What is Zero Trust Network Access (ZTNA)?
What is Zero Trust Network Access (ZTNA)?
Zero Trust Network Access, also known as software-defined perimeter (SDP), is a modern approach to securing access to applications and services both for users in the office and on the road. How ZTNA works is simple: deny everyone and everything access to a resource unless explicitly allowed. This approach enables tighter network security and data security via micro-segmentation that can limit lateral movement if a breach occurs.
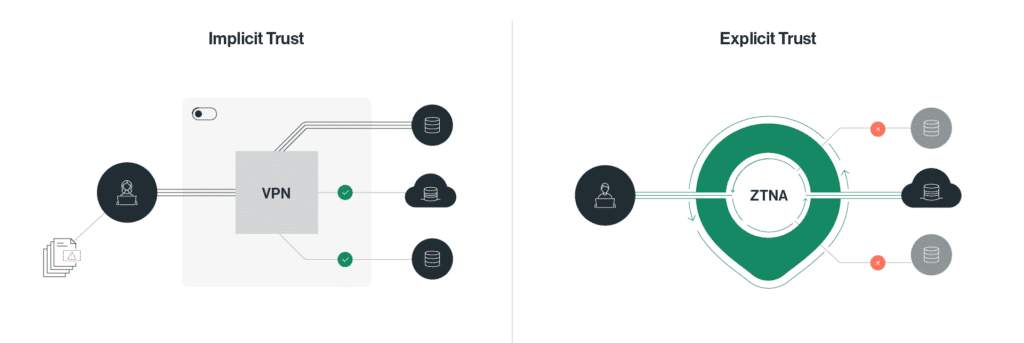
With legacy network solutions based on VPN, authenticated users implicitly gain access to everything on the same subnet. Only a password prevents unauthorized users from accessing a resource. ZTNA flips that paradigm. Users can only “see” the specific applications and resources explicitly permitted by their company’s security policy.
Benefits of ZTNA
ZTNA allows organizations to apply zero trust security to their networks. ZTNA can contribute to several use cases that can help improve an organization’s security posture:
- Enabling microsegmentation—ZTNA allows organizations to segment their networks into smaller parts and establish a software-defined security perimeter to protect each part of the network. This approach reduces the attack surface and prevents lateral movement.
- Minimizing account breach risk—ZTNA minimizes the damage attackers can cause by compromising a user account. Even if an attacker manages to breach an account, the access level remains restricted, and the attacker cannot move through the network or perform sensitive tasks like privilege escalation.
- Mitigating insider threats—traditional security solutions cannot identify or protect against malicious insiders like rogue employees. The zero trust model restricts the damage caused by insider threats by ensuring each user has the least privilege access required. ZTNA also provides visibility to help track malicious insiders.
- Obfuscating internal applications—ZTNA makes applications unavailable over the public Internet. This can help protects companies from data leaks, ransomware, and other Internet-based threats.
- Securing cloud access—ZTNA allows organizations to restrict access to their applications and cloud environments based on business requirements. Every entity (i.e., user or application) has an assigned role in the ZTNA model, with clearly defined access permissions to use cloud infrastructure.
- Supporting compliance—the principle of least privilege enhances compliance with company and industry standards. The organization has more control over how employees use each application and data and can verify that all usage is authorized.
ZTNA Use Cases
ZTNA fits many use cases. Here are some of the most common:
- VPN Alternative – Connect mobile and remote users more securely than legacy VPN. ZTNA is more scalable, provides one security policy everywhere, works across hybrid IT, and offers more fine-grained access. Gartner projected that by 2023, 60% of enterprises would switch from VPN to ZTNA.
- Reduce third-party risk – Give contractors, vendors, and other third parties access to specific internal applications — and no more. Hide Sensitive Applications – Render applications “invisible” to unauthorized users and devices. ZTNA can significantly reduce the risk posed by insider threats.
- Secure M&A integration – ZTNA reduces and simplifies the time and management needed to ensure a successful merger or acquisition and provides immediate value to the business.
Related resources:
How Does ZTNA Work?
ZTNA is not only more secure than legacy remote access solutions, it’s designed for today’s business. Legacy networks assumed a secure network perimeter with trusted entities inside and untrusted entities outside. Today the perimeter is gone. Users work everywhere — not only in offices — and applications and data are increasingly moving to the cloud. Access solutions need to be able to address those changes.
ZTNA provides numerous advantages over other secure remote access solutions, including:
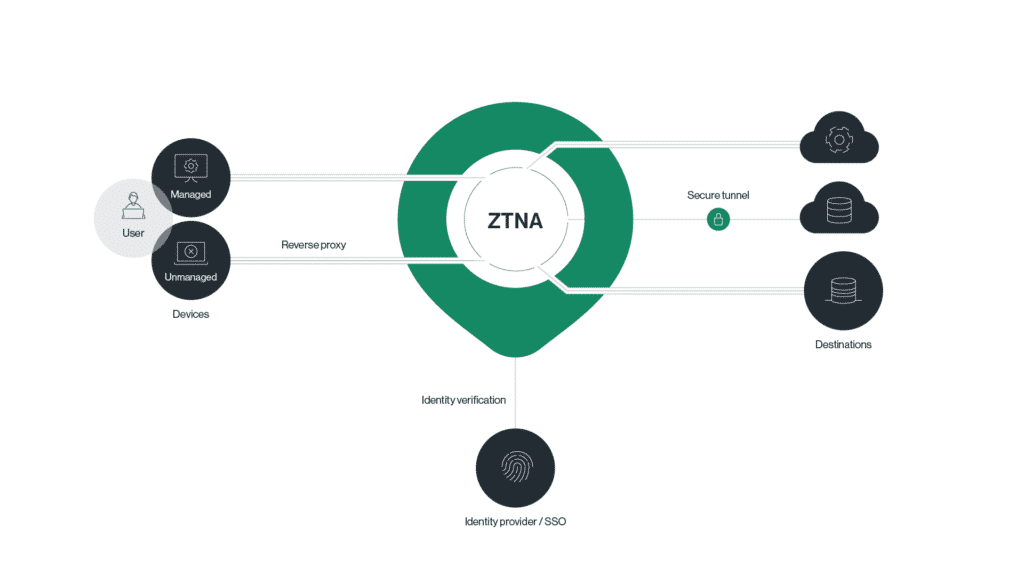
- Application access that dynamically adjusts based on user identity, location, device posture, and more.
- Cloud-based service that supports both managed and unmanaged devices (via a reverse proxy).
- Secure tunnels between the ZTNA service and corporate resources.
- Identity verification and authorization for access to company assets – whether in an on-premises data center or in the cloud.
The 4 Functions of ZTNA
ZTNA performs four essential functions:
- Identify – map all systems, applications and resources that users may need to access from remote.
- Enforce – define the access conditions policies under which specific individuals can or cannot access specific resources.
- Monitor – log and analyze all access attempts of remote users to resources, making sure enforced policies adhere to the business requirements.
- Adjust – modify misconfiguration. Either increase access privileges or reduce to support optimal productivity while minimizing risk and exposure.
ZTNA User Flow
The ZTNA user workflow is as follows:
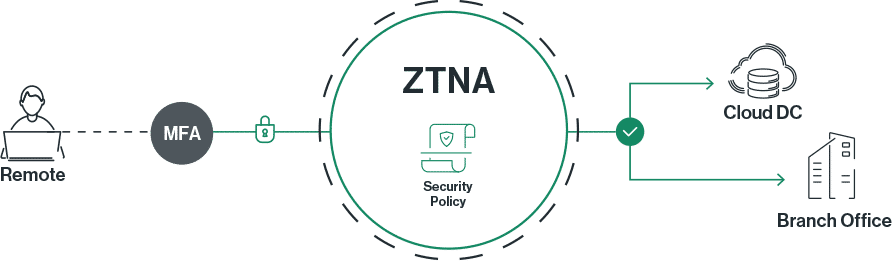
- Authentication: The user connects and authenticates to a Zero Trust controller (or controller function). Multi-factor authentication (MFA) is used to offer enhanced account security.
- Policy Enforcement: The ZTNA controller identifies and implements the appropriate security policy to determine whether the user should be granted access. This can check device attributes — such as its digital certificate and presence of an up-to-date antivirus — and real-time attributes — such as location — to inform an access determination.
- Access: Based on the collected features and security policy, the controller decides whether to grant access. If so, they can access only those applications and resources for which they have authorization.
Related resources:
How to Implement ZTNA?
ZTNA provides much more granular access management than other remote access solutions. To implement ZTNA, take the following steps:
- Assess Existing Architecture: A ZTNA deployment should be designed to meet an organization’s business needs. Assessing the existing network architecture and the endpoints to manage will help in selecting a ZTNA solution.
- Choose a ZTNA Model: ZTNA solutions can be agent-based or service-based. Both have their advantages, and the choice between them should be made based on the organization’s environment and security requirements.
- Solution Selection: After choosing a ZTNA type, the next step is to identify a particular ZTNA solution. Some important considerations include security, ease of use, scalability, and compliance.
- Develop Policies: ZTNA is intended to support and enforce zero-trust access controls. Access policies and user roles should be defined based on the security requirements of various resources and the role of users, applications, devices, etc., within the organization.
- Implement and Test: Deploy the ZTNA solution. Perform testing to ensure that the tool appropriately manages access to corporate resources.
- User Training: Educate users about the new system. Discuss the value of a zero trust security for the business and for their personal security.
- Monitoring and Auditing: Perform ongoing monitoring, auditing, and maintenance of the system throughout its lifetime. Regular audits of security policies and controls help to ensure that the solution is performing as intended.
Agent-Based ZTNA vs. Service-Based ZTNA
| Agent-Based ZTNA | Service-Based ZTNA | |
| Deployment Location | Software agent on user device | Connector deployed in user’s network |
| Platform Support | Platform-specific | Platform agnostic |
| Offline Access | Limited | None |
| Endpoint Visibility | Deep | Limited |
| Ease of Use | Requires more maintenance | More user-friendly |
| Security Integration | Integration with endpoint security solutions | Integration with network security solutions |
ZTNA vs. VPN
ZTNA and VPNs are two options for secure remote access. Remote access VPNs are designed to create a secure, encrypted tunnel to carry traffic between a remote user and the corporate network.
ZTNA and VPNs have significant differences, including:
- Access Management: ZTNA implements zero-trust access controls, while VPNs provide largely unrestricted access to the corporate network.
- Scalability: ZTNA is a cloud-based solution with high scalability, while VPNs are often appliance-based, limiting their scalability.
- Network Performance: Cloud-based ZTNA enables efficient, low-latency connectivity to corporate resources, while point-to-point VPNs often backhaul traffic to the headquarters network before routing it to cloud-based destinations.
VPN Replacement
VPNs are an older, more established solution for secure remote access, but they were designed for a time when most corporate IT assets were on-prem, and a small portion of the workforce was remote. As corporate IT infrastructures and business practices evolve, ZTNA offers a replacement option for VPNs that is better suited to the needs of the modern business.
Secure Remote Access
Companies have a growing number of workers who connect to corporate IT resources from outside the corporate LAN. Hybrid work arrangements, bring-your-own-device (BYOD) policies, and contracting are three common examples of remote work.
Secure remote access solutions protect these remote users’ traffic as it traverses the untrusted public Internet to reach the corporate network. At a minimum, this involves encrypting traffic en route, but more advanced solutions — such as ZTNA and SASE — incorporate access controls and network security functions as part of a converged secure remote access solution.
ZTNA and Micro-segmentation
Network segmentation breaks the corporate network into isolated segments based on purpose and trust level. Micro-segmentation takes this a step further, placing each application within its own segment and applying security policies and access controls to all traffic crossing the network.
ZTNA leverages microsegmentation to enforce its zero-trust security policies. Microsegmentation places trust boundaries around each application, allowing ZTNA to inspect and apply access control policies to requests to that application.
ZTNA and SASE
With Secure Access Service Edge (SASE) the ZTNA controller function becomes part of the SASE PoP and there’s no need for an SDP connector. Devices connect to the SASE PoP, get validated and users are only given access to those applications (and sites) allowed by the security policy in the SASE Next-Generation Firewall (NGFW).
But ZTNA is only a small part of Secure Access Service Edge (SASE). Once users are authorized and connected to the network, IT leaders still need to protect against network-based threats. They still need the right infrastructure and optimization capabilities in place to protect the user experience. And they still need to manage their overall deployment.
SASE addresses those challenges by bundling ZTNA with a complete suite of security services — NGFW, SWG, anti-malware, and Managed XDR — and with network services such as SD-WAN, WAN optimization, and a private backbone.
Enterprises that leverage SASE receive the benefits of Zero Trust Network Access plus a full suite of network and security solutions, all converged together into a package that is simple to manage, optimized, and highly scalable.
Related resources:
- See how simple setting up ZTNA is by watching our demo on how to configure ZTNA.
- Read more about the ZTNA capabilities of SASE
- Watch our Webinar on using SASE for ZTNA
The Future: ZTNA 2.0
The zero-trust security model is still relatively new, and many organizations are still working to adopt zero trust and figure out what it means for them. As a result, many companies are replacing legacy remote access technologies with ZTNA and integrating it into their security architectures.
Over time, ZTNA technology will likely evolve to meet the changing needs of the organization. For example, solutions may incorporate AI to better make access determinations, or the growth of edge computing might inspire a more decentralized approach to zero-trust access management.
Zero Trust Security: Principles and Framework Explained
Explore insights into Zero Trust Security, where the integration of continuous verification and stringent access controls enhances network resilience against contemporary cyber threats. Discover the core principles of this approach for a transformative impact on network security.
How to Implement Zero Trust: 5 Steps and a Deployment Checklist
A zero trust security model can help enterprises improve security of data and IT resources while gaining extended visibility into their ecosystem. Zero trust implementation typically includes at least five steps, which include adding microsegmentation to the network, adding multi-factor authentication, and validating endpoint devices.
Zero Trust Solutions: 5 Solution Categories and How to Choose
Zero trust solutions are security toolkits that incorporate network access controls and security measures to implement the principle of zero trust, which regards all users and entities as potentially malicious until proven safe. Implementing zero trust networks often requires organizations to combine multiple tools and processes.
Secure the Remote Workforce: Deploying Zero Trust Access
Global Workplace Analytics estimates that 25-30% of the workforce will be working from home multiple days a week by the end of 2021. What does this mean for the remote access worker? Organizations must adjust to make it very quick and easy to give highly secure access to any and all remote workers.
See Our Additional Guides on Key Data Security Topics
Data PrivacyAuthored by Imperva |
Cyber SecurityAuthored by Imperva |
RansomwareAuthored by Cynet |








