When Quantum Turns Encryption Into a Time Problem
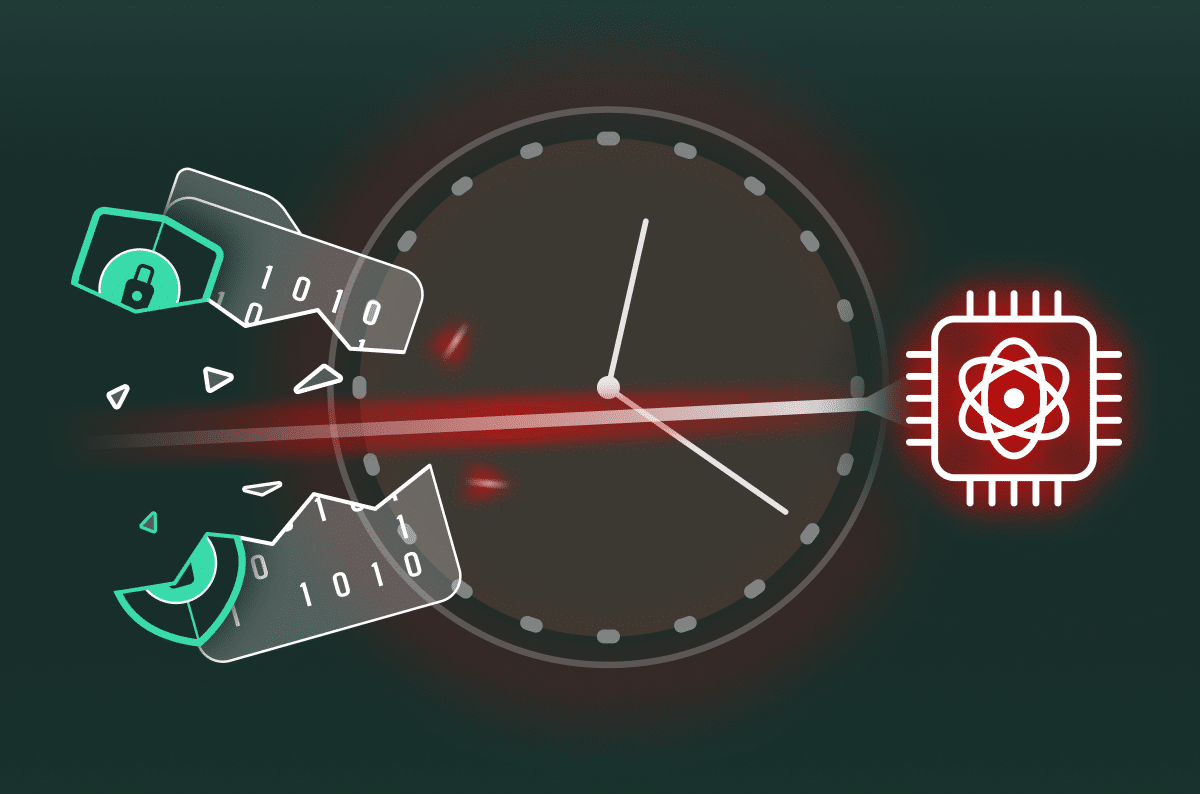
Table of Contents
- 1. The two layers that matter: underlay and overlay
- 2. A simple way to think about PQC
- 3. Why leaders care: data outlives the connection
- 4. Why now: guidance has turned into timelines
- 5. What is actually at risk, without the math
- 6. The role of secure access platforms
- 7. What good readiness looks
- 8. Cato on PQC: planning, not Panic
|
Listen to post:
Getting your Trinity Audio player ready...
|
If your encrypted traffic was captured today, would it still be private in ten years?
That question changes the conversation.
Leaders are used to asking, “Is it encrypted?”
Now they are asking, “How long does it stay confidential?”
That is where post quantum cryptography, or PQC, comes in. Its role is to strengthen the foundations of a secure connection by improving how trust is established before any data is exchanged.
Today’s encryption still works. The concern is whether the trust methods behind it will hold up as quantum computing advances, and how you prove that they will.
The two layers that matter: underlay and overlay
PQC becomes practical when you view it in two layers.
The underlay is the encrypted tunnels carrying traffic between users, sites, clouds, and services. This is where trust is established at scale. If those trust methods are not ready for what comes next, secure access is not ready either.
The overlay is the proof layer: logs, controls, reporting, and evidence. This is how you show what is protected, what is not yet, and where progress is being made.
That is where “harvest now, decrypt later” becomes useful. The underlay reduces the long term risk. The overlay proves you are reducing it.
A simple way to think about PQC
Think about facial recognition. Your phone scans your face and decides it is really you.
Now imagine fake facial scans become so convincing that the old checks start to fail. The phone did not change. Your face did not change. What changed is what an attacker can produce.
Encryption has a similar trust step. PQC upgrades that step, so it still holds as attacker tools get stronger.
Why leaders care: data outlives the connection
Most organizations treat encryption as a control for data in motion. That only works if the trust methods behind it stay reliable for as long as the data still matters.
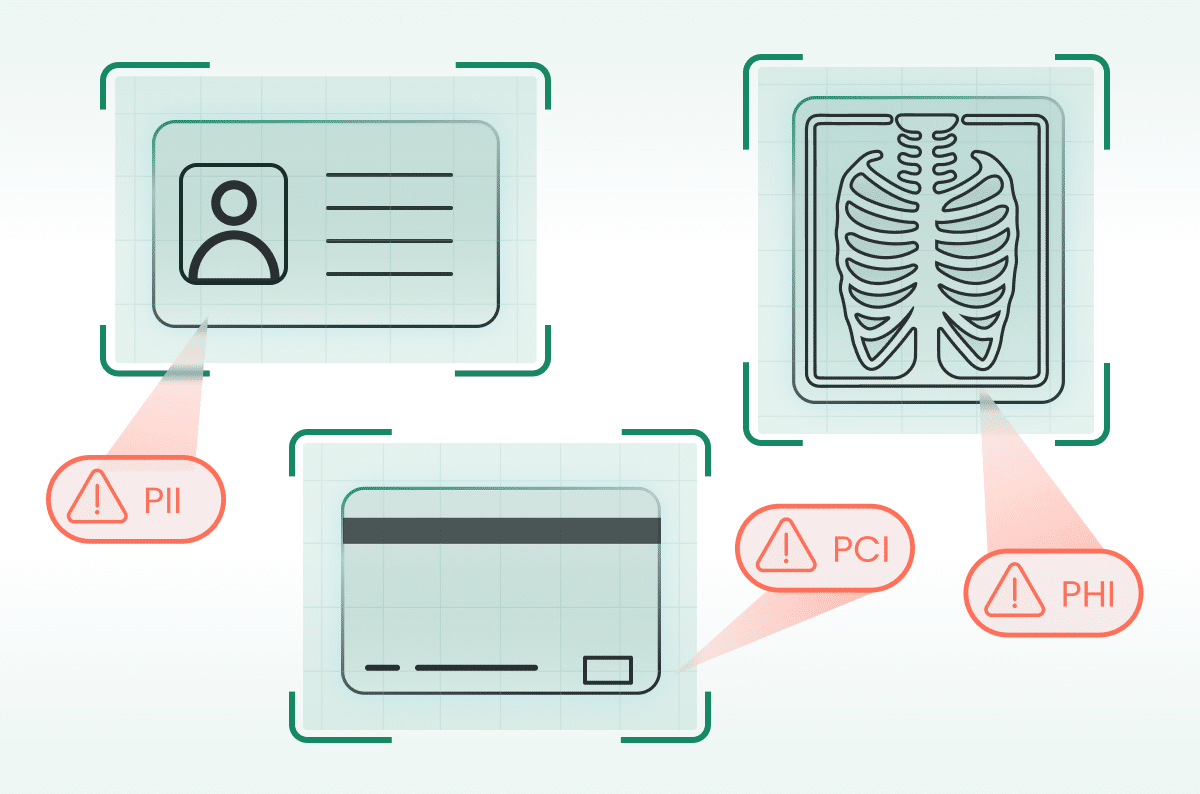
This becomes a leadership issue because a secure session may last seconds, but the data inside it contains can stay remain sensitive for years. Customer and employee records, identity trails, legal and financial material, product plans, source code, and internal strategy all retain value long after the connection ends.
That is why regulators, auditors, customers, and boards will increasingly expect a clear answer and proof.
Why now: guidance has turned into timelines
PQC is no longer a research topic. It is a planning topic because governments and standards bodies have now set a clear direction. That is why it is already showing up in audits RFPs.
What the public guidance is signaling:
- OMB (U.S.): – The U.S. Office of Management and Budget instructs agencies to begin their post‑quantum journey by inventorying all cryptographic systems and then preparing a funding plan to migrate them to quantum‑safe algorithms.
- NCSC (UK): The UK’s National Cyber Security Centre advises organizations to follow a multi‑year roadmap: spend a few years discovering and assessing systems and creating a migration strategy, then carry out early migrations and refine the plan before completing the shift by 2035.
- EU Commission: The European Commission urges Member States to start transitioning to post‑quantum cryptography by the end of 2026 and move critical infrastructure “as soon as possible, no later than 2030,” emphasizing the need to act now.
NIST (U.S.): NIST recommends that organizations begin applying the new post‑quantum standards immediately, identify where vulnerable algorithms are used and plan to replace them, because quantum‑vulnerable algorithms will be deprecated by 2035.
The message is simple: the expectation is not immediate completion, but a clear plan, defined ownership, and measurable progress.
What is actually at risk, without the math
Encrypted traffic has two stages. First, systems establish trust and agree with the encryption that will protect the session. Then the session begins, and data moves under that protection.
PQC focuses on the first stage. If trust at the start of the connection becomes weaker over time, traffic captured today could be exposed later.
That is why PQC is not just a device update. It affects the systems and platforms responsible for creating and managing secure sessions.
The role of secure access platforms
Secure access platforms sit where encrypted sessions are created, inspected, and re-established. That puts them in the right place to handle PQC in a measurable way: they can strengthen the connection layer and show proof from real traffic.
In most buying cycles, the conversation collapses into three questions:
- What is protected today?
- What is not protected yet?
- How do we prove it using real traffic, not slides?
If a vendor cannot answer these questions, buyer confidence drops.
What good readiness looks
A practical model for good PQC readiness is:
- Standards-led: aligned to public guidance and widely reviewed algorithms.
- Phased: start with the highest value flows, expand as compatibility allows.
- Measurable: evidence visible in real sessions and reporting, over time.
A simple leadership test is this: can we explain our current state, the next milestone, and how we will prove progress? If yes, the program is moving in the right direction.
Cato on PQC: planning, not Panic
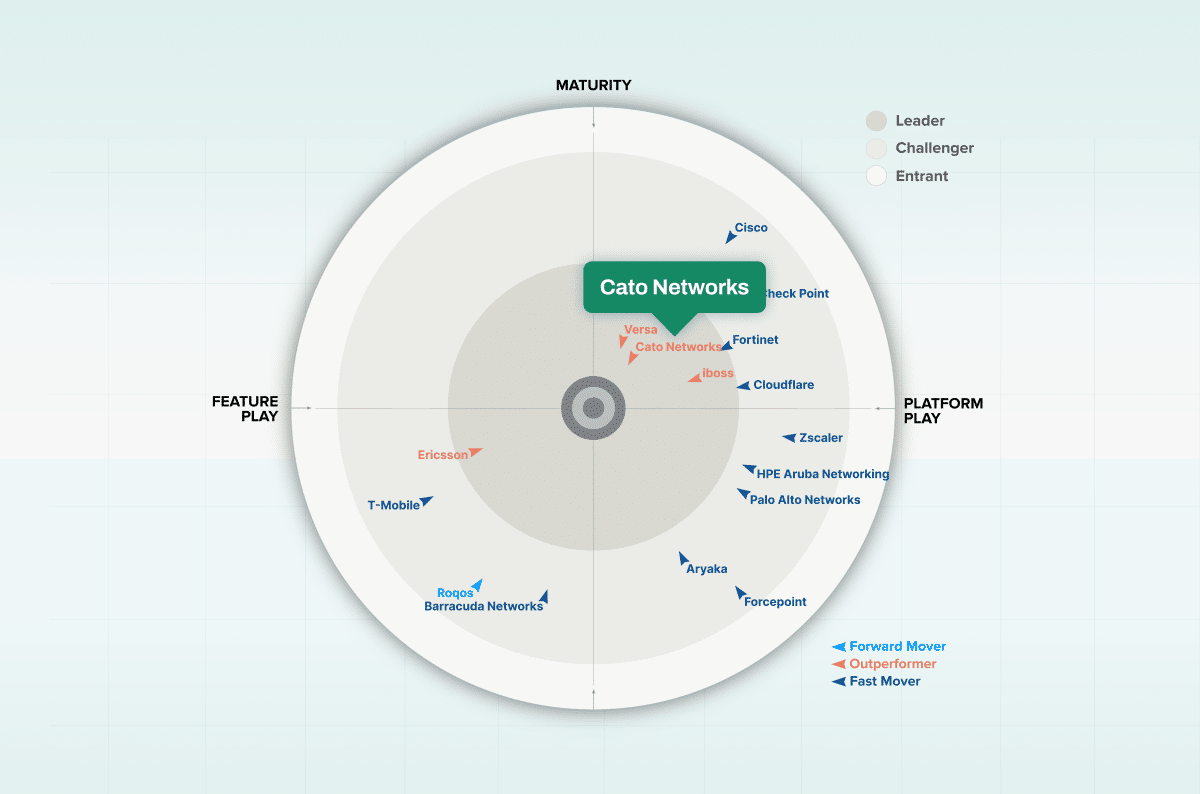
Cato is approaching PQC as a platform transition designed to strengthen the cryptographic foundations of secure access without pushing redesign complexity onto customers. The focus starts where protected connections are established, then extends into the visibility organizations need to track progress and report clearly.
PQC is a planning topic, not a panic topic. It will become increasingly visible in audits, procurement, and risk conversations. The important question is whether the platform you choose makes that transition easier to manage or harder to control. As a leading SASE provider, Cato will continue to share practical guidance and relevant insight as organizations prepare for this shift.