Beyond Access: How Cato Measures and Manages User Risk in Real Time
|
Listen to post:
Getting your Trinity Audio player ready...
|
On a quiet Tuesday morning, Jerry, a fictional system administrator, logged in as usual. While testing a new integration script, he visited a documentation page on an unfamiliar domain. It looked harmless and loaded without issue, but behind the scenes, Jerry’s laptop began making a series of small outbound requests to several low-reputation domains. None of these connections were malicious enough to be blocked, yet the pattern resembled early-stage domain-flux activity.
Across the building, Stacy from Procurement, also part of this example scenario, received a vendor update request that appeared to come from a trusted partner. She opened the attached spreadsheet and continued her day. The file behaved normally, but it quietly attempted to send metadata about her system to an unfamiliar storage endpoint, aligning with indicators such as “Data Transfer to Suspicious Destinations” and “Information Stealers.”
Neither Jerry nor Stacy had malicious intent. They were simply doing their jobs, but their actions, one subtle and one deceptive, elevated their risk profiles in ways that traditional security tools would not have recognized. These fictional examples reflect real-world behaviors that often go unnoticed.
Cato’s User Risk Score identifies these seemingly harmless moments as potential risks and feeds them into the User Risk Level, which is a vital tool for network and security teams for maintaining an always current security posture. It enables zero-trust, dynamic access control policies for both internal applications and internet traffic, providing clear visibility into user risk posture so you can continuously tune policies and adapt your security strategy as threats and user behavior evolve.
How User Risk Score Works
Cato continuously monitors all user activity across its global SASE platform. Each ZTNA client user is dynamically assigned a User Risk Level through a proprietary algorithm that evaluates a wide range of behavioral and security indicators. The system analyzes both threat activity and contextual attributes to reflect each user’s current risk posture in real time.
Cato’s scoring model considers factors such as:
- Malware and Trojan activity including banking malware, information stealers, and backdoors
- Botnet and command-and-control traffic such as beaconing or DNS tunneling behavior
- Ransomware and cryptomining patterns like encryption attempts, ransom note delivery, or abnormal system usage
- Data exfiltration and credential theft through suspicious uploads, phishing, or brand impersonation
- Exploitation and web attack attempts including CVE exploitation, injection attacks, and cross-site scripting
- Scanning and reconnaissance activity from automated tools or targeted vulnerability probes
- Contextual user attributes such as group membership, platform, country, and connection origin
All these data points are correlated into a single Risk Level that evolves dynamically as new activity is observed. Security teams can use this level directly within Internet or WAN policies to automatically restrict or monitor access for users who present higher risk.
Understanding the Why Behind the Score and Acting on It
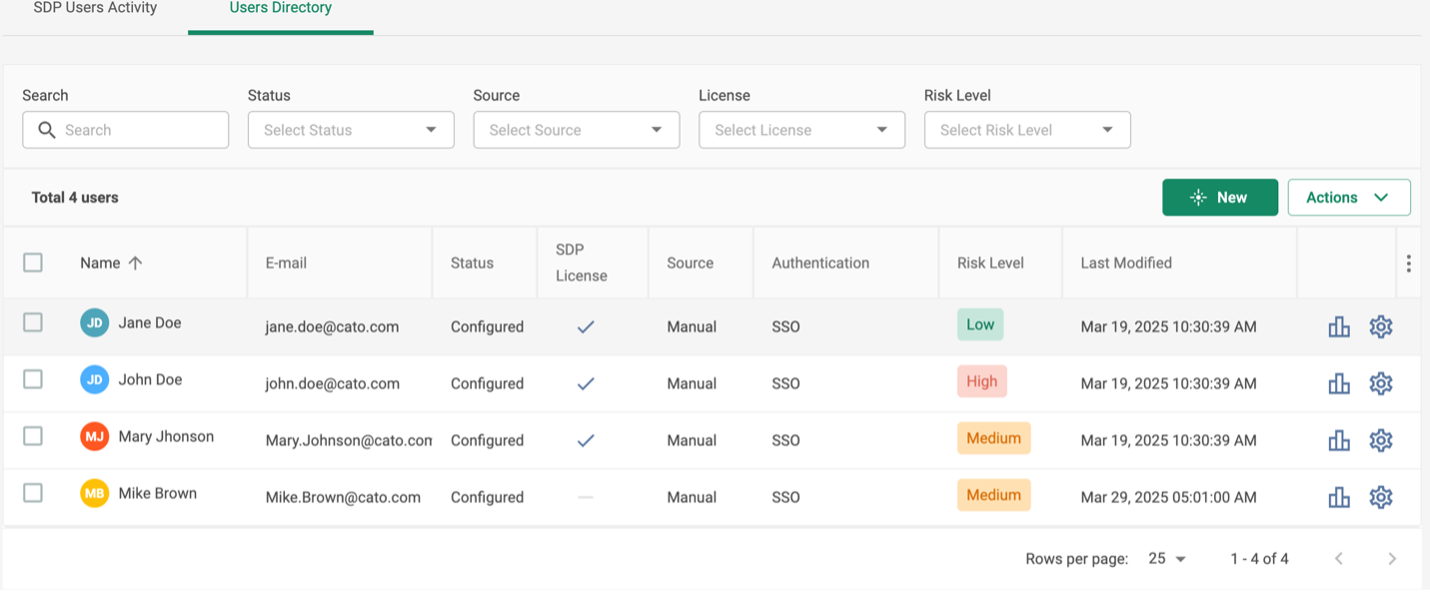
When a user’s score increases, the User Risk Dashboard presents any existing XDR stories related to that user. These stories summarize recent detections such as a blocked malicious website, an attempt to install an unauthorized application, or abnormal data movement. Figure 1 shows how each user is assigned a risk level, and Figure 2 shows the dashboard view you can drill into for deeper investigation.
From the User Risk Dashboard, teams can quickly pivot from “who is risky” to “what happened and why.” The dashboard highlights the user’s group membership, a timeline of the user’s risk level and how it changed over time, and a breakdown of contributing signals by security components such as Anti-Malware, IPS, Firewall, and Suspicious Activity. It also surfaces the top risk-driving threats and events for each component, including MITRE ATT&CK tactics where relevant, and provides administrative actions to reset or revoke the user’s risk level when appropriate.
Figure 1. Viewing user risk levels
Figure 2. User Risk Score Dashboard
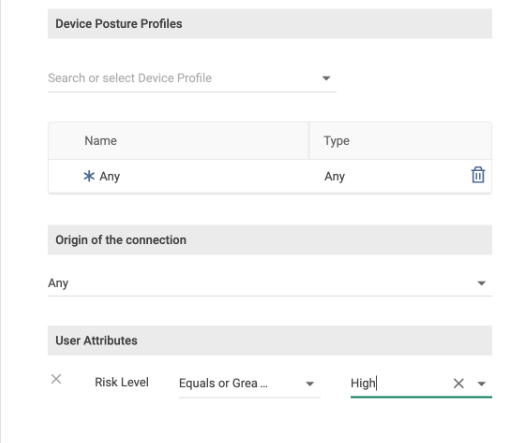
Administrators can reference the User Risk Level directly within Internet and WAN policies to manage access according to user posture. (Figure 3) This makes it possible to automatically apply tighter restrictions or additional validation for higher-risk users, while maintaining a seamless experience for those at lower risk.
The User Risk Level can also be shared with external security systems, such as SIEM or SOAR platforms, through Cato’s event export and integration capabilities. This allows organizations to correlate user risk insights with data from identity providers, endpoint protection, or incident response systems, creating a unified and contextual security view across the enterprise.
Figure 3. Configuring risk-based policy actions to enforce zero-trust dynamically.
Compliance, Framework Alignment, and Security Outcomes
Cato’s User Risk Score helps organizations achieve both operational security and regulatory alignment. It supports modern cybersecurity mandates that emphasize continuous monitoring, behavioral analysis, and dynamic risk management, which are key principles in today’s compliance ecosystem.
- Under the NIS2 Directive, organizations must implement “appropriate and proportionate measures to manage risks to network and information systems.” Continuous user risk scoring directly fulfills this expectation by identifying behavioral anomalies and surfacing them before they escalate.
- Similarly, NIST SP 800-53 Rev 5 (AU-6) instructs teams to “review and analyze system audit records for indications of inappropriate or unusual activity and adjust monitoring when there is a change in risk.” Cato’s automated correlation and scoring system brings this control to life without manual effort.
By integrating these frameworks into daily operations, organizations can:
- Strengthen Zero Trust enforcement with adaptive, user-centric visibility
- Shorten detection and response times for compromised accounts
- Demonstrate compliance readiness during audits
- Maintain clear, auditable trails of user activity and remediation actions
The outcome is a measurable reduction in exposure, faster incident response, and greater assurance that compliance and operational security evolve together.
Conclusion: Seeing and Stopping Risk in Real Time
Cato’s User Risk Score enables security teams to move beyond static access control and truly understand how users behave.
By combining real-time scoring, contextual XDR visibility, and automated policy actions, Cato transforms ZTNA into an adaptive, user-aware defense that continuously measures, manages, and mitigates risk across the enterprise.
In cybersecurity, seeing how users behave is the first step to keeping them, and the business, secure.