Overcoming ZTNA Deployment Challenges with the Right Solution
|
Listen to post:
Getting your Trinity Audio player ready...
|
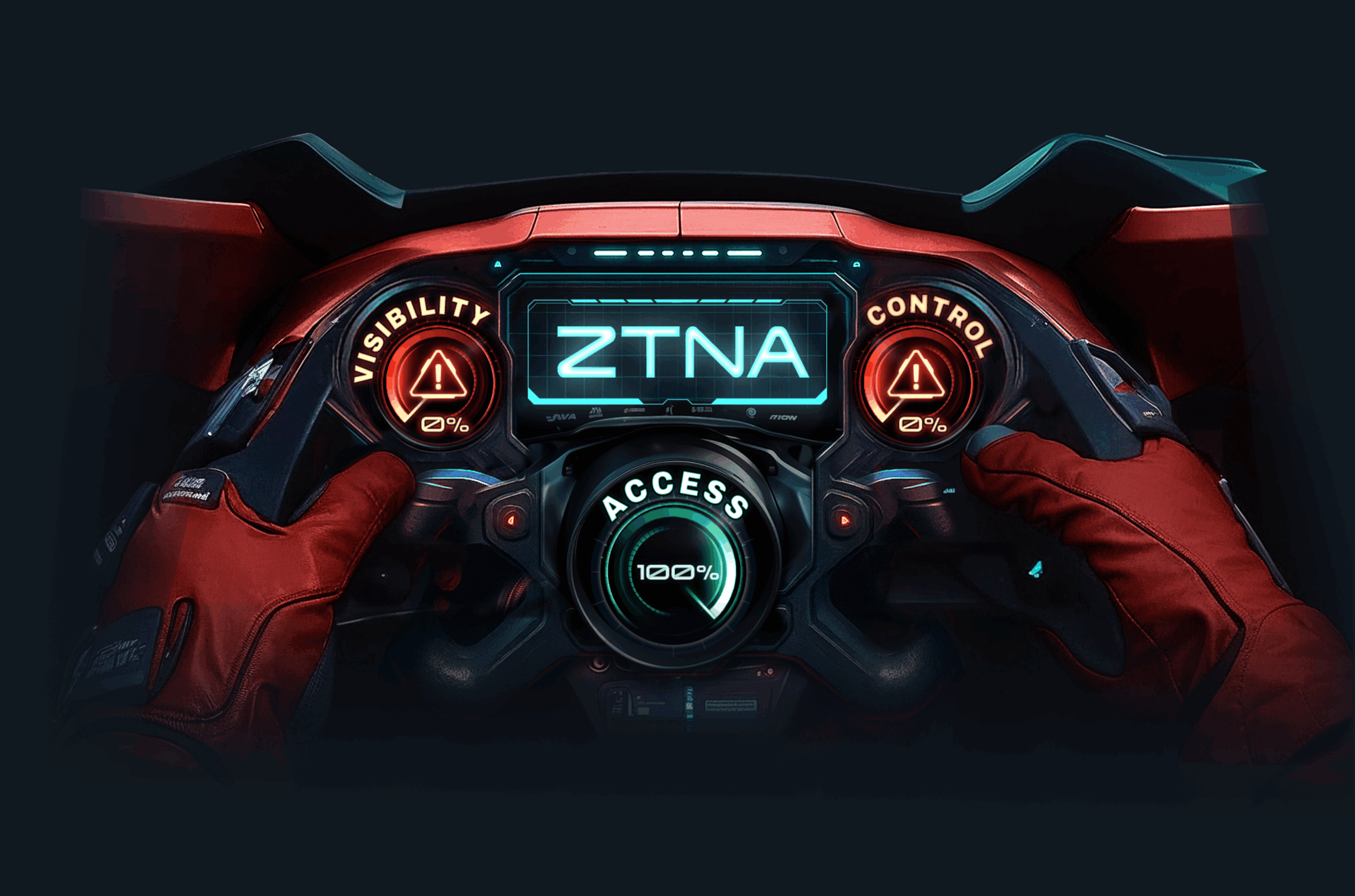
Zero-trust network access (ZTNA) is a superior remote access solution compared to virtual private networks (VPNs) and other legacy tools. However, many organizations are still relying on insecure and non-performant solutions rather than making the switch to ZTNA.
Why You Might Not Be Using ZTNA (But Should Be)
Often, companies have legitimate reasons for not adopting ZTNA – and below we take a closer look at some of the most common concerns:
“A VPN is Good Enough”
One of the simplest reasons why an organization may not want to upgrade their VPN to ZTNA is that they’ve always used a VPN and it has worked for them. If remote users can connect to the resources that they need, then it may be difficult to make a compelling case for a switch. However, even if an organization’s VPN infrastructure is performing well, there is still security to consider.
A VPN is designed to provide a remote user with unrestricted, private access to the corporate network. This means that VPNs lack application-level access controls and integrated security. For this reason, cybercriminals commonly target VPNs because a single set of compromised credentials can provide all of the access needed for a data breach, ransomware infection, or other attacks.
In contrast, ZTNA provides access on a case-by-case basis decided based on user and application-level access controls. If an attacker compromises a user’s account, then their access and the damage that they can do is limited by that user’s permissions.
“ZTNA is Hard to Deploy”
Deploying a new security solution can be a headache for an organization’s security team. They need to integrate it into an organization’s existing architecture, design a deployment process that limits business disruption, and perform ongoing configuration and testing to ensure that the solution works as designed. When an organization has a working VPN solution, then the overhead associated with switching to ZTNA may not seem worth the effort.
While installing ZTNA as a standalone solution may be complex, deploying it as part of a Secure Access Service Edge (SASE) solution can streamline the process. With a managed SASE solution, deployment only requires pointing infrastructure to the nearest SASE point of presence (PoP) and implementing the required access controls.
Secure zero trust access to any user in minutes | ZTNA Demo“VPNs are Required for Compliance”
Most companies are subject to various data protection and industry regulations. Often, these regulations mandate that an organization have certain security controls in place and may recommend particular solutions. For secure remote access, VPNs are commonly on the list of acceptable solutions due to their age and widespread adoption.
However, regulations are changing rapidly, and the limitations of VPNs are well known. As regulators start looking for and mandating a zero-trust approach to security within organizations, solutions like VPNs, which are not designed for zero trust, will be phased out of regulatory guidance.
While regulations still allow VPNs, many also either explicitly recommend ZTNA or allow alternative solutions that implement the required security controls. ZTNA provides all of the same functionality as VPNs but also offers integrated access control. When deployed as part of a SASE solution, ZTNA is an even better fit for regulatory requirements due to its integration with other required security controls and adoption of a least privileges methodology commonly required by regulatory frameworks such as UK NCSC Cyber Essentials and NIST. For organizations looking to achieve and maintain compliance with applicable regulations, making the move to ZTNA as soon as possible will decrease the cost and effort of doing so.
“We’ve Already Invested in Our VPN Infrastructure”
VPNs have been around for a while, so many organizations have existing VPN deployments. When the pandemic drove a move to remote work, the need to deploy remote work solutions as quickly as possible led many organizations to expand their existing VPN infrastructure rather than investigate alternatives. As a result, many organizations have invested in a solution that, to a certain degree, meets their remote work needs. These sunk costs can make ripping out and upgrading VPN infrastructure an unattractive proposition.
However, the differential in functionality between a VPN and a ZTNA solution can far outweigh these costs. ZTNA provides integrated access management, which can reduce the cost of a data breach and simplify an organization’s regulatory compliance strategy. A ZTNA solution that successfully prevents a data breach by blocking unauthorized access to sensitive data may have just paid for itself.
“Our Security Team is Already Overwhelmed with Our Existing Solutions”
Many organizations’ security teams are struggling to keep up. The cybersecurity skills gap means that companies are having trouble finding and retaining the skilled personnel that they need, and a sprawling array of security solutions creates overwhelming volumes of alerts and the need to configure, monitor, and manage various standalone solutions. As a result, the thought of deploying, configuring, and learning to use yet another solution may seem less than appealing.
Yet one of the main advantages of ZTNA is that it simplifies security monitoring and management, especially when deployed as part of a SASE solution. By integrating multiple security functions into a single network-level solution, SASE eliminates redundant solutions and enables security monitoring and management to be performed from a single console. By reducing the number of dashboards and alerts that analysts need to handle, SASE reduces the burden on security teams, enabling them to better keep up with an accelerating threat landscape and expanding corporate IT infrastructure.
ZTNA is the Future of Remote Access
Many organizations have solutions that – on paper – provide the features and functionality that they need to support a remote workforce and provide secure access to corporate applications. However, legacy solutions like VPNs lack critical access controls and security features that leave an organization vulnerable to attack.
As the zero trust security model continues to gain momentum and is incorporated into regulations, organizations will need solutions that meet their security needs and regulatory requirements. ZTNA meets these needs, especially as part of a SASE solution.