Firewall as a Service and your biggest network security challenge

|
Listen to post:
Getting your Trinity Audio player ready...
|
We recently held a webinar focused on educating network professionals about Firewall as a Service (FWaaS). At the beginning of this webinar, we asked the audience “what is your biggest challenge running distributed network security today?” Attendees overwhelmingly noted “monitoring 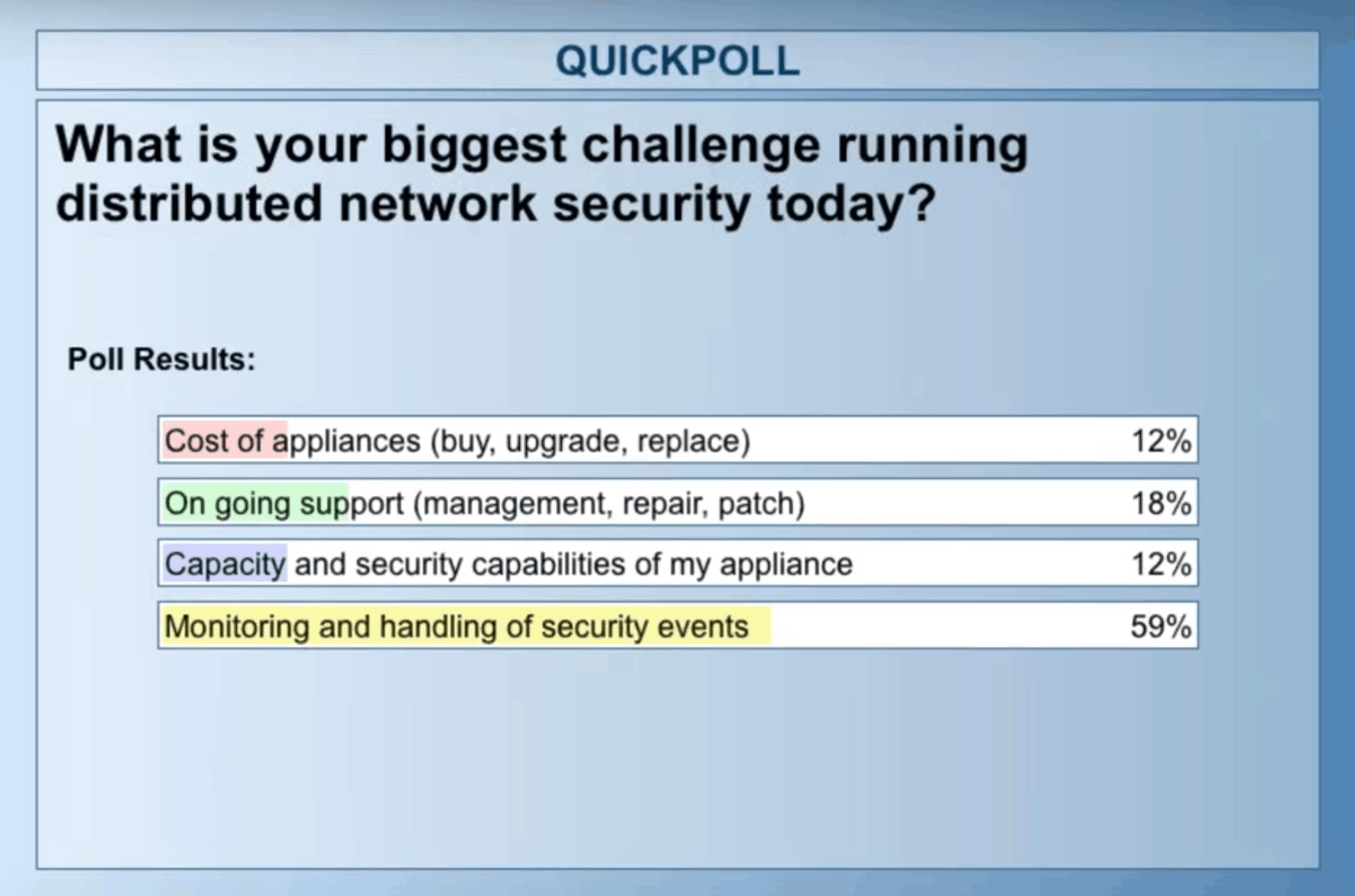
The Challenge of Appliance-Based Network Security
Network security was simpler in the past: there was a clear perimeter (or perimeters for multi-site companies) with networks, users, and applications firmly inside organizations. To securely connect users at any company location to business applications, or to secure traffic over the internet, we could either connect remote sites with an appliance on the perimeter site, or backhaul all the traffic to a datacenter. Today, there are global organizations with 10s of locations, roaming users with business and personal devices, and business applications both inside the local datacenter and in the Cloud. This creates three main challenges when relying on appliance-based network security:
- Appliance sprawl: Companies choosing appliance-based network security are facing complexity involved in planning, configuring and maintaining multiple appliances on each site location. Appliances have a fundamental limitation as they require continuous updates, upgrades, and patch management. In addition, appliances can’t scale with business needs – if at some point the business consumes more traffic or would like to add additional functionality, the appliance must support it or else an upgrade is enforced. In many cases, companies compromise on security due to budget limitations and the capacity constraints of the appliance they have. Last, using appliances requires a business to depend heavily on the vendor for support.
- Direct internet access: Today, most employee traffic is internet traffic – either for business use (e.g. Office 365, Dropbox or Salesforce, etc.) or personal browsing. Two approaches are commonly used to provide secure internet access to employees:
- Exit the internet on each site location and secure it locally. This method contributes to appliance sprawl due to its complexity and manageability overhead.
- Backhaul traffic through the company datacenter and exit to the internet from a central location. This approach is mostly chosen by companies that don’t want to compromise on security and also need WAN access. The backhauling approach means routing the traffic through the datacenter where there is a big firewall to secure it before exiting to the internet. This can be achieved in two ways::
- Establishing a VPN connection to traffic from each location using an appliance. In addition to the appliance sprawl problems, this option requires the management of a complex VPN policy and configuration. VPNs usually result in bad user experiences as the traffic routed over the public internet can suffer from high latency and packet drop.
- Using an MPLS network and routing the traffic over a reliable network. The problem with this option is that MPLS is an expensive network that was not designed to carry heavy traffic (designed for mission-critical applications) and the internet traffic consumes a lot of the MPLS expensive bandwidth. MPLS also has other challenges like the complexity of deployment and provisioning. Both VPN and MPLS are not an effective way to exit the internet as it causes the trombone effect.
- Mobile and cloud access: Connecting mobile users to local and cloud applications while keeping security and visibility is challenging using appliances. For WAN access, most companies use VPN tunneling from a device directly to the perimeter firewall. The challenge here is that users experience high latency when a datacenter is located far away geographically, so the traffic gets routed all over the public internet. Another challenge is that in many cases the business resources are not located in one place, so it requires the complex management of split tunnels. Additionally, users tend to access business applications from personal devices and via private networks without any control or visibility to the organization. To deal with this, many companies use additional solution for SaaS security and visibility called cloud access security brokers (CASB), which requires the management of another security solution.
Gartner’s Perspective on Firewall-as-a-Service
Last month Gartner released its Hype Cycle for Infrastructure Protection. In this report, Gartner mentioned FWaaS for the first time and defined it as a firewall delivered as cloud-based service that allows customers to partially or fully move security inspection to a cloud infrastructure. According to the report, FWaaS is simple, flexible and more secure, and it results in faster deployment and easier maintenance. FWaaS also provides consistently good latency across all enterprise points of presence, so it should provide SD-WAN functionality for resilience. Additionally, the Cloud benefits include centralize management and unique security features based on its full visibility. Gartner’s advice for customers is to trust the Cloud for both security and performance.
What to Look for in FWaaS:
- Traffic inspection and remote access: inspection of both the WAN and internet traffic – a full stateful inspection, SSL inspection and threat prevention capabilities. In addition, a FWaaS should allow remote connections from all locations and mobile users.
- Segmentation: a full understanding of internal networks – IPs, VLANs, NAT and routing decisions
- User and application awareness: the ability to set and enforce security policies based on the user identity, location and machines while accessing applications or URLs
- Flexibility and scalability: On top of all the basic firewall capabilities a FWaaS should have all the benefits of the Cloud. That means a rapid deployment, seamless upgrade, elasticity and elimination of all the challenges involved in managing appliances.
There are a few popular alternatives to the FWaaS model, but they lack fundamental requirements. For example, using secure web gateways (SWG) in the Cloud lacks visibility and security for WAN traffic, can’t take an active role in the network segmentation, and doesn’t offer a VPN connection back to company resources. Additionally, options like appliance stacking – racking and stacking appliances in the cloud or using a virtual edition of firewalls – just moves the problem to the Cloud. Upgrades and maintenance are still a huge challenge for such solutions.
Firewall-as-a-service brings a unique opportunity to organizations to simplify network security. To learn more about how Cato Networks deal with those challenges and how Cato’s firewall-as-a-service works please watch our recorded webinar.
Read more about the firewall as a service market




