Why Remote Workforce and Legacy Security Architectures Don’t Mix
|
Listen to post:
Getting your Trinity Audio player ready...
|
Last week, we announced the results of our fifth annual IT survey, The Future of Enterprise Networking and Security: Are You Ready for the Next Leap. It was a massive undertaking that saw 2,376 participants from across the globe provide detailed insights into how their organizations responded to the COVID-19 crisis, their plans for next year, and what they think about secure access service edge (SASE).
When the dust settled and the results tallied, we found an optimistic group of IT leaders, confident in their networks but concerned about securing and managing their remote workforce.
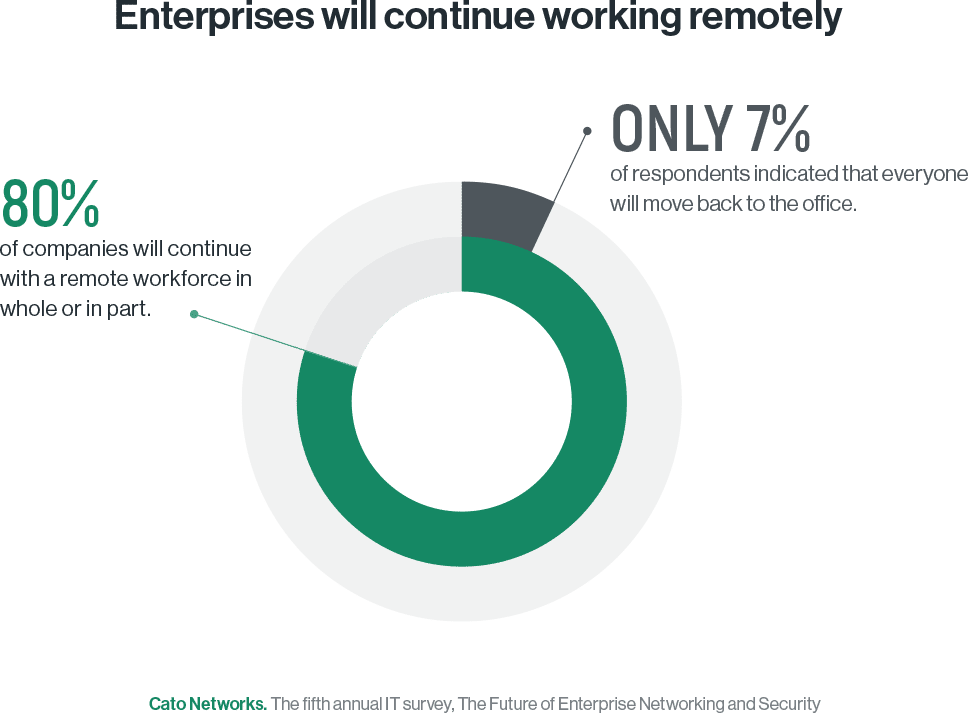
Make no mistake about it, work-from-home (WFH) and the remote workforce aren’t going away any time soon. Only 7%of respondents indicated that everyone will move back to the office. More than half (80%) indicated their companies will continue with a remote workforce in whole or in part.
With users working remotely, IT organizations still need the same level of security controls and visibility. But delivering those capabilities can’t be done by compromising application performance. And that’s a problem for legacy security architectures as they add latency, crippling application performance, and lack the optimization techniques for improving the remote experience.
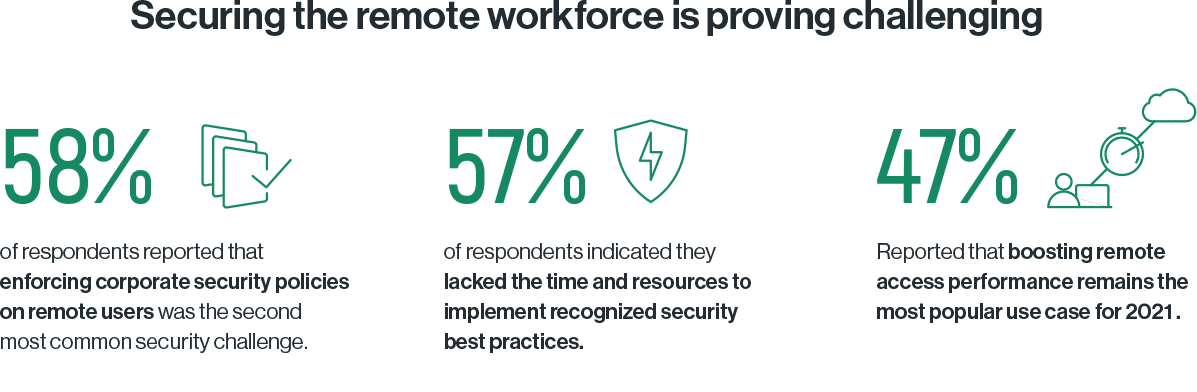
It’s no surprise then that boosting remote access performance was the most popular primary focus for IT leaders over the next 12 months (47% of respondents). At the same time, when asked to cite the primary security challenges facing their IT organizations, 58% of respondents pointed to “enforcing corporate security policies on remote users” making it second to only “Defending against emerging threats like malware/ransomware” (66% of respondents).
But the problems of securing the remote workforce don’t stand on their own. They’re compounded by all of the legacy security challenges facing IT teams. More than half (57% of respondents) indicated that they lacked sufficient time and resources to implement security best practices. And those best practices can be as mundane as patching software and systems shortly after vendors release patches (32% of respondents).
Astounding. In the 21st century with networks that have seen throughput jump ten thousand-fold over the past 30 years and we still have patching problems?
IT managers shouldn’t blame themselves, though. It’s clear where the problem lies — in the architecture. As Cato security engineer, Peter Lee, noted in this blog when documenting the vulnerability and subsequent patches issued for VPN servers:
“Patching has become so common that we just assume that’s the way it has to be. “Patch Tuesday” has us expecting fixes to problems every week. In reality, patching is an artifact of the way all appliances are built. If we eliminate the appliance architecture, we can eliminate the overhead and risk of patches.”
Eliminating appliances will not only eliminate patching problems, it will also eliminate the performance and visibility challenges introduced by legacy security architectures. Of course, this assumes enterprises can replace legacy security architectures with an approach that will:
- Simplify today’s security stack
- Eliminate the patching headaches
- Deliver secure access everywhere, at scale, without compromising performance
- Give visibility and control into all traffics flows
What architecture will do that? According to respondents — SASE.
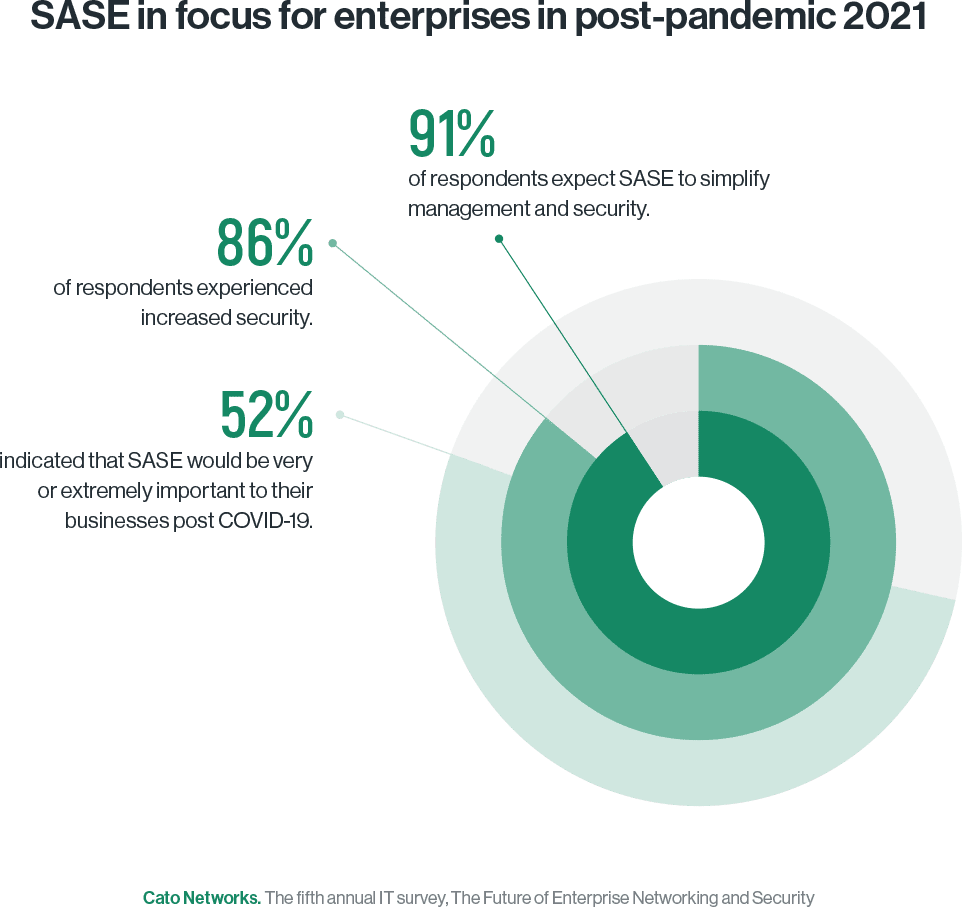
More than 91% of respondents expect SASE to simplify management and security. Of those who’ve already adopted SASE, 86% of respondents experienced increased security, 70% indicated time savings in management and maintenance, 55% indicated overall cost saving and greater agility, 36% saw fewer complaints from remote users, and 36% realized all these benefits. No wonder that more than half of the respondents indicated that SASE would be very or extremely important to their business post COVID-19.
Isn’t it time you considered SASE? To learn more about Cato’s SASE platform, contact us here.




