The Meltdown-Spectre Exploits: Lock-down your Servers, Update Cloud Instances
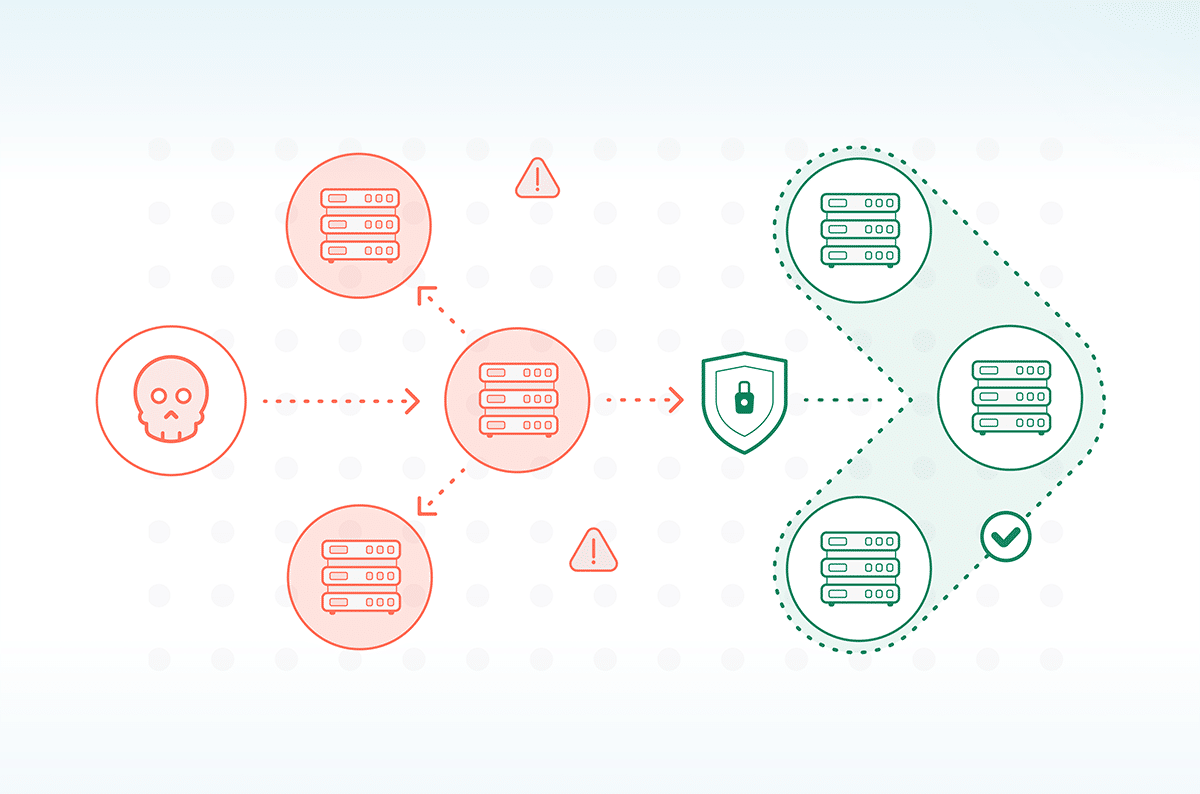
The much publicized critical CPU vulnerabilities published last week by Google’s Project Zero and its partners, will have their greatest impact on virtual hosts or those servers where threat actors can gain physical access.
The vulnerabilities, named Meltdown and Spectre, are hardware bugs that can be abused to leak information from one process to another in the underlying process or the dependent on operating system. More specifically, the vulnerability stems from a misspeculated execution that allows arbitrary virtual memory reads, bypassing process isolation of the operating system or processor. Such unauthorized memory reads may reveal sensitive information, such as passwords and encryption keys. These vulnerabilities affect many modern CPUs including Intel, AMD and ARM.
Cato Research Labs analyzed the security impact of vulnerabilities Spectre (CVE-2017-5753, and CVE-2017-5715) Meltdown (CVE-2017-5754) on Cato Cloud and our customers’ networks. Any measures needed to protect the software or hardware have been taken by Cato.
We highly recommend that Cato customers follow their cloud provider’s guidelines for patching operating system running in the virtual machine of their cloud hosts. Most cloud providers have already patched the underlying hypervisors. Specific patching instructions can be found here for Microsoft Azure, Amazon AWS, and Google Cloud Platform.
Additional information about the attacks is described in Google Project Zero blog. Meltdown was discovered by Jann Horn at Google Project Zero; Werner Haas and Thomas Prescher at Cyberus Technology; and Daniel Gruss, Moritz Lipp, Stefan Mangard, Michael Schwarz at the Graz University of Technology.
Horn and Lipp were also credited in the discovery of Spectra along with Paul Kocher in collaboration with ( in alphabetical order) Daniel Genkin of the University of Pennsylvania and the University of Maryland, Mike Hamburg from Rambus, and Yuval Yarom from the University of Adelaide and Data61.