Zero Trust for the East/West Battleground
|
Listen to post:
Getting your Trinity Audio player ready...
|
Most major breaches do not spiral out of control because attackers get in. They spiral because attackers are free to move once they are inside.
After gaining an initial foothold through compromised credentials, a misconfigured cloud workload, a remote device, or a third-party connection, sophisticated attackers pivot. They scan the network, escalate privileges, and move laterally across the LAN and datacenter until they reach critical systems. Without segmentation and inspection of east–west traffic, one compromised device can quickly become an enterprise-wide incident.
Most of the highest-profile, memorable breaches underscore this consistent pattern:
- In 2019, Capital One attackers moved from an exposed cloud workload to sensitive data due to weak internal segmentation.
- In 2020, SolarWinds attackers leveraged trusted internal access to move laterally across poorly segmented environments.
- In 2021, Colonial Pipeline shut down operations after compromised credentials enabled internal access to critical systems.
- More recently, MGM Resorts suffered a major disruption after attackers gained entry and spread across internal networks.
In each case, the breach became high profile not simply because attackers entered the network, but because they could move freely within it.
Today’s enterprise environments make this risk even greater. Remote and hybrid users connect from unmanaged networks. Contractors and third parties often have broad access. Guest Wi-Fi, IoT devices, and cloud workloads expand the attack surface. Mergers and acquisitions introduce entirely new networks with unknown vulnerabilities. The perimeter is no longer the primary risk. The internal network is.
This is why east–west security must be foundational.
Securing the Internal Network by Design
Cato was built to secure traffic everywhere, including lateral movement inside production LANs, datacenters, cloud environments, and IoT/OT networks. Segmentation is enforced using identity-aware, application-aware policies that are consistent across the entire environment. In addition to VLANs and physical segmentation, Cato creates logical boundaries between users, devices, workloads, and operational systems.
If a remote user’s laptop is compromised, it cannot pivot into sensitive server segments. If a contractor device is infected, it cannot scan the internal LAN. If a cloud workload is exploited, it cannot laterally access databases without inspection and policy enforcement. Every segment becomes a controlled boundary rather than an open pathway.
Segmentation alone is not enough, however; traffic between segments must also be inspected.
Cato applies full IPS inspection to east–west traffic using over 200 threat intelligence feeds, AI and machine learning models, and a laundry list of inspection engines and IoCs (Indicators of Compromise). Internal protocols such as SMB, RDP, DNS, and application traffic are continuously inspected just as rigorously as Internet traffic. The system does not assume internal traffic is safe; it verifies it.
The most damaging modern attackers rarely move aggressively. They probe quietly, escalate privileges slowly, and pivot over time. Cato’s Dynamic Prevention capability monitors behavioral patterns across hosts and segments, correlating suspicious activity that may appear benign in isolation. By analyzing conditions over time, Cato detects sophisticated low-and-slow attacks and can automatically enforce restrictions when risk thresholds are reached. This stops lateral movement before malware spreads or sensitive data is accessed.
All inspection is powered by Cato’s Single Pass Cloud Engine (SPACE), a cloud-native inspection architecture that operates inline at scale. Because SPACE is centrally managed and continuously updated, organizations do not need to deploy and maintain internal hardware appliances. Threat intelligence, signatures, and prevention logic are updated automatically across the global cloud platform, ensuring protection evolves as threats evolve.
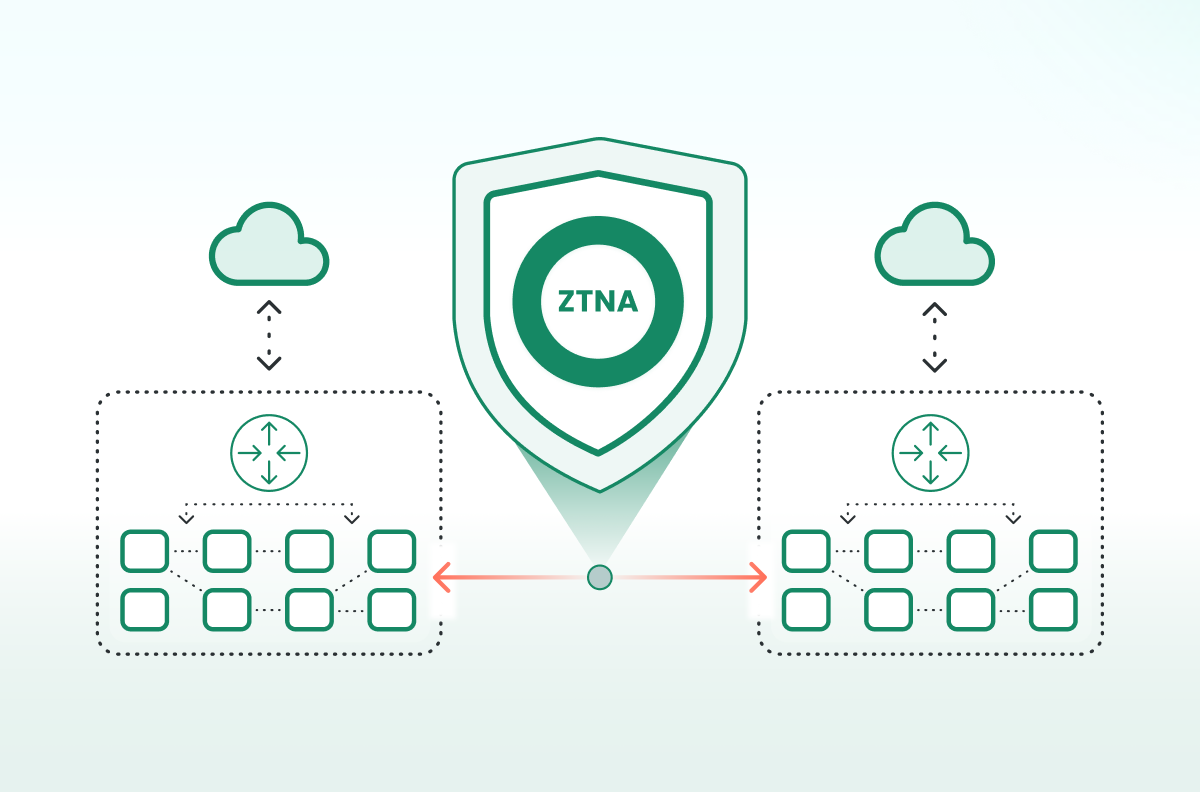
Centralized Policy, Enforced Everywhere
Effective segmentation and inspection require consistent policy enforcement. Cato delivers centralized cloud management through a single management application where security teams define segmentation and inspection policies once and enforce them across branches, datacenters, cloud workloads, remote users, and IoT/OT environments.
This eliminates policy drift between regions, inconsistent or multi-vendor firewall configurations, and forgotten datacenter rules. Security teams gain unified visibility and control across the entire enterprise, with policies applied immediately and uniformly.
M&A: The Hidden East–West Risk Multiplier
Mergers and acquisitions present one of the highest-risk moments in enterprise security. Newly integrated networks often include flat architectures, outdated systems, unvetted contractor access, and unknown vulnerabilities. Without strong segmentation and inspection, integrating these environments can expose the entire organization.
Cato instantaneously extends the umbrella of protection to these new risks. New sites can be connected through zero-touch deployment, and corporate segmentation policies are applied immediately through centralized cloud management. All east–west and north–south traffic is inspected from day one. Protection does not wait for a lengthy network redesign and device configuration, it’s enforced instantly, dramatically reducing post-acquisition risk.
Contain the Breach Before It Spreads
The most dangerous attackers attempt to not just gain access, but also to move laterally to find the most valuable data. Organizations that rely only on perimeter defenses effectively grant them that freedom.
Cato removes that freedom. With identity-aware segmentation, full IPS inspection of east–west traffic, AI-driven dynamic prevention, and centralized cloud policy enforcement, Cato limits lateral movement across production LANs, datacenters, cloud environments, IoT/OT systems, and M&A additions.
The question is no longer whether attackers will get in. The question is whether they can move once they do. Cato ensures that they cannot. Organizations can register here to see how Cato secures east–west traffic across LAN, datacenter, cloud, and IoT environments, and avoid becoming the next high-profile breach in the headlines.