When the Middle East Went Remote: A Case Study in Coping with the Unexpected

|
Listen to post:
Getting your Trinity Audio player ready...
|
Instability linked to the Iran conflict has pushed many organizations across the Middle East to activate continuity plans. In practice, one of the fastest and most common actions was a regional move to work from home.
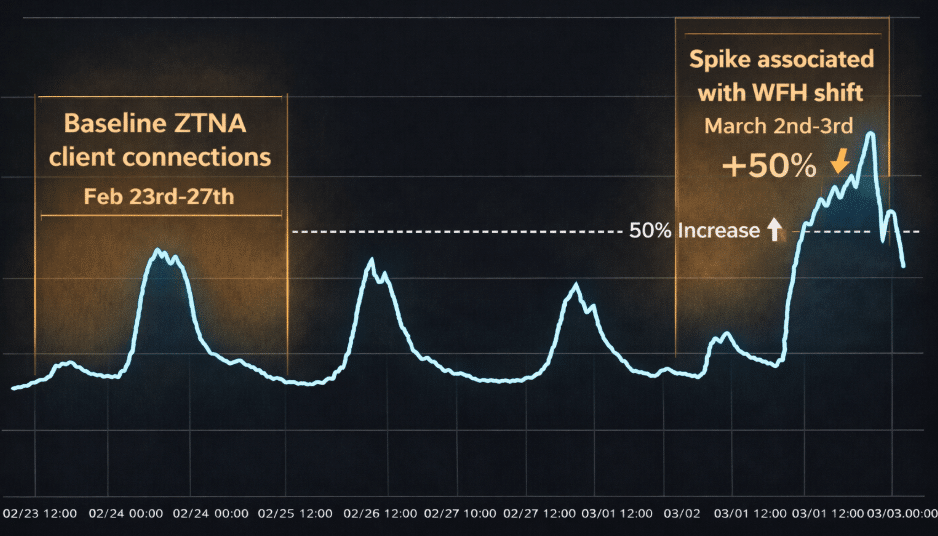
At Cato, we observe these shifts quickly because our global cloud backbone sits on the path of customer connectivity. In this post, we share what we saw across the region using the UAE as an example: a sudden traffic shift, including an approximately 50 percent spike starting on March 2 at our Dubai PoP.
Dubai case study: remote access spiked
The significant increase came through remote connections. The traffic spike came from a significant increase in ZTNA connections. Cato Universal ZTNA (UZTNA) connects internal and external users to applications using a least-trust approach that combines identity and policy. A rapid increase like this is a strong indicator that many users who typically work from offices switched to home networks in a short window.
Figure 1 illustrates the shift from the baseline (Feb 23–27) to the spike starting on March 2.
Figure 1. Baseline ZTNA connections during Feb 23–27, then spiked on March 2–3
What this means to Cato SASE customers
The sudden shift to remote work can present legacy, product-based architectures with performance, security, and resilience challenges, which the Cato SASE Platform addresses.
Continuity without VPN bottlenecks
When a workforce flips to remote, legacy designs often create urgent work for IT. VPN concentrators hit concurrency limits, licenses run short, and teams rush changes under pressure Beyond capacity, a sudden WFH shift often forces changes across the stack, including security enforcement points, application access paths, and how traffic is routed and inspected.
- Security infrastructure: shifting inspection and enforcement from the office perimeter to users and devices at home.
- Application access: revalidating who can reach which internal apps, from where, and under what conditions.
- Traffic paths: avoiding hairpinning through a datacenter and keeping routes efficient for SaaS and internet access.
- Policy consistency: preventing “temporary” access expansions that turn into long-term risk.
The Cato SASE Platform includes secure remote access. When remote connectivity demand rises sharply, users still connect to the nearest PoP, and security policies continue to apply without IT needing to scale appliances, redesign routing, or introduce risky emergency workarounds. Cato helps IT validate that remote access is healthy and quickly isolate whether disruptions are network-related or identity-related.
Consistent security for office users and home users
Work from Home (WFH) policies increase exposure. Home networks are less controlled; devices roam, and breaking news periods often correlate with spikes in phishing and credential abuse. During regional instability, IT organizations need to verify that:
- Least privilege access to key apps remains intact
- Threat detections are not rising unchecked
- High-risk app categories are not becoming common paths for users
SASE matters here because policy follows identity and context, not location. Remote users can get the same controls they have in the office, including consistent access rules and inspection, so IT organizations are not forced into a weaker security posture just to stay operational.
Performance under uncertainty
A WFH shift not only results in more remote access traffic. It also changes traffic patterns, increasing SaaS usage and amplifying dependency on last-mile conditions and ISP routing. When usage shifts, IT organization to monitor:
- SaaS and collaboration experience for remote users remains responsive and consistent
- Latency and packet loss changes by region or ISP are within norms
- No single app or category becomes a bottleneck.
Cato’s distributed architecture and PoP-based enforcement help absorb spikes and support continuity as usage shifts quickly. The practical outcome is stable access to business-critical applications even when the region is under stress, and the user’s location becomes highly variable.
Remote work without security redesign
A sudden shift to remote work can disrupt enterprise operations. It’s not simply a matter of connecting users from home instead of the office. There are additional architectural, security, and performance implications that IT must address. These pose major problems for legacy, product-based approaches that treat these domains separately.
Cloud-native platforms that treat remote users the same as office users eliminate these complexities. A consistent set of security and access policies follows users wherever they work. The result is fewer urgent changes during disruptions and a more stable, consistent security posture as users move between locations.