine to the VPN endpoint. Without built-in access controls, VPNs cannot enforce zero trust’s least privilege access policies.
Integrated Security: VPNs have no built-in security capabilities, meaning that traffic must be routed through a full security stack en route to its destination. With corporate assets scattered on-prem and in the cloud, this usually results in traffic being routed to a central location for inspection, increasing network latency.
Optimized Routing: VPNs are point-to-point solutions, which limit the routes that traffic can take and can cause significant latency due to suboptimal routing. This may cause security controls to be bypassed or disabled in favor of improved network performance.
Two of the foundational concepts of zero trust security are access control and monitoring for security issues during an authenticated user’s session. VPNs provide neither of these key capabilities, and their performance and scalability limitations mean that users may attempt to evade or bypass defenses to improve performance and productivity. While zero trust is rapidly becoming essential for corporate cybersecurity, VPNs are ill-suited to implementing a zero trust architecture.
Achieving Zero Trust with SSE and SASE
These two essential capabilities of zero trust — access control and session security monitoring — are the reason why Security Service Edge (SSE) and Secure Access Service Edge (SASE) are ideal for implementing a corporate zero trust program. SASE solutions include zero trust network access (ZTNA) functionality, which provides the ability to enforce least privilege access controls across the corporate WAN.
Alongside ZTNA, SSE and SASE solutions also offer a range of key security functions, including Firewall as a Service (FWaaS), an intrusion prevention system (IPS), a secure web gateway (SWG), and a cloud access security broker (CASB). Converging security functions with access control makes SASE an all-in-one solution for zero trust.
SASE’s design can also eliminate the network performance impacts of security. Deployed as a cloud-native solution on a global network of points of presence (PoPs), SASE can inspect traffic at the nearest PoP before optimally routing it to its destination. Cloud-native design ensures that converged security has the resources required to perform vital security functions without incurring latency.
Cato provides the world’s most robust single-vendor SASE platform, converging Cato SD-WAN and a cloud-native security service edge, Cato SSE 360, including ZTNA, SWG, CASB/DLP, and FWaaS into a global cloud service. With over 75 PoPs worldwide, Cato optimizes and secures application access for all users and locations, and is easily managed from a single pane of glass. Learn more about how Cato SASE Cloud can support your organization’s zero trust security goals by signing up for a free demo today.
Secure remote access is a common need for the modern enterprise. While employees almost exclusively worked from the office in the past, this has changed... Read ›
4 Ways Where Remote Access VPNs Fall Short Secure remote access is a common need for the modern enterprise. While employees almost exclusively worked from the office in the past, this has changed in recent years. The pandemic and the globalization of the workforce means that organizations may have users connecting and working from all over the world, and these remote users need secure remote access to corporate networks and other resources.
Historically, virtual private networks (VPNs) were the only available solution, and this familiarity has driven many organizations to expand their existing VPN infrastructure as the need for secure remote access has grown. However, VPNs are network solutions that were designed for corporate networks and security models that no longer exist, and cannot provide secure, high-performance network access to a workforce that requires a more modern remote access solution.
Let’s take a closer look at how remote access VPNs fall short:
1. Lack of built-in security/access management
VPNs are designed to provide secure remote access to corporate networks or IT resources. This includes creating an encrypted VPN tunnel between two endpoints — such as a remote employee’s computer and a VPN server on the corporate network — for business traffic to travel over.
While VPNs can protect against eavesdroppers, that’s about all that they can do. They include no built-in access management or security controls beyond requiring a username and password at logon. Protecting the corporate network against any threats that come over the VPN connection — such as those from an infected computer or a compromised user account — or implementing a zero-trust security policy requires additional security solutions deployed behind the VPN endpoint.
2. Geographic constraints
VPNs are designed to connect two points with an encrypted tunnel that network traffic can flow over. Securing corporate network traffic along its entire route requires VPN connections along each leg of that route. Corporate IT environments are becoming more distributed with the growth of cloud computing, remote sites, Internet of Things (IoT) devices, and business use of mobile devices. Securing access to all of the corporate WAN often creates tradeoffs between network performance and security.
VPNs’ lack of built-in security means that security solutions must be deployed behind each VPN server, making it more difficult to directly link every potential traffic source and destination. Instead, many organizations backhaul traffic to the headquarters network for inspection, degrading performance and increasing latency.
[boxlink link="https://www.catonetworks.com/resources/why-remote-access-should-be-a-collaboration-between-network-security/?utm_medium=blog_top_cta&utm_campaign=remote_access_whitepaper"] Why remote access should be a collaboration between network & security | White Paper [/boxlink]
3. Inefficient routing
The point-to-point nature of VPN connections means that a VPN connection can only provide secure access to a single location. For example, a user may be able to connect directly and securely to the corporate WAN.
However, corporate networks are increasingly distributed with infrastructure in on-prem data centers and scattered across multi-cloud environments. As a result, VPNs either force users to have VPNs configured for multiple different locations or to accept inefficient network routing that passes through a single VPN terminus en route to their intended destination.
4. Excessive trust in endpoint security
The goal of a VPN is to protect remote users’ network traffic from being intercepted or eavesdropped upon en route to its destination. VPNs don’t inspect the traffic that they carry or perform any access control beyond basic user authentication. As a result, VPNs are overly trusting in the security of the endpoints that they connect.
Some of the threats that VPNs provide no protection against include:
Infected Devices: If a remote employee’s device is compromised with malware, the malware can send traffic over the device’s VPN connection as well. This could allow an attacker to bypass security restrictions and gain access to corporate networks.
BYOD Devices: The rise of remote work has resulted in increased use of personally owned devices for business purposes. These devices can connect to corporate IT assets via VPNs and may be infected with malware or non-compliant with corporate security policies.
Compromised Accounts: VPNs only implement access control in the form of user authentication when setting up a VPN session. If an attacker has compromised a user’s authentication credentials (password, etc.), they can log in as that user and connect to corporate IT assets.
VPNs only secure the connection over which two endpoints are communicating. They’re overly trusting of the endpoints involved in the communication, which can result in malware infections or other threats to corporate assets.
Building Secure Remote Access for the Modern Enterprise
VPNs have significant limitations in terms of their performance, usability, and security. While these issues may have been manageable in the past, rapidly evolving corporate networks make them an increasingly unsuitable solution for secure remote access. Relying on legacy remote access VPNs forces companies to make choices between network performance and security.
Organizations looking to modernize their IT infrastructure to better support remote and hybrid work schedules need to replace their VPNs. Secure Access Service Edge (SASE) provides the capabilities that they need, eliminating the limitations of VPNs and providing numerous additional benefits.
With SASE, companies can move security to the network edge, enabling network optimization without sacrificing security. To learn more about how a cutting-edge SASE solution can enhance an organization’s remote access infrastructure, sign up for a free demo of Cato SASE Cloud, the world’s first global SASE platform, today.
Technological innovation, an evolving threat landscape, and other factors mean that the security needs of tomorrow may be very different from those of yesterday. However,... Read ›
Designing the Corporate WAN for the Security Needs of Tomorrow Technological innovation, an evolving threat landscape, and other factors mean that the security needs of tomorrow may be very different from those of yesterday. However, many organizations are still reliant on security models and solutions designed for IT architectures that are rapidly becoming extinct. Keeping pace with digital transformation and protecting against cyber threats requires a new approach to security and security architecture capable of supporting it.
Cybersecurity is Only Going to Get More Complicated
In many organizations, security teams are understaffed and overwhelmed by their current responsibilities. However, the challenge of securing organizations against cyber threats will only grow more difficult and complex. Some of the main contributors to these challenges include:
Evolving Networks: Corporate networks have grown and evolved rapidly in recent years with the adoption of cloud computing, remote work, and Internet of Things (IoT) and mobile devices. As technology continues to evolve, corporate IT networks will continue to grow larger and more diverse, making them more difficult to monitor, manage, and secure.
Sophisticated Threats: The cyber threat landscape is changing rapidly as demonstrated by the evolution of the ransomware threat and the emergence of a cybercrime service economy. Security teams must develop and deploy defenses against the latest attacks faster than attackers can circumvent them.
Regulatory Requirements: The enactment of the EU’s GDPR kicked off a wave of new data privacy laws, complicating the regulatory landscape. As laws are created and updated, security teams must take action to demonstrate that they are in compliance with the latest requirements.
Complex Policies: Changes in corporate networks, work models, and cyber threats drive the evolution of more complex corporate IT policies. For example, the introduction of bring your own device (BYOD) policies makes it necessary for security teams to enforce these policies and ensure that devices not owned by the company do not place it at risk.
Security teams can’t scale to keep up with their growing responsibilities, especially since a cyber skills gap means that many are already understaffed. Protecting the growing enterprise from the security threats of tomorrow requires a more manageable and maintainable security strategy.
[boxlink link="https://catonetworks.easywebinar.live/registration-101?utm_medium=blog_top_cta&utm_campaign=future_of_security_webinar"] The Future of Security: Do All Roads Lead to SASE? | Webinar [/boxlink]
Zero Trust Is a Core Pillar for Balancing Business and Security Needs
A corporate security policy should complement, not conflict with an organization’s business needs. Corporate security programs should be designed to support business processes and goals such as:
Remote Access: Employees need remote access to corporate resources, but the company needs to ensure that this remote access does not create additional risk to the organization. Corporate security programs should provide secure, high-performance remote access to corporate resources.
Access Management: Access management is essential to managing corporate security risk and maintaining regulatory compliance. Access control policies should allow legitimate users efficient access to corporate resources while preventing unauthorized access.
Compliance: Companies must be able to achieve and demonstrate compliance with a growing array of regulations. This includes global network visibility and security controls that meet regulatory requirements.
A zero trust security architecture provides a logical balance between security and business needs. With zero trust, access is granted to corporate assets on a case-by-case basis with decisions made based on least privilege access principles. This ensures that legitimate users have the access needed to do their jobs while minimizing the impact of compromised accounts and other intrusions. Additionally, authenticated users’ sessions should be monitored and terminated if risky or malicious activity is detected.
However, a zero trust security strategy is only useful if it can be enforced consistently across an organization’s entire corporate WAN without compromising network performance. Traditional, perimeter-focused security strategies — depending on virtual private networks (VPNs) and security appliances — force choices between network performance and security.
Zero Trust Security Requires a Strong, Stable Foundation
The effectiveness of a zero trust architecture depends on the solutions that it is built on. Zero trust must consistently apply access controls and security policies across the entire corporate WAN. If a weak point exists in an organization’s defenses, an attacker can use it as an entry point to gain access to corporate resources.
Implementing consistent security protections across the enterprise can be a significant challenge. The modern corporate WAN is composed of a variety of environments, including on-prem and cloud-based deployments, as well as IoT and mobile devices alongside traditional computers. These varying environments and endpoints affect the security solutions that can be deployed, which can result in a security architecture that suffers from visibility and enforcement gaps and complex management and maintenance.
However, while endpoints may differ across the corporate WAN, the network is mostly consistent regardless of environment. Deploying access management and security controls at the network level makes consistent enforcement of zero trust access controls and security policies possible.
Security Service Edge (SSE) and Secure Access Service Edge (SASE) provide an ideal foundation for a zero trust architecture. They converge zero trust network access (ZTNA) — which offers the access management that zero trust requires — with the tools needed to secure legitimate users’ sessions, including Firewall as a Service (FWaaS), an intrusion prevention system (IPS), a secure web gateway (SWG), and a cloud access security broker (CASB). In SASE solutions, these security functions are combined with built-in network optimization technologies to apply zero trust access controls and enterprise-grade security protection before routing traffic on to where it needs to go.
Cato provides the world’s most robust single-vendor SASE platform, converging Cato SD-WAN and a cloud-native security service edge, Cato SSE 360, including ZTNA, SWG, CASB/DLP, and FWaaS into a global cloud service. With over 75 PoPs worldwide, Cato optimizes and secures application access for all users and locations, and is easily managed from a single pane of glass. Learn more about how Cato SASE Cloud can help your organization to build a zero trust architecture that grows with the organization by signing up for a free demo today.
While zero trust promises reduced exposure to security incidents and data breaches, as well as simplified compliance with regulatory requirements, deploying a zero trust architecture... Read ›
A True Zero Trust Architecture Requires Security Integration While zero trust promises reduced exposure to security incidents and data breaches, as well as simplified compliance with regulatory requirements, deploying a zero trust architecture is not as simple as implementing least privilege access controls and replacing legacy virtual private networks (VPNs) with zero trust network access (ZTNA). Effective zero trust security acknowledges that strict access controls will not block all threats and takes steps to manage the security risks of authenticated users.
An integrated security architecture that goes beyond ZTNA is essential for effective zero trust security.
Zero Trust is About More Than Access Controls
Zero trust is a model intended to address the security risks associated with the legacy, perimeter-focused security model. Under this model, insiders — connected directly or via a VPN — are granted unrestricted access to corporate networks, systems, and applications.
Due to the limitations of VPNs, the focus of zero trust discussions is often on controlling users’ access to corporate resources. By strongly authenticating users and implementing the principle of least privilege and granting users only the access and permissions that are required for their roles, access management can significantly decrease an organization’s security risks.
However, strong user authentication and access control are not enough for zero trust. While zero trust can ensure that only legitimate, authenticated users have access to corporate resources, these users can still pose a threat due to malice, negligence, or compromised devices. Additionally, attackers may target an organization through attack vectors not associated with user accounts, such as exploiting a vulnerable web application. Effective zero trust architectures must have controls in place to address the threats not mitigated by strong access control.
Microsegmentation Limits Corporate Security Risks
Network segmentation is not a new concept. The legacy castle-and-moat security model is designed to segment an organization’s internal, private network from the public Internet. By forcing all traffic crossing this border to flow through network firewalls and other security solutions, organizations prevent some threats from ever reaching their systems.
Microsegmentation is designed to manage the potential damage caused by threats that manage to bypass perimeter-based defenses and gain access to an organization’s internal network. By breaking the enterprise network into multiple small networks, microsegmentation makes it more difficult for a threat to move laterally through an organization’s systems.
The primary goal of zero trust security is to limit the probability and impact of security incidents, but these breaches will still happen. Microsegmentation reduces the impact of these breaches by limiting the systems, applications, and data that an attacker can access without crossing additional security boundaries and subjecting their actions to further inspection.
Microsegmentation Needs More Than Just ZTNA
For many organizations, ZTNA is the cornerstone of their zero trust security strategy. By replacing legacy, insecure VPNs with ZTNA, an organization gains the ability to enforce least-privilege access controls and dramatically reduce the probability and impact of cybersecurity incidents.
However, while ZTNA is an invaluable solution for zero trust security, it’s not enough on its own. ZTNA provides the access controls needed for zero trust, but additional solutions are needed to implement microsegmentation effectively. In addition to ZTNA’s access controls, companies also need to be able to inspect network traffic and block potential threats from crossing network boundaries.
True zero trust security requires multiple solutions, not only ZTNA but also a network firewall and advanced threat prevention capabilities. Ideally, these solutions should be integrated together into a single solution, providing an organization with comprehensive security visibility and management without the complexity and network performance impacts of a sprawl of disparate standalone security solutions.
[boxlink link="https://catonetworks.easywebinar.live/registration-85?utm_medium=blog_top_cta&utm_campaign=using_sase_for_ztna_webinar"] Using SASE For ZTNA: The Future of Post-Covid 19 IT Architecture | Webinar [/boxlink]
SSE and SASE Enable Effective Zero Trust Security
Security Service Edge (SSE) and Secure Access Service Edge (SASE) are the ideal solution for implementing a corporate zero trust program.
SSE and SASE converge ZTNA, Firewall as a Service (FWaaS), and Advanced Threat Prevention capabilities — including an Intrusion Prevention System (IPS) and Next-Generation Anti-Malware (NGAM) within a single solution. Additionally, as a cloud-native security platform, SSE or SASE can be deployed near an organization’s users and devices, minimizing network performance impacts while providing consistent security visibility and policy enforcement across the corporate WAN.
Cato provides the world’s most robust single-vendor SASE platform, converging Cato SD-WAN and a cloud-native security service edge, Cato SSE 360, including ZTNA, SWG, CASB/DLP, and FWaaS into a global cloud service. With over 75 PoPs worldwide, Cato optimizes and secures application access for all users and locations, and is easily managed from a single pane of glass. Learn more about implementing an effective zero trust security program with Cato SASE Cloud by signing up for a free demo today.
SASE (Secure Access Service Edge) is an enterprise networking and security service that converges SD-WAN with multiple security functions – including FWaaS, CASB, DLP, SWG,... Read ›
An Inside Look at Life Before and After Deploying SASE SASE (Secure Access Service Edge) is an enterprise networking and security service that converges SD-WAN with multiple security functions - including FWaaS, CASB, DLP, SWG, and ZTNA - into a converged, cloud-native service that is manageable, optimized, secure and easy to use.But what does life after SASE really look like when implemented in an enterprise? To find out, we interviewed Ben De Laat, Head of IT Security at BrandLoyalty, who implemented Cato’s SASE Cloud, together with trusted Cato Partner and IPknowledge’s Managing Director, Steven de Graaf, who assisted with the implementation. This blog post is an abridged version of their insights. For a more detailed account of their experiences, you can read the full eBook, here: “Life after deploying SASE”.
SASE Migration Use Cases
First, let’s start our SASE journey by understanding when is the best time to transition to SASE? It’s strongly recommended to consider a migration to SASE when:
MPLS contracts are up for renewal and can be replaced with a more secure and higher performing alternative at a lower cost.
Employees are working at multiple global locations and require a secure and frictionless solution.
IT is managing complex networking environments and need a simple-to-use, high-performing and secure substitute.
The workforce is employed remotely or in a hybrid manner and needs a scalable and secure solution to connect all employees, but without backhauling and based on least-privileged access.
Your SASE Migration Plan
The operational migration to SASE is quick and efficient, sometimes requiring only weeks from start to finish! To accommodate and complement this quick shift, it is recommended to prepare a well thought out plan that can help evangelize the transition internally, monitor it and track success. We recommend such a migration plan include:
The strategic business value - How SASE will enable employees to focus on their core responsibilities, instead of them having to spend time and become frustrated when dealing with the effects of misconfigured firewalls or URL filters that are blocking valid websites.
The technological value - How SASE’s converged architecture and single software stack will eliminate IT and IS overhead and hassle, ensure optimized connectivity and provide an optimal security posture.
The financial value - How SASE will reduce the annual costs of networking and security, coupled with the value to the business.
[boxlink link="https://www.catonetworks.com/resources/inside-look-life-before-and-after-deploying-sase/?utm_medium=blog_top_cta&utm_campaign=before_and_after_sase"] An Inside Look: Life Before and After Deploying a SASE Service | Whitepaper [/boxlink]
Life After SASE: What’s New?
What can IT leaders, security professionals and business leaders expect once they’ve migrated to a SASE service? Here are six new SASE-driven organizational achievements that will make you throw your hands in the air and wonder why you didn’t migrate to SASE sooner.
Newfound Network VisibilitySASE’s convergence of end-to-end networking and security provides newfound visibility into the network. Rather than having network and security information split between discrete tools and services, IT has a single pane of glass with visibility into the entire network. All security and networking events are stored in a common database, mapped onto a single timeline. With one timeline for networking and security, IT can troubleshoot problems faster, spot anomalies quicker, and enable better operational monitoring.
An Optimal Security PostureSASE provides insights into which systems and services are being used by employees and third parties and their vulnerabilities. If necessary, this information can also help IT identify system replacements and eliminate shadow IT.
Better IT Services for the Business and for UsersSASE’s seamless, unified service displaces point solutions in a robust and reliable manner. This new architecture enables IT to monitor operational activity so they can optimize line provisioning. In addition, with SASE replacing the grunt work, IT teams have more time to work on strategic business initiatives.
Seamless Remote Work UnlockedSASE replaces high latency VPNs. Instead, traffic is routed over a global private backbone and monitored for threats. The result is high-performance and secure connectivity for all users, everywhere.
Optimized Connectivity and PerformanceSASE optimizes performance and the user experience by throughput maximization, providing increased and cost-effective bandwidth by routing traffic on a cloud-native, global, private backbone with multiple internet access links and active-active configurations.
Peace of MindWith SASE, both end-user and IT and IS can focus their efforts on fulflling business-critical initiatives. No more operational overhead, fretting over updates and lack of visibility into metrics and performance.Are you ready to get started with SASE? Read more about what the transition to SASE looks like in our new eBook “Life after deploying SASE”.
In one artificially cold evening, I invited myself to an intimate fireside chat with my new BFF, ChatGPT, who I now call CG in short. ... Read ›
Fireside Chat About Network Security With ChatGPT (AI) In one artificially cold evening, I invited myself to an intimate fireside chat with my new BFF, ChatGPT, who I now call CG in short.
Being a new artificial intelligence open to help humans as myself understand the universe we live in, I wanted to pick its brain (or should it be brains, in plural?) about a topic close to my heart.
I opened asking:
Can I ask you a few questions about network security?
And CG answered:
Sure, I would be happy to help with any questions you have about network security. As a large language model trained by OpenAI, I have been trained on a wide range of text and I can generate human-like responses based on the input that I receive
I asked:
What are the common components in network security?
CG knew it right away:
There are several common elements that are often found in network security, including:
Firewalls: These are devices or software programs that control incoming and outgoing network traffic based on predetermined security rules.
Encryption: This is the process of encoding data so that it can be transmitted securely and only accessed by authorized users.
Access control: This refers to the policies and procedures that regulate who or what is allowed to access specific network resources.
Intrusion detection and prevention: These are systems that monitor network traffic for signs of malicious activity and take action to prevent or respond to attacks.
Virtual Private Networks (VPNs): These are networks that use encryption and other security measures to create a secure connection over a public network, such as the internet.
Security patches and updates: Regularly applying security patches and updates to network devices and software is essential for closing vulnerabilities and keeping networks secure.
[boxlink link="https://catonetworks.easywebinar.live/registration-enhancing-your-enterprise-network-security-strategy?utm_medium=blog_top_cta&utm_campaign=enhancing_network_security_webinar"] Enhancing Your Enterprise Network Security Strategy | Webinar [/boxlink]
With all those components traditionally being on-premises, I asked:
What are the limitations of on-premises security products?
CG seemed to know exactly where I was going with this:
The limitations of on-premises security products can vary depending on the specific product and the context in which it is used. However, some common limitations of on-premises security products include:
High upfront cost: On-premises security products often require a significant upfront investment, including the cost of hardware, software, and installation. This can be a barrier for organizations with limited budgets.
Limited scalability: On-premises security products are typically designed for a specific number of users or devices, and adding additional users or devices can be challenging and costly. This can make it difficult for organizations to keep pace with growing needs.
Dependence on local infrastructure: On-premises security products are typically installed and operated on the organization's own servers and networks, which can create dependencies on local infrastructure. If there are problems with the local infrastructure, it can affect the availability and performance of the security product.
Maintenance and support: On-premises security products require ongoing maintenance and support, which can be time-consuming and costly. Organizations may need to hire specialized staff or contract with third-party service providers to provide this support.
Limited flexibility and agility: On-premises security products are often inflexible and can be slow to adapt to changing needs and requirements. This can make it difficult for organizations to respond quickly to new threats or opportunities.
Overall, the limitations of on-premises security products can make them less suitable for organizations that need to scale quickly, are constrained by budgets, or require high levels of flexibility and agility.
I wanted to know a bit more, so asked:
What about remote users? Where does ZTNA fit in here?
As you can imagine, CG is never caught off guard:
Remote users are individuals who access a network or its resources from outside the organization's physical location. In terms of network security, remote users present unique challenges, as they are often accessing the network over a public network such as the internet, which can be vulnerable to attacks.
One way to address these security challenges is through the use of a Zero Trust Network Architecture (ZTNA), which is a network security model that assumes that all users, regardless of location, are untrusted until they have been authenticated and authorized. With ZTNA, access to network resources is strictly controlled and only granted on a need-to-access basis. This approach can help to protect against a wide range of security threats, including those posed by remote users.
CG was starting to complain that I was asking too many questions too quickly, so I felt it was time to wrap it up with one final question:
Can you explain what is SASE and why it is important to digital enterprises?
CG was kind (and wise), and answered me this:
SASE, or Secure Access Service Edge, is a new approach to networking and security that is gaining popularity in the digital enterprise world. It is important because it combines networking and security functions into a single, cloud-based service, which offers several advantages over traditional networking and security approaches.
One of the key benefits of SASE is that it allows organizations to connect users and devices securely to any application or service, no matter where they are located. This means that employees can access the resources they need to do their job, even if they are working remotely or on-the-go. This can help improve productivity and enable organizations to support a remote and mobile workforce.
Another advantage of SASE is that it provides a more flexible and scalable approach to networking and security. Traditional networking and security solutions are often complex and inflexible, making it difficult for organizations to adapt to changing business needs. With SASE, organizations can easily add or remove users and devices, and scale their network and security capabilities up or down as needed.
Finally, SASE can help organizations reduce their networking and security costs. Because SASE is delivered as a cloud-based service, organizations don't have to invest in expensive hardware and software to set up and manage their networking and security infrastructure. This can help organizations save money and reduce the burden on their IT teams.
Overall, SASE is important to digital enterprises because it offers a more flexible, scalable, and cost-effective approach to networking and security.
I am not sure what the future holds for AI and for humanity, and whether there’s a place on earth for both of us, but for now, chatting with an AI is just fun.
Thank you, CG (https://chat.openai.com/)
As companies look to reduce corporate risk, protect against data breaches and other incidents, and maintain regulatory compliance, a zero trust security strategy provides significant... Read ›
Cloud-Based Security is Well-Suited for Zero Trust Architectures As companies look to reduce corporate risk, protect against data breaches and other incidents, and maintain regulatory compliance, a zero trust security strategy provides significant advantages when compared to legacy models.
However, zero trust is only effective if it is enforced and supported by strong security solutions. For most organizations, cloud-based solutions are the only means of supporting a secure, high-performance, and scalable zero trust architecture.
Effective Zero-Trust is Resource-Intensive
The zero trust security model was designed to address the inadequacies of traditional, castle-and-moat security. Under this legacy security model, all insiders are implicitly trusted and granted unrestricted access to corporate assets, while traffic crossing the boundary of the corporate network is considered suspect and subject to inspection. As cloud adoption and remote work become more common and cyber threat actors grow more sophisticated, this model is increasingly ineffective.
Zero trust security says that no one, internal or external, should be implicitly trusted. Instead, requests for access to corporate resources are considered on a case-by-case basis. Additionally, access controls are defined based on the principle of least privilege, minimizing access and limiting the potential impact of a compromised account.
However, while zero trust provides much better security than legacy models, it comes at the cost of additional resource consumption. Unlike virtual private networks (VPNs) used by the legacy security models, zero-trust network access (ZTNA) solutions must evaluate each access request against role-based access controls and other criteria. Additionally, authenticated users are monitored throughout their session for potential threats or risky actions, and these sessions are terminated as needed.
As corporate networks grow and traffic volumes expand, network security resource requirements increase as well. Without the right infrastructure, applying robust protections to growing networks without sacrificing network performance can be difficult.
[boxlink link="https://catonetworks.easywebinar.live/registration-enhancing-your-enterprise-network-security-strategy?utm_medium=blog_top_cta&utm_campaign=enhancing_network_security_webinar"] Enhancing Your Enterprise Network Security Strategy | Webinar [/boxlink]
Why Zero Trust Should Be Built In the Cloud
Historically, corporate security architectures have been deployed on-prem as part of a castle-and-moat security model. However, in the modern network, this increasingly causes network latency and performance degradation as traffic is backhauled to a central location for inspection.
As organizations work to implement zero-trust security across their entire IT infrastructures, security architectures should move to the cloud. Cloud-native security solutions provide numerous benefits. Including:
Asset Locations Agnostic: Companies are increasingly moving applications and data storage to the cloud, and the adoption of Software as a Service (SaaS) solutions contributes to this trend. Deploying security in the cloud means that it is close to where an organization’s applications and data are located, reducing the network latency and performance impacts of security inspection.
Greater Scalability: Cloud-native ZTNA solutions have the ability to scale to meet demand. Like microservices, additional instances can be deployed or allocated as needed to handle growing traffic volumes or computationally intensive security inspection.
Global Reach: As companies embrace remote or hybrid work models, employees may spend part or all of their time outside of the office. A ZTNA solution deployed as part of a global network can minimize latency impacts on user requests by bringing security near the network edge.
As corporate networks grow larger and more distributed, security must be scalable and not geographically constrained by the location of an organization’s on-prem infrastructure. Cloud-based — and more specifically cloud-native — security is essential to implementing effective zero-trust security without sacrificing network performance and employee productivity.
Implementing Zero Trust with SSE and SASE
A globally distributed, cloud-native ZTNA solution can meet the access control requirements of a corporate zero trust security program. However, effective zero trust is more than simply implementing least privilege access controls for all access requests. Once a user has authenticated, their entire session should be monitored for suspicious or malicious activities that could place the organization at risk.
To accomplish this, an organization requires additional security capabilities, such as a next-generation firewall (NGFW), an intrusion prevention system (IPS), a secure web gateway (SWG), and a cloud access security broker (CASB). Hosting these capabilities on-prem eliminates the benefits of cloud-based ZTNA as it forces traffic to be backhauled for security inspection and imposes the same scalability limitations of on-prem appliances. Effective zero trust requires a fully cloud-native network security stack.
Security Service Edge (SSE) and Secure Access Service Edge (SASE) are ideally suited to implementing zero trust security for the growing corporate WAN. SSE and SASE solutions integrate ZTNA functionality with a full network security stack, including Firewall as a Service (FWaaS), IPS, SWG, and CASB. SASE goes a step further, incorporating SD-WAN and network optimization capabilities as well. Deployed as a global, cloud-native solution, SSE and SASE implement a scalable, high-performance zero trust architecture.
Cato provides the world’s most robust single-vendor SASE platform, converging Cato SD-WAN and a cloud-native security service edge, Cato SSE 360, including ZTNA, SWG, CASB/DLP, and FWaaS into a global cloud service. With over 75 PoPs worldwide, Cato optimizes and secures application access for all users and locations, and is easily managed from a single pane of glass. Learn more about how Cato SASE Cloud makes building a zero trust security architecture that grows with the business easy by signing up for a free demo today.
Computers have become a core component of the modern company. Many employees spend most or all of their workdays on them, interacting with a variety... Read ›
Your Employees Need High-Performance, Secure Internet Access (and Aren’t Getting It) Computers have become a core component of the modern company. Many employees spend most or all of their workdays on them, interacting with a variety of different pieces of software. To do their jobs, employees need high-performance, secure access to corporate networks and IT assets. This is true whether an employee is working from the office or from off-site.
As remote and hybrid work schedules become more common, companies are deploying secure remote access solutions, such as virtual private networks (VPNs) to support them. However, this often means making tradeoffs between the performance of remote workers’ network connectivity and its security.
High-Performance Internet Access is Essential for the Modern Business
In the past, most of an organization’s employees worked on-site. This meant that they were connected directly to the headquarters network and protected by its perimeter-based security solutions. However, in recent years, a growing percentage of an organization’s employees are working from outside the office. Companies have adopted remote and hybrid work policies in response to the COVID-19 pandemic and to take advantage of the global workforce. At the same time, corporate IT assets are increasingly moving to the cloud. Software as a Service (SaaS) and cloud-native applications can offer improved performance, availability, and scalability for an organization’s employees and customers.
As a result of these shifts, the corporate LAN is becoming increasingly irrelevant as it hosts a diminishing percentage of an organization’s IT assets. However, the headquarters network is also where an organization’s security solutions are located and where the traffic is routed. Remote workers need high-performance network access to corporate networks and resources. Yet the design of many modern corporate networks means that this is not always a reality.
[boxlink link="https://www.catonetworks.com/resources/why-remote-access-should-be-a-collaboration-between-network-security/?utm_medium=blog_top_cta&utm_campaign=remote_access_collab"] Why remote access should be a collaboration between network & security | Whitepaper [/boxlink]
Where Legacy Secure Remote Access Falls Short
With a growing percentage of corporate workforces working on remote or hybrid schedules, a secure remote access VPN is essential. In many cases, companies are reliant on VPNs to provide this capability. Legacy VPN solutions are simply not designed to meet the needs of the modern enterprise.
Some of the primary ways in which they fall short include:
Inefficient Routing: Remote access VPNs are designed to route remote workers’ traffic to a VPN server, which is typically located on the corporate headquarters network. However, with a growing percentage of companies’ IT assets not located on-prem, this creates inefficient routing that degrades network performance and increases latency.
Inadequate Security: From a security perspective, all that a VPN does is provide an encrypted tunnel over which traffic is sent between the remote worker and the corporate network. Protecting against cyber threats and implementing a zero-trust security policy requires additional solutions alongside or instead of the VPN servers, which increases the cost and complexity of an organization’s IT infrastructure and limits its scalability.
VPNs were designed to implement a perimeter-focused security model where most of an organization’s IT assets were located on the headquarters network and needed to be protected against external threats. But this security model is no longer effective.
As a result, employees and companies are suffering from poor network performance in their remote access solutions as they try to use legacy secure remote access solutions to implement an outdated security model for a network architecture that no longer exists.
Choosing Both Performance and Security
VPNs’ design and lack of built-in security forces a tradeoff between network performance and security. Routing remote workers’ network traffic through the headquarters network for security inspection creates inefficient routes and network latency for remote users and cloud-based assets. Allowing remote users to connect directly to cloud-based assets, which provides the network performance that companies need, bypasses perimeter-based security stacks and leaves the organization at risk due to VPNs’ lack of built-in security.
Avoiding the tradeoff between network performance and security requires replacing legacy VPNs with a modern remote access solution. Secure Access Service Edge (SASE) provides numerous benefits over VPNs, including:
Cloud-Native Design: SASE solutions are deployed on globally distributed points of presence (PoPs). This allows them to be deployed geographically near an organization’s IT assets, reducing network latency, and enables them to take full advantage of the benefits of the cloud, such as scalability and availability.
Zero-Trust Access Control: SASE solutions integrate secure remote access capabilities in the form of zero-trust network access (ZTNA). This allows them to implement zero-trust access controls for remote users, a capability that VPNs do not share.
Integrated Security: SASE solutions combine ZTNA with a full network security stack and network optimization capabilities. Integrating security solutions with ZTNA eliminates the need for standalone security solutions alongside a VPN endpoint and enables direct connectivity to cloud-based assets without backhauling traffic to an on-prem security architecture or sacrificing security for network performance.
Corporate networks and business needs are evolving, and VPNs are not keeping up. Cato SASE Cloud, the world’s most mature single-vendor SASE platform, provides companies with the ability to support their remote workers with high-performance, secure network access. Learn more about improving the performance and security of your corporate WAN by signing up for a free demo of Cato SASE Cloud today.
Cybersecurity is all about risk management. Companies are faced with numerous, diverse cyber threats, and the job of the corporate security team is to minimize... Read ›
SASE is the Right Choice for Cyber Risk Management Cybersecurity is all about risk management. Companies are faced with numerous, diverse cyber threats, and the job of the corporate security team is to minimize the risk of a data breach, ransomware infection, or other costly and damaging security incident.
Cybersecurity tools and solutions are designed to help companies to achieve this goal of managing enterprise security risk. Of the many options out there, Secure Access Service Edge (SASE) is ideally suited to supporting all aspects of a corporate cyber risk management program.
Companies Face Significant Cyber Risks
Cybersecurity has become a top-of-mind concern for most businesses. Data breaches and ransomware attacks occur on a regular basis, often with price tags in the millions of dollars. Avoiding these incidents is essential to the profitability and survival of the business. With the growth of automated attacks and an “as a Service” cybercrime economy, the bar to entry into the cybercrime space has fallen. As cybercrime groups grow more numerous and sophisticated, any organization can be the target of a devastating attack.
Risk treatment strategies
Companies facing growing levels of cybersecurity risk need to take steps to manage these risks. In general, companies have four tools for risk treatment strategies: mitigation, transference, avoidance, and acceptance.
#1. Mitigation
Risk treatment by mitigation focuses on reducing the risk to the organization by implementing security controls. For cybersecurity risks, this could include patching vulnerable systems or deploying threat prevention capabilities that can identify and block attempted attacks before they reach vulnerable systems.
SASE solutions are ideally suited to threat mitigation due to their global reach and convergence of many security functions — including a next-generation firewall (NGFW), intrusion prevention system (IPS), cloud access security broker (CASB), zero-trust network access (ZTNA), and more — within a single solution. By consistently enforcing security policies and blocking attacks across the entire corporate WAN, SASE dramatically reduces an organization’s cybersecurity risk.
[boxlink link="https://catonetworks.easywebinar.live/registration-enhancing-your-enterprise-network-security-strategy?utm_medium=blog_top_cta&utm_campaign=enhancing_network_security_webinar"] Enhancing Your Enterprise Network Security Strategy | Webinar [/boxlink]
#2. Transference
Transference involves handing over responsibility for managing risk to a third-party provider. A common form of risk transference is taking out an insurance policy. In the event that an organization experiences a risk event — such as a cyberattack — the insurance provider takes on most or all of the cost of remediating the issue and restoring normal operations.
As a managed service, SASE can be useful for risk transference because much of the responsibility for implementing a strong security program is the responsibility of the service provider, rather than the organization. For example, maintaining the security stack — a process that can require in-depth network understanding and security expertise — is outsourced with the Firewall as a Service (FWaaS) capabilities of managed SASE deployments.
By enabling an organization to implement a mature security program and improving corporate security visibility and threat prevention, managed SASE makes it easier for organizations to get cybersecurity insurance. This is especially important with the rising risk of ransomware attacks, as insurance providers are implementing increasingly stringent security requirements for organizations to take out security policies.
#3. Avoidance
In some cases, cybersecurity risks that an organization may face are avoidable. For example, if a particular vulnerability poses a significant risk to an organization’s security, the choice to stop using the vulnerable component eliminates the risk to the organization. Avoidance-based risk treatment strategies can be highly effective, but they can come with opportunity costs if a secure alternative is not available for a vulnerable component.
SASE supports risk avoidance by offering a secure alternative to legacy network security solutions. Historically, many organizations have relied on a castle-and-moat security model supported by virtual private networks (VPNs) and similar solutions. However, these models have significant shortcomings, not least the rapid dissolution of the network perimeter as companies adopt cloud computing, remote work, Internet of Things (IoT), and mobile devices.
SASE solutions help to avoid the risks associated with legacy, castle-and-moat security models by supporting granular application-based protection. With zero-trust network access (ZTNA) built into SASE solutions, organizations can avoid the security risks associated with legacy VPNs, such as poor access management.
#4. Acceptance
Completely eliminating all risk is impossible, and, in some cases, the return on investment of additional risk treatment may be too low to be profitable. Companies need to determine the level of risk that they are willing to accept — their “risk appetite” — and use other risk treatment methods (mitigation, transference, and avoidance) to reduce their risk down to that level.
Ensuring that accepted cyber risk is within an organization’s risk appetite requires comprehensive visibility into an organization’s IT infrastructure and the risks associated with it. SASE provides global visibility into activities on the corporate WAN, and built-in security solutions enable an organization to gauge their exposure to various cyber threats and take action to manage them (via firewall security rules, CASB policies, and other controls) or intelligently accept them.
Cybersecurity Risk Management with Cato
Cato provides the world’s most robust single-vendor SASE platform, converging Cato SD-WAN and a cloud-native security service edge, Cato SSE 360, including ZTNA, SWG, CASB/DLP, and FWaaS into a global cloud service. With over 75 PoPs worldwide, Cato optimizes and secures application access for all users and locations, and is easily managed from a single pane of glass. Learn more about how your organization can manage its cyber risk exposure by signing up for a free demo of Cato SASE Cloud today.
Regulatory compliance is a major concern for many organizations. The risks and costs of non-compliance are numerous, including brand damage, regulatory penalties, and even the... Read ›
Addressing Regulatory Compliance Challenges for the Distributed Enterprise Regulatory compliance is a major concern for many organizations. The risks and costs of non-compliance are numerous, including brand damage, regulatory penalties, and even the inability to perform business-critical activities, such as processing payment card data.
Digital transformation and the evolution of the regulatory landscape can pose significant compliance challenges for organizations. In most cases, the legacy security technologies designed for primarily on-prem, castle-and-moat security models are no longer enough for security. Maintaining regulatory compliance in the face of digital transformation requires security solutions designed for modern IT environments.
Companies Face Significant Compliance Challenges
Every company is subject to several regulations. Common examples include employer laws, privacy regulations (such as the GDPR), and financial regulations (such as SOX). While this has been true for some time, the complexity of achieving and maintaining regulatory compliance has grown significantly in recent years. Two of the major contributors are the changing regulatory landscape and the expansion of corporate IT networks.
An Evolving Regulatory Landscape
Within the last few years, the regulatory landscape has grown increasingly complex. Companies have long been subject to regulations such as the Payment Card Industry Data Security Standard (PCI DSS, which protects the data of payment card holders, and the Health Insurance Portability and Accessibility Act (HIPAA), a US regulation for protected health information (PHI).
However, the enactment of the General Data Protection Regulation (GDPR) within the EU has set off a surge in new data privacy laws. The GDPR defined many new rights for data subjects, and laws based upon it, such as the California Consumer Privacy Act (CCPA) and its update the California Privacy Rights Act (CPRA), implement these and other rights to varying degrees.
The patchwork of new regulations makes it more difficult for companies to achieve, maintain, and demonstrate compliance. At the same time, existing regulations, such as PCI DSS, are undergoing updates to keep up with evolving data security threats and IT infrastructure.
The Increasingly Distributed Enterprise
Regulatory compliance has also been complicated by the growing distribution of the modern enterprise. The move to cloud computing means that companies may not know where their sensitive data — potentially covered under various regulations — is being stored and processed. The growth of remote work means that employees may be downloading and processing user records in jurisdictions with different data privacy laws.
Some regulations, such as the GDPR, prohibit the transfer of constituents’ data outside of countries with “adequate” data privacy laws, a requirement that might be violated by the use of cloud computing and support for remote work. Companies may also struggle to ensure that mandatory security controls are in place for data stored on devices and infrastructure outside of their control.
It is much harder to maintain compliance with digital transformations: data is all over the place (or the world) and so are users. The way to overcome this is to use a solution that ensures that the organization has global network visibility and the ability to enforce corporate policy across its entire IT infrastructure.
[boxlink link="https://www.catonetworks.com/resources/why-remote-access-should-be-a-collaboration-between-network-security/?utm_medium=blog_top_cta&utm_campaign=remote_access_collab"] Why remote access should be a collaboration between network & security | Whitepaper [/boxlink]
Legacy Remote Access Technology No Longer Works
Historically, companies have implemented a perimeter-focused security model. Initially, this ensured that traffic moving between the corporate network and the public Internet was inspected and secured. As companies expanded to the cloud and remote work, network traffic between remote sites was backhauled to a central location for inspection and enforcement before being routed to its destination.
Correctly implemented, this model may give an organization the visibility and control that it requires for compliance. However, it does so at the cost of network performance and scalability. As corporate networks expand, a growing volume of traffic must pass through the central inspection point.
Growing traffic volumes place additional strain on network and security solutions and add to the network latency impacts on cloud-based software and remote users. Additionally, as virtual private networks (VPNs), the solutions used to implement these castle-and-moat designs, lack any built-in access controls or security capabilities, centralized security architectures require multiple standalone solutions, making them complex and expensive to scale to meet demand.
Maintaining Regulatory Compliance Despite Enterprise Expansion
The limitations of VPNs and legacy security architectures have inspired the zero trust security movement. Implementing a zero trust security model at scale requires solutions capable of enforcing access controls across an organization’s entire IT infrastructure without sacrificing network performance or visibility.
The right way to accomplish this is with a zero trust architecture that is cloud-native and globally available. Cloud-native security solutions can acquire additional resources as needed, allowing them to scale with the business and growing traffic volumes. Additionally, cloud-native security services are available everywhere that an organization’s users and data are, decreasing the performance impacts of regulatory compliance and security.
With the right zero trust architecture, there is no need to compromise or balance between business growth and regulatory compliance. Strong, scalable security meets regulatory requirements, and global visibility and automated data collection and report generation simplify regulatory compliance. Security Service Edge (SSE) and Secure Access Service Edge (SASE) provide the zero trust security architecture that enterprises need to achieve regulatory compliance. By converging networking and network security functionality into a cloud-native solution, SASE moves security tools needed for dynamic regulatory compliance to the cloud.Cato provides the world’s most robust single-vendor SASE platform, converging Cato SD-WAN and a cloud-native security service edge, Cato SSE 360, including ZTNA, SWG, CASB/DLP, and FWaaS into a global cloud service. With over 75 PoPs worldwide, Cato optimizes and secures application access for all users and locations, and is easily managed from a single pane of glass. Learn more about simplifying network security and regulatory compliance with Cato SASE Cloud by signing up for a free demo today.
As security professionals, we are inundated with news stories and articles about cyber attacks and breached companies. Sometimes, attacks become newsworthy because of the attacked... Read ›
The 3 Worst Breaches of 2022 That You Should Know About (That Didn’t Get Much Press or Attention) As security professionals, we are inundated with news stories and articles about cyber attacks and breached companies. Sometimes, attacks become newsworthy because of the attacked company, for example when it's a notable enterprise. Other times, the attack technique was so unique, that it deserves a headline of its own.
In this blog post, we take a different approach. Instead of naming and shaming, we will review three of the worst breaches and attacker tactics and techniques of 2022 that might have gone by unnoticed, and use them as a way to learn how to better protect ourselves.
This blog post is based on episode #9 of the Cato Networks cybersecurity Master Class (“The 3 Worst Breaches of 2022 That You Probably Haven’t Heard Of”). The Master Class is taught by Etay Maor, Sr. Director of Security Strategy at Cato Networks and an industry recognized cyber security researcher and keynote speaker. You can watch all the episodes of the Master Class, here.
Attack #1: Ransomware: The Sequel
Ransomware as a service is a type of attack in which the ransomware software and infrastructure are leased out to the attackers. In this first case, the threat actors used ransomware as a service to breach the victim’s network. They were able to exploit third-party credentials to gain initial access, progress laterally and ransom the company, all within mere minutes. The swiftness of this attack is unusual. In many cases, attackers stay in the networks for weeks and months before demanding the ransom.
So, how did attackers manage to ransom a company in minutes, with no need for discovery and weeks of lateral movement?
Watch the Master Class to learn more about the history of ransomware, ransomware negotiation and various types of ransomware attacks.
[boxlink link="https://catonetworks.easywebinar.live/registration-the-3-worst-breaches-of-2022?utm_medium=blog_top_cta&utm_campaign=3_worst_breaches_webinar"] The 3 Worst Breaches of 2022 (That You Probably Haven’t Heard Of) | Webinar [/boxlink]
Attack #2: Critical Infrastructure: Sabotaging Radiation Alert Networks
Attacks on critical infrastructure are becoming more common and more dangerous. Breaches of water supply plants, sewage systems and other such infrastructures could put millions of residents at risk of a human crisis. These infrastructures are also becoming more vulnerable, with tools like Shodan and Censys that enable finding vulnerabilities fairly easily.Let Etay Maor take you on a deep dive into ICS (Industrial Control Systems). Why are attacks moving from IT to OT (Operational Technology)? And, in the Master Class, we discuss security solutions for protecting critical infrastructure, like zero trust and SASE.
Attack #3: Ransomware (That Could Have Been Prevented)
The third attack is also a ransomware attack. This time, it consisted of a three steps approach of infiltration, lateral progression over the network, and exfiltration. You’ll learn the ins and outs of this attack, including who the victim is and why their point security solutions were not able to block this attack.Etay Maor conducts a full breach analysis, taking us from a “single-point-of-failure” mindset to a holistic and contextual approach that requires securing multiple choke points.To learn more about each of these three attacks, what to expect in 2022-2023 and how a converged security solution can assist in preventing similar attacks in the future, watch the Master Class.
Zero-day attacks are a growing threat to corporate cybersecurity. Instead of reusing existing malware and attack campaigns that are easily detected by legacy security solutions,... Read ›
Effective Zero-Day Threat Management Requires Cloud-Based Security Zero-day attacks are a growing threat to corporate cybersecurity. Instead of reusing existing malware and attack campaigns that are easily detected by legacy security solutions, cyber threat actors tune their malware to each campaign or even each target within an organization.
These zero-day attacks are more difficult and expensive to detect, creating strain on corporate security architectures. This is especially true as the growth of corporate IT infrastructures generates increasing volumes of network traffic that must be inspected and secured. Managing cyber risk to corporate IT systems requires security solutions that can scale to meet growing demand.
Zero-Day Threats Are Harder to Detect
Historically, antivirus and other threat detection technologies used signature-based detection to identify malware and other malicious content. After a new threat was identified, a signature was built based on its unique features and added to the signature library. All future content would be compared to this signature, and, if it matched, would be identified as a threat and remediated.
This approach to threat detection requires limited resources and can be highly effective at identifying known threats. However, a signature must first exist for threats to be identified. The growth of zero-day attacks leaves signature-based detection blind to many threats and creates a delay between the emergence of a new threat and solutions’ ability to identify it.
Other approaches to threat detection can identify novel and zero-day threats. For example, anomaly detection identifies deviations from normal behavior that could point to either benign errors or attempted attacks. Behavioral analysis monitors the actions of user accounts, applications, and devices for risky or malicious behaviors that pose a threat to a system.
These forms of threat detection have the ability to provide much more robust protection to an organization’s systems against novel and evolving threats. However, this improved detection comes at a price. In general, anomaly and behavioral detection consume more processing power and require access to larger datasets than traditional, signature-based detection systems. Also, non-signature detection systems have the potential for false positive detections, creating additional alerts for security personnel to sort through.
[boxlink link="https://catonetworks.easywebinar.live/registration-enhancing-your-enterprise-network-security-strategy?utm_medium=blog_top_cta&utm_campaign=enhancing_network_security_webinar"] Enhancing Your Enterprise Network Security Strategy | Webinar [/boxlink]
Legacy Firewall Security Solutions Can’t Keep Up
Zero-day threat detection is essential for protecting against modern cyber threats, but it is also resource-intensive. As traffic volumes increase, the additional work required to identify novel threats can put strain on an organization’s network security architecture.
This is especially true for organizations that rely on legacy next-generation firewalls (NGFWs). Firewall security solutions deployed within an organization’s on-prem data center have limited scalability. If traffic volumes exceed the compute capabilities of an appliance-based solution or software running on a server, then the organization needs to acquire and deploy additional hardware to secure the traffic without compromising network performance. This is especially true if TLS decryption is required for inspection of encrypted traffic as this can exhaust an appliance’s compute capacity.
As the cyber threat landscape evolves, organizations will need to identify and respond to more numerous and sophisticated cyber threats, which increases the resource requirements of cyber threat detection. With legacy, appliance-based solutions deployed on-prem, companies are already forced to choose between properly protecting their environments against cyber threats and the performance of their corporate networks.
Cloud-based Security is Essential for Modern Threat Management
One of the main limitations of security solutions is that effectively inspecting and securing network traffic is computationally expensive. With limited resources, TLS decryption and in-depth inspection of network traffic can cause performance issues, especially as corporate networks and their traffic bandwidth increase.
The best way for companies to keep pace with the growing resource requirements of security is to take advantage of cloud scalability and adaptability. Cloud-native security solutions can expand the resources that they consume as needed to cope with growing network traffic volumes and the associated cost of security inspection and threat detection and response.
Secure Access Service Edge (SASE) solutions take full advantage of the benefits of the cloud to optimize corporate network security. SASE solutions converge many network and security functions into a single solution, eliminating the redundancy and waste of standalone solutions. Additionally, as cloud-native solutions, SASE solutions elastically scale to meet growing network traffic volumes or the resource requirements of expensive security operations.
In addition to solving the problem of the resource consumption of security functions, SASE solutions also provide numerous other benefits, including:
Greater Visibility: SASE solutions integrate traffic inspection and threat detection across the entire corporate WAN and not only the internet. This provides improved security visibility and additional context regarding cyber threats.
Improved Threat Detection: SASE solutions can also leverage this increased visibility — as well as threat intelligence data — to more accurately identify threats to the organization. Security integration also means that threat response activities can be coordinated across the corporate WAN, providing better protection against distributed attacks.
Enhanced Network Performance: SASE solutions are globally distributed and integrate network optimization functions as well as security features. Traffic can be inspected and secured at the nearest SASE point of presence before being optimally routed to its destination.
Cato provides the world’s most robust single-vendor SASE platform, converging Cato SD-WAN and a cloud-native security service edge, Cato SSE 360, including ZTNA, SWG, CASB/DLP, and FWaaS into a global cloud service. With over 75 PoPs worldwide, Cato optimizes and secures application access for all users and locations, and is easily managed from a single pane of glass. Learn more about how Cato SASE Cloud’s threat detection capabilities can help protect your organization against zero-day threats with a free demo.
Ever since the 1990s, IT has been dominated by appliance-centric architecture. But in 2015, Cato revolutionized this paradigm by envisioning networking and security delivered as... Read ›
SASE Vendor Selection: Should You Focus on Outcomes or Tools? Ever since the 1990s, IT has been dominated by appliance-centric architecture. But in 2015, Cato revolutionized this paradigm by envisioning networking and security delivered as a converged, cloud-native service. This evolution was not unlike the massive shift created by AWS’s global cloud service, which provided a new kind of infrastructure that supported scalability, resiliency, elasticity, security, connectivity and global distribution (and more).
While AWS is not necessarily the cheapest option, businesses today still choose AWS (or Azure, Google Cloud and other public cloud providers) so they can focus their IT teams on business critical projects and strategic initiatives, instead of requiring them to maintain and manage infrastructure. In other words, AWS became an extension of the IT team, turning it into a business enabler.
Cato is following a similar path. The Cato SASE Cloud provides high performance routing and security inspection of enterprise network traffic. To ensure high availability and maximal security posture, the Cato SASE cloud is optimized and maintained by our professionals from DevOps, networking and security. As a result, Cato too is an extension of the IT team, while owning the outcome: a secure and resilient infrastructure. This blog post compares Cato SASE to legacy applications while demonstrating the strategic business value of Cato. A more in-depth comparison can be found in the whitepaper which this blog post is based on. Click here to read it.
Cato SASE Cloud vs. Legacy Appliances
How is the value of Cato justified? While legacy appliances are tools, Cato SASE Cloud is built for outcomes: highly available, scalable and secure connectivity for everyone, everywhere.
Cato ensures:
Disruption-free capacity handlingNo infrastructure maintenance24x7 NOC24x7 SOC24x7 Support
Tools on the other hand create:
Complexity when deploying and planning capacity A capacity vs. usage tradeoffDifficulties maintaining the security postureAn extended attack surface of appliancesLimited support effectiveness and limited customer environment access
[boxlink link="https://www.catonetworks.com/resources/outcomes-vs-tools-why-sase-is-the-right-strategic-choice-vs-legacy-appliances/?utm_medium=blog_top_cta&utm_campaign=features_vs_outcomes"] The Pitfalls of SASE Vendor Selection: Features vs. Strategic Outcomes | Whitepaper [/boxlink]
Cloud-Delivered vs. Appliance-Delivered Features
Features differ in their deployment, management, scalability, and effectiveness. Let’s look at some examples of these differences through the lens of managed vs. standalone features and adaptable vs. rigid features.
Managed vs. Standalone Features
Managed - Cato’s IPS is always in a fully optimized security posture. We evaluate threats and vulnerabilities, develop mitigations and deploy only after ensuring performance isn’t negatively impacted.
Standalone - An IPS from an appliance vendor requires the IT team to deploy, assess the deployment impact on performance and ensure all appliances are kept up-to-date. Consequently, these teams are in “detect mode” instead of “prevent mode”.
Adaptable vs. Rigid Features
Adaptable - Cato’s cloud-native architectures make inspection capabilities available whenever there are new loads or new requirements, at any scale or location, and seamlessly.
Standalone - When locations and capacity are constrained, it’s the customer’s responsibility to predict future inspection capabilities. As a result, new branches, users and applications turn into business disruptors, instead of driving growth.
Conclusion
“DIY” is a good solution in some cases, but not for enterprises looking to achieve agile and flexible networking and security infrastructure. The required infrastructure expertise coupled with the lack of IT resources make DIY unsustainable in the long haul. Instead, a new partnership model with technology-as-a-service providers is required. This partnership can help organizations achieve the outcomes they need to drive their business and achieve their strategic goals.
Read more from the whitepaper “The Pitfalls of SASE Vendor Selection: Features vs. Strategic Outcomes”, for a closer look.
The cybersecurity industry is well known for its buzzwords. Every year, a new word, phrase, or acronym emerges to describe the latest and greatest tool... Read ›
If You Want a True Security Platform, You Need SASE The cybersecurity industry is well known for its buzzwords. Every year, a new word, phrase, or acronym emerges to describe the latest and greatest tool that is absolutely essential to an organization’s ability to protect itself against cyber threats. Recently, the focus has been on ‘security platforms’, which are intended to simplify security architectures by consolidating many security capabilities within a single solution. This approach can provide many benefits, but many of these so-called ‘security platforms’ lack the ability to meet the security needs of the modern business.
The Goal: Combining Many Security Functions Within a Single Solution
Companies face a variety of cyber threats, a problem that is exacerbated by the evolution of corporate IT infrastructures and the cyber threat landscape. With the rise of cloud computing, remote work, and Internet of Things (IoT) and mobile devices, cyber threat actors have many potential targets for their attacks.
Historically, companies addressed these new cyber risks by selecting security solutions that were targeted at solving a certain problem or closing a particular security gap. For example, an organization may augment firewall security solutions with the threat prevention capabilities of an intrusion prevention system.
However, this approach often results in complex, unusable security architectures. With many standalone security solutions, corporate security teams are overloaded with security alerts, waste time configuring and context switching between solutions, and must contend with security tools that have both overlapping functionality and leave visibility and security gaps.
With the cybersecurity skills gap making it difficult to attract and retain essential security talent, many companies are focusing their efforts on simplifying and streamlining their security architectures. Integrated security platforms are the new goal, combining many security functions within a single solution in an attempt to reduce or eliminate the challenges caused by security architectures composed of an array of standalone solutions.
[boxlink link="https://catonetworks.easywebinar.live/registration-enhancing-your-enterprise-network-security-strategy?utm_medium=blog_top_cta&utm_campaign=enhancing_network_security_webinar"] Enhancing Your Enterprise Network Security Strategy | Webinar [/boxlink]
A Security Platform Needs to Meet a Company’s Security Needs
An effective security platform is one that is designed to meet the needs of the modern, growing corporate network. This includes the following capabilities:
Product Consolidation: Product consolidation is the key selling point of a security platform since it allows organizations to eliminate the complexity and overhead of managing many standalone solutions. Security platforms should offer several security functions — such as a next-generation firewall (NGFW), zero-trust network access (ZTNA), intrusion prevention system (IPS), cloud access security broker (CASB), and more — and be managed and monitored via a single pane of glass.
Universal Protection: The corporate WAN is rapidly expanding and includes on-prem, cloud-based, and remote devices. A security platform must be able to secure all of the corporate WAN without negatively impacting network performance, such as the latency caused by backhauling network traffic to an organization’s on-prem security architecture for inspection and policy enforcement.
Scalable Protection: Corporate networks are growing rapidly, and the introduction of cloud infrastructure, IoT devices, and other endpoints increases the volume of traffic flowing over the corporate WAN. Security platforms must be able to scale to secure growing traffic volumes without negatively impacting network performance or requiring the deployment of additional solutions.
Cloud Support: Cloud adoption is near-universal across organizations, and 80% of companies have deployed multi-cloud infrastructure. Cloud-based and on-prem infrastructure differs significantly, and security platforms should operate effectively and provide strong risk management across an organization’s entire IT architecture.
Consistent Policy Enforcement: Consistently enforcing security policies across on-prem and cloud-based infrastructure is complex, especially in multi-cloud environments where different cloud providers offer different sets of security tools and configuration options. A security platform should enable an organization to enforce security policies across all of the environments that compose an organization’s cloud infrastructure.
The goal of replacing standalone security solutions with security platforms is to simplify and streamline security. To accomplish this, security platforms must meet all of an organization’s security needs. Otherwise, companies will need to deploy additional security tools to close gaps, starting the cycle over again.
SASE is the Ultimate Security Platform
Replacing an organization’s complex security infrastructures with an integrated security platform can be a significant challenge. With diverse environments, each with its own unique security needs and limitations, identifying and configuring a solution that is universally effective can be difficult.
Secure Access Service Edge (SASE) is the only security platform with a guaranteed ability to meet all of the security requirements of the modern business. Some of the key capabilities of SASE include:
Cloud-Native Protection: SASE solutions are deployed within cloud points of presence (PoPs). SASE’s cloud-native design ensures that it can scale with the business and can secure corporate devices wherever they are.
Converged Security: SASE solutions converge many network and security functions — including ZTNA, IPS, and firewall security functions — into a single solution. This convergence eliminates the complexity caused by standalone solutions and can also enable increased efficiency and optimization.
Network-Level Protection: SASE secures the corporate network by sending all traffic through a SASE PoP en route to its destination. This ensures consistent security policy enforcement and management across all of an organization’s IT environments.
Cato provides the world’s most robust single-vendor SASE platform, converging Cato SD-WAN and a cloud-native security service edge, Cato SSE 360, including ZTNA, SWG, CASB/DLP, and FWaaS into a global cloud service. With over 75 PoPs worldwide, Cato optimizes and secures application access for all users and locations, and is easily managed from a single pane of glass. Learn more about consolidating and streamlining your organization’s security architecture with Cato SASE Cloud by signing up for a free demo today.
Firewalls – the foundation of an organization’s network security strategy – filters network traffic and can enforce an organization’s security rules. By limiting the traffic... Read ›
Why Application Awareness is Essential for Firewall Security Firewalls - the foundation of an organization’s network security strategy - filters network traffic and can enforce an organization’s security rules. By limiting the traffic that enters and leaves or enters an organization’s network, a firewall can dramatically reduce its vulnerability to data breaches and other cyberattacks.
However, a firewall is only effective if it can accurately identify network traffic and apply the appropriate security policies and filtering rules. As application traffic is increasingly carried over HTTP(S), traditional, port-based methods of identifying application traffic are not always effective. Application awareness identifies the intended destination of application traffic, providing the visibility that next-generation firewalls (NGFWs) require to apply granular security policies.
What is Application Awareness?
Different network protocols have different functions and present varying security risks. This is why firewalls and other network security solutions are commonly configured with rules that apply to specific ports and protocols, such as restricting external access to certain services or looking for protocol-specific threats.
However, the growth of Software as a Service (SaaS) solutions and other web-based solutions has caused the HTTP(S) protocol to support a wider range of services. As a result, filtering traffic and applying security rules based on port numbers is less effective than before.
Application-aware networking and security solutions can identify the application that is the intended destination of network traffic. Doing so without relying solely on common port numbers requires a deep understanding of the network protocol and commands used by the application. For example, web browsing data and webmail data carried over HTTPS may have similar network packet headers but contain very different types of data.
The ability to differentiate between types of application traffic can provide several benefits beyond security. For example, an organization may implement network routing and quality of service (QoS) rules for traffic based on the target application. Latency-sensitive videoconferencing traffic may be prioritized, while browsing traffic to social media and other non-business sites may have a lower priority if it is permitted at all.
[boxlink link="https://catonetworks.easywebinar.live/registration-101?utm_medium=blog_top_cta&utm_campaign=future_of_security_webinar"] The Future of Network Security: Do All Roads Lead to SASE? | Webinar [/boxlink]
How Application Awareness Enhances Firewall Security
The Internet is increasingly dominated by HTTP(S) traffic as various applications move to web-based models with the growth of SaaS and other cloud-based services. The rise of DNS over HTTPS (DoH) and other protocols that attempt to leverage built-in TLS support within the HTTPS protocol accelerates this trend. However, these various types of traffic carried over the HTTP(S) protocol may present different levels of risk to the organization and be vulnerable to different types of attacks.
A one size fits all approach to securing these diverse applications can negatively impact application performance and security. An organization’s firewall rules may be configured based on the traffic associated with a particular protocol as a whole, so all web traffic may be permitted through, while other protocols may be blocked entirely. Additionally, security solutions may inspect traffic for malicious content that poses no risk to a particular application or overlook application-specific security risks.
Integrating application awareness into security solutions provides them with valuable context that can improve network security as well as network routing. For example, an understanding that a particular type of traffic is associated with Internet of Things (IoT) devices can enable next-generation firewalls (NGFWs) to search for threats common to those devices or block access to the devices from outside of the corporate WAN.
Granular network traffic inspection and security rules are essential to implementing an effective zero-trust security strategy. Application awareness is essential to achieving this granularity, especially as increasing volumes of application traffic are carried over the HTTP(S) protocol.
Taking Full Advantage of Application Awareness with SASE
Application awareness can provide benefits for numerous network tools, including those with both network performance and security functions. For example, on the networking side, application awareness is valuable to software-defined WAN (SD-WAN) solutions because it informs the routing of various traffic types over the corporate WAN and can help determine the priority of different types of traffic. On the security side, firewalls and other security solutions can use application awareness to tune security rules to an application’s unique needs and risk profile.
While application awareness can be implemented in each solution that uses it, this is an inefficient approach. SD-WANs, NGFWs, and other solutions that use application awareness all need to know the intended destination of a particular type of traffic. If each solution independently maintains a library of traffic signatures and applies them to each traffic flow, the result is a highly-redundant system that may negatively impact network latency and performance.
Secure Access Service Edge (SASE) solutions eliminate this redundancy and these performance impacts by converging many of the functions that require application awareness into a single solution. Under this design, SD-WANs, NGFWs, and other solutions that need insight into the destination of application traffic can access this information without computing it independently.
Cato provides the world’s most robust single-vendor SASE platform, converging Cato SD-WAN and a cloud-native security service edge, Cato SSE 360, including ZTNA, SWG, CASB/DLP, and FWaaS into a global cloud service. With over 75 PoPs worldwide, Cato optimizes and secures application access for all users and locations and is easily managed from a single pane of glass. Learn more about Cato SASE Cloud’s targeted application security capabilities by signing up for a free demo today.
Cloud-based deployments provide many benefits to organizations, such as greater scalability, flexibility, and availability than many organizations can achieve in-house. However, cloud infrastructure also comes... Read ›
Designing a Security Strategy for the Multi-Cloud Enterprise Cloud-based deployments provide many benefits to organizations, such as greater scalability, flexibility, and availability than many organizations can achieve in-house. However, cloud infrastructure also comes with its costs, such as the challenges of securing an organization’s on-premises and cloud environments. For organizations making the move to the cloud, redesigning their security strategies to protect multi-cloud deployments can pose a significant challenge.
Most Companies Are Multi-Cloud
Cloud adoption is growing rapidly as companies take advantage of the numerous benefits and advantages available with cloud infrastructure. However, most organizations are not selecting a single cloud provider to augment or replace their existing on-prem data centers. In fact, 89% of businesses have a multi-cloud strategy.
When looking to move to the cloud, many options are available, and different cloud platforms are optimized for particular use cases and have their own advantages and disadvantages. Since companies’ cloud-based infrastructure is designed to fulfill various purposes — data storage and hosting of both internal and public-facing applications — the variety of cloud environments makes it possible for companies to choose environments that are optimized for a particular use case.
Multi-Cloud Environments Create Security Challenges
While multi-cloud deployments provide numerous advantages when compared to on-prem infrastructure, such as scalability, flexibility, availability, and cost savings, they also have their downsides.
Some of the security challenges associated with multi-cloud environments include:
Shared Responsibility Model: In cloud environments, a cloud customer shares responsibility for managing and securing their cloud infrastructure with the cloud provider. The cloud customer must gain and maintain expertise in understanding and securing their part. Disparate Environments: Multi-cloud deployments are composed of cloud infrastructure developed by various providers. The heterogeneity of an organization’s cloud deployment can make it complex to develop firewall security rules and enforce consistent security policies across multi-cloud and on-prem environments. On-Prem and Cloud-Based Infrastructure: Organizations rarely abandon on-prem infrastructure entirely when they move to the cloud. As a result, they must design security architectures that span on-prem and multiple cloud deployments. In some cases, security solutions designed for one environment may be less effective or entirely unable to function in another. Platform-Specific Solutions: Most cloud providers offer security solutions and configuration settings designed to secure deployments on their cloud platform. However, these solutions and settings vary from one provider to another, increasing the complexity of correctly configuring security settings and implementing consistent security across multiple environments.
Perimeterless Security: Historically, many organizations have adopted a perimeter-focused firewall security strategy designed to protect on-prem IT infrastructure. With cloud environments — and especially multi-cloud deployments — the perimeter has dissolved, making it necessary to design and implement a security strategy not focused on securing a perimeter. New Security Threats: A move to the cloud opens up an organization to new security threats not present in on-prem environments. As the number of cloud environments increases, so does the number of potential attack vectors.
Many organizations struggle with cloud security due to the unfamiliarity of cloud infrastructure and the differences between securing on-prem and cloud-based environments. With multi-cloud deployments, these challenges are amplified, and companies must figure out how to secure environments where legacy security models and technologies may not be effective.
[boxlink link="https://www.catonetworks.com/podcasts/private-cloud-public-cloud-where-do-we-stand-with-the-great-migration-of-services/?utm_medium=blog_top_cta&utm_campaign=convergence_podcast_ep2"] Private Cloud + Public Cloud: Where Do We Stand With the Great Migration of Services? | Podcast Episode [/boxlink]
SASE Enables Effective multi-cloud Security
Much of the complexity of multi-cloud security comes from the fact that a multi-cloud deployment consists of many unique cloud environments. What might work to secure one environment may be ineffective or infeasible in another.
Secure Access Service Edge (SASE) solutions diminish the complexity of securing multi-cloud deployments by securing the network instead. All traffic flowing to, from, and between an organization’s cloud-based and on-prem infrastructure travels over the network. By implementing security inspection and policy enforcement at the network level, SASE can consistently apply security across an organization’s entire IT infrastructure.
In addition to simplifying multi-cloud security, SASE also provides numerous other security benefits, which include:
Global Reach: SASE is deployed within cloud-based points of presence (PoP). Globally distributed PoPs ensure that traffic can be inspected at a geographically close PoP and then routed on to its destination without the backhauling required by on-prem security deployments. Security Integration: SASE solutions implement a full network security stack, including an NGFW, IPS, CASB, ZTNA, and more. By converging multiple security functions into a single solution, SASE achieves greater optimization than standalone solutions. Network Optimization: SASE PoPs also integrate network optimization capabilities such as SD-WAN and a global private backbone. PoPs are also connected by dedicated, high-performance network links to optimize network performance and minimize latency.
Scalable Security: As a cloud-native solution, SASE can also take advantage of the scalability benefits of the cloud. This makes it possible for SASE PoPs to scale to secure higher-bandwidth network traffic without negatively impacting network performance.
Cato provides the world’s most robust single-vendor SASE platform, converging Cato SD-WAN and a cloud-native security service edge, Cato SSE 360, including ZTNA, SWG, CASB/DLP, and FWaaS into a global cloud service. Cato optimizes and secures application access for all users and locations and is easily managed from a single pane of glass. Learn more about how Cato SASE Cloud can help your organization secure its on-prem and multi-cloud infrastructure by signing up for a free demo today.
As organizations grow more reliant on expanding IT infrastructures, cyber threats are also growing more sophisticated. A mature security program is essential to protect the... Read ›
How a Managed Firewall Can Help Close Corporate Security Gaps As organizations grow more reliant on expanding IT infrastructures, cyber threats are also growing more sophisticated. A mature security program is essential to protect the organization against cyber attacks. However, many security teams lack the resources and personnel to keep pace of their expanding duties.
As security teams become overwhelmed, identifying ways to ease their burden is essential to minimizing the security gaps that leave companies vulnerable to attacks.
Most Security Teams are Struggling
Security teams’ responsibilities are rapidly expanding, and many are struggling to keep up. Some of the major challenges that IT and security teams face include:
Expanding IT Infrastructure: Corporate IT infrastructures are expanding and growing more diverse due to numerous drivers. Companies are increasingly adopting cloud infrastructure, remote and hybrid work models, and Internet of Things (IoT) and mobile devices. All of these bring new attack vectors and unique security requirements. Heterogeneous Architectures: The modern IT environment includes various architectures and environments. Each of these must be properly configured, and secured. This can create a diverse security architecture of standalone products that are difficult to effectively monitor, and manage.
Security Alert Overload: This collection of various security solutions also contributes to the alert overload facing modern security teams. The average enterprise security operations center (SOC) sees over 10,000 alerts per day, each of which requires an average of 24-30 minutes to address. With the inability to properly investigate every security alert — or even a reasonable percentage of them — security teams might make decisions that let real threats slip through the gaps, potentially while they waste their efforts on false positives. Vulnerability Management: Software vulnerabilities in production systems are an issue that is quickly spiraling out of control. Over 28,000 new vulnerabilities were discovered in 2021 alone, a 23% growth over the more than 23,000 discovered the previous year. Identifying, testing, and applying patches for vulnerabilities in corporate software and hardware — including the third-party libraries and components used by them — is a significant task, and many patch management programs lag behind, leaving the organization vulnerable.
At the same time, the cybersecurity industry is facing a significant skills gap, which means that companies struggle to attract and retain skilled personnel to fill critical roles. Overwhelmed and understaffed security teams lead to security gaps.
[boxlink link="https://catonetworks.easywebinar.live/registration-the-upside-down-world-of-networking-and-security?utm_medium=blog_top_cta&utm_campaign=upside_down_webinar"] The Upside-Down World of Networking & Security | Webinar [/boxlink]
Firewall Management is a Major Chore
Closing these security gaps requires the ability to reduce security teams’ workloads to a manageable level. One area with significant room for improvement is firewall management.
A network firewall is the cornerstone of an organization’s security architecture; however, it is not an easy tool to manage. Some of the time-consuming duties associated with firewall management include:
Firewall Rule Maintenance: Network firewall rules should be designed to restrict network traffic to only that required for business purposes. With increasingly diverse IT infrastructures, organizations must develop and maintain a range of firewall rules tuned to the needs of different devices and environments. Patch Management: Like other products, firewalls need patches and updates, and, due to their role within an organization’s environment, are common targets of attack. Security personnel should promptly test and apply updates when they become available. Monitoring and Management: Firewalls are not “set it and forget it” systems and require ongoing monitoring and maintenance to be effective. Investigating alerts, validating the effectiveness of firewall rules, and other ongoing activities consume time and resources.
Firewalls can significantly benefit an organization by blocking inbound and WAN-bound attacks before they reach their intended targets. By performing all of these firewall management tasks, security personnel lower corporate cybersecurity risk and achieve clear benefits to the organization.
However, the time spent configuring and managing firewalls could also be spent on other valuable security tasks as well. For example, the time and resources devoted to firewall management may have also been used to identify and remediate an intrusion before it became a data breach or malware infection.
A Managed Firewall Realigns Security Priorities
Security teams have roles and responsibilities that commonly exceed their abilities to carry them out. As corporate infrastructure grows larger and more complex, the growth in security team headcount cannot keep up. As a result, some work may be left undone, and security teams are often forced to perform triage to determine which tasks can be delayed or left incomplete with minimal risk to the organization.
Organizations can resolve this issue by taking steps to alleviate the burden on security personnel. By taking some of the tedious work — such as firewall maintenance— off of their plates, an organization can free up resources and its security team’s time and expertise for tasks where it is more greatly needed.
A managed firewall can enhance security while reducing overload on security personnel. A managed firewall service enables an organization to outsource responsibility for firewall management to a team of third-party experts. This provides companies with firewall rules based on evolving threat intelligence and solutions configured in accordance with industry best practice and regulatory requirements.
A managed Secure Access Service Edge (SASE) deployment takes this a step further, handing over the responsibility for maintenance of the organization’s entire network security stack to a third-party provider instead of just the firewall. Managed SASE also comes with additional benefits, such as improved integration of network and security functionality and optimized routing of WAN traffic over dedicated network links.
Cato provides the world’s most robust single-vendor SASE platform, converging Cato SD-WAN and a complete cloud-native security service edge, Cato SSE 360, including Zero Trust Network Access (ZTNA), Secure Web Gateway (SWG), Cloud Access Security Broker (CASB), Data Loss Prevention (DLP), and Firewall as a Service (FWaaS) into a global cloud service. Cato optimizes and secures application access for all users, locations, and applications, and empowers IT with a simple and easy to manage networking and security architecture. Learn more about optimizing your organization’s security operations by signing up for a free demo today.
Corporate IT networks are rapidly changing. Evolving cloud and technological innovation have spurred digital transformation efforts. The pandemic has normalized remote and hybrid work, causing... Read ›
SASE Enables Consistent Security for the Modern Enterprise Corporate IT networks are rapidly changing. Evolving cloud and technological innovation have spurred digital transformation efforts. The pandemic has normalized remote and hybrid work, causing many employees to work from outside the office and creating the need to securely provide remote access to the workforce.
These changes in corporate IT infrastructure create new security challenges as companies adapt to protect new environments and to combat an evolving cyber threat landscape. In many cases, organizations are finding that their existing security architecture — which was designed to secure an IT infrastructure that is mostly or wholly on-premises — is not up to the task of meeting the security requirements and business needs of the modern, digital enterprise.
The Corporate WAN is Rapidly Changing
In the past, the majority of an organization’s IT assets were located on-prem. The company managed its own data centers, and employees were primarily connected directly to the corporate LAN. Additionally, a company’s IT assets were largely homogenous, consisting of workstations and servers that had similar, well-known security needs.
Within the last several years, the corporate network has undergone significant changes. With the introduction of cloud computing, a growing percentage of an organization’s IT assets are located outside of the traditional network perimeter on infrastructure managed by a third party. Since 89% of companies have multi-cloud deployments, companies must learn to properly operate and manage multiple vendors’ unique solutions.
The growth of remote and hybrid work models in recent years has further transformed the corporate network. In addition to moving employees and their devices off-site, remote work also impacts the range of devices used for business purposes. Mobile devices are increasingly gaining access to corporate data and systems, and bring your own device (BYOD) policies mean that company data may be accessed and stored on devices that the company does not own or fully control.
Finally, the adoption of new technologies to improve corporate productivity and efficiency has an impact. Internet of Things (IoT) devices — including both commercial and consumer systems — are connected to corporate networks. These IoT devices have unique security challenges and introduce significant risk to corporate networks.
As corporate IT environments change, so do their security needs. New environments and devices have unique security risks that must be mitigated. The solutions designed for on-prem, primarily desktop environments, may not effectively protect new infrastructure if they can be used by them at all.
[boxlink link="https://catonetworks.easywebinar.live/registration-whats-the-difference-between-sse-360-and-sase?utm_medium=blog_top_cta&utm_campaign=AMA_sse_webinar"] Ask Me Anything: What’s the Difference Between SSE and SASE? | Watch Now [/boxlink]
Legacy Solutions Do not Fit Modern Security Needs
Many organizations have existing security architectures that are designed for a particular IT architecture. As this architecture evolves, these security solutions are often ill-suited to securing an organization’s new deployment environments and devices for various reasons, including:
Location-Specific Protection: Often, corporate security architectures are designed to define and secure the perimeter of the corporate network against inbound threats and outbound data exfiltration. However, the growth of cloud computing, remote work, and the IoT means that this perimeter is rapidly expanding to the point where it is infeasible and pointless to secure since it includes the entire Internet.Limited Scalability: Appliance-based security solutions, such as network firewalls, are limited by their hardware. A computer only has so much memory and CPU, and a network interface card has a maximum throughput. Cloud scalability and the growth of corporate networks can result in security appliances being overwhelmed with more traffic than they can handle.Computational Requirements: Many endpoint security solutions require a certain amount of processing power or memory on the device to function. As resource-constrained devices such as mobile and IoT devices become more common, these solutions may not be usable in all areas of an organization’s IT infrastructure.Environment-Specific Requirements: As corporate IT environments grow more complex and diverse, different environments may have specific security considerations. For example, appliance-based network firewalls and security solutions are not a feasible option in cloud deployments since the organization lacks control over its underlying IT infrastructure.
Attempting to adapt an organization’s existing security architecture to secure its evolving environment can create disjointed security policies that are inconsistently enforced across the corporate WAN. For example, cloud-based infrastructure can be protected by cloud-focused security solutions that differ from those protecting on-prem infrastructure, which increases the complexity and overhead of security management. Remote workers and mobile devices may suffer network performance issues as traffic is backhauled for security inspection before being routed on to its destination.
The legacy security solutions that comprise traditional perimeter-focused security architectures are designed for networks that are rapidly becoming extinct. Often, these solutions adapt poorly to securing the modern, distributed corporate WAN.
Designing Security for the Modern Enterprise
As corporate networks become more distributed, security must follow suit. Effectively protecting the modern corporate WAN requires security solutions that can provide consistent protection and security policy enforcement throughout the corporate network.
Secure Access Service Edge (SASE) is designed for the distributed enterprise and addresses the common shortcomings of legacy security solutions. SASE is implemented using a network of cloud-based points of presence (PoPs) that can be deployed geographically near an organization’s scattered IT assets and can take advantage of cloud scalability to meet evolving business needs. SASE solutions also incorporate a full security stack — including solutions designed for cloud infrastructure and remote users — enabling traffic to be inspected by any PoP before being optimally routed to its destination.
Cato provides the world’s most robust single-vendor SASE platform, converging Cato SD-WAN and a cloud-native security service edge, Cato SSE 360, including ZTNA, SWG, CASB/DLP, and FWaaS into a global cloud service. With over 75 PoPs worldwide, Cato optimizes and secures application access for all users and locations, and is easily managed from a single pane of glass. To learn more about Cato SASE Cloud and how it can help your organization’s security architecture keep up with the evolution of your network infrastructure, sign up for a demo today.
A growing percentage of Internet traffic is protected by encryption. While estimates vary, most agree that at least 80% of Internet traffic uses SSL/TLS to... Read ›
Traditional Firewalls Can’t Keep Up with the Growth of Encrypted Traffic A growing percentage of Internet traffic is protected by encryption. While estimates vary, most agree that at least 80% of Internet traffic uses SSL/TLS to ensure confidentiality, integrity, and authenticity of the data being transmitted. According to Google, approximately 95% of web browsing uses the encrypted HTTPS protocol.
This trend toward traffic encryption has been driven by a few different factors. As users become more educated about the differences between unencrypted HTTP and encrypted HTTPS and the threat of various attacks, they are opting for the more secure option wherever possible. Web browser vendors like Google are encouraging this trend by defaulting to the encrypted version of sites and labeling sites that only support HTTP as unsafe and reducing their SEO scores.
The move toward data encryption is a mixed blessing for cybersecurity. On one hand, the widespread use of SSL/TLS can help protect against phishing attacks or the exposure of user credentials and other sensitive data to someone eavesdropping on corporate network traffic. On the other hand, the same encryption that protects against eavesdroppers can also limit the effectiveness of an organization’s cybersecurity tools. Identification of malware and other malicious content with network traffic requires the ability to inspect the contents of packets traveling over the network. If this traffic is encrypted and network security solutions do not have the encryption key, then their threat prevention and detection capabilities are limited.
Network security solutions can overcome these challenges, but it comes at a cost. As the volume of network traffic increases and a growing percentage is encrypted, traditional network firewalls are falling behind, creating unnecessary tradeoffs between network performance and security.
Encrypted Traffic Inspection is a Bottleneck
Some organizations address the challenges that traffic encryption poses to security by performing TLS inspection. Security solutions that have access to the encryption keys used to protect network traffic can decrypt that traffic and inspect it for malicious content or data exfiltration before allowing it to continue on to its destination.
SSL inspection provides the ability to perform the deep packet inspection that security solutions need to do their jobs. However, decryption is a computationally expensive and time-consuming process. With growing volumes of encrypted traffic, decryption functionality within security solutions can create a significant bottleneck and degrade network performance. These issues are exacerbated by the fact that multiple solutions within an organization’s security architecture may need insight into the contents of network packets to fulfill their role. For example, firewalls, intrusion prevention systems (IPSs), secure web gateways (SWGs), and other security solutions may decide whether to allow or block traffic based on its contents.
[boxlink link="https://catonetworks.easywebinar.live/registration-the-upside-down-world-of-networking-and-security?utm_medium=blog_top_cta&utm_campaign=upside_down_webinar"] The Upside-Down World of Networking & Security | Webinar [/boxlink]
Decrypting TLS traffic can exhaust these security tools’ compute capacity, creating a bottleneck. If an organization has deployed multiple solutions that independently perform TLS decryption and deep packet inspection, then the effects of decryption on network performance are cumulative.
TLS inspection is essential to identifying and blocking threats before they enter an organization’s network and to stopping data exfiltration before it becomes a breach. However, the costs of doing so can be high, creating a tradeoff between network performance and security.
SASE Enables Scalable Enterprise Security
TLS inspection is a vital capability for many security solutions because it enables deep packet inspection and detection of malicious content within network traffic. One of the primary barriers to implementing TLS inspection at scale is that security solutions’ resources are exhausted, which can create significant latency as each tool in an organization’s security architecture individually decrypts and inspects network traffic.
Secure Access Service Edge (SASE) provides the ability to perform TLS inspection while minimizing the impacts on network performance and latency. Three core capabilities that make this possible include:
#1. Solution Convergence: SASE solutions converge a full network security stack into a single solution. This makes it possible to decrypt traffic once and provide all security solutions with access to the decrypted data for inspection without jeopardizing security. By eliminating the individual traffic decryption by each device, SASE dramatically decreases the impact of TLS inspection on network performance.
#2. Cloud-Native Design: SASE points of presence (PoPs) are built with cloud-native software. By deploying security functionality in the cloud, SASE can take advantage of cloud scalability, eliminating the bottlenecks created by computationally expensive decryption operations.
#3. Cost Saving: By offloading all the TLS inspection work to an elastic cloud-native SASE service, enterprises don't need to worry about upgrading on-premises appliances prematurely. This saves the organization both the procurement and the integration costs of the new appliances.
TLS inspection is vital to companies’ ability to protect themselves against evolving cyber threats. As the volume of encrypted traffic grows, traditional firewalls can’t keep up, creating tradeoffs between network performance and security. SASE is vital to the future of enterprise security because it enables strong corporate network security without compromising performance.
Cato provides the world’s most robust single-vendor SASE platform, converging Cato SD-WAN and a cloud-native security service edge, Cato SSE 360, including ZTNA, SWG, CASB/DLP, and FWaaS into a global cloud service. With over 75 PoPs worldwide, Cato optimizes and secures application access for all users and locations, and is easily managed from a single pane of glass. Learn more about improving your network visibility, performance, and security with Cato SASE Cloud by signing up for a demo today.
Today, nearly all companies have some form of cloud infrastructure, and 89% are operating multi-cloud deployments. In general, this trend seems to be continuing with... Read ›
Network Firewalls Are Still Vital in the Era of the Cloud Today, nearly all companies have some form of cloud infrastructure, and 89% are operating multi-cloud deployments. In general, this trend seems to be continuing with many companies planning to move additional assets to the cloud.
With the adoption of cloud infrastructure, organizations must reexamine their existing security infrastructures. Some security solutions are ill-suited to securing cloud environments, and the cloud introduces new security risks and challenges that must be managed as well. However, network firewalls are still a relevant and vital security solution in the era of the cloud.
Cloud Security Can Be Complex
Companies are moving to the cloud due to the various benefits that it provides. Cloud deployments increase the scalability and flexibility of IT infrastructure and are also better suited to supporting a distributed enterprise comprised of on-site and remote workers. Additionally, the cloud supports new methods of application development, such as a transition to serverless applications.
Another major selling point of the cloud is that customers can outsource responsibility for some of their infrastructure stacks to the service provider. Up to a certain layer, the service provider is wholly responsible for configuring, maintaining, and securing the leased infrastructure. However, this does not translate to a total handover of security responsibility. Under the cloud shared responsibility model, the cloud customer is responsible for managing and securing the portion of the infrastructure stack that they access and control.
Cloud deployments differ significantly from traditional, on-prem data centers. Many organizations struggle to effectively adapt their security models and architectures to support their new cloud environments, leading to widespread security misconfigurations and frequent cloud data breaches.
The interconnection between on-prem and cloud environments and between applications within cloud deployments makes network security vital to cloud security. Network firewalls are a crucial part of this, inspecting traffic flowing between different areas and limiting the risk of threats entering the corporate network or spreading within it.
[boxlink link="https://www.catonetworks.com/resources/why-remote-access-should-be-a-collaboration-between-network-security/?utm_medium=blog_top_cta&utm_campaign=network-and-security-wp"] Why remote access should be a collaboration between network & security | White Paper [/boxlink]
What to Look for in a Network Firewall
Many organizations already have network firewalls in place; however, a network firewall designed to secure the perimeter of the corporate LAN is ill-suited to protecting a distributed enterprise WAN. As companies move to the cloud, there are a number of core capabilities a network firewall should include:
Location Agnostic
Companies are growing increasingly distributed. In addition to traditional on-prem data centers, organizations are moving data storage and applications to cloud-based infrastructure, often as part of multi-cloud deployments. At the same time, employees are moving outside of the traditional network perimeter with the growth of remote and hybrid work, and the use of mobile devices for business.
As a result, network firewalls need to be able to provide protection wherever a device is located. Backhauling traffic to the corporate network for security inspection doesn’t work because it hurts network performance and increases load on on-prem IT infrastructure. Network firewalls must be as distributed as the rest of an organization’s IT assets.
Performance
Companies are increasingly dependent on Software as a Service (SaaS) applications to provide critical functionality to both on-prem and remote employees. Often, these SaaS applications are latency-sensitive, and poor network performance has a significant impact on corporate productivit
Network firewalls must offer strong performance to avoid creating tradeoffs between network performance and security. If network firewalls create latency due to inefficient routing or an inability to inspect traffic at line speed, they are more likely to be bypassed or otherwise undermined.
Scalability
Corporate IT infrastructures are rapidly expanding as companies adopt cloud infrastructure, Internet of Things (IoT) devices, and mobile devices. As a result of this digital transformation, there are more devices, more applications, and more data flowing over corporate networks.
Network firewalls are responsible for inspecting and securing this network traffic, so they must scale with the network. As IT infrastructure takes advantage of the power of cloud scalability and IoT devices proliferate, network firewalls also need the scalability that the cloud provides.
Solution Integration
Since corporate security architectures are growing increasingly complex, the variety of environments and endpoints that security analysts must secure can result in an array of standalone security solutions. This security sprawl is exacerbated by the evolution of the cyber threat landscape and the need to deploy defenses against new and emerging threats.
These complex and disconnected security architectures overwhelm security personnel and degrade a security team’s ability to rapidly identify and respond to threats. Standalone solutions require individual configuration and management, force context switching between dashboards when investigating an incident, and make security automation difficult or impossible.
A network firewall is the foundation of a corporate security architecture. To enforce consistent security policies and controls across all of an organization’s IT assets — including on-prem, cloud-based, and remote systems — companies need a network firewall that can operate effectively in all of these environments. Additionally, this firewall should be integrated with the rest of an organization’s security architecture to support rapid threat detection and response and enable security automation.
Simplifying Network Security with SASE
The transition to cloud-based infrastructure makes reconsidering and redesigning corporate security architecture critical. Cloud environments are more distributed and more exposed to potential threat actors than on-prem environments, and perimeter-based security models that worked in the past no longer apply when the perimeter is rapidly dissolving. While companies could attempt to build and integrate their own security architectures using various standalone solutions, a better approach is to adopt security designed for the modern corporate network.
Secure Access Service Edge (SASE) implements security with a network of cloud-based points of presence (PoPs) that meet all of the needs of the modern network firewall:
Location Agnostic: SASE PoPs are deployed as virtual appliances in the cloud. This allows them to be deployed anywhere, making them geographically convenient to devices located on-prem, remote, or in the cloud.Performance: Each SASE PoP converges a full security stack, so security inspection and policy enforcement can happen at once and anywhere. This eliminates the need to backhaul traffic for scanning.Scalability: SASE PoPs host cloud-native software that can leverage the scalability benefits of cloud infrastructure. A SASE Cloud can elastically scale vertically with more compute and throughput in a certain PoP, and horizontally with more PoPs in new geographical locations.Solution Convergence: SASE PoPs converge a range of network and security functions, including a next-generation firewall, intrusion prevention system (IPS), zero-trust network access (ZTNA), SD-WAN, and more. A solution built to converge these functions into a single platform can optimize and streamline their interactions to a degree that is impossible with standalone solutions.
Cato provides the world’s most robust single-vendor SASE platform, converging Cato SD-WAN and a cloud-native security service edge, Cato SSE 360, including ZTNA, SWG, CASB/DLP, and FWaaS into a global cloud service. With over 75 PoPs worldwide, Cato optimizes and secures application access for all users and locations, and is easily managed from a single pane of glass. Learn more about how Cato SASE Cloud can improve your organization’s cloud security by signing up for a demo today.
The modern business looks very different from that of even a few years ago. IT technologies have changed rapidly, and corporate networks are quickly becoming... Read ›
Why Traditional NGFWs Fail to Meet Today’s Business Needs The modern business looks very different from that of even a few years ago. IT technologies have changed rapidly, and corporate networks are quickly becoming more distributed and complex. While this brings business benefits, it also creates significant challenges.
One of the biggest hurdles that companies face is ensuring that the evolution of their IT infrastructure does not outpace that of their security infrastructure. Many companies have spent significant time and resources designing and implementing security architectures around traditional next-generation firewalls (NGFWs) and other security solutions. Attempting to make evolving IT infrastructure work with these existing security deployments is a losing battle, as these solutions were designed for networks that are rapidly becoming a thing of the past.
The Modern Enterprise is Expanding
In recent years, enterprise IT infrastructures have evolved, driven by the pandemic, shifting business needs, and the introduction of new IT and security technologies. Some of the most significant recent changes in corporate IT infrastructure include:
Cloud Adoption
Nearly all companies have cloud-based infrastructure, and 89% have a multi-cloud deployment. This expansion into the cloud moves critical data and applications off-site and contributes to an increasingly distributed enterprise. Corporate WANs must be capable of efficiently and securely routing traffic between an organization’s various network segments.
Remote Work
The pandemic accelerated a transition to remote and hybrid work policies. With employees able to work from anywhere, corporate IT infrastructure must adapt to support them. Between remote work and the cloud, a growing percentage of corporate network traffic has no reason to pass through the headquarters network and its perimeter-based security solutions.
Branch Locations
In addition to the growth in remote work, companies may also be expanding to new branch locations. Like remote workers, the employees at these sites need high-performance connectivity to corporate resources hosted both in on-prem data centers and in the cloud.
Mobile Device Usage
With the growth of remote work has also come greater usage of mobile devices — both corporate and personally owned — for business purposes. Devices that may not be owned or controlled by the company may have access to sensitive corporate data or IT resources, making access management and traffic inspection critical for corporate security.
Internet of Things (IoT) Devices
IoT devices have the potential to increase an organization’s operational efficiency and ability to make data-driven decisions. However, these devices also have notoriously poor security, posing a significant threat to the security of corporate networks where they are deployed. Corporate IT architectures must be capable of limiting the risk posed by these devices, regardless of where they are deployed within the corporate WAN.
With the evolution of corporate networks, traditional LAN-focused security models are no longer effective. While protecting the corporate LAN is important, a growing percentage of an organization’s employees and devices are located outside of the traditional network perimeter. Defending cloud-based assets and remote workers with perimeter-based defenses is inefficient and hurts network performance and corporate productivity. As enterprise networks expand and grow more distributed, security architectures must be designed to protect the corporate WAN wherever it is.
Appliance-Based NGFWs Have Significant Limitations
Traditionally, most organizations have implemented perimeter-based defenses using appliance-based security solutions. If most or all of an organization’s IT infrastructure and employees are located on-site, then appliance-based security solutions can effectively meet the needs of the enterprise.
However, this description no longer fits most companies’ IT environments, making the traditional perimeter-focused and appliance-based security model a poor fit for organizations’ security needs. Some of the main limitations of appliance-based security solutions such as next-generation firewalls (NGFWs) include:
Coverage Limitations
NGFWs are designed to secure a protected network by inspecting and filtering traffic entering and leaving that network. To do so, they need to be deployed in line with all secured traffic flowing through them. This limits their effectiveness at securing the distributed enterprise as they must either be deployed at protected networks — which is increasingly unscalable with the growth of cloud deployments, remote work, and branch locations — or have all traffic rerouted to flow through them, which increases latency and harms network performance.
[boxlink link="https://catonetworks.easywebinar.live/registration-the-upside-down-world-of-networking-and-security?utm_medium=blog_top_cta&utm_campaign=upside_down_webinar"] The Upside-Down World of Networking & Security | Webinar [/boxlink]
Limited Scalability
An appliance-based NGFW is limited by its hardware and has a maximum volume and rate of traffic that it can inspect and secure. As companies increasingly adopt cloud-based infrastructure, this creates challenges as cloud resources can rapidly scale to meet increased demand. Scaling an appliance-based security solution may require acquiring and deploying additional hardware, an expensive and time-consuming process that limits corporate agility.
Complex Management and Maintenance
To be effective, security solutions such as NGFWs must be tuned to address the security concerns of their deployment environments. As companies expand to include cloud-based infrastructure, remote work, and branch locations, they may need to protect a wide range of environments. The resulting array of security solutions and custom configurations makes security management complex and unscalable.
Traditional NGFWs were designed for corporate IT environments where an organization’s assets could be protected behind a defined perimeter and used infrastructure under the organization’s control. As corporate networks evolve and these assumptions become invalid, traditional NGFWs and similar perimeter-focused and appliance-based security solutions no longer meet the needs of the modern enterprise.
Redesigning the NGFW for the Modern Business
Businesses’ digital transformation initiatives and efforts to remain competitive in a changing marketplace have driven them to adopt new technologies. Increasingly, corporate assets are hosted in the cloud, and IT architectures are distributed.
Attempting to use traditional security solutions to secure the modern enterprise forces companies to make tradeoffs between network performance and security. As IT architecture moves to the cloud and becomes distributed, NGFWs and other corporate cybersecurity solutions should follow suit.
The evolution of the corporate network has driven the development of Secure Access Service Edge (SASE) solutions, which overcome the traditional limitations of NGFWs and integrate other key network and security functions. These cloud-based solutions provide various benefits to the organization, including:
Global Reach: SASE cloud-native software is deployed in points of presence (PoPs) all over the world. This enables delivery of NGFW capabilities anywhere, minimizing the distance between on-prem, cloud-based, and remote devices and the nearest PoP.
Improved Visibility: With SASE, all traffic traveling over the corporate WAN passes through at least one SASE PoP. This enables security inspection and policy enforcement and provides comprehensive visibility into corporate network traffic.
Simplified Management: All SASE features are managed through a single pane of glass. This simplifies security monitoring and management, and enables unified and consistent enforcement.
Security Integration: SASE PoPs consolidate numerous security and network capabilities into one coherent service, enabling greater optimization than standalone solutions.
Scalable Security: SASE PoPs run cloud-native software. Scaling up to meet increasing demand happens elastically, without downtime, and without customer involvement. Enterprises no longer need to worry about mid-term hardware failure or refresh.
Performance Optimization: Delivering security next to the user and the application instead of carrying user and application traffic into a central security stack reduces network latency, and improves user experience and productivity.
Cato Networks built the world’s first cloud-native, single-vendor SASE. The Cato SASE Cloud Is available from a private cloud of 75+ PoPs connected by dedicated, SLA-backed private global backbone. See the capabilities of Cato SASE Cloud for yourself by signing up for a free demo today.
Our list of experts encompasses professionals and leaders who, together, deliver an overarching understanding of the Cybersecurity industry and the evolving nature of security threats.... Read ›
15 Cybersecurity Experts To Follow on LinkedIn Our list of experts encompasses professionals and leaders who, together, deliver an overarching understanding of the Cybersecurity industry and the evolving nature of security threats. By following them, you can gain deep insights into cybersecurity’s latest developments and trends, deepen your understanding of the hacker mindset and get a glimpse into future predictions. As global cybersecurity leaders who’ve seen the dark side, they have an interesting and unique perspectives that can provide value to anyone working or interested in cybersecurity. Read on to see who the top 15 cybersecurity experts are that we recommend following on Linkedin.
1. Brian Krebs
https://www.linkedin.com/in/bkrebs/
@briankrebs
Brian is an investigative reporter and journalist who focuses his work on cybercrime and cybersecurity. He is the author of a daily blog that is hosted on his website KrebsOnSecurity.com. For 14 years, (2005 to 2019), Brian reported for The Washington Post. He also authored more than 1000 blog posts for the Security Fix blog.
The KrebsOnSecurity blog covers a wide variety of topics, from data breaches to security updates to human stories of cyber scams. They are all reported in an informative, yet personalized, manner; almost as if you were listening to a friend tell you a story. The busy comment section adds an inviting and interactive feeling.
2. Andy Greenberg
https://www.linkedin.com/in/andygreenbergjournalist/
@a_greenberg
Andy Greenberg is a cybersecurity writer for the online media outlet, WIRED, and an author. Andy’s stories cover cybersecurity, privacy, hackers and information freedom. Some of his recent articles cover the war in Ukraine, how data and organizations are hacked to seize political control and recent cyber attacks. Andy has written two books. The first, Sandworm: A New Era of Cyberwar and the Hunt for the Kremlin's Most Dangerous Hackers, was published in 2019. The second, Tracers in the Dark: The Global Hunt for the Crime Lords of Cryptocurrency, will be released in November 2022.
3. Mikko Hypponen
https://www.linkedin.com/in/hypponen/
@mikko
The known security term "if it’s smart, it’s vulnerable” was coined by this security expert and influencer - Mikko Hypponen. Mikko is the Chief Research Officer at WithSecure and the Principal Research Advisor at F-Secure, as well as a researcher, keynote speaker, columnist and author. Mikko’s work covers global security trends and vulnerabilities, privacy and data breaches. Follow him to uncover data-driven analyses of what’s going on in privacy and security, accompanied by his take into what the future of cybersecurity holds.
4. Graham Cluley
https://www.linkedin.com/in/grahamcluley
@gcluley
Graham is a researcher, blogger, public speaker and podcaster. He talks about computer security threats and works with law enforcement agencies on hacker and cyber gang investigations. Graham’s daily blog, grahamcluley.com, focuses mainly on cyber attacks and scams. Reports are bite-sized and include concise explanations coupled with tips for readers. Graham also hosts the Smashing Security podcast, together with Carole Theriault.
[boxlink link="https://www.catonetworks.com/cybersecurity-masterclass/?utm_medium=top_cta&utm_campaign=masterclass_lobbypage"] Cybersecurity Master Class | Check it out [/boxlink]
5. Daniel Miessler
https://www.linkedin.com/in/danielmiessler/
@DanielMiessler
Head of Vulnerability Management and AppSec at Robinhood by day, security writer by night, Daniel creates and delivers security-related content on a regular basis via his website, danielmiessler.com. There, you can find blogs, tutorials and podcasts on information security, often combined with his philosophical and political views. The result is a wealth of candid information, depicting a refreshing and humanistic view of information security.
6. Ido Cohen (Darkfeed)
@ido_cohen2
If you’re looking to stay up-to-date on all things ransomware, Ido’s Twitter page is one to follow. Through quick and concise updates, Ido provides all the necessary information about recent attacks, ransomware gangs, ransomware strains and threats. While you might not get in-depth analyses or intense research reports from Ido, you will stay in the know about news, so you can pick and choose what to dig deeper into on your own time.
7. Etay Maor
https://www.linkedin.com/in/etaymaor/
An industry-recognized cybersecurity speaker and a Business Insider “IBM Rockstar Employee”, we’re proud to call Etay one of our own, as Senior Director of Security Strategy at Cato Networks. Etay is an adjunct professor at Boston College, and is part of the Call for Paper (CFP) committees for the RSA Conference and QuBits Conference. In addition to following him on LinkedIn, Etay has a dedicated Cybersecurity Masterclass series, designed to teach professionals of all levels the best practices they need to protect their enterprise. Watch his Masterclass series on everything from identifying and mitigating deepfake threats, setting up threat hunting and threat intelligence programs, and more.
8. Kevin Mitnick
https://www.linkedin.com/in/kevinmitnick/
@kevinmitnick
Convicted-hacker turned security consultant, Kevin is a valuable source of cybersecurity information, especially when it comes to social engineering and system penetration. Kevin now runs a security firm, speaks in the media at cybersecurity events and has authored a number of popular books. Follow him and his blog to (start to) understand the mindset of hackers.
9. Chuck Brooks
https://www.linkedin.com/in/chuckbrooks/
@ChuckDBrooks
Chuck is a thought leader, speaker and writer for cybersecurity who boasts multiple accolades, like “Top Person To Follow on Tech by Linkedin” and “received Presidential Appointments for Executive Service by two US Presidents”. By following him on Linkedin you will be exposed to his articles and speaking occasions, as well as his commentary on current affairs.
10. Dan Lohrmann
https://www.linkedin.com/in/danlohrmann/
@govcso
Dan is a renowned cybersecurity speaker, author and blogger, as well as an advisor for government organizations. His blog covers technological trends and global changes from a bird's eye view, while his social channel provides a newsfeed which outlines recent attacks and events from a governmental and geo-political security perspective. Together, they provide a broad overview of cybersecurity needs for the public sector.
11. Magda Chelly
https://www.linkedin.com/in/m49d4ch3lly/
@m49D4ch3lly
Dr. Magda Lilia Chelly is a cybersecurity leader, influencer and author who appears regularly in the media. She has authored three books and regularly leverages her public stance to promote social issues, like gender equality in the workplace or WLB. By following her, you’ll devour a broad range of cybersecurity topics, from remote work requirements to risk management to cybersecurity trends. Most of her thoughts and content are strategic, and can help any leader looking to design or improve their organizational security.
12. Rinki Sethi
https://www.linkedin.com/in/rinkisethi/
@rinkisethi
Rinki is the CISO at bills.com and was formerly the CISO at Twitter and the Information Security VP at IBM and Palo Alto Networks. As a security leader, she not only builds and manages cybersecurity strategies, but she also shares her thoughts and knowledge. By following her social channels, you will get access to her curated list of cybersecurity resources as well as a peek into the professional and personal life of a CISO.
13. Tyler Cohen Wood
https://www.linkedin.com/in/tylercohen78/
@TylerCohenWood
A recognized top cybersecurity influencer, Tyler is a co-founder of a cybersecurity product and a Talk Show host at My Connected Life, which discusses digital health. She is also an author, a writer and a public speaker. Tyler’s work focuses mainly on how to mitigate cyber threats in a digital world, from a unique perspective that combines both personal opinion and business requirements.
14. Bill Brenner
https://www.linkedin.com/in/billbrenner/
@BillBrenner70
Bill is an infosec expert who researches, writes and builds communities. He’s also a VP at CyberRisk Alliance. On his social channels he shares the latest updates about vulnerabilities and security controls. What’s unique about him is that he has a down-to-earth approach to cybersecurity, by understanding that security’s job is not to scare, but to provide practical and feasible assistance to CISOs.
15. Richard Bejtlich
https://www.linkedin.com/in/richardbejtlich/
@taosecurity
As a security strategist, former computer incident response team lead and martial arts student, Richard definitely knows about defense. In the past, he published a number of books as well as a blog. Today, we recommend following him on Twitter, where he shares his personal (and sometimes tongue-in-cheek commentary) on security-related current affairs.
Who Else Should We Follow?
Working in cybersecurity often feels like playing a never ending game of Whack-A-Mole. Cybersecurity experts, like those listed above, can help security experts shorten the path to determining what they should focus on strategically, which issues they should pay attention to and how to allocate their resources.Are there any other experts who help you prioritize what to work on? Share with us on Linkedin.
SD-WAN, SASE, & SSE are becoming mainstream, but confusion hasn’t left the building. Yet. What survey are you talking about? Twice a year, Cato Networks... Read ›
Cato 2022 Mid-Year Survey Result Summary SD-WAN, SASE, & SSE are becoming mainstream, but confusion hasn’t left the building. Yet.
What survey are you talking about?
Twice a year, Cato Networks runs a global survey that collects and analyzes the state of enterprise networking and security. Our last survey has broken all records with 3129 respondents from across the globe. More accurately, 37% from America, 33% from Europe, middle east and Africa, and 30% from Asia and Australia.
52% of them were channel partners (not necessarily ours, yet), and 48% were end customers. All of them, collectively, work with network and network security on a daily basis and know a thing or two about highest priority challenges faced by the modern enterprise.
Respondent demographics also indicate that we are looking at a versatile and reliable dataset. In terms of enterprise sizes, 27% of respondents have more than 100 sites to manage, 22% have between 25 to 100, and 51% have up to 25 sites. 44% of them operate a global organization compared to 56% who are regional or national.
When asked about their position and responsibilities, 62% confirmed they hold an IT management or leadership position. 27% with specific focus on network and 17% with specific focus on security.
We believe it’s fair to say the results we’re going to share here are as objective as possible.
The Market is Aware of SASE and SSE, But Aren’t Clear on the Differences
The market is showing awareness and understanding of both SASE (est. 2019) and Security Service Edge (SSE) (est. 2021.) However, the rise of “too many acronyms” is leading to market confusion, specifically related to architecture, value propositions and differentiation.
When we asked, “How well do you believe you understand the SASE architecture and its benefits?”, 45% responded that they feel they understand both very well. It would look very positive if we stopped here, but at the same time, 20% felt vague regarding the architecture, 12% felt vague about the value, and 23% felt vague about both. Oh no.
The confusion continued even further when we asked if they know what’s the difference between SASE and SSE. It wasn’t a test, but only 47% passed. Very close to the 45% who felt confident on SASE’s architecture and value.
Going about it from another angle, we asked “Do you consider SSE as an interim step to SASE?”. 29% answered they do, and 38% answer they don’t. The red flag is the 33% who answered that they aren’t sure what the difference is between SSE and SASE.
[boxlink link="https://www.catonetworks.com/resources/cato-sse-360-finally-sse-with-total-visibility-and-control/?utm_source=blog&utm_medium=top_cta&utm_campaign=cato_sse_360"] Cato SSE 360: Finally, SSE with Total Visibility and Control | Whitepaper [/boxlink]
Choose Wisely: Will it Be One or Multi-Vendor SASE?
In answer to our question “What is your SASE migration timeline?”, 17% responded it already stared in 2020 or 2021, 18% responded that it is happening this (2022) year, and 44% said that it’s targeted for 2023.
Similarly, 54% reported they already have C-level sponsorship for their SASE project from either their CEO (12.5%), CIO (24%), CFO (5%) or CISO (12.5%).
But with so much focus on SASE and confusion surrounding SSE, what’s most important to pay attention to?
36% of respondents who already have SD-WAN in their networks indicated that they plan to replace it. 29% plan to deploy SSE as an interim step towards full SASE deployment, and 38% told us they are going all in on SASE.
On top of those findings, 40% indicated that a single-vendor SASE is very important in their vendor selection, and 25% ranked this as extremely important. This correlates very well with 77% who indicated a single management for all network and security infrastructure is very or extremely important.
So, what’s the gist here?
The bottom line here is simple. SASE is the end-game and the SASE revolution is currently well underway.
Every IT leader and team should both strategize and prioritize their path to SASE. It can be a gradual multi-project approach or undertaken as a single project. It can rely on an existing network and security stack or a refresh of legacy products.
Crowd wisdom also shows that so many people who work daily with SD-WAN, SASE and SSE value the importance of single-vendor and single management solutions, and so should you.
So, when your C-level sponsor asks you about your SASE migration strategy, make sure you are aligned with the voice of the industry, that you have a plan, and that you know how to choose the right vendor for your enterprise.
And what about the confusion between SASE and SSE? What about those who don’t feel they know enough about one or both acronyms? It’s a perfectly normal place to be in, and a challenge anyone can easily overcome in just a few short hours.
Cato Networks offers free SASE and SSE education courses to get you up to speed and on par with industry standards. Check out our free SASE and SSE certification courses, to expand your knowledge base, and learn about these new and evolving categories.
Now how ‘bout that?
In 2021, Gartner introduced a new security category – SSE (Security Service Edge). In this blog post, we’ll explain what SSE is, how SSE is... Read ›
SSE (Security Service Edge): The Complete Guide to Getting Started In 2021, Gartner introduced a new security category - SSE (Security Service Edge). In this blog post, we’ll explain what SSE is, how SSE is different from SASE and compare traditional SSE solutions to Cato SSE 360. This blog post is an excerpt from our new Cato SSE 360 whitepaper, but if you’re interested in learning more information, we highly recommend you read the complete whitepaper.
What is SSE?
Before we explain SSE, let’s start by giving more context. In 2019, Gartner introduced the new SASE market category. SASE (Secure Access Service Edge) is the convergence of SD-WAN and network security as a cloud-native, globally-delivered service. As a result, SASE solutions can provide work from anywhere (WFA users) with optimized and secure access to any application. From the security side, SASE includes SWG, CASB/DLP, FWaaS and ZTNA.
Then, in 2021, Gartner introduced another related market category called SSE (Security Service Edge). SSE offers a more limited scope of converged network security than SASE. SSE converges SWG, CASB/DLP and ZTNA security point solutions, into a single, cloud-native service. Therefore, SSE provides secure access to internet and SaaS applications, but does not address the network connectivity and east-west WAN security aspects of that access, which remains as a separate technology stack.
[boxlink link="https://www.catonetworks.com/resources/cato-sse-360-finally-sse-with-total-visibility-and-control/?utm_source=blog&utm_medium=top_cta&utm_campaign=cato_sse_360"] Cato SSE 360: Finally, SSE with Total Visibility and Control | Whitepaper [/boxlink]
SSE vs. SASE
To sum up the comparison:
SASE Traditional SSE Services Year Introduced 2019 2021 Technological Pillars Converged Networking and Network Security Limited convergence of network security only Key Components SD-WAN, SWG, CASB/DLP, FWaaS, ZTNA, RBI, Unified Management SWG, CASB/DLP and ZTNABusiness Value Resiliency, security, optimization, visibility and control Limited network security (secure access to SaaS and web traffic)
Why Do Businesses Need SSE? (Traditional SSE Capabilities and Benefits)
Optimized and secure global access to internet and SaaS applications and data is essential for businesses’ technical requirements and the evolving threat landscape. But rigid security architectures and disjointed point solutions lower business agility and increase risk. This is where SSE shines.
SSE provides:
Consistent security policy enforcement - full inspection of traffic between any two edges while enforcing threat prevention and data protection policies
Reduced attack surface with Zero Trust Network Access (ZTNA) - ensuring users can only access authorized applications
Elastic, high performance security inspection - securing traffic at scale through a global backbone of scalable Points of Presence (PoPs)
Improved security posture - monitoring the threat landscape and deploying mitigations to emerging threats through the SSE provider’s SOC (instead of the IT staff)
Reduced enterprise IT workload without customer involvement - continuously updating the cloud service with new enhancements and fixes, while reducing workload
As a result of these benefits, SSE offers businesses secure public cloud and web access, threat detection and prevention capabilities, secure and optimized remote access and sensitive Data Loss Prevention.
How to Get Started with SSE
Today, many businesses are still using legacy architectures. This impedes digital transformation because:
Legacy networks are built around physical corporate locations - a digital architecture requires re-architecture of the network
Centralized (backhauling) security models slow down secure cloud access - direct secure Internet should be available at any location for any user
Legacy security solutions can’t scale - they can’t support a hybrid workforce working from anywhere
Disjointed solutions are fragmented and complex to manage - this requires more work from IT and increases the likelihood of manual configuration errors
To get started with SSE, businesses should choose an SSE vendor that can help them overcome these challenges. Such a vendor will provide total visibility and control across all edges and all traffic, support a global footprint with high performance security, converge management and analytics with a single pane of glass, ensure a future proof and resilient SSE service.
Introducing Cato SSE 360: Going Beyond Gartner’s SSE
Cato SSE 360 goes beyond Gartner’s scope of SSE, to provide total visibility, optimization and control for all traffic, users, devices, and applications everywhere. Not only does it provide secure and optimized access to the internet and public cloud applications, but also to WAN resources and cloud datacenters, reducing your attack surface and eliminating the need for additional point solutions like firewalls, WAN optimizers and global backbones. And, Cato SSE 360 provides a clear path to single-vendor SASE convergence through gradual migration, if and when your organization requires. Follow the link for more information about Cato SSE 360.
Cato SSE 360 reduces cost and complexity with simple management through a single pane of glass, self-healing architecture and defenses that evolve automatically while mitigating emerging threats. Customers can choose to manage themselves or co-manage with partners.
Platform overview:
Cato SSE 360 Components
Cato SSE 360 provides the following platform components:
Cloud-native security service edge
Cato global private backbone
Cato SDP clients
IPsec-enabled devices and Cato Socket SD-WAN for locations
Comprehensive management application for analytics and policy configuration
As a result, Cato SSE 360 is ideal for the following use cases:
Scalable hybrid work
Gradual cloud migration
Secure sensitive data
Instant deployment of security capabilities
Future-proofing and ongoing security maintenance
Seamless, single-vendor SASE convergence
Cato SSE 360 extends SSE by providing full visibility and control across all traffic, optimized global application access and is the only service which supports a seamless path to a complete, single-vendor SASE, if and when required. Read the full Cato SSE 360 whitepaper and get started on your SSE journey today.
For decades, enterprises have been stuck on complex and rigid architecture that has prevented them from achieving business agility and outdoing their competition. But now... Read ›
How to Gradually Deploy SASE in an Enterprise For decades, enterprises have been stuck on complex and rigid architecture that has prevented them from achieving business agility and outdoing their competition. But now they don’t have to. SASE (Secure Access Service Edge), was recognized by Gartner in 2019 as a new category that converges enterprise networking and security point solutions into a unified, cloud-delivered service. Gartner predicts that “by 2025, at least 60% of enterprises will have explicit strategies and timelines for SASE adoption encompassing user, branch and edge access, up from 10% in 2020.”SASE converges networking and security into a single architecture that is:
Cloud-native
Globally distributed
Secure
And covers all edges
Enterprises can deploy SASE at the flip of a switch or gradually. In this blog post, we list five different gradual deployment use cases that enterprise IT can incorporate. For more detailed explanations, you can read the in-depth ebook that this blog post is based on, “SASE as a Gradual Deployment”.
[boxlink link=”https://www.catonetworks.com/resources/5-questions-to-ask-your-sase-provider/?utm_source=blog&utm_medium=top_cta&utm_campaign=5_questions_for_sase_provider”] 5 Questions to Ask Your SASE Provider | eBook [/boxlink]
Use Case #1: MPLS Migration to SD-WAN
SASE can support running MPLS alongside SD-WAN. In this first use case, enterprises leverage SASE’s SD-WAN functionalities, while turning off MPLS sites at their own schedule. Existing security and remote access solutions remain in place.
Use Case #2: Optimize Global Connectivity
SASE improves performance across global sites and WAN applications. Enterprises can use SASE for global connectivity and keep MPLS connections for critical WAN applications.
Use Case #3: Secure Branch Internet Access
SASE eliminates the need for edge security devices by including new technologies instead. For example, NGFW, IPS, ZTNA, and more. In this use case, MPLS is augmented with SASE security.
Use Case #4: Cloud Acceleration and Control
SASE’s global network of PoPs (Points of Presence) optimizes traffic in the network and to cloud data centers. Enterprises can leverage SASE instead of relying on the erratic Internet.
Use Case #5: Remote Access
SASE optimizes and secures remote traffic. By replacing VPNs with SASE, enterprises can ensure remote access to all edges through a secure network of global PoPs.
Introducing Cato: The World’s First SASE Service
Cato is the world’s first SASE platform, which supports gradual migration while connecting all network resources, including branches, mobile, remote employees, data centers, and more. Through a global and secure cloud-native network, Cato also offers:
Managed threat detection and response
Event discovery
Intelligent last-mile management
Hands-free management
So much more
To learn more about MPLS to SASE deployment, read the ebook "SASE as a Gradual Deployment".
Until COVID-19, the majority of employees worked mainly from the office. But then, everything we knew was turned upside down, both professionally and personally. The... Read ›
Your Post COVID Guide: Strategically Planning for the Hybrid Workforce Until COVID-19, the majority of employees worked mainly from the office. But then, everything we knew was turned upside down, both professionally and personally. The workforce moved to and from the office, again and again, finally settling into a “hybrid workforce” reality.
For IT teams, this abrupt change was unexpected. As a result, organizations did not have the infrastructure in place required to support remote users. At first, IT teams tried to deal with the new situation by stacking up legacy VPN servers. But these appliances did not meet agility, security and scalability demands.
Now, organizations need to find a different strategic solution to enable a productive hybrid workforce that can adapt to future changes. In this blog post, we cover the three main requirements of such a strategic solution and our technological recommendations for answering them.
(For a more in-depth analysis, you can read the ebook “The Hybrid Workforce: Planning for the New Working Reality”, which this blog post is based on.)
[boxlink link="https://www.catonetworks.com/resources/the-hybrid-workforce-planning-for-the-new-working-reality/?utm_source=blog&utm_medium=top_cta&utm_campaign=hybrid_workforce"] The Hybrid Workforce: Planning for the New Working Reality | EBOOK [/boxlink]
Requirement #1: Seamless Transition Between Home and Office
Most traditional infrastructure, namely MPLS, SD-WAN and NGFW/UTM, is focused on the office. However, there is no infrastructure that extends to remote work and home environments. This extension is required to enable a remote workforce.
Solution #1: ZTNA and SASE
ZTNA (Zero Trust Network Access) and SASE (Secure Access Service Edge) decouple network and security capabilities from physical appliances. Instead, they provide them in the cloud. This solution converges all infrastructure into a single platform that is available to everyone, everywhere.
Requirement #2: Scalable and Globally Distributed Remote Access
Today’s VPNs are appliance-centric, making them resource-intensive when scaling and maintaining them.
Solution #2: Remote Access as a Service
A global cloud service can provide remote access to a significant user base. This will free up IT resources for infrastructure management.
Requirement #3: Optimization and Security for All Traffic
Having remote access is not enough. Teams also need traffic optimization and security for performance and preventing breaches.
Solution #3: A Single Solution for All Needs
Some remote access solutions include optimization and security for all traffic types. This can be done through WAN optimization, cloud acceleration and threat prevention.
Next Steps
A global and agile network and security infrastructure can serve your hybrid workforce and help you prepare for whatever is next. Read the ebook to learn how.
A CIO position is exciting but also challenging, especially if it’s your first role… And, if you don’t plan what you want to accomplish, you... Read ›
How to Succeed as a CIO in 100 Days A CIO position is exciting but also challenging, especially if it’s your first role... And, if you don’t plan what you want to accomplish, you might find yourself putting out fires or chasing your own tail. Learn how to navigate the first 100 days of your important new role, in our helpful online guide. Use it to achieve professional success and establish your position as an invaluable business leader. (And, for more in-depth explanations, tips and stats, check out the e-book this blog post is based on.)
Phase 1: Get to Know the Organization and the Team (3 weeks)
The first step at a new company is to get to know the people and learn the company culture. Spend time with your team, stakeholders and company leadership. Use this opportunity to learn about the business, IT’s contribution and where IT fits in the business’s future goals. During these talks, map out any potential gaps or weaknesses you can identify.
To see example questions to ask during these sessions, check out the eBook.
Phase 2: Learn the IT and Security Infrastructure (3 weeks)
Once you’ve understood the expectations from your department, it’s time to learn the network infrastructure and architecture.
Take scope of:
Technologies in use
Potential hazards
SLAs
The delivery model
Existing processes
On-site and off-site work
Digital transformation status
Vendors
Similar to phase one, start mapping out any network strengths and weaknesses.
[boxlink link="https://www.catonetworks.com/resources/your-first-100-days-as-cio-5-steps-to-success/?utm_source=blog&utm_medium=top_cta&utm_campaign=first_100_days_cio"] Your First 100 Days as CIO: 5 Steps to Success | EBOOK [/boxlink]
Phase 3: Set a Strategy and Goals (2 weeks)
Finally, now is the time to determine your strategy for the upcoming year.
Organize your notes from phases 1 and 2.
Research new technologies, tools, trends and capabilities that could be relevant to your industry and requirements.
Map out your department’s strengths, weaknesses, threats and opportunities.
Determine your vision and mission statement.
Define your objectives.
Phase 4: Incorporate Digital Transformation (2 weeks)
According to McKinsey Global, following Covid-19, companies are accelerating digitization by three to seven years, acting even 40 times faster than expected! This means that CIOs who want to be perceived as future leaders need to keep up to date with digital technologies.
Look beyond traditional architectures and into trends like cloudification, convergence and mobility. According to Lars Norling, Director of IT Operations from ADB Safegate “Our analysis clearly showed the shift in the IT landscape, namely extended mobility and the move towards providing core services as cloud services. This led us to look outside of the box, beyond traditional WAN architectures.”
Gartner identifies SASE (Secure Access Service Edge) as the leading transformative technology today. SASE converges network and security into one global cloud service while reducing IT overhead, ensuring speed and performance and incorporating the latest security solutions.
Phase 5: Set Priorities (2 weeks)
Are you excited to get started on executing your plan? It’s almost time to do so. But first, prioritize the activities you want to take on, based on business requirements, ROI, urgency and risks.
Day 101
The steps above are intended to help you make days 101 and onwards a smashing success. So go over your plans, take a deep breath and get started. Good luck!
To learn more about digital transformation and SASE, let’s talk.
Read more about your first 100 days in the ebook, “Your First 100 Days as CIO: 5 Steps to Success”.
MPLS (Multiprotocol Label Switching) has been an industry-standard in enterprise networking for decades. But with modern enterprises relying more and more on public cloud services... Read ›
What Others Won’t Tell You About MPLS MPLS (Multiprotocol Label Switching) has been an industry-standard in enterprise networking for decades. But with modern enterprises relying more and more on public cloud services like Office 365, Salesforce and SAP Cloud, is MPLS enough? Perhaps there’s another solution that can meet the capacity, security, and agility requirements of the next-generation enterprise network.
5 Considerations for Evaluating MPLS and Its Alternatives
1. Agility: Can Your Network Move at the Speed of Business?
Modern enterprises need a solution that enables them to expand their business quickly and connect new sites to their existing networks. But traditional MPLS requires rolling out permanent infrastructure, which can take months and keeps businesses dependent on telco service and support.
2. Cost: Is Your Cost Per Megabit Too High?
The modern enterprise network is internet-bound, which makes it bandwidth-intensive. Enterprises need a solution that is priced in an internet-friendly manner since counting every megabit is counter-productive. But MPLS costs are megabit-based, and each megabit is pricey. Redundant circuits, resilient routing and WAN optimization drive the bill even higher.
3. Flexibility: Can The Business Transition Between On and Off-site Work?
New, post-pandemic workplaces have to be able to automatically transition between remote and on-site work. But in case of connectivity issues, transitioning to MPLS backups could cause significant delays that impede productivity.
4. Security: Can Enterprise Users Access Resources Anywhere?
To support remote work and a distributed workforce, resources, users, data and applications need to be secured wherever they are. But MPLS VPNs are hard to manage and backhauling traffic to the data centers adds latency, making the network vulnerable.
5. Management: Do You Have Visibility and Control of Your Network?
Modern businesses need co-managed networks so they can have visibility and control without having to take care of all the heavy lifting. But MPLS requires businesses to control the entire network or hand it all over to telcos.
[boxlink link="https://www.catonetworks.com/resources/what-telcos-wont-tell-you-about-mpls/?utm_source=blog&utm_medium=top_cta&utm_campaign=other_mpls"] What Others Won’t Tell You About MPLS | Download eBook [/boxlink]
Is SD-WAN the Solution for MPLS’s Shortcomings?
SD-WAN can replace some types of MPLS traffic, saving businesses from many of MPLS’ costs. However, MPLS doesn’t answer all business needs, including:
Cloud - SD-WAN focuses on physical WAN.
Security - SD-WAN employs only basic security features.
Remote and Hybrid Work - SD-WAN is a branch-oriented solution that cannot support remote work on its own.
Visibility - SD-WAN requires adding more vendors, which creates fragmented visibility.
How SASE Answers All Future WAN Needs
The solution for all future enterprise network needs is a converged solution that includes SD-WAN, a global backbone, pervasive security, and remote access in a single cloud offering.
A SASE platform offers just that:
A single platform for all capabilities, which can be activated separately at the flip of a switch.
A global WAN backbone over the cloud, ensuring traffic runs smoothly with minimal latency across global PoPs.
A unified security-as-a-service engine by converging ZTNA with SD-WAN.
A single pane of glass for all policies, configurations, monitoring, and analytics.
Flexible management - self-service, co-managed, or fully managed.
Read more about MPLS vs. SASE in the complete eBook, What Others Won’t Tell You About MPLS.
With corporations paying ransoms of seven figures and upwards to restore business continuity, cyber attackers have turned to ransomware as a lucrative income. But in... Read ›
How to Protect from Ransomware with SASE With corporations paying ransoms of seven figures and upwards to restore business continuity, cyber attackers have turned to ransomware as a lucrative income. But in addition to the immediate cost, which could reach millions of dollars, ransomware will also leave organizations with significant long-term damage. This blog post will explain the four main areas of impact of ransomware on organizations, and how Cato SASE Cloud can help prevent ransomware and protect businesses.
This blog post is based on the e-book “Ransomware is on the Rise - Cato’s Security-as-a-Service Can Help”.
4 Ways Ransomware Affects Organizations
1. Immediate Loss of Productivity
Organizations depend almost entirely on data and applications for their daily operations, including making payments, creating products and delivering and shipping them. If this comes to a halt, the loss of productivity is enormous. For some global enterprises, this could even mean losing millions of dollars per hour. Recovering backups and attempting data recovery could take IT teams weeks of work. To restore productivity, some businesses prefer to pay the ransom and get operations back on track.
2. Data Encryption
According to Cybercrime Magazine, the global cost of ransomware damages will exceed $20 billion in 2021 and $265 Billion by 2031. One of the ways attackers gain these amounts is encrypting organizational data, and requiring a payment for instructions on how to decrypt it. To motivate victims to pay, attackers might threaten to destroy the private key after a certain amount of time, or increase the price as time passes.
To view the entire list and additional ways ransomware impacts organizations, check out the ebook.
[boxlink link="https://www.catonetworks.com/resources/ransomware-is-on-the-rise-catos-security-as-a-service-can-help/?utm_source=blog&utm_medium=top_cta&utm_campaign=ransomware_ebook"] Ransomware is on the Rise – Cato’s Security as a Service can help | eBook [/boxlink]
How Cato SASE Cloud Prevents Ransomware
By converging network and security into a global, cloud-native service, Cato’s SASE platform provides visibility into traffic, edges and resources, which enables building a comprehensive and unique security solution that protects from malware while eliminating false positives.
Here’s are six ways Cato SASE Cloud protected organizations from ransomware:
1. Reputation Data & Threat Intelligence
Cato leverages threat intelligence feeds from open-source, shared communities and commercial providers. In addition, after finding that 30% of feeds contain false positives or miss IoCs, Cato built a complementing system that uses ML and AI to aggregate records and score them.
2. Blocking Command and Control Communication
Cato IPS prevents delivery of ransomware to machines, which is the primary way perpetrators gain hold of systems prior to the attack. If an attacker is already inside the network, Cato prevents the communication that attackers use to encrypt files and data.
3. Blocking Suspicious SMB File Activity
Cato IPS detects and blocks irregular network activity, which could be the result of attackers using SMB to rename or change extensions of encrypted files.
4. Zero Trust Network Access
Cato SASE Cloud provides a zero-trust approach to ensure users and hosts can only access applications and resources they are authorized for. This reduces the attack surface, limiting ransomware's ability to spread, encrypt and exfiltrate data.
5. Stopping Known and Zero-Day Threats
Leveraging machine learning, Cato’s advanced anti-malware solution defends against unknown threats and zero-day attacks, and is particularly useful against polymorphic malware designed to evade signature-based inspection engines.
6. An IPS that Sees the Full Picture, Not a Partial One
Cato’s IPS has unique capabilities across multiple security layers, including: layer-7 application awareness, user identity awareness, user/agent client fingerprint, true file type, target domain/IP reputation, traffic attributes, behavioral signature and heuristic, and more.
Scale Your Security Team with Cato MDR
Cato can offload the resource-intensive process of detecting compromised endpoints from organizations’ already-busy IT and security teams. This eliminates the need for additional installations as Cato already serves as the customer’s SASE platform, supplying unparalleled visibility into all traffic from all devices.
Capabilities provided:
Automated Threat Hunting
Human Verification
Network-Level Threat Containment
Guided Remediation
Reporting & Tracking
Assessment Check-Ups
Cato MDR service can help you identify and contain ransomware and suspicious activities before they activate and impact your business. Through lateral movement detection and baselining host behavior, Cato MDR service gives your network an extra set of eyes to detect, isolate and remediate threats. Contact us to learn more.
See the e-book “Ransomware is on the Rise - Cato’s Security-as-a-Service Can Help”.
The SD-WAN contract renewal period is an ideal time to review whether SD-WAN fits into your future plans. While SD-WAN is a powerful and cost-effective... Read ›
Renewing Your SD-WAN? Here’s What to Consider The SD-WAN contract renewal period is an ideal time to review whether SD-WAN fits into your future plans. While SD-WAN is a powerful and cost-effective replacement for MPLS, enterprises need to make sure it answers their evolving needs, like cloud infrastructure, mitigating cyber risks, and enabling remote access from anywhere.
4 Things to Consider Before Renewing your SD-WAN Contract
Consideration #1: Security
Enterprises need to reduce their attack surface, ensuring that only required assets are accessible, and only to authorized users.
Questions to ask yourself:
Does my SD-WAN solution include advanced security models like ZTNA?
How does my SD-WAN’s security solution integrate with other point solutions?
Does my SD-WAN solution offer threat prevention and decryption?
Consideration #2: Cloud Optimization
Traffic from and to the cloud needs to be optimized in terms of performance and security.
Questions to ask yourself:
How does my SD-WAN solution manage multi-cloud environments?
Does my SD-WAN solution provide migration capabilities?
Can my SD-WAN solution scale according to my needs?
[boxlink link="https://www.catonetworks.com/resources/5-things-sase-covers-that-sd-wan-doesnt/?utm_source=blog&utm_medium=top_cta&utm_campaign=5_sd-wan_gaps_answered_by_sase"] 5 Things SASE Covers that SD-WAN Doesn’t | EBOOK [/boxlink]
Consideration #3: Global Access
Enterprises need predictable and reliable transport to connect global locations to the cloud and data centers.
Questions to ask yourself:
Does my SD-WAN solution provide a global infrastructure to ensure low latency and optimized routing?
How does my SD-WAN solution ensure secure global access?
Will my SD-WAN solution provide an alternative in case of a network outage?
Consideration #4: Remote Access
Remote access for employees and external vendors needs to be supported to ensure business agility.
Questions to ask yourself:
How does my SD-WAN solution secure remote users?
How does my SD-WAN solution ensure remote users get optimized performance?
Does my SD-WAN solution protect from supply chain attacks?
SASE, the Next Step After SD-WAN
SASE (Secure Access Service Edge) provides value in areas where SD-WAN lacks. SASE is the next step after SD-WAN because it provides enterprises with all the point solutions’ advantages, but without the friction of integrating and maintaining them. SASE is a single platform that converges SD-WAN and network security into a single, cloud-native global service.
In fact, according to Gartner, by 2024, more than 60% of SD-WAN customers will have implemented a SASE architecture, compared to approximately 35% in 2020.
How SASE Answers Network and Security Requirements
Let’s see how SASE provides a solution for each of the considerations above.
Security – SASE’s converged, full security stack extends advanced and up-to-date security measures to all edges.
Cloud optimization – SASE provides frictionless and optimized cloud service with immediate scaling capabilities everywhere.
Global access – SASE PoPs deliver the service to users and locations that are nearest to them, as well as accelerating east-west and northbound traffic to the cloud.
Remote access – SASE delivers secure remote access, with the ability to instantly scale to address the new work-from-anywhere reality.
SD-WAN vs. SASE
After SD-WAN solves the branch-data center-edge challenge, SASE enables enterprises to globally expand their environment to the cloud in an optimized and secure manner.
Let’s see how the two compare:
How to Get Started with SASE
Cato is the world’s first SASE platform, converging SD-WAN and network security into a global cloud-native service. Cato optimizes and secures application access for all users and locations. Using Cato SASE Cloud, customers easily migrate from MPLS to SD-WAN, improve connectivity to on-premises and cloud applications, enable secure branch Internet access everywhere, and seamlessly integrate cloud data centers and remote users into the network with a zero-trust architecture. With Cato, your network and business are ready for whatever’s next. Start now.
When SD-WAN emerged a decade ago, it quickly became a viable and cost-effective solution to MPLS. Back then, it was the technology for digital transformation.... Read ›
5 SD-WAN Gaps that are Answered by SASE When SD-WAN emerged a decade ago, it quickly became a viable and cost-effective solution to MPLS. Back then, it was the technology for digital transformation. But today, enterprises have more advanced network and security needs, and IT leaders are realizing that SD-WAN doesn’t address them.
What’s the alternative? According to Gartner, it’s SASE (Secure Access Service Edge), an architecture that converges SD-WAN and security point solutions into a unified and cloud-native service. Gartner predicts that by 2024 more than 60% of SD-WAN customers will implement a SASE architecture.
This blog post will help you understand which SD-WAN gaps are answered by SASE, and how they are reconciled. To read the entire analysis, you can read the e-book.
SASE vs. SD-WAN for Enterprises
Let’s look at five network and security considerations modern enterprises have and how SD-WAN and SASE each respond to them.
1. Advanced Security
Enterprises today must prepare for cybersecurity attacks by implementing security solutions that will protect their critical applications. With SD-WAN, IT teams are required to add additional appliances, like NGFW, IPS and SWG. This increases the cost of deployments and complicates maintenance. SASE, on the other hand, has a built-in network security stack that secures all edges and all locations.
2. Remote Workforce
The hybrid work model is here to stay. Employees will continue to connect from home or other external locations, and third parties require access to the network as well. SD-WAN does not support this type of connectivity, since it was designed for replacing MPLS between physical locations. SASE, on the other hand, connects remote users from anywhere to the nearest PoP (point of presence), for optimized and secure access.
[boxlink link="https://www.catonetworks.com/resources/5-things-sase-covers-that-sd-wan-doesnt/?utm_source=blog&utm_medium=top_cta&utm_campaign=5_sd-wan_gaps_answered_by_sase"] 5 Things SASE Covers that SD-WAN Doesn’t | EBOOK [/boxlink]
3. Cloud Readiness
Cloud connectivity is essential for business agility, global connectivity and access to business applications. SD-WAN is limited in cloud-readiness, and requires management and integration of proprietary appliances and expensive cloud connectivity solutions. SASE, on the other hand, is based on cloud datacenters that are connected to the SASE cloud. In addition, cloud applications don’t require integration and application traffic from edges is sent to cloud instances.
4. Global Performance
Global connectivity is the backbone of businesses, but SD-WAN provides connectivity through third-party backbone providers, which are not always reliable. SASE has a private global backbone that is WAN optimized.
5. Simple Management
Work has become more complicated and noisy than ever, so IT teams need a solution that will reduce overhead, not add to it. SD-WAN and security solutions require IT teams to manage, maintain and troubleshoot functions separately. SASE converges all functions, providing visibility and simple, centralized management.
Conclusion
Enterprises today need their IT and security to support and accelerate the development and delivery of new products, and to help them respond to business changes. SASE lowers business costs, complexity and risks by connecting network and security into a holistic platform.
To learn more about how SASE can replace SD-WAN and help IT teams prepare for the needs and opportunities of tomorrow, read the e-book. To get a consultation and understand how SASE can answer your specific needs, contact us.
In today’s business climate, standing still is the kiss of death. Businesses that wish to remain competitive, increase profit margins and improve customer success need... Read ›
The ROI of Doing Nothing: How and Why IT Teams Should Strategically Plan In today’s business climate, standing still is the kiss of death. Businesses that wish to remain competitive, increase profit margins and improve customer success need to adopt new technologies and discover new markets. To support these efforts, IT teams need to be prepared for digital change - by making a strategic leap towards a network and security architecture that enables rapid and agile digital transformation. After all, today’s point solutions that only address cloud migration, remote work or certain security threats, will only remain relevant for so long.
This blog post breaks down the considerations and requirements of strategic change, while comparing two courses of action - transforming early or waiting for the last minute - and proposes a plan for gradual adoption of SASE.
If you’d like to read a more in-depth breakdown of the process, with calculations and user testimonials, you’re welcome to view the e-book that this blog is based on.
5 Expected Network Demands in the Near Future
The first step to take when deciding how to address network changes is to understand what to expect, i.e why IT teams even need to change course. Let’s look at five network demands IT teams will probably encounter in the (very) near future.
1. Accelerated Application Migration to the Cloud
As more teams require access to applications and infrastructure in the cloud, IT teams need to find ways to manage user and service access, deal with “Shadow IT” and enforce cloud policies from legacy networks. This is essential for ensuring secure connectivity and business continuity.
2. Rising MPLS Bandwidth Costs
MPLS is expensive and eats up a large portion of IT spend. As applications generate more traffic, video and data, costs are expected to go up even more. IT teams need to find a more cost-effective replacement, or get a higher budget.
3. Connecting Remote Workers
Remote and hybrid work are expected to stay long after Covid-19. But, ensuring performance, security and user experience for WFA users with traditional remote-access VPN is mission impossible for IT teams. This requires a long-term solution that is both stable and reliable.
4. Connecting the Supply Chain
The new workforce consists of contractors, consultants and other service providers that require network access. However, connecting these outsourced suppliers also creates security threats. IT teams need to find a solution that enables external collaboration without the risk.
5. Rapid Global Expansion
Organizations are growing and expanding, both organically and through acquisitions. Many times, expansion takes place into new geographies and locations. IT teams are required to integrate new employees and users as quickly and seamlessly as possible, within hours and days, not months.
New Networking Demands Create New Organizational Challenges
Now that we’ve listed these network challenges, let’s understand what they mean for IT teams, on an organizational level.
Upgrades and Replacements for Hardware Appliances - More users and traffic mean more required network bandwidth. Once existing appliances reach their limit, they will need to be updated, which is both expensive and time-consuming.
Increased Cost of Human Resources - Securing and managing applications and services requires human talent and time. This means training, hiring or off-loading to a third party.
The Telco Headache - Managing a relationship with a Telco can be frustrating and cause major overhead. As needs grow, it will become even more difficult to find the right person who will take responsibility, answer tickets and respond to requests in a timely manner.
[boxlink link="https://www.catonetworks.com/resources/the-roi-of-doing-nothing/?utm_source=blog&utm_medium=top_cta&utm_campaign=roi_of_doing_nothing"] The ROI of Doing Nothing | EBOOK [/boxlink]
The Solution: Build a Digital Strategy and Act On It
With so many complicated networking challenges around the horizon, the question isn’t whether to transform, only when. To answer this question, it’s important to have a strategy in place. This strategy will allow you to address future challenges with ease and expertise, while eliminating headaches. Let’s look at two ways to build and act on a digital strategy.
The Cost of Acting Now vs. Acting Later
Businesses today face two options. For simplicity, let’s divide them into two stages: 1 and 2.
Stage 1 businesses are those that spend a significant, yet manageable, amount of their budget on MPLS. On the contrary, stage 2 companies spend an extremely large amount of money on MPLS, as new locations and workers that need to connect cloud applications and locations are added to the network.
IT teams can transform technologically when businesses are either in stage 1 or stage 2. By transforming early, problems of digital transformation can be easily avoided. Instead of putting out fires, stage 1 companies have time to plan, think through issues and devise a strategy for today and tomorrow’s requirements.
Stage 2 companies, on the other hand, are in the worst position to make a transition. This is because the money, resources and time spent on legacy solutions will determine how much money, resources and time they will have for new challenges, impacting the success and ROI of the new solution. Putting out fires is the worst reason to make a strategic decision.
The SASE Solution To Rapid Digital Transformation
According to Gartner, “Current network strategy architectures were designed with the enterprise data center as the focal point for access needs. Digital business has driven new IT architectures like cloud and edge computing and work-from-anywhere initiatives, which have in turn, inverted access requirements, with more users, devices, applications, services and data located outside of an enterprise than inside. The Covid-19 pandemic accelerated these trends.”
The industry has rallied around Gartner’s SASE (Secure Access Service Edge) architecture as the best solution to meet the challenges introduced by cloud, mobility and other dynamic shifting network traffic (which we described above).
This is because SASE provides:
Cloud-native connectivity
Worldwide access
Secure access
High performance
Access to any resource, including cloud applications and the Internet
A broad range of capabilities - NGFW, IPS, MDR and more
Scalability, without rigid constraints
5 Steps to SASE Adoption:
Think Strategically While Acting Gradually
We’ve determined that the current network is the problem and that SASE is the solution. This begs the question, how can IT teams adopt SASE without disrupting the business?
SASE can be adopted gradually and grow incrementally as current MPLS contracts expire. Here are the five steps to take to enable digital transformation and prepare your network for “whatever’s next”:
Step 1: No Change - Deploy SD-WAN devices to connect certain sites to MPLS and the Internet. The rest of the network and MPLS connections remain unmodified.
Step 2: Complement MPLS - Deploy SASE where MPLS is unavailable or too expensive, to improve connectivity to WAN applications.
Step 3: Introduce Security - Deploy functions like NGFW, Web gateways IPS, anti-malware, zero trust as existing applications meet end-of-life or can’t scale, or to new edges.
Step 4: Optimize Datacenter Access - Implement advanced routing to benefit SaaS applications instead of having them rely on the Internet, which is erratic.
Step 5: Connect Remote Users - Bring mobile and WFA users to the SASE cloud for optimized performance with ZTNA, while removing VPNs, servers, and other devices.
Conclusion: Time to Spring Into Action
Act now. You can start with a plan, a partial transition or testing, but don’t wait. By doing so, you will prevent:
High MPLS costs
Management overhead of siloed appliances and external services
Skyrocketing costs of complex MPLS networks
Constrained resources when MPLS costs rise
IT challenges to support network and security complexity
Slow and bulky networks that can’t meet digital transformation requirements
Low ROI following network and digital transformation
To learn more about the considerations and see a breakdown of transition costs and savings, access the ebook The ROI of Doing Nothing. To see how organizations can save money and achieve more than 200% ROI with Cato SASE Cloud, read the Forrester TEI (Total Economic Impact) Report.
SD-WAN networks provide multiple benefits to organizations, especially when compared to MPLS. SD-WAN improves cloud application performance, reduces WAN costs and increases business agility. However,... Read ›
Is SD-WAN Enough for Global Organizations? SD-WAN networks provide multiple benefits to organizations, especially when compared to MPLS. SD-WAN improves cloud application performance, reduces WAN costs and increases business agility. However, SD-WAN also has some downsides, which modern organizations should take into consideration when choosing SD-WAN or planning its implementation.
This blog post lists the top considerations for enterprises that are evaluating and deploying SD-WAN. It is based on the e-book “The Dark Side of SD-WAN”.
Last Mile Considerations
SD-WAN provides organizations with flexibility and cost-efficiency compared to MPLS. For the last mile, SD-WAN users can choose their preferred service, be it MPLS or last-mile services like fiber, broadband, LTE/4G, or others.
When deciding which last-mile solution to choose, we recommend taking the following criterion into consideration:
Costs
Redundancy (to ensure availability)
Reliability
Learn more about optimizing the last mile.
Middle Mile Considerations
MPLS provides predictability and stability throughout the middle mile. When designing the SD-WAN middle mile, organizations need to find a solution that provides the same capabilities.
Relying on the Internet is not recommended, since it is unpredictable. The routers are stateless and control plane intelligence is limited, which means routing decisions aren’t based on application requirements or current network levels. Instead, providers’ commercial preferences often take priority.
Learn more about reliable global connectivity.
Security Considerations
Distributed architectures require security solutions that can support multiple edges and datacenters. The four main options enterprises have today are:
The SD-WAN Firewall
Pros:
- Built into the SD-WAN appliance
Cons:
- Do not inspect user traffic
Purchasing a Unified Threat Management Device
Pros:
- Inspects user traffic
Cons:
- Requires a device for each location, which is costly and complex
Cloud-based Security
Pros:
- Eliminated firewalls at every edge
Cons:
- Based on multiple devices - the datacenter firewall, the SD-WAN and the cloud security device. This is also costly and complex.
A Converged Solution
SASE (Secure Access Service Edge) - converges SD-WAN at the edge and security in the middle, with one single location for policy management and analytics.
Cloud Access Optimization Considerations
In a modern network, external datacenters and cloud applications need to be accessed by the organization’s users, branches and datacenters. Relying on the Internet is too risky in terms of performance and availability.
It is recommended to choose a solution that offers premium connectivity or to choose a cloud network that egresses traffic from edges as close as possible to the target cloud instance.
[boxlink link="https://www.catonetworks.com/resources/the-dark-side-of-sd-wan-are-you-prepared?utm_source=blog&utm_medium=top_cta&utm_campaign=dark_side_ebook"] The Dark Side of SD-WAN | Read The eBook [/boxlink]
Network Monitoring Considerations
When monitoring the network, enterprises need to be able to identify issues in a timely manner, open tickets with ISPs and work with them until the issue is resolved.
It is recommended to set up 24/7 support and monitoring to orchestrate this and prevent outages that could impact the business.
Considerations When Managing the SD-WAN
Transitioning to SD-WAN requires deciding how to manage relationships with all the last-mile ISPs, as well as the network itself. You can manage these internally or outsource to providers.
Ask yourself the following questions:
Is it easier to manage multiple providers directly or through a single external aggregator?
How much control do you need over deployment and integrations?
What are your priorities for your internal talent’s time and resources?
Conclusion
Organizations today need to shift to support the growing use of cloud-based applications and mobile users. SD-WAN is considered a viable option by many. But is it enough? Use this blog post to evaluate if and how to implement SD-WAN. To get more details, read the complete e-book.
To learn more about SASE, let’s talk.
SASE (Secure Access Service Edge) is a new enterprise architecture technology that converges all network and security needs, by design. By replacing all point solutions,... Read ›
8 Reasons Enterprises are Adopting SASE Globally SASE (Secure Access Service Edge) is a new enterprise architecture technology that converges all network and security needs, by design. By replacing all point solutions, SASE provides a unified, global and cloud-based network that supports all edges. As a result, SASE solutions improve organizational performance, business agility and connectivity. They also reduce IT overhead.
Ever since SASE was coined as a category by Gartner in 2019, the global adoption of SASE has grown significantly. Here are eight drivers and global trends that are driving this change.
This blog post is based on the e-book “8 SASE Drivers for Modern Enterprises”.
8 SASE Drivers for Modern Enterprises
1. Enabling the “Branch Office of One”
Thanks to mobile devices and constant connectivity, employees can stay connected at all times and work from anywhere. This has turned them into a “branch office of one”, i.e a fully functional business unit, consisting of one person.
The remote working trend has been intensified by COVID-19, which has significantly enhanced its adoption. Some form of working from home is probably here to stay. McKinsey found that 52% of employees would prefer a flexible working model even after COVID.
Therefore, IT and security teams are adopting SASE solutions to enable these “branches of one” to work seamlessly and securely. SASE optimizes traffic to any edge while continuously inspecting traffic for threats and access control. This ensures all employees anywhere are productive, can access all company assets and can communicate with all employees and partners, at all times.
2. Direct-to-Internet Branch Access
Traditional branch offices are also evolving. Many employees have a constant need to communicate with others across the world and to connect to global cloud infrastructures, platforms and applications. So while these employees might be sitting together physically, they are de facto a collection of branch offices of one, with intensive communication and security requirements.
IT and security teams are implementing SASE solutions to enable high-performance to the cloud for these employees. SASE provides SD-WAN capabilities and a global private backbone that replaces the costly MPLS and the erratic Internet.
[boxlink link="https://www.catonetworks.com/resources/8-sase-drivers-for-modern-enterprises/?utm_source=blog&utm_medium=top_cta&utm_campaign=8_sase_drivers"] 8 SASE Drivers for Modern Enterprises | eBook [/boxlink]
3. Consolidating Vendors
The growing number of network and security requirements has flooded the market with vendors and point solutions. IT and security teams are having a difficult time figuring out which platform can answer their exact needs, both now and in the future. In addition, integrating and managing all these solutions creates time-consuming complexities and overhead.
SASE is being adopted as a single, user-friendly converged solution for all network and security needs, now and in the future. With a single console for configuration, management and reporting - visibility and management capabilities are improved. In addition, implementing one security solution enables enforcing a single set of policies across the entire network and reducing the attack surface.
4. Adopting Zero Trust
Zero trust is a security model in which users are continuously authenticated before they are given access to assets or apps. It is based on the premise of “never trust, always verify”, to ensure the principle of least privilege is enforced and attackers can’t gain access to sensitive assets. Zero trust is essential for securing a global, dispersed workforce that connects remotely and not from the physical, enterprise network.
The mindset of IT and security teams is shifting, from securing physical locations to connecting and securing users and devices. Zero trust is deployed as part of SASE as a solution to access needs. By using simple mobile client software or clientless browser access, users connect dynamically to the closest SASE PoP, where their traffic is routed optimally to the data center or application. There, it is authenticated before providing access.
Check out the full ebook to view the entire list and four additional SASE drivers.
The Future of Enterprise Networks
Agile solutions that provide secure, global access with high performance are driving global digital transformation. It is becoming evident, however, that point solutions can't meet all the enterprise needs. These changes are driving the adoption of SASE, a convergence of network and security functions that drives traffic through a global network of local PoPs.
With SASE, traffic is sent to the local SASE PoP. Once traffic enters the PoP, SASE applies network and security policies and forwards it over an optimized, global, private backbone. The SASE cloud service takes care of delivering and managing a comprehensive security stack, including upgrades and security updates, for all connected users and cloud resources.
The result is optimized, secure and high performing traffic that drives business agility.
CATO Networks is Driving SASE Globally
Cato pioneered the convergence of networking and security into the cloud. Aligned with Gartner's Secure Access Service Edge (SASE) framework, Cato's vision is to deliver a next generation secure networking architecture that eliminates the complexity, costs, and risks associated with legacy IT approaches based on disjointed point solutions. With Cato, organizations securely and optimally connect any user to any application anywhere on the globe. Our cloud-first architecture enables Cato to rapidly deploy new capabilities and maintain optimum security posture, without any effort from the IT teams. With Cato, your IT organization and your business are ready for whatever comes next.
See the ebook “8 SASE Drivers for Modern Enterprises”.
The role of the CIO has changed dramatically in the past years. Until now, CIOs had been focusing on ongoing IT management. But today, technology... Read ›
5 Strategic Projects for Strategic CIOs The role of the CIO has changed dramatically in the past years. Until now, CIOs had been focusing on ongoing IT management. But today, technology creates new business models and helps achieve business goals. This makes technology the defining pillar of business transformation. CIOs who realize this and identify the right opportunities for strategically leveraging technology, can transform their organization.
Let’s look at five strategic projects that can help CIOs drive innovation and generate new revenue streams.
Project #1: Migrating MPLS or SD-WAN to SASE
Many organizations have replaced their MPLS with SD-WAN, or are in the process of doing so. SD-WAN emerged a few decades ago as a cost-effective replacement to MPLS, because it answers MPLS constraints like capacity, cost and lack of flexibility. However, SD-WAN does not provide solutions for modern requirements like security threats, remote work, global performance and cloud-native scalability.
SASE (Secure Access Service Edge) is the next step after SD-WAN. A Gartner-coined term, SASE is the convergence of SD-WAN, network security and additional IT capabilities into a global, cloud-native platform. Compared to SD-WAN and other point solutions, SASE ensures reliability, performance, security and connectivity.
In fact, according to Gartner’s Hype Cycle of Network Security 2020 - by 2024, more than 60% of SD-WAN customers will have implemented a SASE architecture, compared to approximately 35% in 2020.
How CIOs Create Business Value with SASE:
By migrating to SASE, CIOs ensure all employees will always be able to connect via a secure, global and performance optimized network. With SASE, CIOs are also relieved from the complexity and risk of supporting the business with point solutions, which are often outdated.
Project #2: Building Cloud Native Connectivity
Cloud-native infrastructure, platforms and applications provide businesses with flexibility, scalability and customizability. They also increase the speed and efficiency of processes.
Technological advancements have enabled this transition, but it is the growing need for remote accessibility and global connectivity that is accelerating it. On-premises solutions can no longer answer modern business needs for performing business activities.
SASE is a cloud-native technology, providing businesses with all the benefits of the cloud and connecting all edges, branches, users and data centers.
How CIOs Create Business Value with Cloud Native Connectivity
By building cloud native connectivity across all edges, CIOs provide employees with optimized performance, security and accessibility to any required internal or external business application. Cloud readiness also enables agile delivery to customers.
[boxlink link="https://www.catonetworks.com/resources/deploy-your-site-in-under-6-minutes/?utm_source=blog&utm_medium=top_cta&utm_campaign=6_minute_demo"] Deploy your site in under 6 minutes with Cato SASE Cloud! | Check it out [/boxlink]
Project #3: Implementing a Full Security Stack in the Cloud
Cyber attacks are becoming increasingly more sophisticated, widespread and with the potential to create more destruction. Coupled with the dissolvement of network borders, IT and security teams need to rethink their security strategy and solutions.
Existing point security solutions simply cannot keep up with all these changes. In addition, the overhead tax IT and security teams pay for finding, purchasing, managing, integrating and updating various security solutions from numerous vendors is very high.
A converged security solution implements innovative security models, like ZTNA (Zero Trust Network Access) alongside security measures like threat prevention and decryption. In addition, it is automatically updated, to ensure it can thwart CVEs and zero day threats.
How CIOs Provide Business Value with Full Stack Cloud Security
By implementing a complete security stack in the cloud, CIOs provide the company’s employees and customers with the confidence that their information is secure and accessible only to authorized users and services. In addition, IT and security teams regain peace of mind to operate with confidence and stress free.
Project #4: Enable Access to All Edges
Working remotely from home, the road or a different office is becoming increasingly popular, and is turning into a working model that is here to stay. In addition, the global distribution of networks has also introduced many new entry points to business systems. But, traditional access capabilities are not designed for these types of connectivity models.
SASE provides dynamic and secure access through global PoPs (Points of Presence). Traffic from remote users, data centers, applications or other edges is automatically detected and sent to the nearest PoP. There, it is authorized and then given access.
How CIOs Provide Business Value with Global Access to All Edges
By providing users with secure access while ensuring first-class citizen performance, CIOs become enablers for business agility and speedy deliveries. The freedom and flexibility to work from anywhere and connect to anywhere power new opportunities for business initiatives. In addition, they provide employees with working conditions fit for modern life and ensure they will not look elsewhere for an employer that enables working remotely.
5. Optimize Routing with Global Connectivity
Businesses today route high volumes of traffic, from globally dispersed employees and other edges. Performance optimization is essential for connectivity and communication so employees can get things done. However, the Internet is too erratic to be relied on, and SD-WAN providers are forced to integrate with third party backbone providers for such optimization.
SASE solutions provide a global backbone and WAN optimization, serving IT and security capabilities to all users and accelerating east-west and northbound traffic to the cloud.
How CIOs Provide Business Value with Optimized Global Connectivity
By ensuring low latency and optimized routing, CIOs are fulfilling a key requirement for business agility. From video streaming to accessing information to transferring data, optimized routing facilitates and powers business activities.
How to Get Started
Looking at this list might be daunting at first. However, all these projects can be achieved through the implementation of SASE. SASE converges network and security point solutions into a single, global, cloud-native platform that enables access from all edges. Therefore, it provides a single and streamlined answer to all network and security needs, now and in the future.
Cato is the world’s first SASE platform. Using the Cato SASE Cloud, customers easily migrate from MPLS to SD-WAN, improve connectivity to on-premises and cloud applications, enable secure branch Internet access everywhere, and seamlessly integrate cloud data centers and remote users into the network with a zero-trust architecture. With Cato, your network and business are ready for whatever’s next. Start now.
You can read more from the following resources:
Your First 100 Days as CIO: 5 Steps to Success
5 Things SASE Covers that SD-WAN Doesn’t
What is SASE?
The Hybrid Workforce: Planning for the New Working Reality
MPLS is a reliable routing technique that ensures efficiency and high performance. However, global changes like remote work, mobile connectivity and cloud-based infrastructure require businesses... Read ›
Pros and Cons of MPLS: Is It Right for Your Network? MPLS is a reliable routing technique that ensures efficiency and high performance. However, global changes like remote work, mobile connectivity and cloud-based infrastructure require businesses to reconsider their MPLS network strategy. This blog post explains what MPLS is, how it works, MPLS advantages and disadvantages and what to consider next.
What is MPLS?
MPLS (Multiprotocol Label Switching) is a network routing technique that is based on predetermined paths, instead of routers determining the next hop in real-time. This enables quicker and more efficient routing, as the router only needs to view a packet label, instead of looking up the address destination in complex routing tables. In addition, using MPLS requires setting up a dedicated connection. It is de facto a private network.
How does MPLS Work?
In MPLS, when a data packet enters the network, it is assigned a data label by the first router in the path. The label predetermines the path the packet needs to follow. It includes a value, as well as additional fields to determine the quality of service required, the position of the label in the stack and time-to-live. Based on this label, the packet is routed to the next router in its path.
The second router that receives the packet then reads this label and uses it to determine the following hop in the network. It also removes the existing label from the packet and adds a new one. This process is repeated until the data packet reaches its destination. The last router in the path removes the label from the data packet.
Since the path is predetermined, the routers only need to read the label and do not need to check the packet’s IP address. This enables faster and more efficient routing.
MPLS routing terms:
Label Edge Router (LER) - the first or last routers that either assign the first data label and determine the path or pop the label off the packet. The first router is also known as Ingress Label Switching Router (Ingress LSR) and the last as Egress LSR.
Label Switching Router (LSR) - the routers along the path that read the labels, switch them and determine the next hop for the packets.
Label Switching Path (LSP) - the path the packets are routed through in the network
Now let’s look at the advantages and disadvantages of MPLS routing.
[boxlink link="https://www.catonetworks.com/resources/what-telcos-wont-tell-you-about-mpls?utm_source=blog&utm_medium=top_cta&utm_campaign=wont_tell_you_about_mpls"] What Others Won’t Tell You About MPLS | Find Out [/boxlink]
MPLS Advantages & Benefits
MPLS provides multiple advantages to network administrators and businesses. These include:
Reliability
Routing based on labels over a private network ensures that packets will be reliably delivered to their destination. In addition, MPLS enables prioritizing traffic for different types of packets, for example routing real-time, video packets through a lower latency path. This reliability is guaranteed through service level agreements (SLAs), which also ensure the MPLS provider will resolve outages or pay a penalty.
High Performance
MPLS dedicated infrastructure assures high-quality, low latency and low jitter performance. This ensures efficiency and a good user experience. It is also essential for real-time communication, like voice, video and mission-critical information.
MPLS Disadvantages
However, there are also disadvantages to MPLS.
Expensive
MPLS services are expensive, due to their commitment to ensure high bandwidth, high performance and competitive SLAs. Deployments and upgrades of the required private connection can also turn into a resource-intensive process.
Rigid
MPLS is built for point-to-point connectivity, and not for the cloud. Therefore, the WAN does not have a centralized operations center for reconfiguring locations or deploying new ones and does not enable quick scalability.
Does Not Support All Edges
MPLS cannot be extended to the cloud since it requires its own dedicated infrastructure. Therefore, it is not a good fit for remote users or for connecting to SaaS applications.
Conclusion
MPLS is a trustworthy solution for legacy applications in enterprises. However, the transition to the cloud and remote work require businesses to reconsider their network strategy and implement more cost-effective and efficient solutions. Alternatives like SASE (Secure Access Service Edge) combine all the advantages of MPLS, SD-WAN and more.
To learn more about SASE and to see how it improves your MPLS connectivity, contact us.
Cato Networks was founded with a vision to deliver the next generation of networking and network security through a cloud–native architecture that eliminates the complexity,... Read ›
Total Economic Impact™Study: Cato Delivers 246% ROI and $4.33 Million NPV Cato Networks was founded with a vision to deliver the next generation of networking and network security through a cloud–native architecture that eliminates the complexity, costs, and risks associated with legacy IT approaches. We aim to rapidly deploy new capabilities and maintain a security posture, without any effort from the IT teams.
The question is - are we living up to our goals?
To help us and our potential customers gauge the potential impact and ROI of Cato Networks, we commissioned Forrester Consulting to conduct a Total Economic Impact (TEI) study. To be completely honest, even we were blown away by the success these companies achieved through the Cato SASE Cloud.
The study shows how Cato Networks is helping reduce costs, eliminate overhead, retire old systems, enhance security, improve performance and create higher employee morale.
Some of the key findings Forrester found, were that by using Cato, a composite organization can enjoy:
246% ROI
$4.33 million NPV
Payback in less than 6 months
$3.8 million saved on reduced operation and maintenance
Almost $44,000 saved on reduced time to configure Cato on new sites
$2.2 million saved by retiring systems that Cato replaces
Reduced time and transit cost
Security consistency
And more
This matters because today organizations are struggling with managing security and network services. They have dedicated teams for VPN, internet and WAN, and more, which need to individually manage updates at each network site. This is time-consuming and costly. In the long run, this prevents the business from transforming digitally, maintaining a competitive advantage and delivering the best services they can to their customers.
Let’s dive into some more of these key findings.
[boxlink link="https://www.catonetworks.com/resources/the-total-economic-impact-of-cato-networks?utm_source=blog&utm_medium=top_cta&utm_campaign=tei"] The Total Economic Impact™ of Cato Networks | Read The Full Report [/boxlink]
Reduced Operation and Maintenance Costs
The study revealed that Cato Networks enables saving $3.8 million in reduced operation and maintenance costs over three years. This objective is extremely important for multiple organization stakeholders, as network and security engineers spend a lot of time managing systems instead of optimizing them.
“Honestly, I was shocked to see how easy it was to set up and maintain an SD-WAN solution based on the whole Cato dashboard. Now there’s a saying that with [the previous solution], you need 10 engineers to set it up and 20 engineers to keep it running. With Cato, this all went away. It’s in the dashboard. Within the hour, you understand the idea behind it and then you can just do it.”
- IT manager, motor vehicle parts manufacturer
Reduced Configuration Time
With companies scaling and requiring flexibility to connect employees and customers from anywhere, setup and configuration time has become an important consideration when choosing a network and security solution. According to the study, Cato Network saves nearly $44,000 and a huge number of manual hours over three years.
“The other thing that we were driving towards was, because we do mergers, because we do a lot of office moves, [because] we go into different geographies, I wanted an ‘office in a box,’ fire- and-forget sort of management plane separation approach where my team could do a lot with just shipping a box out [and] having a reasonably intelligent individual follow a diagram, plug it in, have it light up in a management portal, and we're in business.”
- Director of technology, advisory, tax and assurance
Savings From Retired Systems
Expensive hardware is a huge pain for IT and security teams. It requires maintenance, upgrades, fixes and integrations with other platforms. By migrating to SASE and retiring old systems, organizations can save $2.2 million dollars with Cato, over three years.
“We don’t need to go invest in those other solutions because the Cato transport with the intelligence and the security layer does everything we need it to do.”
- Director of technology, advisory, tax and assurance
Additional Benefits
According to the report, Cato Networks also provides additional, unquantifiable benefits, like:
Reduced time and transit costs -Saving time and money transporting the equipment to remote sites.
Increased security posture - By ensuring the consistency of security rule sets across the organization.
Better application performance - Enabling practitioners to get their work done faster.
Higher employee morale - According to a director of technology, advisory, tax and assurance: “I know that if I tried to roll it back in my firm, [the employees] would revolt because of the speed it gets. My engineers love it because you ship it, we’ll configure it, it shows up, and we’re off to the races.”
Flexibility - The ability to add new mobile users without the need to add infrastructure and to deploy sites quickly.
Read the Complete Report
You’re welcome to read the complete report to dive deeper into how businesses can digitally transform with Cato Networks. It has all the financial information, more quotes and use cases, and a breakdown of costs and savings to help you gain a more in-depth understanding of Cato Network’s business impact. Read the complete TEI report.
To speak with an expert about how you can achieve such ROI in your company, contact us.
Survey Reveals Confusion about the Promise of SASE Prioritizing between network security and network performance is hardly a strategy. Yet, Cato’s recent industry survey with... Read ›
Security or Performance Survey Reveals Confusion about the Promise of SASE
Prioritizing between network security and network performance is hardly a strategy. Yet, Cato’s recent industry survey with non-Cato customers, Security or Performance: How do you Prioritize?, shows that de facto 2045 respondents (split evenly between security and network roles), need to – or believe they’ll have to – choose between security and performance.
Nothing too earth-shattering there; Gartner and other industry leaders have long reached the conclusion that Secure Access Service Edge (SASE) is the suitable network to support both security and performance needs of the digital business. So, unless using SASE, enterprises would inevitably end up having to compromise between the two.
But here’s what is shattering (and particularly confusing): Albeit the fact that the essence of SASE is never having to choose between security and performance; the 8.5% of respondents already using non-Cato’s SASE revealed an unavoidable need to compromise between them – similar to non-SASE users.
Why the Confusion?
We believe this confusion is due to vendors claiming to provide a SASE platform, where in reality they’re merely offering a portfolio of point solutions, packaged into what they misleadingly call SASE. This state was anticipated by Gartner with an explicit warning that “vendor hype complicates the understanding of the SASE market.”1
A true SASE solution – one that supports both security and performance requirements – must converge SD-WAN and cloud-native security services (FWaaS, SWG, CASB, SDP/ZTNA) in a unified software stack with single-pass processing. This approach boosts performance, increases security, and reduces overall network complexity. Deploying point-solutions patched together from so-called SASE vendors, doesn’t add up to a real SASE service. This can’t offer the enhanced security and optimized performance of a converged platform. Yet, this is the SASE service respondents know, hence their confusion is apparent across the survey.
For example, when asked how they react to performance issues with cloud applications, reactions of SASE and non-SASE users were similar. 67% of SASE users would add bandwidth, and 61% of non-SASE users claimed the same. 19% of SASE users would buy a WAN optimization appliance, as 21% of non-SASE users indicated as well.
Evidently SASE users are still suffering from performance issues, and they are forced to add point solutions accordingly. This slows down performance and makes their network more complex and less secure.
Confusion on this topic was even more noticeable among SASE users, where 14% (compared to 9% among non-SASE users) admitted they simply don’t know what to do in case of performance issues. Here are some examples of answers: “Ignore and pray it goes away,” “wait it out – ugh,” “suffer through it,” “don’t know,” and “not sure.”
Improving remote access performance was one of the three main business priorities for all respondents. This makes perfect sense in the new work-from-everywhere reality; and this is one of the most straightforward use cases of SASE. Yet even here, SASE and non-SASE users experience the same problems. 24% of SASE users vs. 27% of non-SASE users complain about poor voice/video quality. Slow application response received the same 50% from both SASE and non-SASE users.
Respondents were also asked to rate the level of confidence in their ability to detect and respond to malware and cyber-attacks. Here too, results across the board were highly comparable. On a scale of
1-10 the average answer for SASE users was 4, and for non-SASE users 3.
Both answers indicate a low level of confidence in dealing with critical situations that can severely impact the network. Although Gartner claims that SASE is the future of network security, for these respondents it’s as if having SASE makes no difference at all.
[boxlink link="https://www.catonetworks.com/resources/the-total-economic-impact-of-cato-networks?utm_source=blog&utm_medium=top_cta&utm_campaign=tei"] What to expect when you’re expecting…SASE | Find Out [/boxlink]
Making Sense of the Confusion
Respondents already using SASE are confused – and probably disappointed – from their first experience with what was presented to them a SASE service. Be aware of vendors that take an appliance, convert it to a virtual machine, host it in the cloud and call it SASE. Unfortunately, this sounds like trying to deliver a Netflix-like service from stacking thousands of DVD players in the cloud. And, from the very beginning, Gartner advised to “avoid SASE offerings that are stitched together.”
We’re honored that Cato SASE Cloud users present the flip side of this confusion. Aligned with Gartner’s SASE framework, we deliver a converged, cloud-native platform that is globally distributed across 70+PoPs, and covers all edges. As opposed to confused respondents using so called SASE services, our customers clearly understand the value of SASE and have no dilemma when it comes to security and performance. SASE is not a trade-off between performance and security efficacy, but rather the convergence of both.
“With Cato, we could move people out from our offices to their home, ensuring the same security level, performance.”
“The big difference between Cato and other solutions is the integration of network management and security.”
“Cato provides us with a platform for delivering the networking and security capabilities that help our users increase their productivity.”
“The business is moving very fast. Now with Cato we can match that speed on the network side.”
What about all those non SASE users? What’s their strategy?
Only 29% indicated they have no plans to deploy SASE.
Clearly, respondents realize the value of SASE and admit that SASE is a must; the question for them isn’t if to migrate, but rather when. This is also in line with Gartner’s prediction that “by 2025, at least 60% of enterprises will have explicit strategies and timelines for SASE adoption.” Let’s hope these respondents are introduced to true SASE offerings and enjoy both security and performance. No compromising…
On December 9th, 2021, the security industry became aware of a new vulnerability, CVE-2021-44228. With a CVSS (Common Vulnerability Scoring System) score of a perfect... Read ›
Cato Networks Rapid Response to The Apache Log4J Remote Code Execution Vulnerability On December 9th, 2021, the security industry became aware of a new vulnerability, CVE-2021-44228. With a CVSS (Common Vulnerability Scoring System) score of a perfect 10.0, CVE-2021-442288 has the highest and most critical alert level.
To give some technical background, a flaw was found in the Java logging library “Apache Log4j 2” in versions from 2.0-beta9 to 2.14.1. This could allow a remote attacker to execute code on a server running Apache if the system logs an attacker-controlled string value with the attacker's JNDI LDAP server lookup.
More simply put, this exploit would allow attackers to execute malicious code on Java applications, and as such, it poses a significant risk due to the prevalence of Log4j across the global software estate.
Cato’s Security Researchers Never Sleep, So You Can
Since the disclosure, the security analysts here at Cato Networks have been working tirelessly to identify, pinpoint and mitigate any potential vulnerability or exposure that our customers may have to this threat.
Here is our internal log of operations:
9th December 2021: The security community became aware of active exploitation attempts in the Apache Log4j software.
10th December 2021: Cato Networks identified the traffic signature associated with this exploit and started actively monitoring our customer base.
11th December 2021: Cato Networks has implemented a global blocking rule within our IPS for all Cato customers to mitigate this vulnerability.
[boxlink link="https://www.catonetworks.com/cybersecurity-masterclass/?utm_source=blog&utm_medium=top_cta&utm_campaign=masterclass"] Join one of our Cyber Security Masterclasses | Go now [/boxlink]
Action Items to Cato Customers: Just Read eMails
Cato customers have already been informed that if they have the Cato IPS enabled, they are protected. Cato is actively blocking the traffic signature of this vulnerability automatically. No patching or updates to the Cato platform is required.
This is the greatness of an IPS-as-a-Service managed by some of the greatest security researchers. Our customers don’t have to perform any maintenance work to their IPS, and can make a much better use of their time: first by communicating to their upper management that their network is already secured and second, if they are using Apache products, by following the vendor’s advisory for remediation. Thanks to Cato, they can patch Apache at their own speed without fear of infiltration and exploitation.
What about the Cato SASE Cloud? Was it exposed?
In short, no. Our engineering and operations teams have worked side by side with our security analysts to investigate our own cloud and confirm that based on everything that we know, we are not vulnerable to this exploit.
Eventually, no one is 100% bullet proof. The test is really about what you have done to minimize the potential risk, and what you can do to mitigate it when it manifests. Cato has all the resources, the skills and the talent to minimize our attack surface, and make sure that our ability to respond to emerging threats is at the maximum. This is the right balance our customers deserve.
Sadly, This Is Not Over Just Yet
As often happens with such high-profile and critical CVEs, more data and IoCs (Indicators of Compromise) are surfacing as more analysts across the IT and cyber communities dive deeper into the case.
Our researchers are continuing their work as well, monitoring new discoveries across the community on the one hand, and running our own research and analysis on the other – all together targeted to make sure our customers remain protected.
IPS (Intrusion Prevention System) is a technology for securing networks by scanning and blocking malicious network traffic. By identifying suspicious activities and dropping packets, an... Read ›
IPS Features and Requirements: Is an Intrusion Prevention System Enough? IPS (Intrusion Prevention System) is a technology for securing networks by scanning and blocking malicious network traffic. By identifying suspicious activities and dropping packets, an IPS can help reduce the attack surface of an enterprise network. Security attacks like DoS (Denial of Service), brute force attacks, viruses, worms and attacking temporary exploits can all be prevented with an IPS.
However, an IPS alone is not always enough to deal with the growing number of cyber attacks, which are negatively impacting business continuity through ransomware, network outages and data privacy breaches. This blog post explores how to implement an IPS in your overall security strategy with SASE. But first, let’s learn a bit more about IPS.
[boxlink link="https://www.catonetworks.com/resources/eliminate-threat-intelligence-false-positives-with-sase?utm_source=blog&utm_medium=top_cta&utm_campaign=eliminate_threat"] Eliminate Threat Intelligence False Positives with SASE | Get eBook [/boxlink]
IPS vs. IDS - What’s the Difference?
IPS is often confused with IDS (Intrusion Detection System). IDS is the older generation of IPS. As the name implies, it detects and reports malicious activities, without any active blocking mechanisms. As a result, an IDS requires more active attention from IT to immediately block suspicious traffic, but on the other hand, legitimate traffic is never accidentally blocked, as sometimes happens with IPS. IPS is also sometimes referred to as IDPS.
IPS Features – How it Works
Most IPS solutions sit behind the firewall, though one type of IPS, HIPS (host-based IPS) sits on endpoints. The IPS mechanism operates as follows.
The IPS:
Scans and analyzes network traffic, and watches packet flows
Detects suspicious activities
Sends alarms to IT
Drops malicious packets
Blocks traffic
Resets connections
How Does IPS Detect Malicious Activity?
There are two methods the IPS can implement to accurately detect cyberattacks.
1. Signature-based Detection
IPS compares packet flows with a dictionary of CVEs and known patterns. When there is a pattern match, the IPS automatically alerts and blocks the packets. The dictionary can either contain patterns of specific exploits, or educated guesses of variants of known vulnerabilities.
2. Anomaly-based Detection
IPS uses heuristics to identify potential threats by comparing them to a known and approved baseline level and alerting in the case of anomalies.
IPS Requirements
IPS needs to ensure:
Performance – to enable network efficiency
Speed – to identify exploitations in real-time
Accuracy – to catch the right threats and avoid false positives
IPS Joined with the Power of SASE
While IPS was built as a stand-alone solution, today it is best practice to complement it and enhance its capabilities by using IPS that is delivered as part of a SASE solution. This also enables IT to overcome the shortcomings of the stand-alone IPS:
Stand-alone IPS: Shortcomings
Inability to process encrypted packets without this having a huge impact on performance
Perimeter-based approach, which protects from incoming traffic only, and not from internal threats. (Read more about it in our ZTNA hub).
Inspection that is location-bound and does not usually include mobile and cloud traffic
High operational costs when IT updates new signatures and patches
IPS and SASE: Key Benefits
SASE is a global, cloud-native service that converges networking and security functions in one platform. By implementing IPS with SASE, IPS will:
Ensure high performance – scans and analyzes TLS-encrypted traffic without any capacity constraints that would affect performance or scaling capabilities
Secure the network, not the perimeter – inspects inbound and outbound traffic, both on a WAN or to and from the public Internet
Scan and protect all edges - includes remote users and branches, regardless of location and infrastructure (cloud or other)
Always secure and up-to-date – automatically updates the latest signatures, since these updates come from the SASE cloud, without any hands-on involvement from IT
Reducing the Attack Surface with IPS and SASE
IPS adds an important layer of security to enterprise networks, especially in this day and age of more and more highly sophisticated cyber attacks. However, to get the most out of IPS, while reducing IT overhead and costs, it is recommended to implement an IPS together with SASE.
This provides organizations with all IPS capabilities, across their entire network and for all traffic types. In addition, with SASE, the security signatures and patches are managed entirely by the SASE cloud, eliminating false positives and removing resource-intensive processes from IT’s shoulders.
Cato is the leading SASE provider, enabling organizations to securely and optimally connect any user to any application anywhere on the globe. To get a consultation or a demo of the Cato SASE Cloud and how it works with IPS, Contact Us.
In the era of digital transformation, your organization might be looking for a more agile and cloud-friendly alternative to MPLS. But while getting off your... Read ›
How to Terminate Your MPLS Contract Early In the era of digital transformation, your organization might be looking for a more agile and cloud-friendly alternative to MPLS. But while getting off your MPLS contract might seem daunting due to hefty early termination fees, it’s actually easier and less expensive than you might think. Let’s look at the four steps required for terminating your MPLS contract, so you can find more flexible solutions (like SASE).
This blog post is based on the e-book “How to Terminate Your MPLS Contract Early”, which you can view here.
4 Steps for Your Get-Off-MPLS Strategy
Here are the four steps we recommend to help you make a smooth transition from MPLS to the solution of your choice, like SASE:
Understand the scope and terms of your MPLS contract
Identify the MPLS circuits that can (and should) be replaced
Involve your internal finance partners
Use these negotiating tactics with your MPLS provider
Now let’s dive into each one of them.
1. Understand the Scope and Terms of your MPLS Contract
MPLS contracts are long legal documents, but it’s important to understand which terms and conditions you’re obliged to. Here are some important things to look out for:
Does your termination date refer to the entire agreement, or to single MPLS circuits? In most contracts, the latter is the case. This means that your organization might have a number of separate terms for various circuits with different start and end dates. In such cases, it’s recommended to identify circuits that are about to expire the soonest to start the migration with them.
Is there a Minimum Annual Revenue Commitment (MARC)? Many MPLS contracts require a minimal monthly or annual spend. If you retire one of your circuits, and your spending diminishes to below that minimum. you might be subject to a financial penalty.
What is your liability for terminating an MPLS circuit before the termination date? Do you have to pay the entire sum of the fees, or maybe some of them? Discontinuing might still be worth it, despite the fees.
What’s your notice of termination period? Check how early you have to notify the carrier about discontinuing services.
Are you subject to automatic renewal? Are you locked into the contract unless you notify the carrier otherwise?
By understanding what your contract requires, you can now proceed to the next steps of determining your termination and transition plan.
[boxlink link="https://www.catonetworks.com/resources/terminate-your-mpls-contract-early-heres-how/?utm_source=blog&utm_medium=top_cta&utm_campaign=terminate_mpls"] Terminate Your MPLS Contract Early | Here's How [/boxlink]
2. Identify the MPLS Circuits that Can (and Should) Be Replaced
To get a better picture of your available termination options, we recommend preparing a spreadsheet that will help you determine which circuits to target first:
Create a row for each circuit
Detail the liabilities and termination dates for each one.
Order the circuits according to termination dates to see which ones can be migrated the soonest.
Identify circuits that can be terminated without violating MARC and incurring penalties
Check the monthly rate for circuits, in case you want to overlap through the migration
Termination Date
Liabilities
Termination Penalty
MARC Violation (Y/N)
Monthly Rate (Y/N)
Circuit A
Circuit B
Circuit C
Now that you have your circuit status laid out, identify additional factors that will influence your migration options and negotiation:
How much are you spending with your carrier overall? Even if you have early MPLS termination fees, you may be able to negotiate and leverage additional services to help waive them.
What’s the ROI of your services after switching to SASE? The numbers will help you decide which penalties are worth paying.
Now that you’ve identified different action plans, it’s time to get the finance department involved.
Migrating from MPLS to SASE with Cato Networks
Cato is the world’s first SASE platform, converging SD-WAN and network security into a global cloud-native service. Cato optimizes and secures application access for all users and locations. Using Cato SASE Cloud, customers easily migrate from MPLS to SD-WAN, improve connectivity to on-premises and cloud applications, enable secure branch Internet access everywhere, and seamlessly integrate cloud data centers and remote users into the network with a zero-trust architecture. With Cato, your network and business are ready for whatever’s next. Learn more.
In Q1 2021, 190 billion traffic flows passed through Cato’s SASE Network. Leveraging deep network visibility and proprietary machine learning algorithms, our MDR team set... Read ›
Security Threat Research Highlights #1 In Q1 2021, 190 billion traffic flows passed through Cato’s SASE Network. Leveraging deep network visibility and proprietary machine learning algorithms, our MDR team set out to analyze and identify new cyber threats and critical security trends, and have recently published their findings in the SASE Threat Research Report. Below, we provide you with 5 key insights from this report.
Key Highlights from Cato Networks’ SASE Threat Research Report
#1. Top 5 Threat Types in 2021
By using machine learning to identify high-risk threats and verified security incidents, Cato is able to identify the most common types of attacks in Q1 2021. The top five observed threat types include:
Network Scanning: The attacker is detected testing different ports to see which services are running and potentially exploitable.
Reputation: Inbound or outbound communications are detected that point to known-bad domains or IP addresses.
Vulnerability Scan: A vulnerability scanner (like Nessus, OpenVAS, etc.) is detected running against a company’s systems.
Malware: Malware is detected within network traffic.
Web Application Attack: Attempted exploitation of a web application vulnerability, such as cross-site scripting (XSS) or SQL injection, is detected.
The top three threat types demonstrate that cybercriminals are committed to performing reconnaissance of enterprise systems (using both port and vulnerability scans) and are successfully gaining initial access (as demonstrated by the large number of inbound and outbound suspicious traffic flows).
[boxlink link="https://www.catonetworks.com/resources/ransomware-is-on-the-rise-catos-security-as-a-service-can-help?utm_source=blog&utm_medium=top_cta&utm_campaign=ransomware"] Ransomware is on the Rise | Download eBook [/boxlink]
#2. Regional Bans Create False Sense of Security
In the news, most cybercrime and other online malicious activity are attributed to a small set of countries. As a result, it seems logical that creating firewall rules blocking traffic to and from these countries would dramatically improve a company’s security posture.
However, these regional bans actually create a false sense of security. The vast majority of malicious activity originates in the US, accounting for more than these four largest sources (Venezuela, China, Germany, and Japan) put together. Regional bans have little or no impact because most malware sources and command & control servers are in the US.
#3. Cybercriminals Exploit Remote Administration Tools
Remote access and administration tools like, and TeamViewer became significantly more popular during the pandemic. These tools enabled businesses to continue functioning despite a sudden and forced transition to remote work.
However, these tools are popular with cybercriminals as well. Attackers will try to brute-force credentials for these services and use them to gain direct access to a company’s environment and resources. RDP is now a common delivery vector for ransomware, and a poorly-secured TeamViewer made the Oldsmar water treatment hack possible.
#4. Legacy Software and PHP are Commons Targets
An analysis of the Common Vulnerabilities and Exposures (CVEs) most targeted by cybercriminals reveals some interesting trends. The first is that PHP-related vulnerabilities are extremely popular, making up three of the top five vulnerabilities and potentially allowing an attacker to gain remote code execution (RCE).
Another important takeaway is that cybercriminals are targeting age-old threats lurking on enterprise networks. Cybercriminals are commonly scanning for end-of-life, unsupported systems and vulnerabilities that are over 20 years old.
#5. Enterprise Traffic Flows Aren’t What You Expect
The analysis of business network traffic flows shows that Microsoft Office and Google applications are the two most commonly used cloud apps in enterprise networks.
However, that is not to say that they are the most common network flows on enterprise networks. In fact, the average enterprise has more traffic to TikTok than Gmail, LinkedIn, or Spotify. These TikTok flows threaten enterprise security. Consumer applications can be used to deliver malware or phishing content, and the use of unsanctioned apps creates new vulnerabilities and potential attack vectors within a company’s network.
Improve Your Network Visibility and Security with Cato
Cato’s quarterly SASE Threat Research Report demonstrated the importance of deep network visibility and understanding for enterprise security. While some of the trends (such as the exploitation of remote access solutions) may have been predictable, others were less so. To learn more about the evolving threat landscape, read the full report, and stay tuned for the next one.
Cato was able to generate this report based on the deep visibility provided by its SASE network. Achieving this level of visibility is essential for enterprises looking to identify the top trends and security threats within their networks.
Managed Detection and Response (MDR) is a security service designed to provide ongoing protection, detection, and response for cybersecurity threats. MDR solutions use machine learning... Read ›
Understanding Managed Detection and Response: What is MDR? Managed Detection and Response (MDR) is a security service designed to provide ongoing protection, detection, and response for cybersecurity threats. MDR solutions use machine learning to investigate, alert, and contain cyber threats at scale. Additionally, MDR solutions should include a proactive element, including the use of threat hunting to identify and remediate vulnerabilities or undetected threats within an enterprise’s IT environment.
As the name suggests, MDR should be a fully managed solution, on top of being an automated one. While MDR relies heavily on advanced technology for threat detection and rapid incident response, human analysts should also be involved in the process to validate alerts and ensure that the proper responses are taken.
According to Gartner, MDR services provide turnkey threat detection and response through remotely delivered, 24/7 security operations center capabilities. Gartner predicts that half of companies will partner with an MDR provider by 2025.
[boxlink link="https://www.catonetworks.com/services?utm_source=blog&utm_medium=top_cta&utm_campaign=MDR_page#managed-threat-detection-and-response"] Read about our Managed Threat Detection and Response (MDR) [/boxlink]
The Need for MDR
MDR has evolved to meet the cybersecurity needs of the modern enterprise. The rapid expansion of the cyber threat landscape and widespread use of automation by threat actors means that everyone is at risk of cyberattacks. These threats are evolving quickly with new ones introduced every day.
Detecting and responding to these advanced threats requires capabilities that many enterprises are lacking. On average, it takes six months for an enterprise to identify a data breach after it has occurred (the “dwell time”), a number that has doubled in the last two years. Additionally, the cost of a data breach continues to rise and is currently almost $4 million.
MDR is important because it provides enterprises with the security capabilities that they lack in-house. With MDR, enterprises can rapidly achieve the level of security needed to prevent, detect, and respond to advanced threats, as well as sustain these capabilities as cyber threats continue to evolve.
The Challenges MDR Confronts
A six-month dwell time demonstrates that businesses are struggling to identify and respond to cybersecurity incidents, due to various factors, including:
Lack of In-House Security Talent: The cybersecurity industry is experiencing a talent gap with an estimated 3.1 million unfilled roles worldwide, and 64% of enterprises struggle to find qualified security talent. With MDR, enterprises can leverage external talent and resources to fill security gaps.
Complex Security Tools: Security solutions may require careful tuning to an enterprise’s environment, which requires expertise with these tools. MDR eliminates the need for enterprises to maintain these skills in-house.
Security Alert Overload: The average enterprise’s security operations center (SOC) receives over 10,000 security alerts per day, which can easily overwhelm a security team. MDR only notifies the enterprise of threats that require their attention.
Advanced Threat Prevention and Preparation: Preventing, detecting, and remediating attacks by threat actors requires specialized knowledge and expertise. The MDR service includes incident prevention, detection, and response.
MDR by Cato
Cato offers MDR services to its Cato SASE Cloud customers. Some of the key features of Cato MDR include:
Zero-Footprint Data Collection: Cato’s MDR and Zero-Day threat prevention services are built on Cato Cloud, its cloud-native SASE network. With network visibility and security built into the network infrastructure itself, there is no need for additional installations.
Automated Threat Hunting: Cato performs automated threat hunting, leveraging big data and machine learning to identify anomalous and suspicious traffic across its platform. Cato’s rich dataset and wide visibility enable it to rapidly and accurately identify potential threats.
Human Verification: The results of Cato’s automated analysis are verified by human security analysts. This prevents action from being taken based on false positive detections.
Network Level Threat Containment: Cato controls the infrastructure that all network traffic flows over and has application-layer visibility into traffic. This enables Cato to isolate infected systems at the network level.
Guided Remediation: Cato provides guidance to help enterprises through the process of remediating a cybersecurity incident. This helps to ensure that the threat has been eliminated before quarantine is lifted and normal operations are restored.
Cato’s MDR has immediate ‘time to value’ because it can roll out immediately with no additional solution deployment required. To learn more about Cato SASE Cloud and Cato MDR service, contact us. In our next post, MDR: The Benefits of Managed Detection and Response, we take a look at a number of key benefits that enterprises can expect when partnering with an MDR provider.
Before diving into the benefits of partnering with an MDR provider, we recommend reading our previous post, MDR: Understanding Managed Detection and Response. What is... Read ›
The Benefits of Managed Detection and Response (MDR) Before diving into the benefits of partnering with an MDR provider, we recommend reading our previous post, MDR: Understanding Managed Detection and Response.
What is MDR?
In a nutshell, MDR provides ongoing threat detection and response for network security threats using machine learning to investigate, alert, and contain security threats at scale. The “managed” in MDR refers to the fact that these automated solutions are complemented by human operators who validate alerts and support proactive activities such as threat hunting and vulnerability management.
According to Gartner, half of companies will partner with an MDR provider by 2025. This rapid adoption is driven by several factors, including the expanding cybersecurity skills gap and the emergence of technologies like secure access service edge (SASE) and zero trust network access (ZTNA) that enable MDR providers to more effectively and scalably offer their services.
[boxlink link="https://go.catonetworks.com/Eliminate-Threat-Intelligence-False-Positives-with-SASE.html?utm_source=blog&utm_medium=top_cta&utm_campaign=threat_elements"] Eliminate Threat Intelligence False Positives | eBook [/boxlink]
Managed Detection and Response Benefits
MDR providers act as a full-service outsourced SOC for their customers, and partnering with an MDR provider carries a number of benefits:
24/7 Monitoring: MDR providers offer round-the-clock monitoring and protection for client networks. Since cyberattacks can happen at any time, this constant protection is essential for rapid response to threats.
Proactive Approach: MDR offers proactive security, such as threat hunting and vulnerability assessments. By identifying and closing security holes before they are exploited by an attacker, MDR helps to reduce cyber risk and the likelihood of a successful cybersecurity incident.
Better Intelligence: MDR providers have both broad and deep visibility into client networks. This enables them to develop and use threat intelligence based on both wide industry trends and enterprise-specific threats during incident detection and response.
Experienced Analysts: MDR helps to close the cybersecurity skills gap by providing customers with access to skilled cybersecurity professionals. This both helps to meet headcount and ensures that customers have access to specialized skill sets when they need them.
Vulnerability Management: Vulnerability management can be complex and time-consuming, and many companies rapidly fall behind. MDR providers can help to identify vulnerable systems, perform virtual patching, and support the installation of required updates.
Improved Compliance: MDR providers often have expertise in regulatory compliance, and their solutions are designed to meet the requirements of applicable laws and regulations. Additionally, the deep visibility of an MDR provider can simplify and streamline compliance reporting and audits.
Managed Detection and Response Tools
When offered as part of a SASE solution, MDR delivers the following key benefits:
Zero-Footprint Data Collection: With MDR and zero-day threat prevention services built into the SASE Cloud, additional security solutions are unnecessary.
Automated Threat Hunting: When MDR monitors for suspicious network flows using ML/AI, this allows rapid, scalable detection of potential cyber threats, decreasing the time that an intrusion goes undetected (“dwell time”).
Human Verification: All automatically-generated security alerts are reviewed and validated by the SASE vendor’s SOC team. This eliminates false positives and ensures that true threats receive the attention that they deserve.
Network Level Threat Containment: The SASE vendor’s control over the underlying network infrastructure enables it to quarantine infected computers. This prevents threats from spreading while remediation is occurring.
Guided Remediation: MDR built into SASE provides contextual data and remediation recommendations for identified threats to the SASE’s vendor security team.
Adopting MDR for your Organization
Cato’s MDR has immediate ‘time to value’ for its Cato SASE Cloud customers because security is built into its network infrastructure and security services can be rolled out immediately. This allows companies to rapidly achieve the security maturity needed to achieve regulatory compliance and protect themselves against cyber threats.
To learn more about Cato’s MDR services contact us and request a free demo.
We’ve all heard of AV and VPN, but there are many more cybersecurity-related acronyms and abbreviations that are worth taking note of. We gathered a... Read ›
26 Cybersecurity Acronyms and Abbreviations You Should Get to Know We’ve all heard of AV and VPN, but there are many more cybersecurity-related acronyms and abbreviations that are worth taking note of. We gathered a list of the key acronyms to help you keep up with the constantly evolving cybersecurity landscape.
SASE
Secure Access Service Edge (SASE) is a cloud-based solution that converges network and security functionalities. SASE’s built-in SD-WAN functionality offers network optimization, while the integrated security stack – including Next Generation Firewall (NGFW), Secure Web Gateway (SWG), Zero Trust Network Access (ZTNA), and more – secures traffic over the corporate WAN. According to Gartner (that coined the term), SASE is “the future of network security.”
[boxlink link="https://www.catonetworks.com/resources/cato-sse-360-finally-sse-with-total-visibility-and-control/?utm_source=blog&utm_medium=top_cta&utm_campaign=sse_wp"] Cato SSE 360 | Get the White Paper [/boxlink]
CASB
Cloud Access Security Broker (CASB) sits between cloud applications and users. It monitors all interactions with cloud-based applications and enforces corporate security policies. As cloud adoption grows, CASB (which is natively integrated into SASE solutions) becomes an essential component of a corporate security policy.
ZTNA
Zero Trust Network Access (ZTNA), also called a software-defined perimeter (SDP), is an alternative to Virtual Private Network (VPN) for secure remote access. Unlike VPN, ZTNA provides access to corporate resources on a case-by-case basis in compliance with zero trust security policies. ZTNA can be deployed as part of a SASE solution to support the remote workforce of the modern distributed enterprise.
SDP
Software-Defined Perimeter (SDP) is another name for ZTNA. It is a secure remote access solution that enforces zero trust principles, unlike legacy remote access solutions.
ZTE
Zero Trust Edge (ZTE) is Forrester’s version of SASE and uses ZTNA to provide a more secure Internet on-ramp for remote sites and workers. A ZTE model is best implemented with SASE, which distributes security functionality at the network edge and enforce zero trust principles across the corporate WAN.
DPI
Deep Packet Inspection (DPI) involves looking at the contents of network packets rather than just their headers. This capability is essential to detecting cyberattacks that occur at the application layer. SASE solutions use DPI to support its integrated security functions.
NGFW
Next-Generation Firewall (NGFW) uses deep packet inspection to perform Layer 7 application traffic analysis and intrusion detection. NGFW also has the ability to consume threat intelligence to make informed threat decisions and may include other advanced features beyond those of the port/protocol inspection of the traditional firewall.
FWaaS
Firewall as a Service (FWaaS) delivers the capabilities of NGFW as a cloud-based service. FWaaS is one of the foundational security capabilities of a SASE solution.
IPS
Intrusion Prevention System (IPS) is designed to detect and block attempted attacks against a network or system. In addition to generating alerts, like an intrusion detection system (IDS) would, an IPS can update firewall rules or take other actions to block malicious traffic.
SWG
Secure Web Gateway (SWG) is designed to protect against Internet-borne threats such as phishing or malware and enforce corporate policies for Internet surfing. SWG is a built-in capability of a SASE solution, providing secure browsing to all enterprise employees.
NG-AM
Next Generation Anti-Malware (NG-AM) uses advanced techniques, such as machine learning and anomaly detection to identify potential malware. This allows detecting modern malware, which is designed to evade traditional, signature-based detection schemes.
UTM
Unified Threat Management (UTM) is a term for security solutions that provide a number of different network security functions. SASE delivers all network security needs from a cloud service, eliminating the hassle of dealing with appliance life-cycle management of UTM.
DLP
Data Loss Prevention (DLP) solutions are designed to identify and respond to attempted data exfiltration, whether intentional or accidental. The deep network visibility of SASE enables providing DLP capabilities across the entire corporate WAN.
WAF
Web Application Firewall (WAF) monitors and filters traffic to web applications to block attempted exploitation or abuse of web applications. SASE includes WAF functionality to protect web applications both in on-premises data centers and cloud deployments.
SIEM
Security Information and Event Management (SIEM) collects, aggregates, and analyzes data from security appliances to provide contextual data and alerts to security teams. This functionality is necessary for legacy security deployments relying on an array of standalone solutions rather than a converged network security infrastructure (i.e. SASE).
SOC
Security Operations Center (SOC) is responsible for protecting enterprises against cyberattacks. Security analysts investigate alerts to determine if they are real incidents, and, if so, perform incident response and remediation.
MDR
Managed Detection and Response (MDR) is a managed security service model that provides ongoing threat detection and response by using AI and machine learning to investigate, alert, and contain threats. When MDR is incorporated into a SASE solution, SOC teams have immediate, full visibility into all traffic, eliminating the need for additional network probes or software agents.
TLS
Transport Layer Security (TLS) is a network protocol that wraps traffic in a layer of encryption and provides authentication of the server to the client. TLS is the difference between HTTP and HTTPS for web browsing.
SSL
Secure Sockets Layer (SSL) is a predecessor to TLS. Often, the protocol is referred to as SSL/TLS.
TI
Threat Intelligence (TI) is information designed to help with detecting and preventing cyberattacks. TI can include malware signatures, known-bad IP addresses and domain names, and information about current cyberattack campaigns.
CVE
Common Vulnerabilities and Exposure (CVE) is a list of publicly disclosed computer security flaws. . Authorities like MITRE will assign a CVE to a newly-discovered vulnerability to make it easier to track and collate information about vulnerabilities across multiple sources that might otherwise name and describe it in different ways.
APT
Advanced Persistent Threat (APT) is a sophisticated cyber threat actor typically funded by nation-states or organized crime. These actors get their name from the fact that they have the resources and capabilities required to pose a sustained threat to enterprise cybersecurity.
DDoS
Distributed Denial of Service (DDoS) attacks involve multiple compromised systems sending spam requests to a target service. The objective of these attacks is to overwhelm the target system, leaving it unable to respond to legitimate user requests.
XDR
Extended Detection and Response (XDR) is a cloud-based solution that integrates multiple different security functions to provide more comprehensive and cohesive protection against cyber threats. It delivers proactive protection against attacks by identifying and blocking advanced and stealthy cyberattacks.
SSE
Security Service Edge (SSE) moves security functionality from the network perimeter to the network edge. This is the underlying principle behind SASE solutions.
IoC
Indicators of Compromise (IoC) is data that can be used to determine if a system has been compromised by a cyberattack such as malware signatures or known-based IP addresses or domains. IOCs are commonly distributed as part of a threat intelligence feed.
When deciding to digitally transform your network to SASE, the large number of vendors out there might be confusing. What’s the best approach to take... Read ›
Navigating Your First Steps with a Potential SASE Vendor When deciding to digitally transform your network to SASE, the large number of vendors out there might be confusing. What’s the best approach to take when comparing the different service providers? This blog post will provide you a methodical way to manage the conversations with any potential vendor, so you can ensure their solution can answer your needs.
To get the full SASE RFP template to help you navigate the vendor vetting process, click here. But first, let’s understand what SASE is.
What is SASE?
SASE (Secure Access Service Edge) is an innovative network and security architecture that is being increasingly adopted by global organizations. As a unified, global and cloud-based network that supports all edges, SASE improves network performance, reduces the attack surface and minimizes IT overhead.
[boxlink link="https://www.catonetworks.com/resources/sase-rfi-rfp-template/?utm_source=blog&utm_medium=top_cta&utm_campaign=sase_rfi"] SASE RFI Made Easy | Get the Template [/boxlink]
What is SASE?
SASE (Secure Access Service Edge) is an innovative network and security architecture that is being increasingly adopted by global organizations. As a unified, global and cloud-based network that supports all edges, SASE improves network performance, reduces the attack surface and minimizes IT overhead.
What to Discuss with Potential SASE Vendors
We recommend discussing four main categories with your vendor as part of your RFI process:
Your business and IT
The vendor’s architecture
The vendor’s capabilities
The vendor’s service and support
Let’s dive into each one and see which aspects should be covered.
1. Your Business and IT
The purpose of this first discussion area is to help vendors to understand your business goals and your existing architecture. This will enable them to customize their solution to your needs and explain the value it can provide you.
Discussion points should include:
Your business - provide an overview of your business, as well as the SASE project’s business goals in your eyes.
IT architecture - describe your topology and stack, including your network architecture, technologies, topologies, geographies and security capabilities. Include any existing IT projects you are running or plan to incorporate in the future.
Use cases - explain your current and planned use cases. Include geographies, mobile users, branches, cloud migration plans, and more.
Pro tip: provide the vendor with information about your future business goals that are seemingly unrelated to the project. You might be surprised at how SASE can help you achieve them.
2. SASE Architecture
The following section of the SASE RFI template will enable you to validate that the vendor’s SASE architecture meets business network needs. For example, SD-WAN, global reach, where elements are placed, and more.
Discussion points include:
Architecture components - understand how the vendor provides SD-WAN, secure branch access, cloud optimization, global connectivity and mobile access.
Architecture capabilities - ensure the architecture can support and provide high availability, stability, scalability, high performance, and simplified management.
Architecture diagram - ask to see a diagram of the vendor’s architecture.
Pro tip: Ask the vendor to explain how the different components and capabilities contribute to the success of the project and your business goals.
3. SASE Capabilities
This third section in the SASE RFP template includes all the capabilities that will improve your network and security capabilities. You can pick and choose which capabilities you need now, but make sure your SASE vendor can expand to any additional needs you will need in the future.
Capabilities to discuss:
SD-WAN - discuss link management capabilities, traffic routing and QoS, managing voice and latency-sensitive traffic, supported throughputs and edge devices, monitoring and reporting capabilities, how site provisioning works, and roll out strategies.
Security - understand how traffic is encrypted, which threat prevention and threat detection capabilities are available, how branch and cloud security are implemented, how mobile users are secured, which identity and users awareness systems are incorporated, how policies are managed and enforced and which analytics and reporting capabilities are provided.
Cloud - Which components are provided, which integrations are included and how traffic is optimized.
Mobile - How mobile users are connected to the network while optimizing and securing traffic, and if ZTNA is provided.
Global Connectivity - How traffic is optimized and latency is reduced from site to site and across the internet.
Pro tip: Ask the vendor to weigh in on which capabilities can answer your business goals.
4. SASE Support and Services
This fourth and final section of the SASE RFP template is about the relationship between you and the vendor after implementing SASE. It includes the co-management and maintenance of the project, what happens if things go wrong and how you can make changes after roll out.
Discussion points include:
Support and professional services - When and how support is provided, what the SLAs are and which professional services are available.
Managed services - which services are provided, what the different packages are, co-management capabilities, what is available through self-service and outsourcing options.
Pro tip: Ask to speak with existing customers who’ve used support services to find out how the vendor deals with issues.
Next Steps for Finding a SASE Vendor
SASE provides IT managers and network and security teams with a converged, simplified solution that replaces all existing point solutions. However, it’s important to choose the right vendor. A good SASE vendor will answer all of an organization's existing and future needs.
Take your time to discuss all the points from above with the vendor, until you’re confident that your employees’ needs will be answered and the business can continue to grow without network and security frictions.
The discussion points in this blog post are based on a more comprehensive RFP template prepared by Cato Networks. You can get the full template free of charge here.
You probably know what WAN stands for, but what about all of the other acronyms and abbreviations in the networking world? Here’s a list of... Read ›
23 Good-To-Know Networking Acronyms and Abbreviations You probably know what WAN stands for, but what about all of the other acronyms and abbreviations in the networking world? Here’s a list of the key acronyms to help you keep up with the latest in WAN transformation.
SASE
SASE (Secure Access Service Edge) converges network and security functionalities into a single cloud-based solution. SASE merges the network optimization capabilities of SD-WAN with a full security stack, including Next Generation Firewall (NGFW), Secure Web Gateway (SWG), Zero Trust Network Access (ZTNA), and more. According to Gartner that coined the term, SASE is “the future of network security.”
SD-WAN
Software-Defined Wide Area Network (SD-WAN) is a virtual WAN architecture offering optimized traffic routing over multiple different media (broadband, MPLS, 5G/LTE, etc.). By choosing the best available path, SD-WAN provides better performance and reliability than broadband Internet. Keep in mind however, that unless SD-WAN is deployed as part of SASE, it can’t support global connectivity, network optimization, WAN and Internet security, cloud acceleration, and remote users.
MPLS
Multiprotocol Label Switching (MPLS) routes traffic over telecommunications networks using short path labels instead of longer network addresses. MPLS improves the performance and reliability of traffic flows, yet remains an expensive, rigid solution with limited capacity.
[boxlink link="https://www.catonetworks.com/resources/the-top-seven-use-cases-for-sase?utm_source=blog&utm_medium=top_cta&utm_campaign=7_sase_usecase"] Top 7 Use Cases for SASE | Download eBook [/boxlink]
PoP
A Point of Presence (PoP) is an access point to a network, such as a SASE or SD-WAN appliance. Traffic can enter and exit these networks via a PoP. According to Gartner, many emerging edge applications require “a cloud-delivery-based approach, favoring providers with many points of presence (POPs).”
Source: Market Trends: How to Win as WAN Edge and Security Converge Into the Secure Access Service Edge, 29 July 2019, Joe Skorupa, Neil MacDonald
VPN
Virtual Private Network (VPN) solutions provide an encrypted link between a network and a remote user or network. Traffic sent over the VPN acts as if the remote device is directly connected to the network with full access to corporate resources. Enterprises that have traditionally relied on VPN are realizing that it’s poorly suited for the shift to the cloud and work-from-anywhere reality, as it lacks granular security, global scalability and performance optimization capabilities.
UC
Unified Communications (UC) is the integration of corporate communications services, such as voice, messaging, videoconferencing, etc. UC creates a consistent user interface and experience across multiple communications media but requires a high-performance, reliable, and geographically distributed network.
UCaaS
Unified Communications as a Service (UCaaS) is a cloud-based delivery model for UC. With SASE, UCaaS traffic is optimally routed to the UCaaS provider instance, and UC/UCaaS components connected to a SASE Cloud are protected against network attacks without requiring additional security solutions.
QoE
Quality of Experience (QoE) measures how network performance impacts the end user. QoE takes into account the fact that some performance issues may have a negligible impact on application performance while others render an application unusable. For example, SASE provides a higher QoE than VPN for cloud-based applications by eliminating the need to backhaul traffic through the enterprise network.
PbR
Policy-based Routing (PbR) routes network flows based on policies defined by a network administrator. It can provide priority to certain types of traffic or allow it to use more expensive routes, such as MPLS circuits. SD-WAN and SASE solutions offer PbR functionality.
5G
5th generation mobile networks are the most recent generation of cellular networks. They offer higher speeds and support higher densities of devices than previous generations. SD-WAN and SASE solutions often connect to 5G networks to provide increased resiliency.
AIOps
Artificial intelligence for IT operations (AIOps) uses machine learning and big data to improve IT operations. AIOps enables automated data processing, decision-making, and response for IT operations. A SASE architecture enables businesses to realize the full potential of AIOps, allowing IT to focus on valuable business objectives such as user experience, revenue, and growth.
VoIP
Voice over IP (VoIP) enables voice communications over broadband Internet. Telephony data is encoded in network packets and sent over the Internet to its destination rather than traditional phone networks. Like UC solutions, VoIP requires high-performance, reliable, and geographically distributed networks.
CDN
Content Delivery Network (CDN) is a geographically distributed network of servers that serve cached copies of web content. CDNs improve a website’s performance by moving the service closer to end users and decreasing the load on the origin server.
NaaS
Network as a Service (NaaS) is a delivery model for cloud-based networking services. With NaaS, a company can deploy and manage its own networks using infrastructure maintained by its service provider. SASE is an example of a NaaS offering because SASE PoPs provide all required network services in a cloud-based appliance.
ISP
Internet Service Providers (ISP) provide their customers with access to the Internet. In addition to Internet access, ISPs may also offer other services, such as email, web hosting, and domain registration.
uCPE
Universal Customer Premises Equipment (uCPE) is a general-purpose off-the-shelf server, including compute, storage, and networking. uCPEs provide network and security services using network function virtualization.
NFV
Network Function Virtualization (NFV) provides network functions using virtualized services rather than dedicated appliances. This enables these functions to be provided using uCPEs or cloud platforms rather than expensive, dedicated infrastructure.
VNF
Virtual Network Functions (VNF) are virtualized network services that replace dedicated hardware appliances. VNFs can be linked together using service chaining to create more complex functionality. The use of VNFs and service chaining is common among providers of SASE alternatives that lack the required service convergence of SASE.
SDN
Software-Defined Networks (SDN) decouple the control plane from the forwarding plane. The network is defined and managed in software, making it more flexible and adaptable. SD-WAN and SASE are examples of SDN applied to the corporate WAN.
LAN
Local Area Networks (LAN) link computers together within an organization. A LAN is connected to the Internet via one or more ISPs.
BGP
The Border Gateway Protocol (BGP) is a protocol for exchanging routing information between differentautonomous systems (ASes) on the Internet. Each AS advertises which IP addresses it can route traffic to, helping traffic move from its source AS to the AS closest to its destination.
OSPF
The Open Shortest Path First (OSPF) protocol is designed to route traffic within an AS. It uses Dijkstra’s algorithm to find the shortest route to its destination, minimizing the distance that the traffic needs to travel and hopefully the latency as well.
DNS
The Domain Name Service (DNS ) is the “address book” of the Internet. DNS servers translate domain names (like catonetworks.com) to the IP addresses used by computers to route traffic.
While these are some of the most common and important acronyms in networking, this is far from a complete list. To learn more about how modern networks work, read more on the Cato Networks blog.
Understanding the 2021 Strategic Roadmap for SASE Convergence In July 2019, Gartner coined the term Secure Access Service Edge (SASE) to define the next generation... Read ›
The 2021 Strategic Roadmap for SASE Convergence Understanding the 2021 Strategic Roadmap for SASE Convergence
In July 2019, Gartner coined the term Secure Access Service Edge (SASE) to define the next generation of network security technology. SASE solutions acknowledge that modern networks and security challenges are very different from the past. By integrating core security capabilities into a single service and moving them to the cloud, SASE meets the needs of the modern digital business.
In March, Gartner published this year’s 2021 strategic roadmap for SASE convergence, which details how organizations can transition from legacy security architectures to fully integrated SASE deployments. I highly recommend that you check out the report for yourself as it provides a clear and compelling vision for organizations looking to start or continue their journey to SASE.
[boxlink link="https://www.catonetworks.com/resources/cato-sase-cloud-the-future-sase-today-and-tomorrow/?utm_source=blog&utm_medium=top_cta&utm_campaign=Cato_SASE_Cloud"] Cato SASE Cloud: The Future SASE – Today and Tomorrow | eBook [/boxlink]
Architectural Transformation is Driving SASE Forward
Gartner’s claim that SASE is “the future of network security” is based on the fact that corporate networks and infrastructures are evolving and legacy security solutions are not keeping up. In the past, companies could rely on a patchwork of perimeter-based security solutions to protect corporate assets located in on-premises data centers against attack.
The modern enterprise has moved many or all of its IT assets to the cloud to take advantage of the increased flexibility and scalability that it provides. As the traditional network perimeter dissolves and organizations move more quickly, security must become software-defined and cloud-delivered to effectively protect organizations against evolving threats.
Attempting to protect the modern enterprise with a legacy security architecture is unscalable and inefficient. The average organization has dozens of standalone security solutions to configure, monitor, and maintain, often with lean security teams. As a result, many organizations struggle to secure their existing infrastructure let alone securely adapt to changing requirements, such as the adoption of work from home or hybrid work models as a result of the COVID-19 pandemic.
As organizations' infrastructure and business needs evolve, they require modern SASE Architecture to meet their security requirements. Some of the main SASE Benefits to the modern enterprise include:
Solution Integration: SASE includes a full network security stack.
Cloud-Native Security: SASE is hosted in the cloud, making it well suited to securing distributed organizations and cloud-hosted applications.
Flexibility: As a cloud-native solution, SASE offers greater scalability and lower cost than appliance-based solutions.
Network Optimization: SASE solutions include SD-WAN network optimization over encrypted links between SASE PoPs (points of presence).
Short Term Solutions and Recommended Deployment of SASE
The goal of Gartner’s strategic roadmap for SASE adoption is to help enterprises make the move from legacy security architectures to SASE. In many cases, existing commitments and limited resources make it impossible for these organizations to make the jump all at once. Gartner breaks the process into manageable steps to help organizations work through the process.
Gartner defines a number of short-term goals for organizations making the move to SASE. These goals include:
Deploying Zero Trust Network Access (ZTNA): With the rapid growth of remote work, replacing legacy virtual private networks (VPNs) for remote users is a major priority. The ZTNA capabilities of SASE make it a more secure alternative to legacy remote access solutions that allows organizations to implement their zero trust strategies to better protect their data and users.
Creating a Phase-Out Plan: Gartner recommends performing a complete equipment and contract inventory and developing a timeline for phasing out on-premises perimeter and branch security appliances. These solutions can then be replaced with SASE capabilities hosted in the cloud.
Consolidating Vendors: SASE offers complete integration of a wide range of security capabilities, eliminating the need for standalone solutions from multiple vendors. Making the switch to SASE simplifies and streamlines every aspect of security from solution acquisition to long-term monitoring and maintenance.
Performing Branch Transformation: Security appliances deployed at each physical location creates a complex and sprawling security architecture. Working to move these solutions to the cloud centralizes and simplifies an organization’s security.
In addition to these short-term goals, Gartner also outlines a number of long-term goals that an organization should pursue. These largely focus on taking advantage of the security integration and ZTNA capabilities of SASE to centralize and streamline security operations across the enterprise.
Achieving even these short-term goals can be a significant milestone for an organization. Most companies will need to develop a multi-year strategy for making the move to SASE. While this strategy will differ from one company to another, Gartner makes one recommendation that applies across the board: start the process today. To learn more about how to start your transition to SASE, don’t hesitate to contact us or request a demo today.
The COVID-19 pandemic only served to accelerate the growing shift to work from anywhere. Due to the forced, but positive, experiment with remote work, many... Read ›
Work from Anywhere Survey Finds Dramatic Increase in IT Cost The COVID-19 pandemic only served to accelerate the growing shift to work from anywhere. Due to the forced, but positive, experiment with remote work, many enterprises plan to continue supporting remote work indefinitely.
However, the shift to remote work occurred suddenly, catching many enterprises unprepared. In Cato’s recent WFA Survey, 78% of IT professionals were found to be spending more time supporting the remote workforce since the pandemic outbreak. 47% of participants experienced an increase of at least 25%, and 16% of participants suffered from an increase of over 50%.
[boxlink link="https://www.catonetworks.com/resources/the-future-of-enterprise-networking-and-security-2021-survey/?utm_source=blog&utm_medium=upper_cta&utm_campaign=survey_report?utm_source=blog&utm_medium=top_cta&utm_campaign=masterclass_4"] Get the 2021 Networking Survey Report[/boxlink]
Continued IT Challenges
The rapid transition to remote work created a scramble as enterprises tried to suddenly set up remote workforces. And, over a year later, companies are still struggling to effectively support remote work.
One of the primary challenges for enterprises is effectively securing their remote workforce. Nearly half of the respondents say they can’t provide the same level of security to remote users as in the office. This leaves the enterprise vulnerable to phishing and other Internet-borne attacks.
A significant driver of this is the reliance on legacy solutions for secure remote access. Early in the pandemic, the limitations of virtual private networks (VPNs) became plain as a massive increase in remote workers overloaded existing infrastructure. In response, companies adopted workarounds that unfortunately sacrificed enterprise security for performance.
Working from home also has a significant impact on employee productivity. Issues with VPN infrastructure mean that remote users have unstable connections to the corporate network. Additionally, 30% of the respondents claim that application performance is worse when working remotely compared to working from the office. Without the necessary infrastructure to support them, remote workers are not able to perform at their full potential, which hurts the business and its bottom line.
How the Hybrid Working Model Impacts IT
Issues with network connectivity and application performance create additional work for corporate IT departments. The shift to work from anywhere means that support requests, and the time spent on addressing them, have increased dramatically.
The biggest issue faced by IT due to the shift to remote work is that employees no longer have stable, high-performance access to corporate resources. The complexity of addressing these problems has also grown by orders of magnitude. In the past, IT was responsible for ensuring that each branch location had reliable, high-speed access to corporate assets. Now, IT must provide the same guarantees to employees that could be working from anywhere.
The shift to the new hybrid working model has created significant costs for organizations. Poor network and application performance affects employee productivity. And, IT focused on addressing support tickets, lacks the time and resources for infrastructure upgrades and other tasks. Many enterprises have already experienced the increased costs associated with work from home, but may struggle to quantify it.
SASE Gives Enterprises Adaptability
The high costs of work from anywhere stem from the fact that companies are using legacy technologies to support their remote workers. Secure Access Service Edge (SASE) enables the distributed enterprise to achieve the security and performance it needs in a sustainable and scalable way.
SASE converges SD-WAN, network security, and Zero Trust Network Access (ZTNA) into a global, cloud-native service. It optimizes and secures application access for all users and locations. Enterprises that had already adopted SASE were prepared for the pandemic and are ready for the new work from anywhere reality. Employees could connect from anywhere and have their traffic optimally and securely routed to corporate resources.
More enterprises are adopting SASE, which is a positive indication that the industry is moving in the right direction, the SASE direction. In January 2021, 19% were actively planning for a SASE deployment in the next 12 months. Just six months later, this number has increased by more than 10%. In January 2021, only 27% were considering SASE, and six months later, over 40% indicated they were considering SASE.
Post-COVID, work from anywhere is here to stay. Contact us and request a demo to learn how to reduce costs and IT service requests and better support your distributed workforce.
Corporate environments are evolving quickly, and the recent shift towards remote and hybrid work models due to COVID-19 is just the most obvious example of... Read ›
5 Steps to Prepare for SASE Adoption Corporate environments are evolving quickly, and the recent shift towards remote and hybrid work models due to COVID-19 is just the most obvious example of this. The modern enterprise network looks very different from that of even ten years ago, and security is playing catch-up.
Secure Access Service Edge (SASE) offers security designed for the modern enterprise, including native support for remote work. SASE combines networking and security functions into a single cloud service. This combination not only improves the security of the network but makes it faster and more scalable as well.
In recent years, I’ve seen a surge of interest in SASE as organizations start looking for ways to upgrade their infrastructure to support their remote workforce and achieve their goals of implementing zero trust security. However, adopting SASE means that an organization needs to make major changes in how its network operates and is secured. Below are five steps to help you make your SASE adoption process as smooth and painless as possible.
[boxlink link="https://catonetworks.easywebinar.live/registration-86?utm_campaign=blog_CTA_From_VPN_to_ZTNA_to_SASE"] Join our webinar: The Evolution of Remote Access: From VPN to ZTNA to SASE [/boxlink]
#1. Know your Users and their Applications
When planning your SASE migration, it’s important to keep your users in mind. Every organization has a unique user base, and these users and their needs will determine the required configuration for SASE. If you don’t know how your IT environment is used on a daily basis, it is much harder to secure it.
One of the core benefits of SASE is its support for zero trust security, which requires access controls to be defined based upon business needs. Understanding the structure and use cases of your IT environment is essential for ensuring a smooth migration to SASE and building effective test plans to verify services post-cutover.
#2. Know your Security Policies and Regulatory Compliance Obligations
In recent years, the regulatory landscape has exploded. New laws like the EU’s General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA) add further obligations and security requirements for organizations. When designing your SASE Architecture, it’s important to keep these regulations and corporate security policies in mind.
With the recent rise in remote work, it is essential to ensure that your SASE solution is properly set up to support a secure remote workforce. This includes configuring ZTNA/SDP to provide remote access to corporate resources while maintaining compliance with data protection regulations and corporate security policies.
#3. Prepare for the Unknown and Unexpected
The primary goal of SASE security is to simplify and streamline security by consolidating multiple functions into a single service. This enables security teams to have full visibility into their network architecture.
With this increased visibility comes the potential to discover previously unknown security issues within an organization’s IT environment. As you make the migration over to SASE, be prepared to investigate and remediate previously unknown issues, such as security breaches, poorly performing Internet circuits, shadow IT services, and unintentionally permitted traffic flows.
#4. Bring in the ‘A-Team’
A migration to SASE is a complete overhaul of an organization’s IT and security infrastructure. SASE replaces legacy security appliances with a cloud-based, fully-integrated solution. When making this transition, it is vital to engage all stakeholders in the process. This includes internal IT, external contractors, channel partners, MSPs, etc.
By bringing in all of these parties from the very beginning, an organization ensures a smoother transition to SASE. Stakeholders can identify and plan for use cases and business needs from the beginning rather than discovering them later in the process.
#5. Get Ready for Things to Get Better
After making the move, your organization will be able to take full advantage of the benefits of SASE. SASE optimizes both networking and security infrastructure, meaning that your environment will not only be more secure but more agile and efficient as well.
After migrating to SASE, IT will also be freed of the tedious and time consuming maintenance of disparate point solutions, freeing up their time to focus on core business needs.
The Road to SASE Starts Here
If you’re just starting out on your SASE journey, I recommend checking out SASE for Dummies book, which provides a solid grounding on SASE and its benefits to the organization. From there, you can pursue a SASE Expert Certification and build the skills that you will need to effectively implement SASE within your organization.
Digitalization, work-from-anywhere, and cloud computing have accelerated SASE offerings to address the need for secure and optimized access, anytime, anywhere, and on any device. In Gartner’s new... Read ›
New Gartner Report: 2021 Strategic Roadmap for SASE Convergence Digitalization, work-from-anywhere, and cloud computing have accelerated SASE offerings to address the need for secure and optimized access, anytime, anywhere, and on any device. In Gartner’s new report from March 25, Neil MacDonald, Nat Smith, Lawrence Orans, and Joe Skorupa provide invaluable insights with a clear message to enterprises: “SASE is a pragmatic and compelling model that can be partially or fully implemented today.” And, enterprises should build a strategy for replacing legacy point products with a converged SASE platform.
The migration to SASE will enable enterprises to successfully address the current and future networking and security challenges:
Shifting to cloud-delivered security to protect anywhere, anytime access to digital capabilities
Simplifying security management that has become complex due to multiple vendors, policies, and appliances
Reducing cost with MPLS replacement and SD-WAN alternative projects
Better utilizing resources and skills to overcome organizational silos and facilitate growth
Practical Advice to Follow
Gartner analyzes the gaps between the future and current state of SASE offerings, and provides a strategic roadmap, migration plan, and advice on SASE adoption over the next five years.
Short term recommendations:
Deploy ZTNA/SDP to replace legacy VPN for the remote workforce
Implement phase-out tactics for on-premises hardware in favor of SASE services
Reduce cost and complexity by leveraging converged offerings of SWGs, CASBs, and VPN
Initiate branch transformation projects to integrate cloud-based security services
Longer-term recommendations:
Consolidate SASE offerings to a single vendor or two explicitly partnered vendors
Implement ZTNA/SDP for all users, at all locations
Prefer SASE offerings that allow you to control privacy and compliance related matters
Create a sassy team of networking and security experts responsible for secure access across all edges
Strategic Assumptions to Consider
The report brings new statistics and understandings of market trends, naturally accelerated by the global crisis.
By 2024, 30% of enterprises will adopt cloud-delivered SWG, CASB, ZTNA, and FWaaS from the same vendor, up from 5% in 2020
By 2025, 60% of enterprises will have explicit strategies and timelines for SASE adoption, up from 10% in 2020
By 2023, to deliver flexible, cost-effective scalable bandwidth, 30% of enterprises will have only Internet WAN connectivity, up from 15% in 2020.
The fourth industrial revolution – aka Industry 4.0 – represents the next phase of innovation in production processes. Industry 4.0 merges traditional systems with new... Read ›
Industry 4.0 – Talking About a Revolution The fourth industrial revolution – aka Industry 4.0 – represents the next phase of innovation in production processes. Industry 4.0 merges traditional systems with new digital technologies (IoT, AI, big data, AR, robotics, M2M, real-time analytics, and so on), facilitating automation, agility, and efficiency to create a world of smart manufacturing.
In an Industry 4.0 world, supply chains are completely visible and workflows are fully automated. Factories, machines, products, and processes are all smart; all connected; and all sharing data to better serve today’s sophisticated customers. This revolution is basically the digital transformation of manufacturing, with clear benefits that include better security, reduced cost, customer satisfaction, competitive differentiation, and more.
Industry 4.0 was first introduced in 2011, so why all the buzz 10 years later?
You guessed right, it’s none other than COVID-19 accelerating the revolution. According to Gartner, by 2024, following the pandemic, over 30% of manufacturers driving Industry 4.0 programs, will change their business models compared to 10% before the pandemic. This is because manufacturers will come out of the crisis knowing they must adapt to a changed environment, with different user preferences, new processes, and flexible workplace models.
And the pressure is on you to manage and control this new
evolving environment.
Are you in a Position to Join the Revolution?
Gartner advises manufacturers to take into account disruptions such COVID-19 and “overcome impending crises with the least possible damage, and to be better prepared for any kind of downturn or even cyclical crises in the future.” Yet with today’s legacy WAN architecture, following this advice is easier said than done, and overcoming unexpected challenges with the “least possible damage” sounds like mission impossible (minus Tom Cruise and the happy ending).
Gaining business value through the ability to converge the digital and physical environments is the essence of Industry 4.0. However, the potential of this revolution can’t be realized with an outdated, fragmented network infrastructure.
Current networks were never designed to support the fundamental requirements of security, flexibility, availability, and resiliency Industry 4.0 demands. Too many manufacturers are stranded with legacy MPLS-based networks, and IT has no effective way to gain visibility across systems, locations, processes, and users; and extracting actionable data becomes close to impossible. Perhaps this is one of the reasons why Gartner predicted that by 2021 only half of all Industry 4.0 transformation initiatives would be successful.
The Cost of Being Left Behind
Let’s examine one of the essential requirements for leveraging Industry 4.0 – continuous availability. According to ITIC’s recent report, 8 out of 10 enterprises require a minimum of 99.99% uptime for their mission critical systems; and 2 out of 10 enterprises request at least 99.999% availability. These expectations may seem high, but in the context of Industry 4.0, they’re necessary and justified.
The business damage from downtime affects enterprises of all sizes and verticals. In 2020, 98% of enterprises indicated that the hourly cost of downtime was more than $100K; and for 34%, the cost reached $1M! Considering the volume of processes and systems manufacturing includes, just one hour of downtime entails significant loss to the business.
Any trouble with your network could translate into damage to production, loss of data, and negative impact on your brand reputation.
As smart manufacturing continues to evolve, manufacturers must adapt to, and keep up with, changes (both predicted and unpredicted). From IT’s perspective, this calls for a network that enables them to seamlessly and securely support new technologies as they’re introduced, alongside ensuring constant connectivity to everyone, everywhere. Without this, IT won’t be able to support Industry 4.0 projects and manufacturers will find themselves out of the game.
A Smart Factory Calls for a SASE Network
To empower manufacturers to emerge stronger from the global crisis and deliver on the promise of Industry 4.0 – a new (and smart) network is needed. A network that provides the underlying mission critical infrastructure that can support Industry 4.0 technologies. Fortunately, this network already exists. It’s called Secure Access Service Edge (SASE) and is considered by Gartner to be transformational and the future of network security.
SASE converges SD-WAN and network security into a single cloud service, delivering a uniform set of security and optimization capabilities, connecting all users, equipment, and locations. A SASE platform is cloud-native and its service is delivered through a global private backbone, supported by numerous distributed PoPs.
With SASE, IT can eliminate MPLS, deliver optimized performance, maintain a strong security posture, ensure 99.999% availability, and natively support new digital technologies.
How?
Global private backbone ensures IT can connect all enterprise resources over high-speed Internet without compromising on availability or network performance.
Enterprise-grade Security as a Service provides a consistent level of security across all edges, which is simple to manage even by small IT teams.
Built-in ZTNA/SDP guarantees employees continue working from remote without any compromise on performance and productivity; and even in crisis mode – business continues as usual.
Cloud-native integration helps migrate data and applications to the cloud with minimal risk and effort, while eliminating or avoiding the high cost of private cloud connections like Azure ExpressRoute or AWS Direct Connect.
A true SASE network will ensure you can respond better to business needs, deploy workplaces of any kind faster, and enable the Industry 4.0 transformation to support your modern global manufacturing business.
Pre or post COVID-19, the fourth industrial revolution touches upon enterprises of various types, sizes, and locations all sharing the same challenge: How to embrace new technologies that support both current and future needs, justifying their related investment. Manufacturers that succeed in leveraging the use of new technologies will be able to improve business operations, create new value, prevail the global crisis, and be ready for the unexpected; be ready for the new normal.
We’re in the midst of this revolution, and the question to be asked is not will your business be disrupted, but rather when will your business be disrupted, and how can you ensure your underlying network infrastructure is adequate to support the Industry 4.0 journey and create value for your company.
Sources:
Gartner’s Predicts 2020: Resilience in Industrie 4.0 for Advanced Manufacturing Builds on Data and Collaboration Models, ID G00465232
ITIC 2020 Global Server Hardware, Server OS Reliability Survey
Note: This is the second post following AIOps and SASE – A Match Made in the Cloud. The introduction of SASE to the market is... Read ›
Putting AIOps with SASE to Use Note: This is the second post following AIOps and SASE – A Match Made in the Cloud.
The introduction of SASE to the market is enabling enterprises to realize the potential of AIOps, bringing IT operations to a whole new level. Let’s recall the three qualities of AIOps Gartner defined: observe (gathering and monitoring data); engage (understanding and analyzing the data); act (automating actions and responding to problems). SASE improves all these qualities, creating use cases with a clear impact on the business. Here’s how:
1 – Observe Use Case: Intelligent Alerting
Technologies come and go, but data is here to stay. And the volume of data is only increasing, with alerts pouring down noisily on IT. IDC predicts that by 2025, data will grow by 61% reaching 175 zettabytes(!) of data worldwide. Now that’s a lot of data…
Even if IT uses AIOps techniques somehow, without the right network architecture, there’s no intelligent way to gather and monitor massive amounts of data. On top of the challenge of collecting and inspecting data, Computer Weekly recently discussed the struggle IT leaders have with the increasing volumes of alerts, where 99% claim that this is causing problems for their teams, and 83% admit their IT staff is suffering from alert fatigue.
Elad Menahem, our Director of Security, explains this well: “Security analysts face a daily flood of security alerts most of which are simply irrelevant. These false positives result in alert fatigue that leads security professionals to block access to legitimate business resources or simply disable their defenses, increasing the risk of infection.”
We all know the undesirable result of the boy who cried wolf. This is where AIOps with SASE can make a difference. A SASE vendor gathers and stores all data in a big data repository. With full visibility into the entire network, the SASE vendor then provides ongoing monitoring of all traffic, using AIOps to make sense of the data and alerting IT only when needed. Mostly, not alerting IT when it’s not needed. Intelligent alerting reduces alert fatigue and helps IT prioritize attention to what matters most.
2 – Engage Use Case: Root Cause Analysis
Gathering and monitoring data is just the beginning; IT also needs a way to analyze the data in order to find the root cause of a problem. In today’s complex, fragmented network environment, finding the root cause is complex accordingly. A problem can originate from a specific issue or device, or stem from several different events together, but there’s no effective way of uncovering the source within a fragmented architecture.
With SASE complexity goes away. IT can easily view past alerts in a focused context without any noise. Pinpointing problems becomes simple, quick, and accurate. In addition, real-time monitoring provides immediate visibility into the entire network, enabling IT to determine if a problem persists or not.
can also receive alerts together with an analysis, explaining why a specific conclusion was reached. This allows IT to further investigate the root cause of a problem and provide input in order to feed the AI/ML engine for optimizing detection and analysis capabilities moving forward.
3 – Act Use Case: Proactive Incident Detection
Intelligent alerting and root cause analysis facilitate accurate and effective response. AIOps with SASE delivers automated notifications to IT regarding incidents that need attention. Anomaly detection capabilities can alert IT of irregular, suspicious network behavior, so that IT is aware of any potential trouble. This accelerates remediation capabilities with a workflow process that’s already in place, calling for IT intervention only if and when needed.
AIOps with SASE enables IT to adopt a proactive approach to problem detection, adding optimization rules, fine-tuning alert thresholds, tightening security, and so on. Rather than merely reacting to incidents, IT can now predict problems even before they occur, ensuring seamless user experience and directing resources to core business initiatives.
Next Great Leap for IT
AIOps utilizes AI/ML to help IT manage networking and security effectively, in a way that truly supports the digital business. Enterprises that have already implemented SASE as their underlying network will be able to realize the full potential of AIOps, moving past the typical IT benchmarks of uptime and availability.
A SASE network supports a closed feedback loop, where IT can easily see the effectiveness of their actions, way before hearing about a problem from an annoyed end user. Guesstimating, hoping, and praying, are replaced with monitoring, understanding, and acting accordingly. AIOps with SASE empowers IT teams of the future to focus their efforts and skills around the most significant business metrics such as user satisfaction, revenue generation, and growth acceleration.
Imagine handling a vacation booking at The Venetian without the right hotel management software. It’s hard to even picture the time, effort and resources needed... Read ›
AIOps and SASE – A Match Made in the Cloud Imagine handling a vacation booking at The Venetian without the right hotel management software. It’s hard to even picture the time, effort and resources needed for basic actions like verifying a room’s availability, knowing when a room is clean for early check-in, granting guests independent access to hotel facilities without key cards, calculating the cost at check-out, etc.
Now picture an IT team equipped with legacy tools, trying to manually control an enterprise network in a multi-cloud environment, with physical datacenters, global branches, numerous employees working from everywhere and on any device, and huge volumes of data constantly being generated. Sounds out of control...
The analogy is clear: Just like The Venetian can’t be managed like a small inn from the previous century, today’s IT Operations (ITOps) can’t be effectively run with traditional tools designed for a different type of network, and different era. The needs of today’s digital business – especially with a global crisis in the background – call for some heavy-duty automation.
According to Gartner, the notion of ITOps becoming smarter and “independently” automated, is already here and available. And it’s called AIOps.
AIOps to the Rescue
The objective of Artificial Intelligence for ITOs (AIOps) is to empower IT to regain control of network and security in today’s complex, challenging environment via artificial intelligence (AI) and machine learning (ML) techniques that automate ITOps. AIOps continuously learns the patterns of an enterprise’s network, operations, and remediation actions, in order to expedite and improve processes, decision making and overall business performance.
The effect of AIOps is across the board, resulting in highly productive employees, happier customers, and better bottom line. Gartner defines Artificial Intelligence for IT operations (AIOps) as “the application of machine learning and data science to IT operations problems,” and predicts that exclusive use of AIOps for monitoring applications and infrastructure will rise from 5% in 2018 to 30% in 2023. In fact, according to Gartner “the long-term impact of AIOps on IT operations will be transformative.”
Transformative is a word with great significance. As is the word transformational used by Gartner to describe SASE. Is it merely a coincidence that today’s hottest subject – SASE, and AIOps, share the similar quality of being so impactful on the network and security industry? And what makes AIOps worthy of such a title? Let’s find out.
Transforming the Way IT Manages Enterprise Assets
When faced with network issues that need to be addressed, IT must identify what the problem is, but just as important, IT needs to understand how the problem can affect the business. Understanding this is crucial for moving from a reactive mode to a proactive mode.
With AIOps, the process of pinpointing and addressing a problem can be done on the spot, and many times even before the problem occurs. For example, preventing performance degradation or mitigating outages so that the customer experience isn’t affected. This is where AIOps brings ITOps to a whole new level.
How does this magic happen? Gartner defined three major qualities of AIOps:
Observe: Gathering and monitoring data.
Engage: Understanding and analyzing the data.
Act: Automating actions and responding to problems.
By analyzing the data from AI/ML based platforms, IT extracts accurate, actionable insights to automatically detect and respond to problems in real-time, and ahead of time. Analysis and decision-making are “offloaded” to an artificial brain that is able to process data, identify threats, make correlations, alert, and respond faster and more accurately than the manual brain.
AIOps with a SASE Twist
To truly deliver on the transformative promise of AIOps and reap the benefits, the right underlying infrastructure is needed. This means a transformational network infrastructure that enables visibility into all of the enterprise’s data, alongside the ability to deliver continuous insights across all IT platforms and tools.
Full network visibility is dependent on a converged, cloud-native architecture. And Gartner’s Secure Access Service Edge (SASE) is exactly that: the convergence of all networking functions and security into a unified cloud service, based on edge identity, combined with real-time context, and security policies.
Unfortunately, a network built on disparate point solutions with traditional technological silos can’t utilize AIOps to its full potential. In today’s complex network environment, a root cause of a problem can stem from various factors or a combination of some. It can be a problem in a specific branch, cloud datacenter or related to a service or an event; it can be a problem at the network level, application level or device-related. And, if AIOps is dependent of a fragmented infrastructure, finding, remediating, and preventing a problem becomes extremely challenging and significantly less effective.
The Great Responsibility that Comes with AIOps
On a personal note, and unlike a vendor offering boxes, we talk from experience when we say that delivering on the promise of AIOps comes with the great responsibility of having to act quickly and accurately without negatively affecting the customer.
Being the first true SASE vendor means that our infrastructure affects our many customers, and there’s no room for mistakes. This is why we built a global private backbone of 60+ PoPs, with self-healing capabilities that ensure ongoing, uninterrupted service. Our SASE platform enables us to implement the three requirements of Gartner for AIOps:
Gathering and monitoring data, stored in our big data repository (observe).
Applying AI and ML algorithms to understand and analyze the data and identify the root cause of a problem (engage).
Preventing and responding to problems automatically and accurately (act).
With SASE as the underlying network, customers benefit from AIOps without having to plan complicated strategies, make adjustments to their infrastructure, or hire AIOps experts.
AIOps presents a real boost to the modern digital business. We recognize this. Customers realize this. It’s exciting! But AIOps is too huge to cover in one blog post. Stay tuned for future posts, where we’ll share real stories, and explain the magic behind the SASE-based AIOps use cases.
Once Upon a VPN… In today’s challenging reality, remote access has become a basic requirement for businesses of all kinds, sizes, and locations. An enterprise’s... Read ›
SDP/ZTNA vs. VPN Once Upon a VPN...
In today’s challenging reality, remote access has become a basic requirement for businesses of all kinds, sizes, and locations. An enterprise’s ability to shift to a work-from-anywhere model instantly, securely, and at scale, will determine how it will weather the COVID-19 crisis.
A common way to provide remote access is with VPN; and enterprises naturally assumed they could extend their VPN solutions to keep up with evolving business needs, continuous security challenges, and the sudden explosion of remote users.
To find out if this assumption is true, let’s answer the following five questions:
1. Is VPN still relevant?
Over two decades ago VPN was the technology for providing secure remote access to the Internet. And at about the same time, the Motorola StarTAC was the mobile phone available in the market… So yes, while VPN was once the best remote access solution for the business, it no longer is.
The modern digital business of today works differently and requires a new approach to remote access. An approach that enables capabilities such as granular security, global scalability, and optimized performance. Yet, VPN fails to address these capabilities.
VPN doesn’t enable granular security policies. Instead, VPN provides users with a secure connection to the entire network, rather than to specific applications. This expands the attack surface and badly affects the enterprise’s security posture.
VPN was never designed with the purpose of delivering all users, at all locations, immediate and ongoing connectivity to enterprise applications. However, in a work-from-anywhere environment, this is exactly what’s needed; and VPN’s inability to support global scalability results in slow response time and negative impact on employee productivity.
Optimized performance isn’t supported by VPN as it relies on the unpredictable Internet. This means that for global access, IT needs to backhaul traffic to a VPN server in a datacenter and then to the cloud, adding latency to the VPN session and resulting in poor performance.
Simply put, if VPN doesn’t address the security, scalability, and performance needs of the business as it functions today, how relevant can VPN still be?
2. Can SDP address VPN’s limitations?
Software-defined perimeter (SDP) also known as Zero Trust Network Access (ZTNA), is gaining traction as the new (and preferred) approach for granting secure access to the modern business. When offered as a cloud service, SDP eliminates the scalability limitations of VPN and enables immediate increase in remote access, without requiring additional hardware or software. SDP also offers enhanced security as it provides granular access control at the application level, as well as monitoring capabilities.
So, is the answer to question #2 a simple yes? Not exactly. SDP is a better option than VPN, however, SDP as a stand-alone solution doesn’t address the critical needs of continuous threat prevention and performance optimization.
Continuous threat prevention is vital as it protects the network from threats caused by remote users (whether knowingly or unknowingly). Performance optimization is essential for granting users accessing applications from anywhere, the same experience they’d get if they were physically in the office. Without these two key capabilities, replacing VPN with just SDP seems – for lack of a better word – pointless.
3. What does Gartner think?
Gartner considers SDP to be a core component of its new market category called Secure Access Service Edge (SASE). This ensures a unified, cloud-native approach, which is the main difference between a stand-alone SDP and SDP delivered as part of SASE.
According to Gartner’s Hype Cycle for Network Security, 2020, when SDP is integrated into a SASE platform, it presents a “flexible alternative to VPN” with significant benefits to the digital business including:
Advanced security: SASE’s integrated security stack inspects all traffic passing through to the network regardless of its source or destination.
Unlimited scalability: SASE’s cloud-native, distributed architecture supports any number of users, anywhere in the world.
Enhanced Performance: A true SASE platform includes a private backbone and WAN optimization, removing the need for the unreliable public Internet and guaranteeing best performance for all users and applications.
4. What’s the big difference?
The business impact of SDP built into SASE is clear and immediate. Agility, user experience, ease of adoption, granular application access, ongoing threat prevention, and simple policy management are just some of the benefits. Mostly SDP with SASE supports the digital transformation and business continuity by enabling all employees to work securely and effectively from remote.
5. Is there a happy ending?
The Motorola StarTAC was the first flip phone ever and was broadly adopted by consumers across the globe. Still, consumers managed to happily move on (several times) to newly introduced, more advanced, and more relevant phones. The same is true with access solutions. Business needs have changed, requiring full time access to enterprise assets, alongside granular security policies to protect these assets.
SDP with SASE is an agile, remote access solution that delivers instant and unlimited scalability, ease of adoption, enhanced security, and optimized performance to all users worldwide. SDP with SASE is the adaptable solution for enterprises determined to keep their business afloat during a global crisis, while ensuring support for both unexpected changes and planned growth initiatives moving forward. It’s really time to say goodbye to VPN – without regret.
I grabbed a beer with a close friend of mine the other night. He’s in his 30’s, recently married, and expecting his first little one.... Read ›
Network Security is Not a Sports Car I grabbed a beer with a close friend of mine the other night. He’s in his 30’s, recently married, and expecting his first little one. As we chat about his new life, the matter of car buying came up. “My wife told me to go look at this SUV. I know it’s the right move and all, but there’s this hot, little Maserati...”
He didn’t need to finish. I knew what he was getting at. The Maserati, he confessed, made him feel young and free. He could go from 0 to 60 in less than 4 seconds, which we both agreed is great on paper but seldom used in city traffic. The SUV? It’s not quite as sleek and shiny but came with the latest car security features, perfect for his family’s future expansion.
“So, where’s the dilemma?” I asked him. He already answered his life-and-death question. “You’ve got to protect your family.”
“I know,” he said, “but I like having the fastest car I can afford, even if I never really drive that fast.”
Everybody Likes Sports Cars. Even IT Geeks
I wasn’t surprised. I can’t tell you how many times I’ve had similar conversations with IT professionals. The details might be different but the story is the same. A network or security appliance has reached end-of-life, and a project is kicked-off to find the latest and greatest replacement. A natural affinity for big brands with never-ending datasheets and feature lists immediately (and often subconsciously) takes hold. As we all know, “No one ever got fired for buying...” And, so, the team buys the Biggest, Baddest, Brand Appliance loaded with the newest features. Will they ever be used? Probably not. But just having them makes IT feel a bit better, like getting to 60 in less than 4 seconds.
The thing is, there is a penalty paid for that kind of speed. In my friend’s case, it’s the SUV’s security features he’ll be missing from his Maserati. In the case of IT, it’s the overhead that comes with appliances.
We’ve all seen how switching, routing, and, yes, even SD-WAN have rapidly approached commoditization as new vendors have jumped into the market. The core features, once so unique, have become commonplace. Differentiation increasing becomes about price and highly specialized features that are only applicable to a handful of companies. Increasingly, the real value of a solution is less about specific capabilities and more about the operational overhead and agility of the solution. As Gartner puts it “After decades of focusing on network performance and features, future network innovation will target operational simplicity, automation, reliability and flexible business models.”*
But regardless of the vendor, appliances as an architectures come with certain implicit limitations. There's a whole lifecycle that burdens IT with costs and complexity. Appliances need to be bought, deployed, maintained, upgraded, and retired. As patches are released, they need to be staged, tested, and deployed. It’s a complex, time-consuming operation that often necessitates disrupting network operations. And as traffic volumes grow or feature activated, the load on appliance grows, forcing upgrades outside of budgetary cycles. What's more, appliances cover only a small part of the network, requiring additional solutions for the rest of the network making overall visibility control difficult.
Appliances are good for one thing – making money. So Big Brands built on appliances have a vested interest in perpetuating those architectures. They focus on their long lists of increasingly obscure features, many of which you will never be used. But like the sex appeal of a Maserati, you only realize the mistake in buying into the Big Brand marketing when it’s too late – after the crash comes, or, in IT’s case, when the company needs to meet a key business requirement, such as mergers and acquisitions (M&A), cloud migration, and global expansion. Suddenly, the limitations of appliances become all too clear.
Take an M&A, for example. How are you going to get all of the acquired sites and your sites onto common security levels and enforced by the same policy? From a management perspective, how are you going to gain visibility into all security events?
With a NGFW appliance, your options are limited. One solution would be to align everyone to a single vendor. An enormous headache. Another solution is to keep the existing stack and buy additional products for orchestration and monitoring of the multiple security products. More expense. A third option would involve a lot of integration - manual work that no one really has the time for. Which pain would you prefer?
SUV: It’s All About Maturity, Responsibility...And Fun
The other approach is to forgo the sex appeal of the sports car, or in IT’s case, the Big Brand appliance and focus on solutions that really do meet today’s requirements for agility. Gartner terms these cloud-native services SASE (Secure Access Service Edge). They converge networking and security moving the heavy processing of edge appliances into a global, cloud-native platform where they can benefit from all of the elasticity, scalability, and affordability of the cloud.
True, cloud-native SASE services might not have the appeal of the Biggest Brands. They don’t necessarily have legions of features or claims of terabit performance.
What they do bring, however, is a global networking and security platform that empowers IT to be a business enabler and champions. By connecting and securing all enterprise edges – mobile users, remote users, branches, datacenters, cloud applications, and cloud datacenters – SASE is ready for any networking challenge the CIO might face. With all edges on one network, SASE provides the deep, enterprise-wide visibility that makes management and operations much simpler. And with SASE providers running the networking and security on global, cloud-native appliances, appliances are left to be highly scalable, easily upgradable, and always maintained by the provider.
In short, IT gains a platform, not just a product that, like the SUV, brings overall benefits to many areas. All of which makes meeting modern day requirements, simple.
Take that M&A, for example. There’s no need to deploy new appliances or even force a security change. Just have the acquired company connect their branch firewalls to the SASE cloud, and security is immediately unified, enforced, and monitored in a single place.
The same goes for other critical business challenges. Need to deploy five new pop-up stores per month? Good luck configuring, deploying and installing the necessary appliances. With SASE, you can make it 10 or even 100. Small stores can be first brought online instantly by establishing an IPsec tunnel from an existing firewall to the local SASE POP or by equipping the users with the SASE mobile client. Meanwhile, adding SASE’s self-configuring, edge SD-WAN device to the store is easy and gives the store not just SD-WAN, but security and cloud connectivity as well.
Today Is the Day of the SASE SUV
The day has arrived when someone will be fired for buying on brand alone. My friend’s wife couldn’t care a hoot how much he had a need-for-speed or that the car is named Maserati if it put her future children at risk or required them to buy yet another car to accommodate the stroller and car seat.
And the business won’t care about the logo on your router, edge SD-WAN, or NGFW appliance if you can’t be more efficient, agile, and enable the company’s success. If you can’t complete the logistics behind the M&A quickly or if you can’t enable the business to open those stores every month -- and do so with all the needed security and reliable cloud connectivity they require -- then it doesn’t matter if your HQ NGFW appliance comes from a Gartner MQ leader.
So, go enjoy that wonderful weekend with your family, take some time off from work, and don’t worry about what the new ask waiting for you from the CEO. SASE has you covered.
* Gartner, 2019 Strategic Roadmap for Networking, Jonathan Forest, Neil Rickard, 10 April 2019
Gartner does not endorse any vendor, product or service depicted in its research publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s research organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.
Remote access isn’t a new demand, yet COVID-19 caught the industry by surprise, with businesses unprepared to effectively shift to a work-from-everywhere model. Why? Because... Read ›
Remote Access Survey: Is the Industry Ready for a Global Crisis? Remote access isn’t a new demand, yet COVID-19 caught the industry by surprise, with businesses unprepared to effectively shift to a work-from-everywhere model. Why? Because enterprises were suddenly forced to enable remote access to all users, at once, and from anywhere across the globe. Current solutions, such as Virtual Private Network (VPN) servers, provide connectivity for some users, some of the time. But VPN servers can’t support all the users, all the time – which is exactly what’s needed to continue your business during a global crisis.
In our recent Remote Access Survey, we gathered data from 694 IT professionals, who shared their experiences of shifting their business to working remotely, post coronavirus outbreak. We learned that the vast majority (96%) of respondents are still using appliance-based solutions, rather than cloud services. Of those respondents, 64% have a dedicated VPN server, which isn’t suited to deliver the scalability, security and performance needed in today’s evolved business reality.
We found that more than half (55%) of the respondents experienced an increase of 75%-100% in remote access usage. And 28% reported a growth of at least 200%. VPN might still be the most common remote access technology, it was never designed to continuously connect entire enterprises to critical applications. And, in a global health crisis scenario, where everyone requires constant remote access, legacy VPN can’t support the extreme load, resulting in slow response time and affecting user productivity.
VPN provides secure access at network level, rather than at application level. This expands the attack surface and possibility for data breach, affecting the enterprise’s security posture. Providing remote access to specific applications with granular control is critical for ensuring users get access only to authorized applications, whether on premises or in the cloud. This keeps the network safe and prevents unrestricted access. Still, only 29% of the respondents indicated that they manage remote user access at application level.
When asked about performance issues, 67% of the respondents confirmed they receive complaints from their remote users, where connection instability and slow application response are the leading problems. VPN uses the unpredictable public Internet, which isn’t optimized for global access and requires backhauling traffic to a datacenter or up to the cloud. This turns VPN into a chokepoint of network traffic into the datacenter, adding latency and resulting in poor user experience.
Enterprises are seeking to strategically address the pressing matter of remote access. About half (45%) of the respondents are planning to upgrade to a larger VPN server, but interestingly only a third of them are considering a cloud service. We’re not surprised by this, and believe it indicates a current, mutual sense of urgency among enterprises, which often results in having to make rash decisions. Gartner’s new guide “Solving the Challenges of Modern Remote Access,” addresses this crisis atmosphere, offering practical recommendations and a step-by-step decision tree for dealing with the explosion of remote access.
Fortunately, our customers didn’t experience any of the issues described by the survey respondents. Our SASE platform converges networking and security into a unified, global cloud service, enabling seamless connectivity to all locations, users, and applications. Customers can effortlessly move all their users to work-from-anywhere, without degrading performance or security. This is exactly what we mean by a network that’s ready for whatever's next.
Modern enterprises are going through challenging times. Increasing price competition, customer expectations for a seamless buying experience, instant delivery – altogether require a business that... Read ›
SASE and WAN Transformation – A Strategic Duo Modern enterprises are going through challenging times. Increasing price competition, customer expectations for a seamless buying experience, instant delivery – altogether require a business that operates at optimal reliability and efficiency. At the same time, the business must be very agile to quickly adapt to market dynamics. Those business requirements are dependent on having a network and IT infrastructure that is just as agile and dynamic as the business itself.
Businesses must keep their momentum and expect IT to enable their progress. Whether it’s a merger with or acquisition of a competitor, a global expansion, or even the need to quickly open new offices, sites or stores – IT is expected to support it all in significantly shorter delivery times than ever before.
The past, the present, and the alternative future
IT teams have a long tradition of solving point problems with point solutions. A modus operandi fit for old days when there just wasn’t any good and unified alternative. Take global expansion as an example: The business is expanding to Europe. IT now need to connect the new European branches to the company’s applications in the US with guaranteed performance and availability, and without compromising on security. This would translate into multiple projects: negotiate MPLS contracts for global connectivity, deploy WAN optimization to improve the overseas application performance, connect offices with local Internet breakout, and secure each office with UTMs or SWGs.
There is an alternative approach to such scenarios, and it is called a Secure Access Service Edge, or ‘SASE’ in short. A SASE platform converges all the network and network security capabilities, typically deployed as point products, into a unified and globally distributed cloud service. SASE eliminates the need to search, evaluate, procure, integrate and maintain multiple point products needed to keep the business going.
SASE not only addresses the current challenges IT teams face with the exhausting management of multiple point product, but it also addresses the uncertainties of the future. Provided as a cloud-native service, a SASE platform can adapt to new networking and security requirements, future-proofing the IT infrastructure that is supporting the digital business.
The future looks brighter with SASE
Let’s revisit the global expansion example from the perspective of an IT team that is already using a SASE platform. The need to connect the new European offices to the applications located in the US reliably is addressed by the SASE’s global private backbone which provides an MPLS alternative. The SASE’s built-in WAN optimization capabilities ensure application performance is not degraded by long distance latency and limited bandwidth of oversees MPLS connections. Security is already in place and is enforced as soon as the new European sites are online and connected to the SASE cloud. What this means for IT is that all they need to do to support such a business expansion to Europe is to subscribe to a local Internet service -- that’s it.
So let’s compare the old way with the new. In a pre-SASE world, a global expansion project will require the procurement of multiple services (MPLS, local internet) and multiple products (WAN optimization, security, etc.), wherein a SASE world, the only requirements are just one or two Internet circuits for each office. Being an all-in-one platform, SASE also eliminates the repetitive evaluation, procurement, and integration cycles of point products significantly reducing overall project times.
SASE gets you ready for whatever’s next
IT primary responsibility is enabling the business to pursue new opportunities. M&A, cloud migration, global expansion, mobility, or the rapid deployment of new locations all play out in almost every organization.
Traditionally with each project, you would have to choose the solutions to build the infrastructure to support it. It can be Edge SD-WAN to overcome your MPLS limitations, a private global backbone to connect your remote branches, NGFWs , UTMs and SWGs to secure branches with direct internet access, and access and optimization solutions for your clouds and mobile workforce.
Looking at the following table shows that if you choose a SASE platform – all of those IT infrastructure projects will simply go away:
IT teams that lead and execute WAN transformation need to carefully choose the architecture they select to support both current and future needs of the business they serve. The power of a SASE platform as a future-proofing architecture is clear, as it is it only way IT teams can support the efficiency and agility requirements of modern and competitive businesses with an equally efficient and agile IT infrastructure.
Unified Communications-as-a-Service (UCaaS) is increasingly attractive to organizations looking to eliminate the cost of operating on-premises platforms and PSTN access contracts. However, those looking to... Read ›
Reducing WAN Spend when Adopting UCaaS Unified Communications-as-a-Service (UCaaS) is increasingly attractive to organizations looking to eliminate the cost of operating on-premises platforms and PSTN access contracts. However, those looking to adopt UCaaS to save money may be in for a nasty surprise.
UCaaS offerings move unified communications capabilities — integrated calling, conferencing, and messaging applications — normally delivered from on-premises servers, into the cloud. The idea, like so many cloud services, is that UCaaS will lower the adoption barrier by eliminating capital expenses to procure new applications, while also reducing UC implementation and operational costs - and to an extent that’s true.
Our research also shows, though, that many enterprises experience an increase in WAN costs to support connectivity to the cloud. Approximately 38% of companies benchmarked by Nemertes Research in 2018 saw their WAN costs rise as a result of their adoption of UCaaS, with a mean increase in spend of 23.5%. More than a third cited rising network costs as the biggest contributor to increasing their UC open spend in their first year of moving to the cloud.
What’s driving these network cost increases? Two factors in particular:
The need to increase bandwidth between the organization and the Internet to support connectivity to the UCaaS provider
The need to add bandwidth between locations to support new features commonly available from UCaaS providers, like video conferencing.
Those seeing rising network costs typically purchase additional MPLS bandwidth from their existing WAN supplier(s). They have not yet begun to deploy SD-WAN to add bandwidth, support real-time applications, and reduce WAN spend.
SD-WAN reduces WAN expense by virtualizing network access services, allowing organizations to replace or reduce expensive MPLS access links with lower cost Internet services while maintaining necessary performance and reliability to support voice and video communications. Emerging SD-WAN service providers further build upon the benefits of SD-WAN by offering guaranteed end-to-end performance across the globe, as well as direct network connectivity to many UCaaS providers, enabling efficient call flows.
Additional cost reductions result from collapsing the branch stack, replacing dedicated firewalls, WAN optimizers, session border controllers, and routers with converged functions that run features as virtual instances on a virtual customer-premises equipment (vCPE) or are provided by the SD-WAN. Nemertes also finds that network management costs decline on average by 20% for those organizations who have converted at least 90% of their WAN to SD-WAN.
An example of real-world potential savings is shown below. In this scenario, a 200-site organization using MPLS spends $3.476 million per year on network costs. Shifting to 100% SD-WAN reduces those costs to $2.154 million, a net savings of $1.321 million per year.
SD-WAN adoption results in further demonstrable benefits, including improved resiliency by adding secondary network connections to branch offices, faster turn-up of new branch offices, and the ability to more rapidly increasing branch office bandwidth.
Those considering, or adopting UCaaS would be wise to evaluate the impact that UCaaS adoption will have on their network, particularly with regard to demands for additional bandwidth to support video conferencing, and the need for high resiliency, low latency, and low jitter network performance. Evaluate SD-WAN as a means of meeting the performance and reliability needs of UCaaS while reducing WAN spend.
One of the key requirements of Unified Communications-as-a-Service (UCaaS) is the ability to connect to service providers via the Internet. As I discussed in my... Read ›
Optimizing UCaaS Access with SD-WAN Services One of the key requirements of Unified Communications-as-a-Service (UCaaS) is the ability to connect to service providers via the Internet. As I discussed in my previous blog, few companies, especially global organizations, have Internet access at every branch. UCaaS traffic must be backhauled across the WAN to Internet access point resulting in inefficient traffic routing for voice and video calls, and potential quality issues related to excessive delay and jitter.
To remedy this situation, network architects have two primary options: “Meet Me” direct connect services that establish a dedicated link (or links) between the enterprise’s network, and the UCaaS provider’s network, or SD-WAN.
Direct Connect
Direct connect options extend the enterprise WAN so that the UCaaS provider appears as just another node on the network. Once the direct connection is established, typically via Ethernet or MPLS, all sites are able to reach the UCaaS provider’s datacenter without having to traverse enterprise Internet connection points. An architectural example is shown below.
[caption id="attachment_6082" align="aligncenter" width="939"] Figure 1: Direct Connect to UCaaS Provider[/caption]
Approximately 16% of the more than 300 end-user organizations participating in Nemertes recent “WAN Economics 2018-19” research study currently use these types of services to connect to their cloud provider.
UCaaS providers typically offer direct connect services to their data centers for an additional fee (on top of the cost of the circuit or circuits). Examples include AWS Direct Connect (for AWS Chime), Cisco Webex Edge (for Cisco Webex), Google Cloud Interconnect (for G Suite), Microsoft ExpressRoute (for Office 365), and RingCentral CloudConnect (for RingCentral Office). Another downside to this approach is that not all UCaaS providers support this connectivity model.
Another option is the use of WAN-Cloud exchanges. Like the direct connect model, a WAN-Cloud exchange allows an organization to directly connect its existing data network to a UCaaS provider, but only if both have a presence in a co-location facility. A WAN-Cloud exchange may allow an enterprise to easily connect to multiple cloud providers who have a presence within a co-location facility. An architectural model for this approach is shown below:
[caption id="attachment_6083" align="aligncenter" width="939"] Figure 2: WAN-Cloud Exchange Access to UCaaS Provider[/caption]
Here, the customer purchases an interconnect service provided and managed by the co-location provider (e.g. Equinix, Megaport, etc.), and like the earlier direct connect example, the customer must pay an additional fee for this service, and their UCaaS provider must support this connectivity option. Approximately 13% of organizations use carrier exchange services today to connect to their provider(s).
In both of these direct connect models the customer is responsible for ensuring security of the connection between their network, and the UCaaS provider’s network, potentially creating additional cost by adding the need for firewalls and/or application layer gateways at connection points. And, customers must establish separate direct connect services for all of their cloud providers.
SD-WAN
The second approach entails leveraging SD-WAN services as the means of connectivity to the UCaaS provider. Unlike simply extending your existing data network to your UCaaS provider, SD-WAN services offer the option to reduce WAN spend by off-loading UCaaS (and other SaaS) traffic onto lower-cost Internet connection links, improve resiliency, and guarantee performance for latency sensitive traffic like VOIP. SD-WAN virtualizes available access circuits, routing traffic over the ideal path for a given application type. Some SD-WAN service providers offer direct connect connectivity from their own networks to UCaaS providers.
In the case of UCaaS, SD-WAN will pick paths that meet UCaaS requirements for delay and jitter. Some SD-WAN services will provide detailed voice and video quality performance information, and provide managed security between your network and the UCaaS provider, preventing against potential SIP attacks including data exfiltration and denial of service. Twenty-three percent of our research participants are using SD-WAN today, reporting on average 20% reduction in WAN management resource requirements, 33% reduction in troubleshooting time, fewer site outages, and faster recovery time.
An architectural model for in-net SD-WAN is shown below:
[caption id="attachment_6084" align="aligncenter" width="887"] Figure 3: SD-WAN Architectural Model[/caption]
Here, branch offices connect to SD-WAN provider points of presence over the Internet. The enterprise’s logical, virtual WAN is created by the service provider; the provider’s service cloud delivers SD-WAN functionality like routing traffic on the ideal path to support the performance and resilience needs of UCaaS traffic while minimizing cost. One way an SD-WAN service provider can optimize delivery to a UCaaS provider is by selecting an optimal Internet egress point, close to the UCaaS provider, so the last hop across the Internet is a short hop. Another way is to place a POP in the same facility as the UCaaS provider and deliver traffic to its network within the facility, or engineer a dedicated link to a nearby location, the net result being that the Internet is out of the picture for the last hop.
If you are adopting or considering adopting UCaaS make sure to evaluate how you will connect to your UCaaS provider. Consider SD-WAN services for their ability to reduce WAN spend while meeting UCaaS performance, management, and security requirements.
I’ve been an IT manager for a long time, only recently joining the Cato team. Prior to Cato, you might say that I lived my... Read ›
Tales from the Trenches: What I Love About My Cato Cloud I’ve been an IT manager for a long time, only recently joining the Cato team. Prior to Cato, you might say that I lived my life in a box — a Cisco box, a Palo Alto box, a Checkpoint box….you get the point. Now, as the IT manager at Cato, I’ve been using Cato Cloud to run Cato’s internal network. I’ve seen first hand how Cato can simplify the life of an IT manager. Below are some of my tips and observations for how I’ve gotten the most of being “out of the box” with this cloud-based security and networking service.
Bye, bye VPN. I don’t know about you but I’ve never liked my mobile VPN. It’s a pain to configure and even once you get it operational, performance can be pretty debilitating. I used to field many complaints from salespeople or executives on the road as to “how $%^* bad my mobile connection is working.” When I got to Cato, I fell in love with Cato Cloud’s mobile capabilities. The Cato mobile client works faster than any VPN I’ve experienced. Instead of having to connect back to a home office across the globe, the Cato mobile client connects to the nearest Cato PoP regardless of where in the world the device is. All of which cuts latency down because the traffic has less distance to travel and, more importantly, makes for happier roaming executive.
The cloud in my pocket. Before joining Cato, my users would constantly complain about the performance of cloud resources. With the Cato Cloud, my offices feel like they sit right next to the biggest cloud services around, like AWS, Azure, Office 365 and Jira. The performance is that good. That’s because Cato co-locates many of our PoPs in the same physical data centers as the IXPs of leading cloud providers. I’ve been able to configure rules such that our Office 365 traffic from our Tel Aviv office, for example, enters through our Tel Aviv PoP, travels across the Cato Cloud network and, then egresses in Amsterdam right next to the Internet destination. The alternative would have been sending the traffic across the Internet core which is always a crapshoot.
A huge time saver. I used to waste what felt like hours each month jumping between consols, figuring out new UIs, and the like. The simplicity of managing my Cato network has meant I can save a ton of time on the most mundane things like setting up security policies, onboarding new users, or managing a branch. I can’t quantify exactly how much time has been saved but I can tell it’s a lot. Who couldn’t use more time in their workday?
The eye in the sky. Cato gives me real-time transport monitoring through a single pane of glass. This helps me keep an eye on the Internet lines, in particular, in the event of a slowdown during the workday. In the days before we enabled bandwidth throttling, a worker started to upload 520 GB of files to Amazon S3, hogging the site’s upstream capacity. I was quickly able to see which user, what application and what type of traffic was responsible for this massive slowdown and, politely, get him to stop.
Real-time network monitoring makes me look smarter than my users. I use Cato’s analytics to monitor our Internet service usage and the connectivity of our branches. If there’s a problem, I’m the first one to get notified. I get a good chuckle when my sales guys in Atlanta are surprised to find out that they’re having an Internet problem — and I’m already working on it from halfway across the globe.
Security is so much simpler than with a traditional network. With traditional firewalls and security appliances, you need to know the nuances of the different systems you’re working with. They might all block access to specific IPs but some had you thinking in terms of applications while most others built rules based on IP. The transition can be confusing and that’s just one example. Security rules in Cato Cloud were, well, simple. I could choose to define rules how it was most conformable to me — by IP, application, and even by user identity. There aren’t a lot of “vendor extensions” that need to be mastered just to get your security going. If you know the basics of firewall operation that’s enough.
Keeping tabs on security. In most legacy systems that I worked with there was a possibility of receiving a daily or weekly report of security incidents but nothing in real-time. Even with a SIEM, we’d need to have someone examine the logs and reports to determine if there’s been an attack. It meant I was constantly reacting to incidents, a step behind the attackers launching the attacks and often the users who were calling about them. Cato’s real-time alert security notifications put me ahead of our security threats and complaints. I receive email notifications when “something’s up” and can take action right from my mobile device, if necessary.
As an IT manager, I appreciate the simplicity of setting up and managing my company’s network and all the security we need for our users, branches, applications, and data. Cato Cloud might have been early when I first looked at it years ago, but now it’s definitely time for everything the Cato Cloud has to offer.
Unified Communications as a Service (UCaaS) adoption is on the rise in the enterprise and with that comes significant impact for IT managers considering how... Read ›
Why Traditional MPLS Networks are Ill-Suited for UCaaS Unified Communications as a Service (UCaaS) adoption is on the rise in the enterprise and with that comes significant impact for IT managers considering how their MPLS network transformation. I’ll be taking a deeper look into those challenges in this week’s webinar, but here’s a quick preview.
What’s UC and why UCaaS
Like UC, UCaaS improves team collaboration by packaging calling, meetings, team collaboration into a seamless experience. But while UC brings the cost and complexity of hosting and maintaining server infrastructure in the enterprise datacenters, UCaaS avoids those problems, putting UC in the cloud. Organizations gain the flexibility, easy adoption, predictable costs, and quick access to emerging features that are first, and in many cases, only available via the cloud.
The UCaaS challenge for modern WANs
For all of its benefits, UCaaS poses significant challenges for traditional enterprise network architectures.
Most enterprise data networks are still optimized for a computing model in which the bulk of applications reside in the datacenter. Clients - including browser, native app, and those running within virtual desktop infrastructure - are used to interact with applications and data stores either in enterprise-owned facilities or within co-location providers connected to the enterprise network via Ethernet and MPLS. Internet access remains tightly controlled, with only large, or headquarters facilities having local Internet connectivity. Thus, all access to Internet-based apps requires routing flows from the branch to the headquarters or datacenter location, and then out to the Internet.
This approach is ill-suited to a rapidly changing application delivery model in which apps may reside in public cloud infrastructure (e.g. Platform-as-a-Service (PaaS) and Infrastructure-as-a-Service (IaaS) or are obtained from software-as-a-service (SaaS) providers. This is especially true for those adopting Unified Communications-as-a-Service (UCaaS) due to the potential for poor voice and video performance as a result of excessive latency and variable network performance.
Consider the scenario in which a worker at a branch office calls a worker at another branch office. In the centralized Internet access architectural model, that call would go from the originating branch, out the nearest Internet connection point, to the UCaaS provider, and then back in the Internet connection point nearest to the destination branch as shown below:
This inefficient routing of call traffic is likely to lead to poor call performance, as well as potentially overloaded Internet connection points, especially when using high-bandwidth apps like video-conferencing and video streaming.
SD-WANs and needed changes for better UCaaS experience
What’s needed is a rethinking of network architectures, one that is optimized for UCaaS. In this new model, Internet access is available at every branch, ensuring that each branch is able to reach the UCaaS provider as efficiently as possible.
But simply connecting all branches to the Internet creates security challenges and may not provide sufficient performance to support real-time applications. The answer? SD-WAN. SD-WAN enables organizations to bring direct Internet connectivity to all branch offices and may provide performance guarantees to ensure that latency and jitter levels meet the needs of real-time applications.
At the branch, SD-WAN virtualizes wide area network access services, enabling branch office traffic to be sent along the optimal route for performance need. SD-WAN services that provide their own backbone can also optimize traffic globally, avoiding potential performance issues from using Internet-based services (see below).
Furthermore, leveraging SD-WAN services that offer security management can reduce operating costs, and headaches, saving enterprise customers from the expense and complexity of managing distributed Internet access points. They can ensure the application of consistent policies at all branches without the need to deploy additional branch hardware, and they can protect against UC-specific attacks including SIP ex-filtration (in which SIP requests are used to obtain data from endpoints running SIP softphones) as well as denial of service attacks.
Learn more about SD-WAN and UCaaS
The result of using SD-WAN is a modern data network, optimized for cloud-based applications, and able to support the unique performance requirements of UCaaS. To learn more about SD-WAN and UCaaS, join me and Dave Greenfield, Cato’s technology evangelist, on this week’s webinar.
Legitimate websites are hacked and recruited into a spam network During a periodic analysis of Cato Cloud traffic in the Cato Research Lab, we noticed... Read ›
Anatomy of a Blackhat SEO spam campaign (with a twist) Legitimate websites are hacked and recruited into a spam network
During a periodic analysis of Cato Cloud traffic in the Cato Research Lab, we noticed that our security analytics engine was triggered by a request to a code sharing service, Pastebin. The request was originated from a preschool website in Singapore (Figure 1).
Pastebin is a popular service for code storing and sharing. A “paste” within a Pastebin account refers to a piece of code that can be dynamically fetched and placed within a specific context, for example, a web page. While the service is used for legitimate purposes, it can also be used to enable web-based, malicious activities.
[caption id="attachment_1490" align="alignnone" width="750"] Figure 1 - Website screen shot[/caption]
Analyzing the source code of the website led to a script tag, which was the source of the suspicious request. After analyzing other parts of the code, we noticed a few hidden links, which referred to shoe sales websites. Clearly, with no relation to the preschool website. (Figure 2).
[caption id="attachment_1441" align="alignleft" width="750"] Figure 2 - Suspicious code snippet[/caption]
The links are placed in a hidden part of the page overlapping one of the header, so anyone who clicks the header is unknowingly referred to one of those websites. This is a well-known technique called, “clickjacking”, which is used for various malicious purposes, such as collecting forced likes on a Facebook page.
Peaking our interest, we viewed the link in Pastebin. We can see that it contains a piece of Javascript that is executed every time a web browser hits on an infected page, downloading another Javascript code that is hosted on the attacker's server. This allows the attacker to use Pastebin, a legitimate service, as a gateway to malicious code (Figure 3). The paste had more than 500K views since it was posted and the views increased at a rate of 10K during the time of the investigation (Figure 4).
Interestingly, at this point in time the script refers to a HTML page and not Javascript code. The referred HTML contains several scripts intended to create the device fingerprint for users accessing the site. This technique is often used to support user ad-targeting, without the use of cookies that are disabled or not allowed in various regions.
[caption id="attachment_1442" align="alignnone" width="750"] Figure 3 - Malicious paste containing Javascript[/caption]
When we dug a bit more on the specific Pastebin account, we saw additional pastes that indicate the malicious intentions of this actor.
[caption id="attachment_1443" align="alignnone" width="750"] Figure 4 - More than 500K hits on this paste[/caption]
The following figure shows one of the pastes containing a PHP backdoor (Figure 5). A backdoor is a piece of code that is planted in a site and gives an attacker the ability to control the web server of the hacked site. This simple, yet effective, backdoor executes PHP code that the attacker can send using HTTP POST requests.
[caption id="attachment_1444" align="alignnone" width="750"] Figure 5 - PHP backdoor paste[/caption]
The spam network in action
We discovered thousands of infected pages, all hosted on legitimate websites, containing links to the same spam retail network of sites. Each spam page contains a script that redirects users to a retail website operated by the spammers. The redirection occurs only if the user was referred to this page from a major search engine: Google, Bing, Yahoo or AOL (Figures 6,7). This is a common blackhat SEO method used to falsely increase a page’s ranks.
The script is hosted on several subdomains inlcuding “google.jj4.co” and ”gogle.jj4.co,” and the script name also varies.
[caption id="attachment_1447" align="alignnone" width="750"] Figure 6 - the script injection[/caption]
[caption id="attachment_1448" align="alignnone" width="750"] Figure 7 - contents of injected script[/caption]
At the time of publication we could not validate if purchased goods are actually delivered. Obviously, anyone who uses such techniques to acquire traffic is not a trustworthy merchant.
How the initial site takeover occurs
A search for the C&C domain in the paste from Figure 3 led us to the script that was used to attack the sites. The script is designed to exploit cross-site-scripting (XSS) vulnerabilities in Wordpress in order to take over the site, and plant the URL references to products and shops we have seen earlier.
First, the attack scripts appends a simple PHP backdoor to one of the installed Wordpress plugins - the exact PHP code that appears in one of the attacker’s pastes. Later, the script reports the domain and path of the hacked plugin.
[caption id="attachment_1523" align="alignnone" width="975"] Figure 6 - Attack script showing C&C URL[/caption]
[caption id="attachment_1524" align="alignnone" width="975"] Figure 7 - Attack script[/caption]
Lastly, the script attempts to add a user with administrative privileges to Wordpress (Figure 8).
[caption id="attachment_1525" align="alignnone" width="1075"] Figure 8 - Attack script[/caption]
Summary
The use of Pastebin in the context of the spam network is important here, because the attacker can quickly replace the command and control (C&C) server domain in the paste, and have it impact all infected sites. This is needed when C&C servers get blacklisted and there is a need to quickly change them. Obviously, it is hard for Pastebin to detect and stop these activities. While this may be nothing more than an eCommerce scam, the same method can be used to deliver malware through exploit kits that can put end users at a much higher risk. The volume of activity around the Paste indicates hundreds of thousands of users could be impacted.
To prevent your website from being taken over by such attacks, consider regularly patching your Wordpress instances and Wordpress plugins, and limiting admin access to specific IP address, such as your corporate network external IP.
Read about top security websites