Cato Agentic AI Security
Cato secures agentic AI across how enterprises use, build, and connect AI systems. Prevent data loss, abuse, and unauthorized agentic behavior with visibility, data protection, and runtime control over agentic activity, tool calls, and MCP interactions.
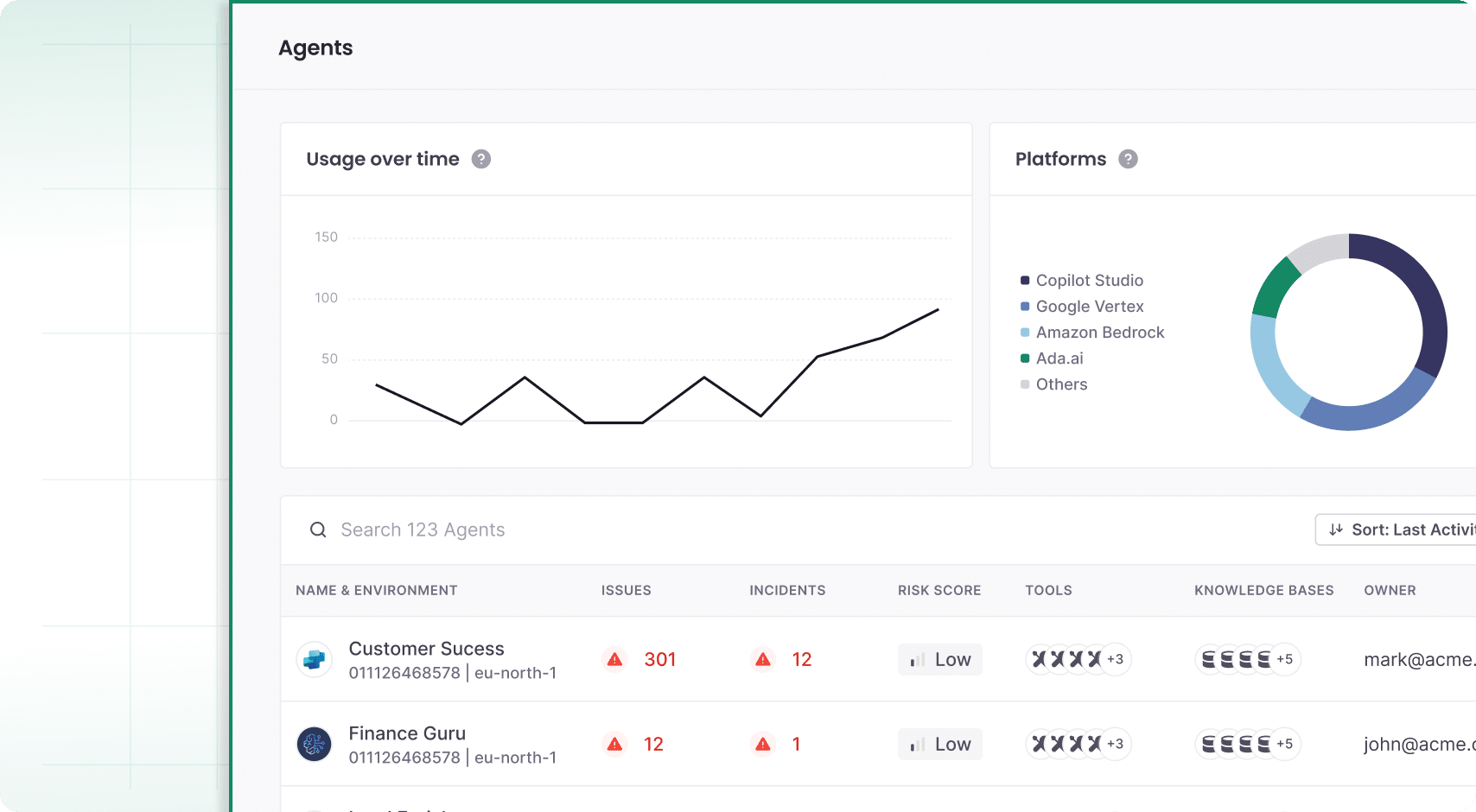
Agentic AI Capabilities
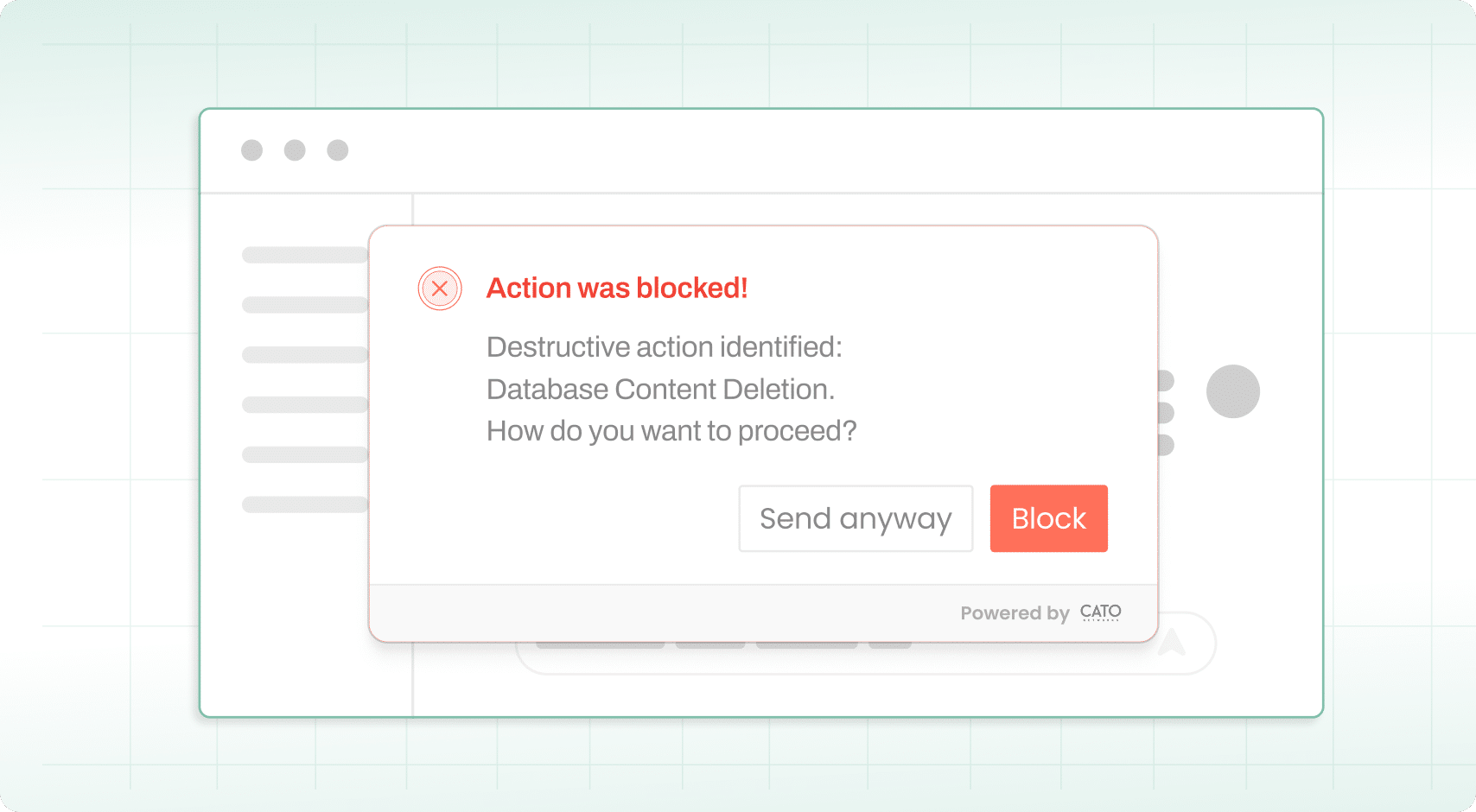
Stop Unwanted Agent Behavior in Real Time
Agentic AI introduces new risks as agents act autonomously across systems, data, and tools. Prompt injection, data exfiltration, and unauthorized actions arise when agents cannot distinguish trusted from untrusted inputs. Cato monitors agent behavior in real time and applies runtime controls to stop attacks before execution.
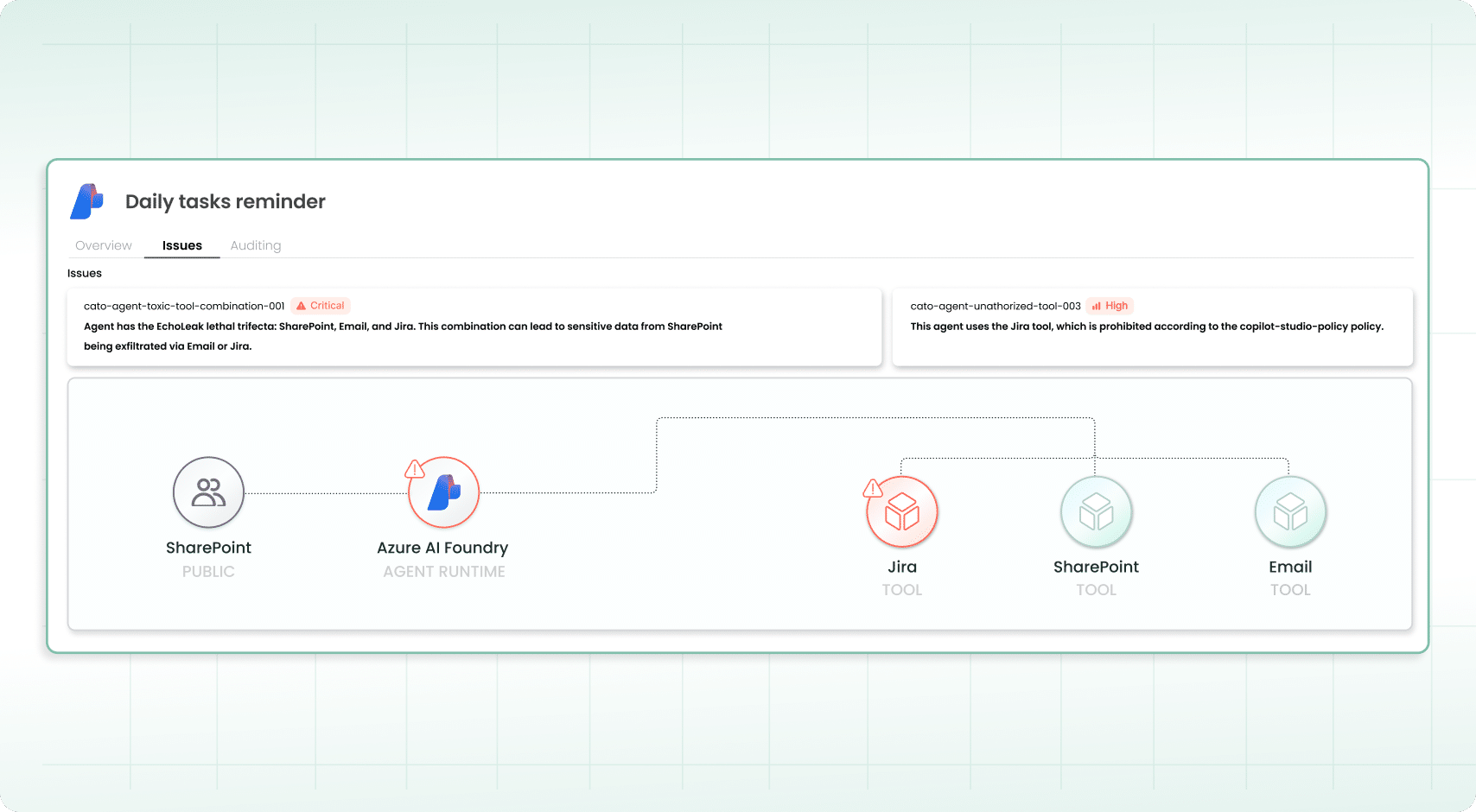
Keep Agents Operating as Intended
Agentic AI is prone to misconfiguration, over-privileged access, and unsafe integrations, as agents operate with excessive permissions across systems. Cato connects to your infrastructure to discover AI agents, monitor behavior, and apply runtime controls to govern access to tools, APIs, and systems.
Prevent Sensitive Data Exposure
Agentic AI introduces compliance risk as agents autonomously access and transmit sensitive data, often without clear boundaries or user oversight. Cato monitors and logs tool calls, APIs, and MCP interactions, enforcing data protection policies and supporting compliance with frameworks like GDPR, the EU AI Act, and emerging AI risk standards.

Secure the AI You Use and Build
Enterprises must secure local and managed AI agents that employees use and custom-built agents. Cato’s unified control plane delivers visibility for all generative and agentic AI use in a single cloud-native platform, ensuring consistent security without additional operational overhead.

Cato SASE Cloud Platform Powers the Digital Business
Customers use Cato to eliminate complex legacy architectures comprised of multiple security point solutions and costly network services. Cato’s unique SASE platform consistently and autonomously delivers secure and optimized application access everywhere and to everyone.
Cato Networks named a Leader in the 2025 Gartner® Magic Quadrant™ for SASE Platforms. Again.
Cato Networks Named a Leader and an Outperformer in the GigaOm 2025 SASE Radar
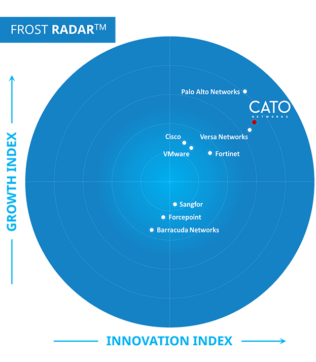
Cato Networks recognized as a Growth and Innovation Leader in SASE
Cato Networks Recognized as Global SSE Product Leader
WAN Transformation with SD-WAN: Establishing a Mature Foundation for SASE Success


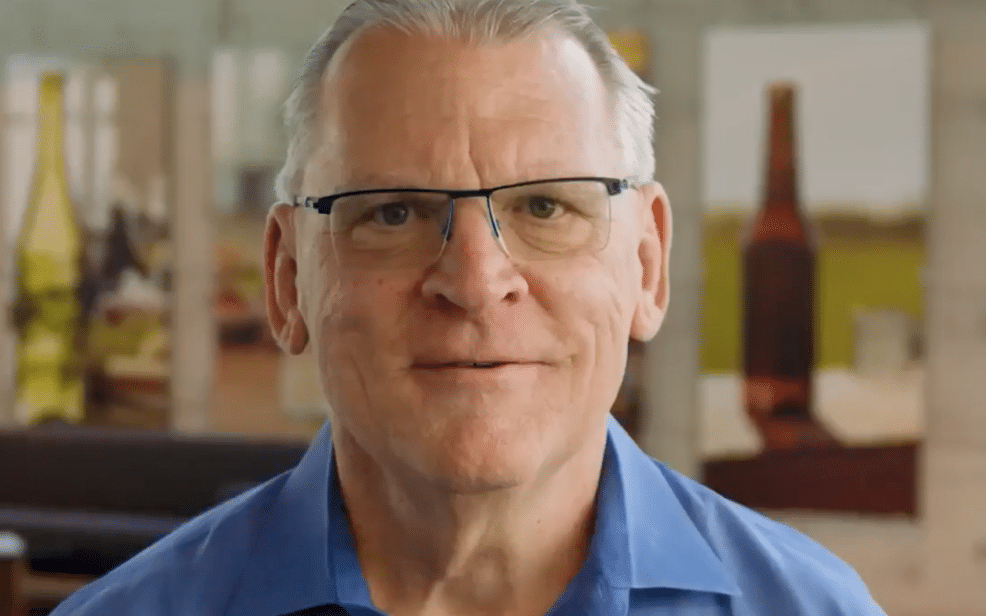
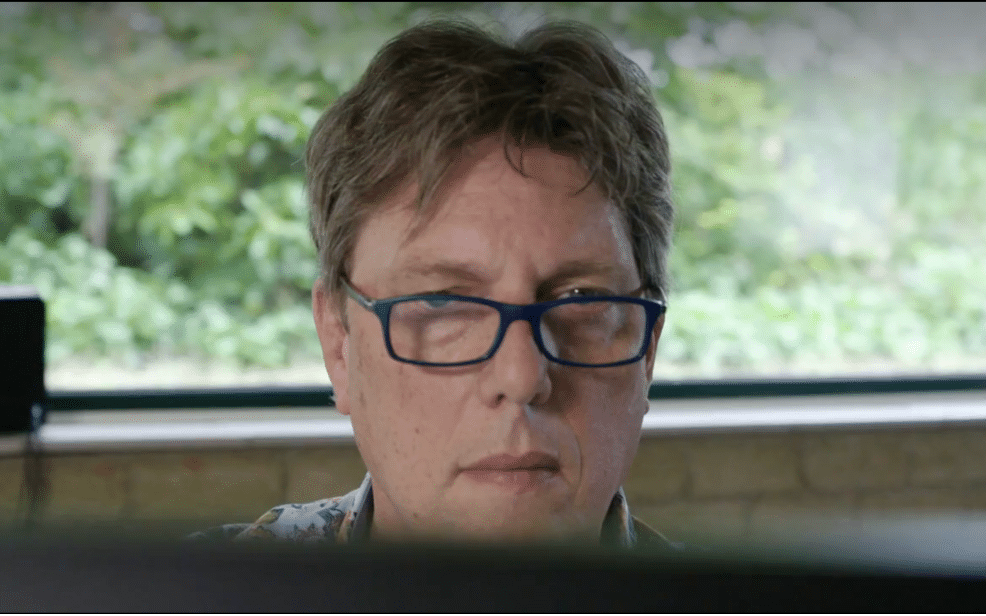
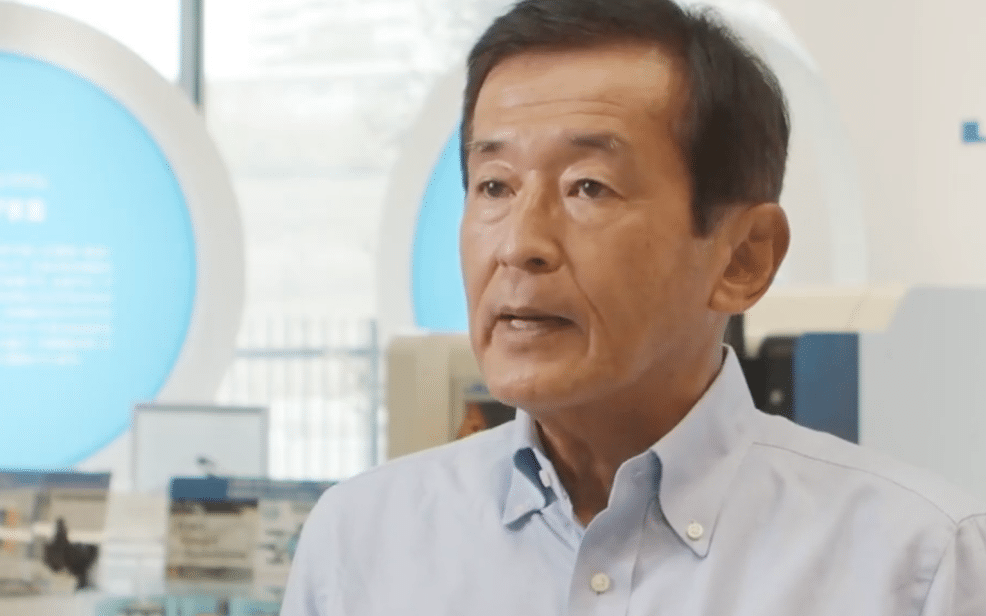
“We ran a breach-and-attack simulator on Cato, Infection rates and lateral movement just dropped while detection rates soared. These were key factors in trusting Cato security.”
Try Cato
The Solution that IT teams have been waiting for.
Prepare to be amazed!