SASE Enables Consistent Security for the Modern Enterprise
|
Listen to post:
Getting your Trinity Audio player ready...
|
Corporate IT networks are rapidly changing. Evolving cloud and technological innovation have spurred digital transformation efforts. The pandemic has normalized remote and hybrid work, causing many employees to work from outside the office and creating the need to securely provide remote access to the workforce.
These changes in corporate IT infrastructure create new security challenges as companies adapt to protect new environments and to combat an evolving cyber threat landscape. In many cases, organizations are finding that their existing security architecture — which was designed to secure an IT infrastructure that is mostly or wholly on-premises — is not up to the task of meeting the security requirements and business needs of the modern, digital enterprise.
The Corporate WAN is Rapidly Changing
In the past, the majority of an organization’s IT assets were located on-prem. The company managed its own data centers, and employees were primarily connected directly to the corporate LAN. Additionally, a company’s IT assets were largely homogenous, consisting of workstations and servers that had similar, well-known security needs.
Within the last several years, the corporate network has undergone significant changes. With the introduction of cloud computing, a growing percentage of an organization’s IT assets are located outside of the traditional network perimeter on infrastructure managed by a third party. Since 89% of companies have multi-cloud deployments, companies must learn to properly operate and manage multiple vendors’ unique solutions.
The growth of remote and hybrid work models in recent years has further transformed the corporate network. In addition to moving employees and their devices off-site, remote work also impacts the range of devices used for business purposes. Mobile devices are increasingly gaining access to corporate data and systems, and bring your own device (BYOD) policies mean that company data may be accessed and stored on devices that the company does not own or fully control.
Finally, the adoption of new technologies to improve corporate productivity and efficiency has an impact. Internet of Things (IoT) devices — including both commercial and consumer systems — are connected to corporate networks. These IoT devices have unique security challenges and introduce significant risk to corporate networks.
As corporate IT environments change, so do their security needs. New environments and devices have unique security risks that must be mitigated. The solutions designed for on-prem, primarily desktop environments, may not effectively protect new infrastructure if they can be used by them at all.
Ask Me Anything: What’s the Difference Between SSE and SASE? | Watch NowLegacy Solutions Do not Fit Modern Security Needs
Many organizations have existing security architectures that are designed for a particular IT architecture. As this architecture evolves, these security solutions are often ill-suited to securing an organization’s new deployment environments and devices for various reasons, including:
- Location-Specific Protection: Often, corporate security architectures are designed to define and secure the perimeter of the corporate network against inbound threats and outbound data exfiltration. However, the growth of cloud computing, remote work, and the IoT means that this perimeter is rapidly expanding to the point where it is infeasible and pointless to secure since it includes the entire Internet.
- Limited Scalability: Appliance-based security solutions, such as network firewalls, are limited by their hardware. A computer only has so much memory and CPU, and a network interface card has a maximum throughput. Cloud scalability and the growth of corporate networks can result in security appliances being overwhelmed with more traffic than they can handle.
- Computational Requirements: Many endpoint security solutions require a certain amount of processing power or memory on the device to function. As resource-constrained devices such as mobile and IoT devices become more common, these solutions may not be usable in all areas of an organization’s IT infrastructure.
- Environment-Specific Requirements: As corporate IT environments grow more complex and diverse, different environments may have specific security considerations. For example, appliance-based network firewalls and security solutions are not a feasible option in cloud deployments since the organization lacks control over its underlying IT infrastructure.
Attempting to adapt an organization’s existing security architecture to secure its evolving environment can create disjointed security policies that are inconsistently enforced across the corporate WAN. For example, cloud-based infrastructure can be protected by cloud-focused security solutions that differ from those protecting on-prem infrastructure, which increases the complexity and overhead of security management. Remote workers and mobile devices may suffer network performance issues as traffic is backhauled for security inspection before being routed on to its destination.
The legacy security solutions that comprise traditional perimeter-focused security architectures are designed for networks that are rapidly becoming extinct. Often, these solutions adapt poorly to securing the modern, distributed corporate WAN.
Designing Security for the Modern Enterprise
As corporate networks become more distributed, security must follow suit. Effectively protecting the modern corporate WAN requires security solutions that can provide consistent protection and security policy enforcement throughout the corporate network.
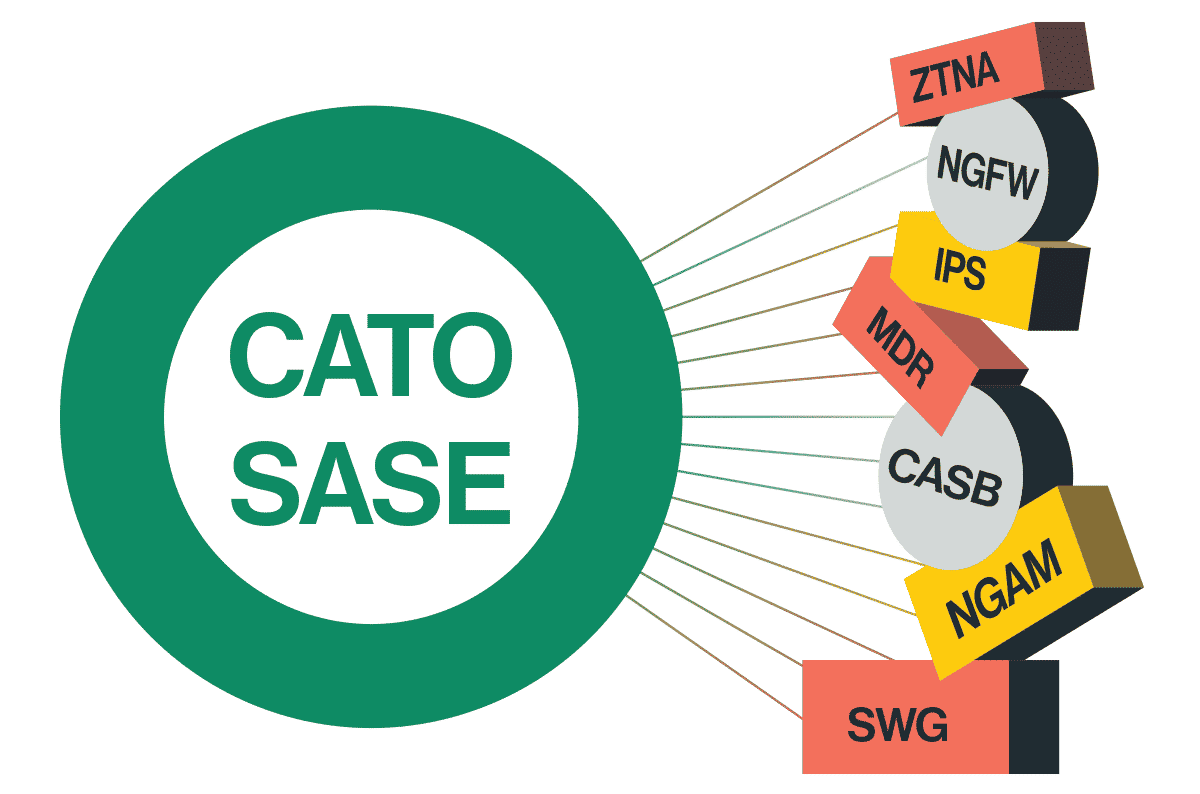
Secure Access Service Edge (SASE) is designed for the distributed enterprise and addresses the common shortcomings of legacy security solutions. SASE is implemented using a network of cloud-based points of presence (PoPs) that can be deployed geographically near an organization’s scattered IT assets and can take advantage of cloud scalability to meet evolving business needs. SASE solutions also incorporate a full security stack — including solutions designed for cloud infrastructure and remote users — enabling traffic to be inspected by any PoP before being optimally routed to its destination.
Cato provides the world’s most robust single-vendor SASE platform, converging Cato SD-WAN and a cloud-native security service edge, Cato SSE 360, including ZTNA, SWG, CASB/DLP, and FWaaS into a global cloud service. With over 75 PoPs worldwide, Cato optimizes and secures application access for all users and locations, and is easily managed from a single pane of glass. To learn more about Cato SASE Cloud and how it can help your organization’s security architecture keep up with the evolution of your network infrastructure, sign up for a demo today.