Threat Intelligence Feeds and Endpoint Protection Systems Fail to Detect 24 Malicious Chrome Extensions
Table of Contents
- 1. Browsers: Today's Security Frontier
- 2. How Malicious Chrome Extensions Make Their Way Into Your Browser
- 3. Endpoint Protection and Threat Intelligence Research Alone Do Not Detect Malicious Chrome Extensions
- 4. Network-Based Discovery Is Critical for Spotting Malicious Extensions
- 5. Fake Postman Extension Leads to Credential Theft
- 6. Recommendations for Organizations
- 7. Conclusions
- 8. IoCs
|
Listen to post:
Getting your Trinity Audio player ready...
|
Network data from hundreds of Cato customers suggests malware communication persists despite the use of legacy security controls, services, and detection methods
Cato Research Labs released new findings today identifying 24 malicious Chrome extensions and 40 malicious domains, all previously thought to be benign. Some extensions simply introduced adware, but others stole user credentials and may allow attackers to exfiltrate data or manipulate search results to lure users into downloading malware. None of the extensions or the domains had been reported as malicious by endpoint protection systems (EPPs) or threat intelligence (TI).
The fact these malicious extensions and domains went undetected underscores the limitations of legacy protection systems. Attackers can employ a wide range of techniques to avoid detection by EPPs and TI. As such, enterprises cannot assume updated defenses will protect them. Putting into place the security measures to detect the C&C server communications of a malicious Chrome extension, or any malware for that matter, will fill this gap.
Browsers: Today’s Security Frontier
Everyone uses browsers, and it’s this popularity that makes them particularly enticing targets for adversaries. Browser extensions provide fertile ground for attackers to access resources on client computers, often with the same permissions as the browser itself.
Many researchers consider malicious extensions as simply PuPs (Potentially unwanted Programs) or Adware, but malicious extensions can be far riskier than just showing ads. From manipulating search results to luring users to download malware to exfiltrating clipboard data or screenshots, malicious Chrome extensions pose a huge and growing risk for every enterprise. We saw this last fall with the Razy malware outbreak that also involved a Chrome extension.
How Malicious Chrome Extensions Make Their Way Into Your Browser
Google does a good job identifying and blocking malicious Chrome extensions. The process of uploading a new extension to Google’s Chrome Web Store typically takes several weeks while the extension code and activity are reviewed automatically and manually by Google. Using the Chrome browser’s standard security settings will block the installation of extensions from outside Google’s Chrome Web Store. However, users can change this setting in the browser configuration.
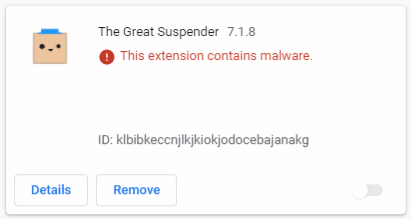
Google also reviews abuse notifications from users and removes extensions identified as malicious from the Chrome Web Store. In those cases, the Chrome browser will mark the extension as malware; users are expected to remove the extension.
Endpoint Protection and Threat Intelligence Research Alone Do Not Detect Malicious Chrome Extensions
With those security controls in place and companies already investing heavily in endpoint protection, you might think that users would be safe from malicious extensions. However, our research shows this is not the case.
Overall, we discovered 85 malicious Chrome extensions on our customer networks. Some had never appeared in the Google Chrome Web Store, while others had been removed by Google. Nevertheless, they were still found operating on customer networks.
How can users continue to run malicious extensions despite the many security controls? During our research, we identified four approaches attackers use to introduce malicious extensions into user browsers:
- Browser Configuration and Third-Party Sites: Some extensions enter browsers due to poor browser configuration and downloading CRX (Chrome extension installation file) from malicious sites, i.e., not Google’s official web store. One malicious site we identified that distributes malicious CRXs is https://extore[.]space/inspire. Some of the extensions are real and benign, while others might be fake with malicious code.
- Malicious Code Injection During Update: In other cases, Google might have approved the extensions, but attackers later injected malicious code in one of the extension’s updates after the extension becomes popular.
- Extension Rights Acquisition: Other ways are by adversaries purchasing a popular extension’s rights from the developer and then injecting malicious code. Taking over the key (which generates the extension ID) and credentials from the developer might also be a way to get plugged into a popular extension.
- Independent Code Downloads: We’ve also identified other Malwares/PUPs or malicious extensions that would download and install additional (other) malicious extensions.
Network-Based Discovery Is Critical for Spotting Malicious Extensions
Cato made these discoveries by analyzing five days of data from hundreds of Cato customers’ networks. Rather than hunting for specific malware signatures, Cato uses a network-based approach that identifies the network traffic patterns indicative of all malware. As such, this methodology is not only useful for identifying these specific extensions but for continuously hunting for any malware communicating with a C&C server.
The research had two phases. First, we automatically correlated network traffic with extension behavior and then preliminarily classified extensions as malicious or benign. The result: 97 of 551 unique extensions from our data were identified as likely being malicious. The second phase was to manually inspect each extension, definitively classifying them as malicious or benign. The final result was 85 malicious extensions, representing an 87% success rate for our initial automated phase.
We achieved this remarkably successful approach by analyzing and correlating networking and security information across multiple dimensions, including looking for:
- Traffic to Parked or Malicious Domains. Identifying traffic generated by extensions to parked domains or malicious domains typically yielded known malicious extensions. What’s more, by checking the network behavior and other traffic data, such as the URL and other HTTP parameters, we were able to identify other malicious extensions that were using the same behavior and communicating with domains previously not classified as malicious.
- Identical Extensions Communicating with Different Domains: Attackers have identical extensions (as defined by their unique extension ID) communicating with many different domains. They’ll target a particular area (creating PDFs was particularly popular), labeling each extension differently and having them communicate with a different domain, mimicking a benign extension’s behavior. Using the same approach, we analyzed different extensions that communicate to the same domain. This behavior was suspicious, and after analyzing the specific extensions, they were identified as malicious.
- Unencrypted Extension IDs: Having the extension ID in clear-text or encoded to base64 in the URL, headers or payload is also suspicious. It may be evidence of the adversaries trying to understand the traffic origin (as sometimes they share the same domain across many extensions). It might also be used as an access-control function on the server-side to allow traffic only from the extension and not from security researchers or automatic web-classification algorithms trying to investigate and classify the domain.
Fake Postman Extension Leads to Credential Theft
While our approach identified many extensions that were believed to be benign, of particular note was one extension that disguised itself as the popular Postman application.
Postman allows developers to test and use APIs, typically using their credentials in the process. The fake Postman extension enables attackers to exploit those credentials to access the company’s application. To make matters worse, the malicious extension closely mimics the real Postman extension, even using the same icon and offering the same capabilities.
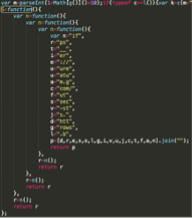
We validated that the extension was malicious by analyzing the extension’s code. Some of the code (JavaScript) was obfuscated, hiding its C&C targets, a common trick used by attackers.
Recommendations for Organizations
Cato recommends taking several actions to protect your users from these and other malicious extensions:
- Define and maintain a whitelist policy of extensions ID allowed in your organization. Ensure whitelisted extensions are from Google’s Chrome Web Store only.
- Assess the permissions granted by the extension. Permissions to use cookies, manipulate network traffic or access all tabs and sites require more in-depth investigation.
- Monitor for browsers with poor security settings (lower than “Standard”).
- Monitor network traffic to identify periodic communication with C&C servers.
Conclusions
Despite their investment in EPP and TI, enterprises continue to be infected by malicious Chrome extensions. Attackers introduce the extensions through a range of techniques bypassing legacy protection approaches. However, rather than hunting for a specific malicious extension, enterprises can best protect themselves by identifying the unique network patterns indicative of all malware.
IoCs
Extension ID:
djdcfiocijfjponepmbbdmbeblofhfff (Fake Postman)
mfdcjdgkcepgfcfgbadbekokbnlifbko (Fake Postman)
dfehheanbnmfndkffgmdaeindpjnicpi
mgkmlkgpnffmhhfallpoknfmmkdkfejp (QuickNewsWorld Promos)
ijbcfkkcifjgnikfcmbdfbddcgjdmgga
lamaflkhfcmnjcfkcolgmmlpajfholja
iogkcdbmgbhoelodlobknifhlkljiepm
flhahaabnnkoccijodlhobjfchcchgjd
loiloamappomjnanlieaipcmlpmmolkg
pdlfbopkggkgdmgkejgjgnbdbmfcnfjn (EZPackageTracking Promos)
epcdjnnpcbidnlehlklebmdijbjleefc
lepjcehmlpfdgholbejebidnnkkannpl (DOCtoPDF)
njmjfnbhppmkpbbcfloagfmfokbokjgo (pdfconverterds)
ljnppgaebjnbbahgmjajfbcoabdpopfb (Search Manager)
llfdfhfdkdpkphlddncfjmajiciboanf
pdfakgkkbagclonnhakillpkhoalfeef
ndhhhgoicnabjcgnamebnbdgkpobbljm
cpdngajmgfolfjhnccalanfegdiebmbm (PBlock+)
ciiobgcookficfhfccnjfcdmhekiadje (ViewPDF)
nofdiclilfkicekdajkiaieafeciemlh (Your Docs To PDF)
fichcldcnidefpllcpcpmnjipcdafjjl (pdfconverterds)
cflijgpldfbmdijnkeoadcjpfgokoeck (pdfconverterds)
fkacpajnbmglejpdaaeafjafjeleacnj (pdfconverterds)
hadebekepjnjbcmpiphpecnibbfgonni (ViewPDF)
Domains:
gojoroh[.]com
bekprty[.]com
bkpqdm[.]com
yetwp[.]com
qalus[.]com
mucac[.]com
sanaju[.]com
exploremethod[.]com
pupahaqo[.]com
ruboja[.]com
jurokotu[.]com
kuqotaj[.]com
lufacam[.]com
wunab[.]com
qojonoko[.]com
bunafo[.]com
bunupoj[.]com
cajato[.]com
cusupuh[.]com
kohaguk[.]com
naqodur[.]com
pocakaqu[.]com
qunadap[.]com
qurajoca[.]com
qusonujo[.]com
womohu[.]com
wuqah[.]com
dagaju[.]com
kogarowa[.]com
qufobuh[.]com
bosojojo[.]com
dubocoso[.]com
fupoj[.]com
jagufu[.]com
nopuwa[.]com
qotun[.]com
tafasajo[.]com
tudoq[.]com
kuratar[.]com
secure.browser-status[.]com