Featured
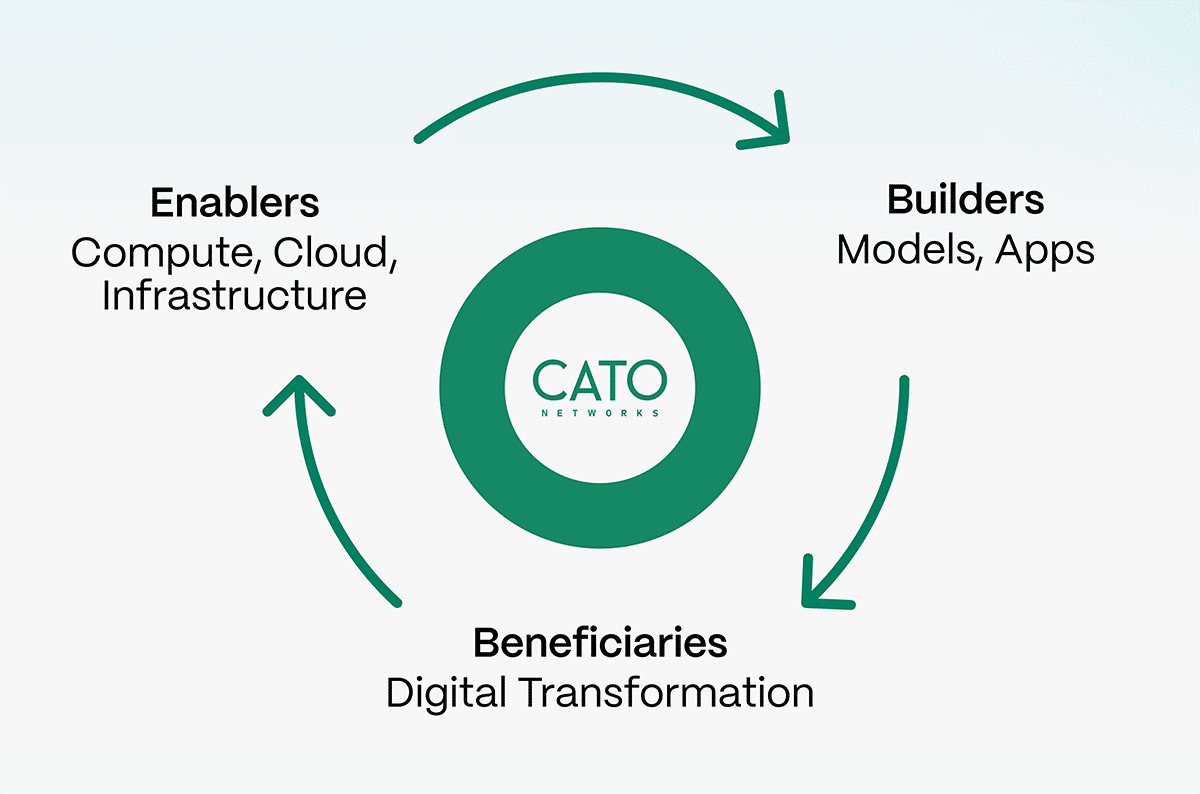
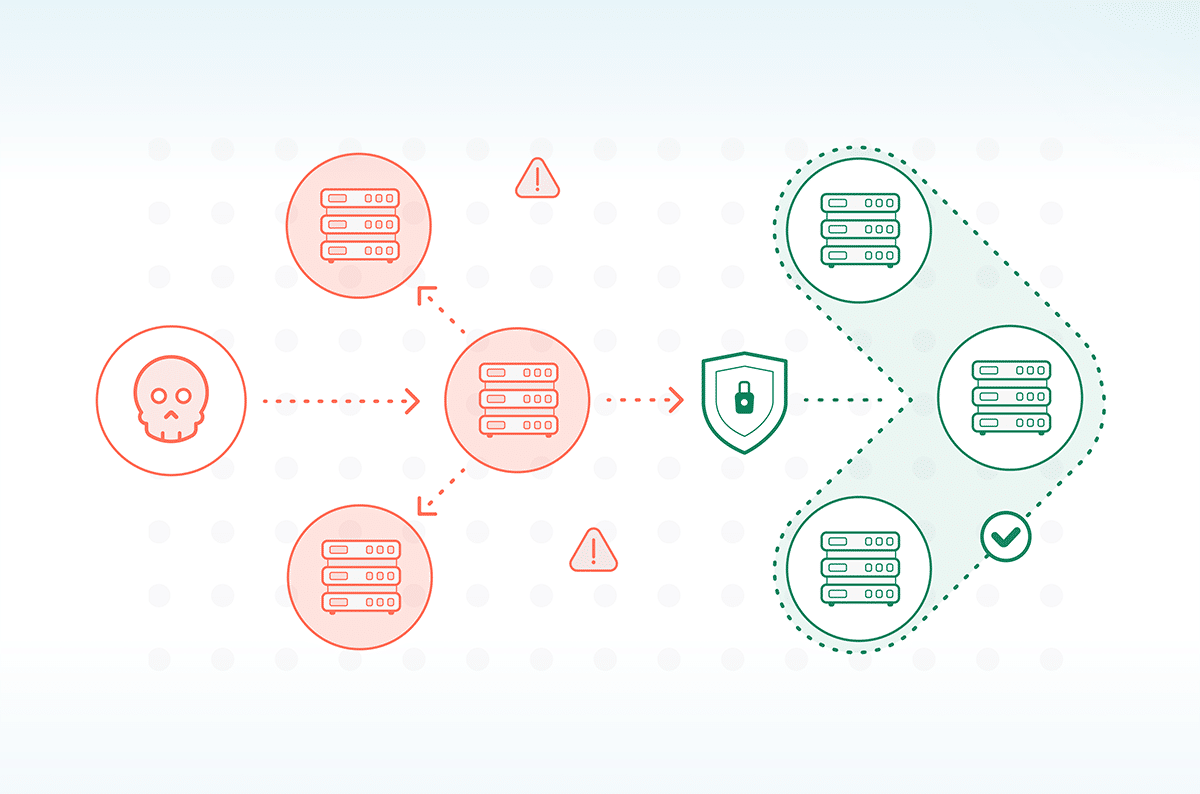
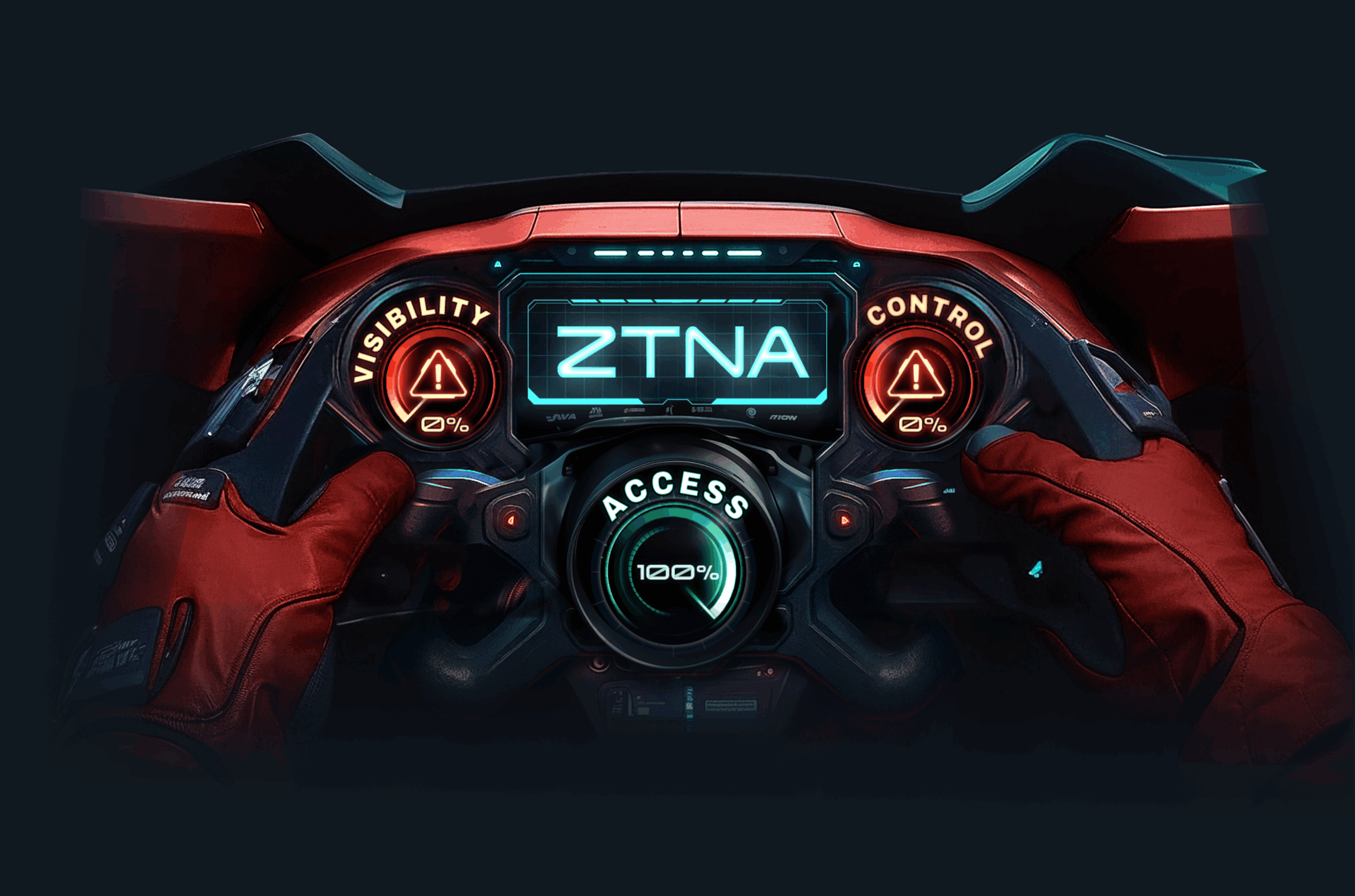
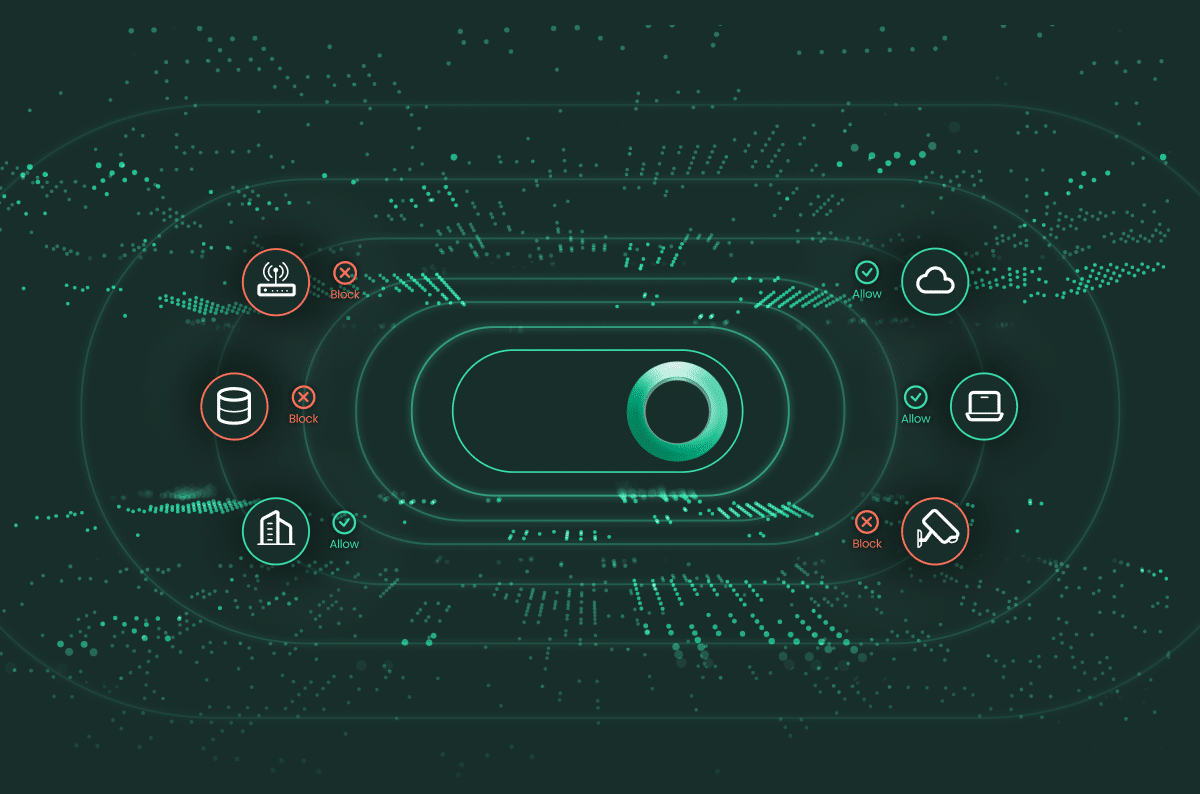
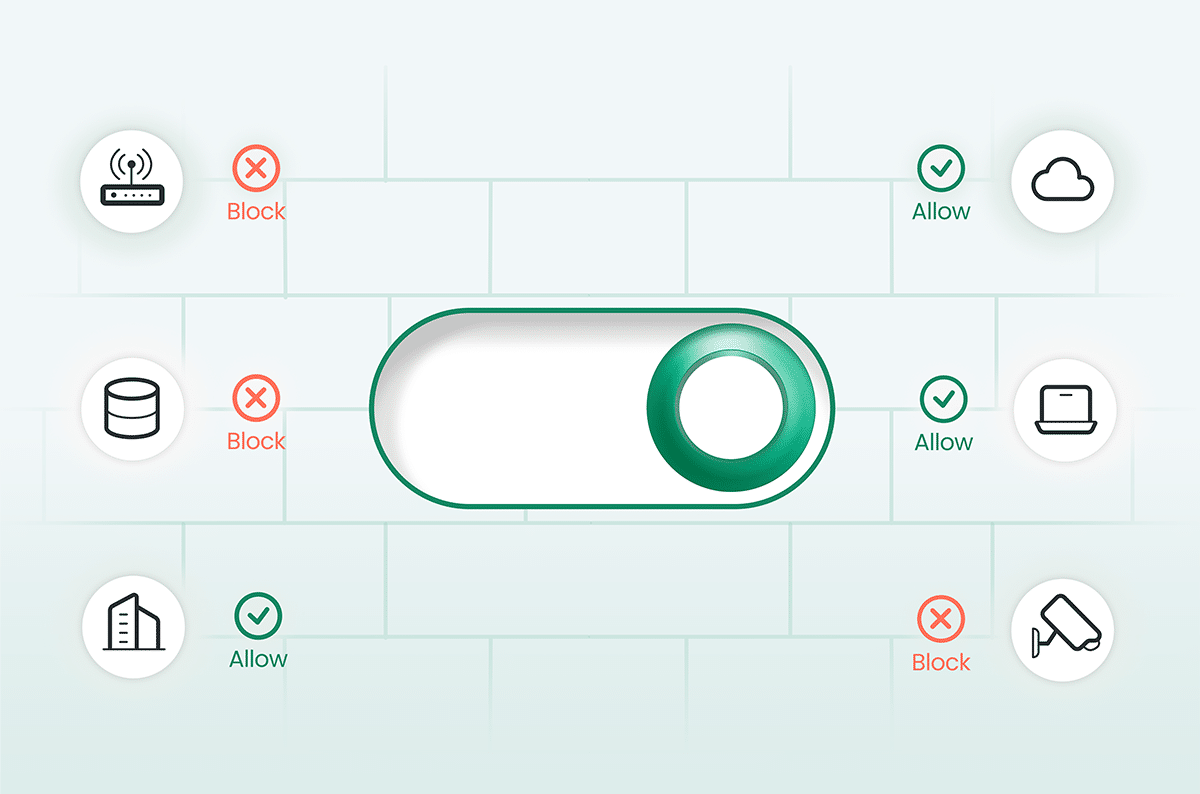
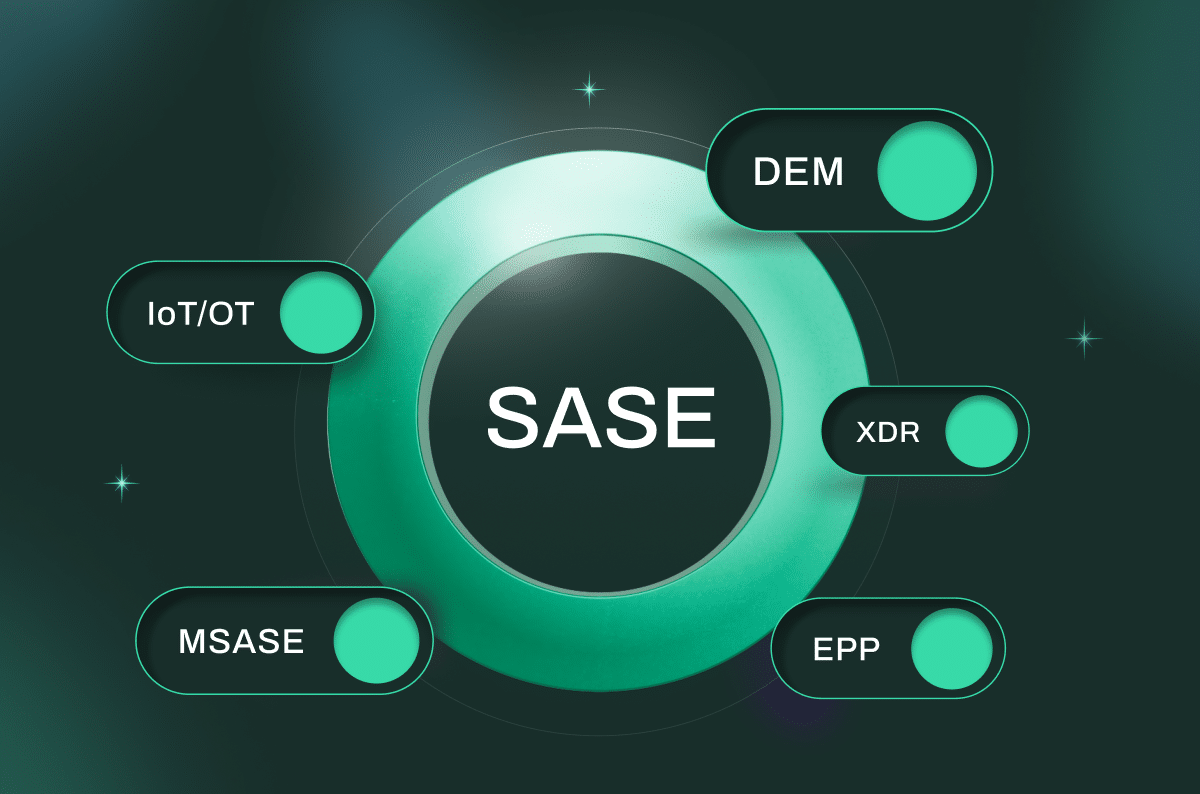
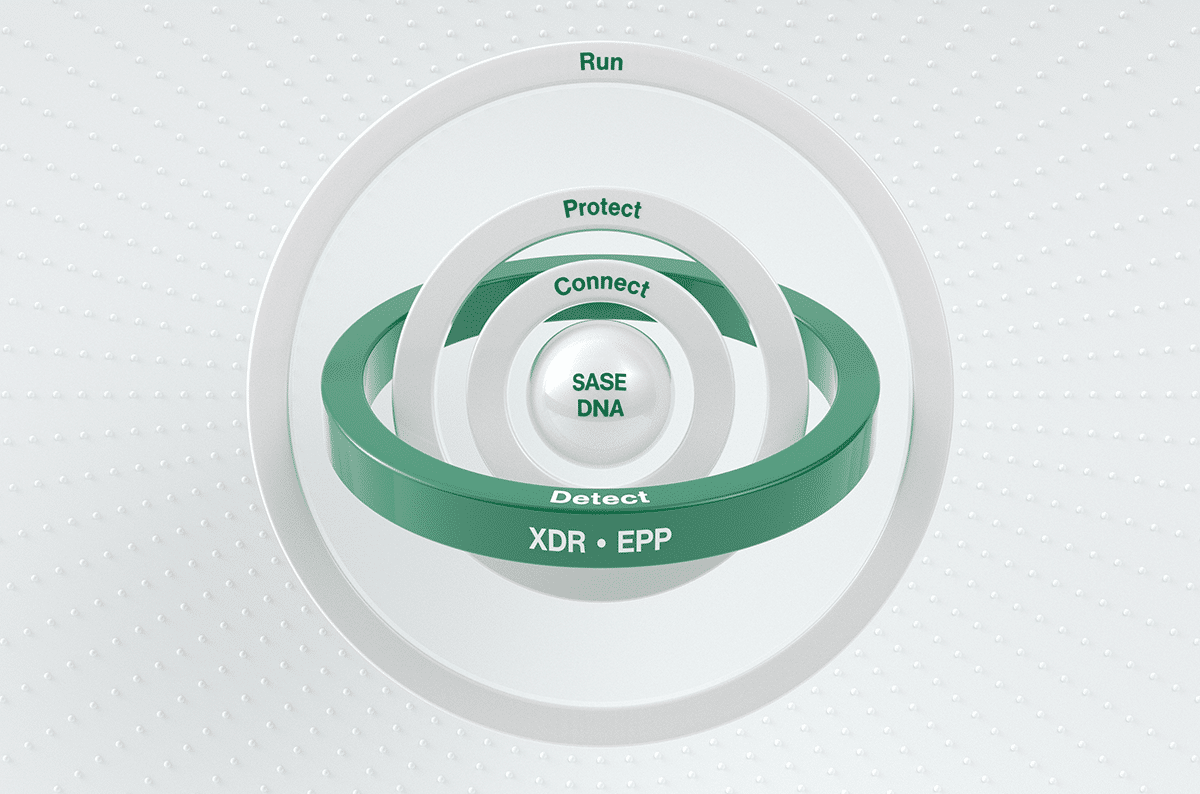
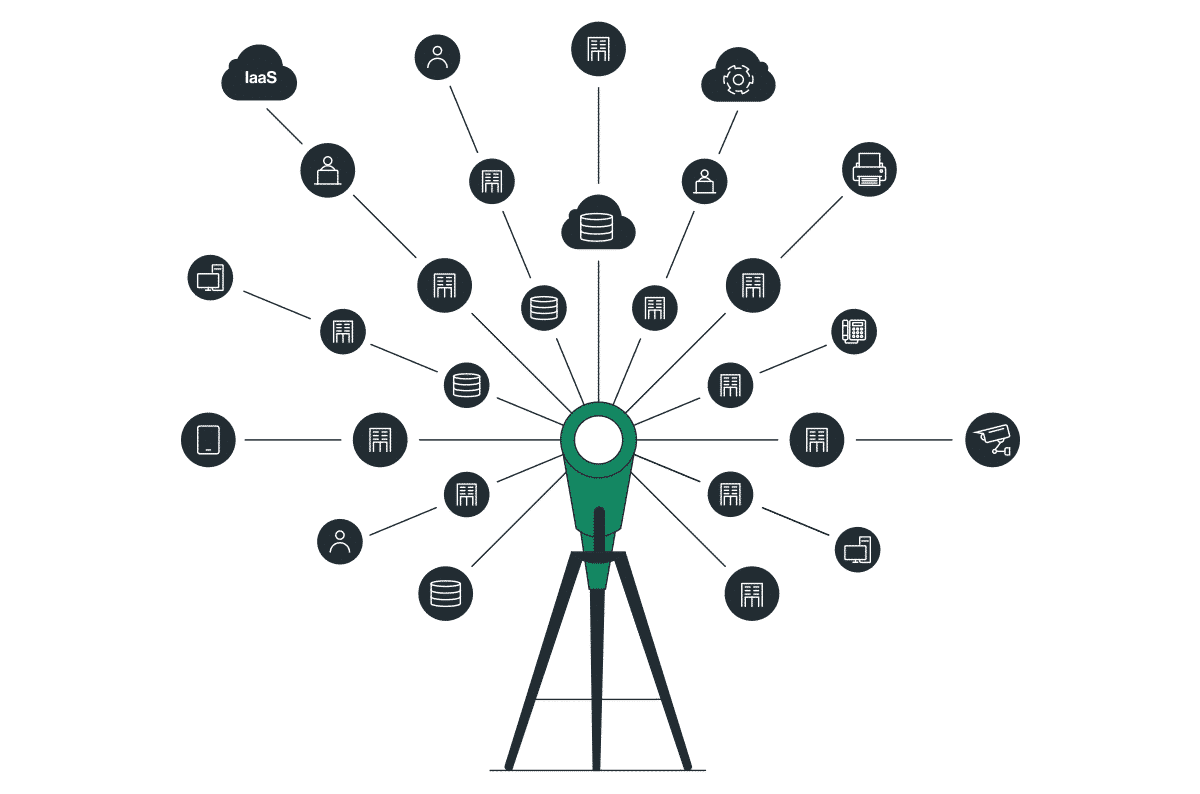
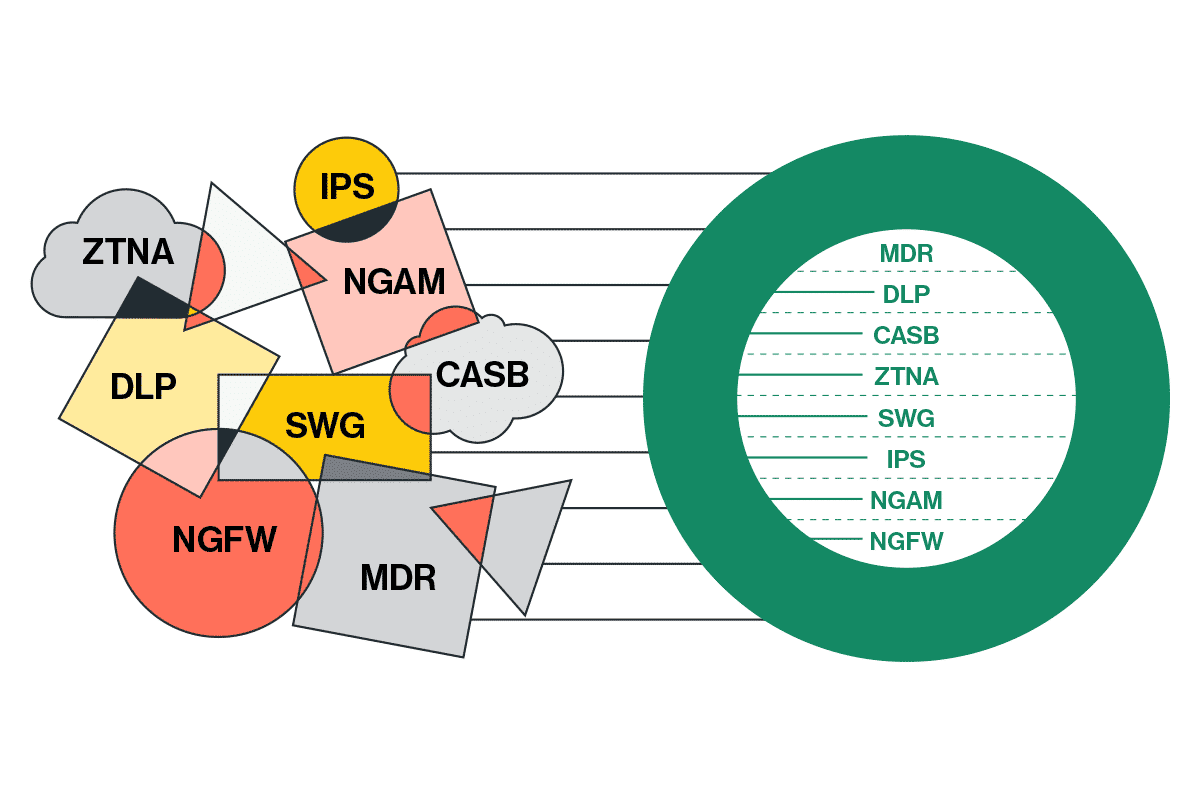
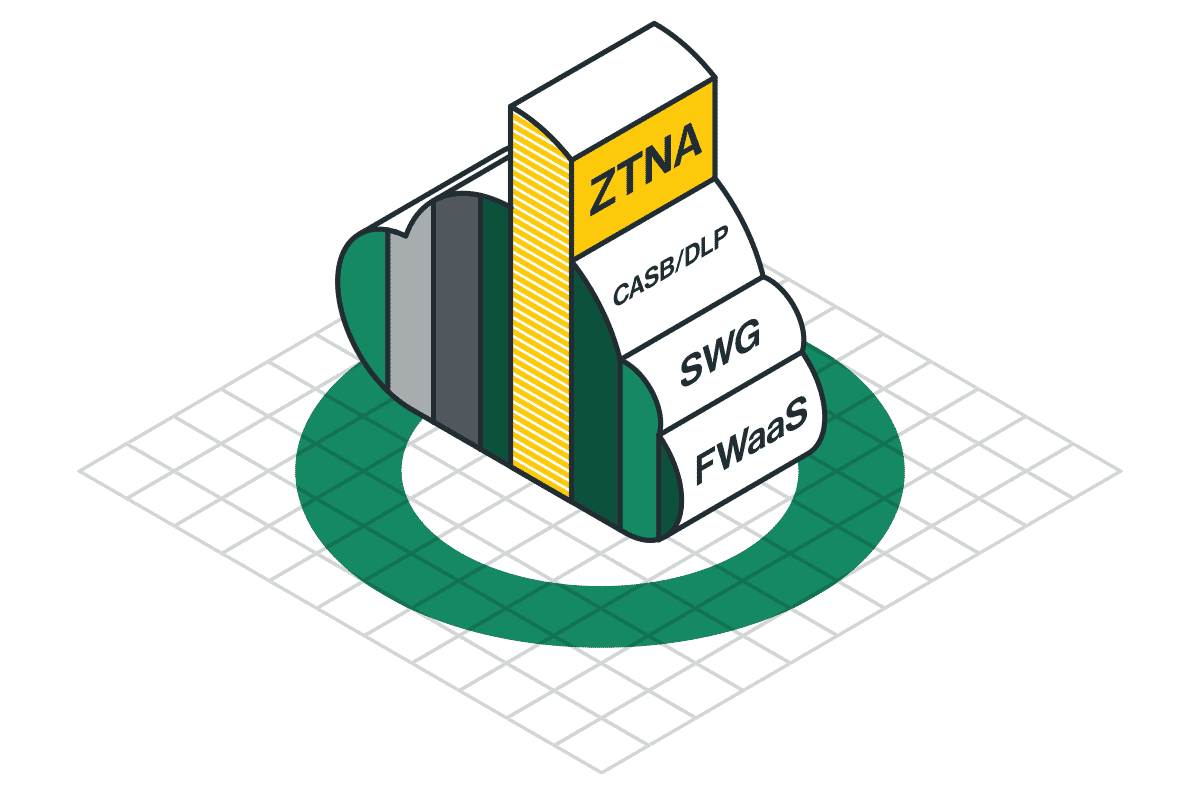
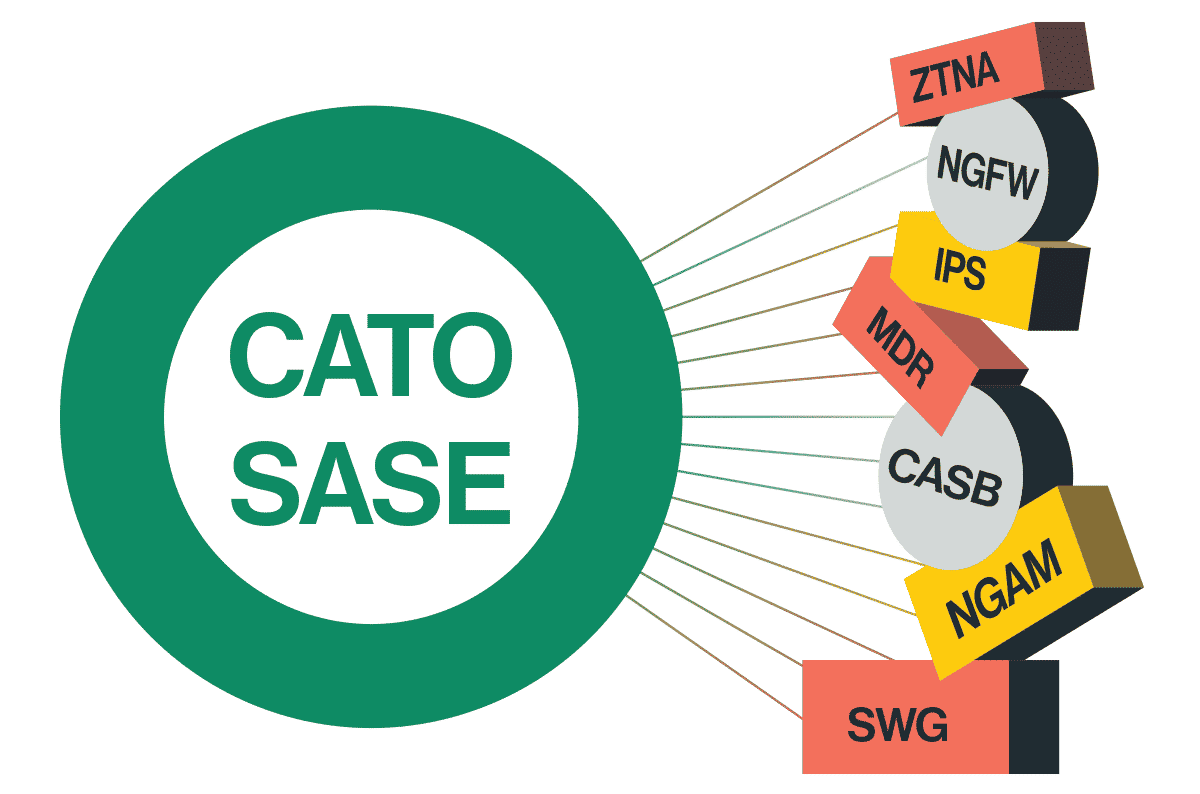
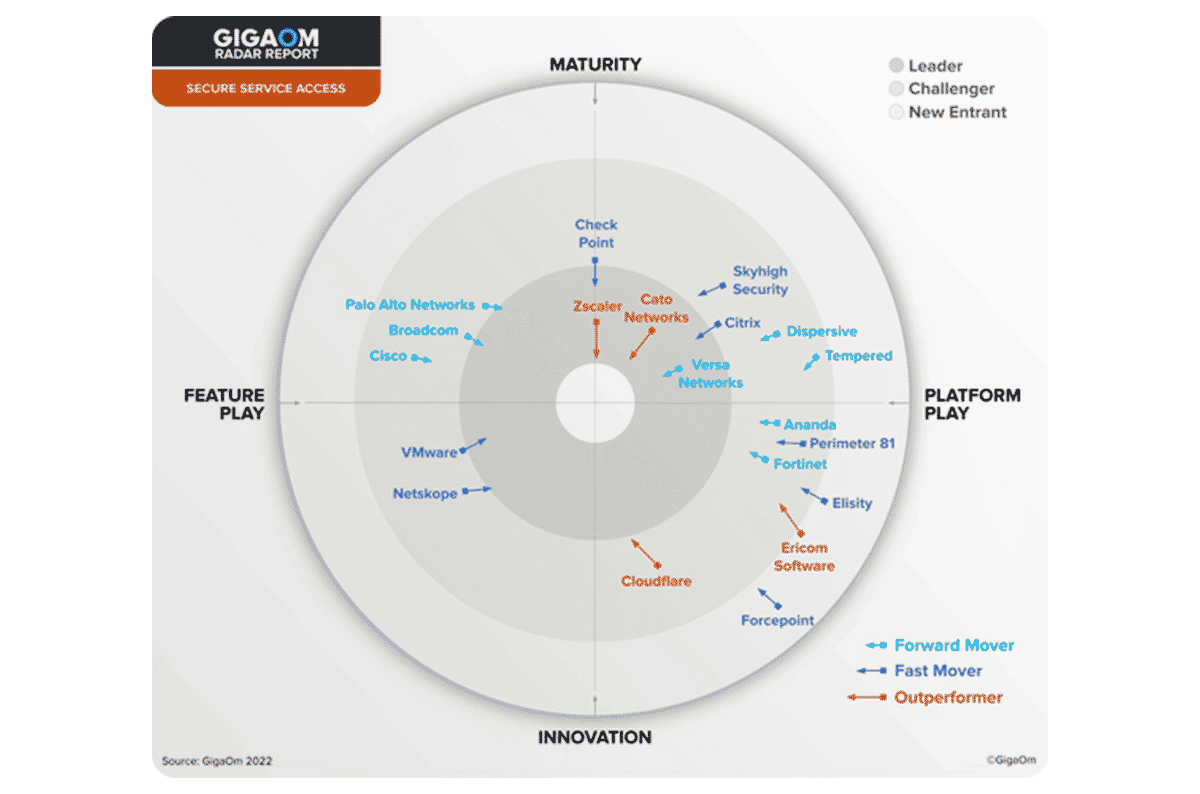
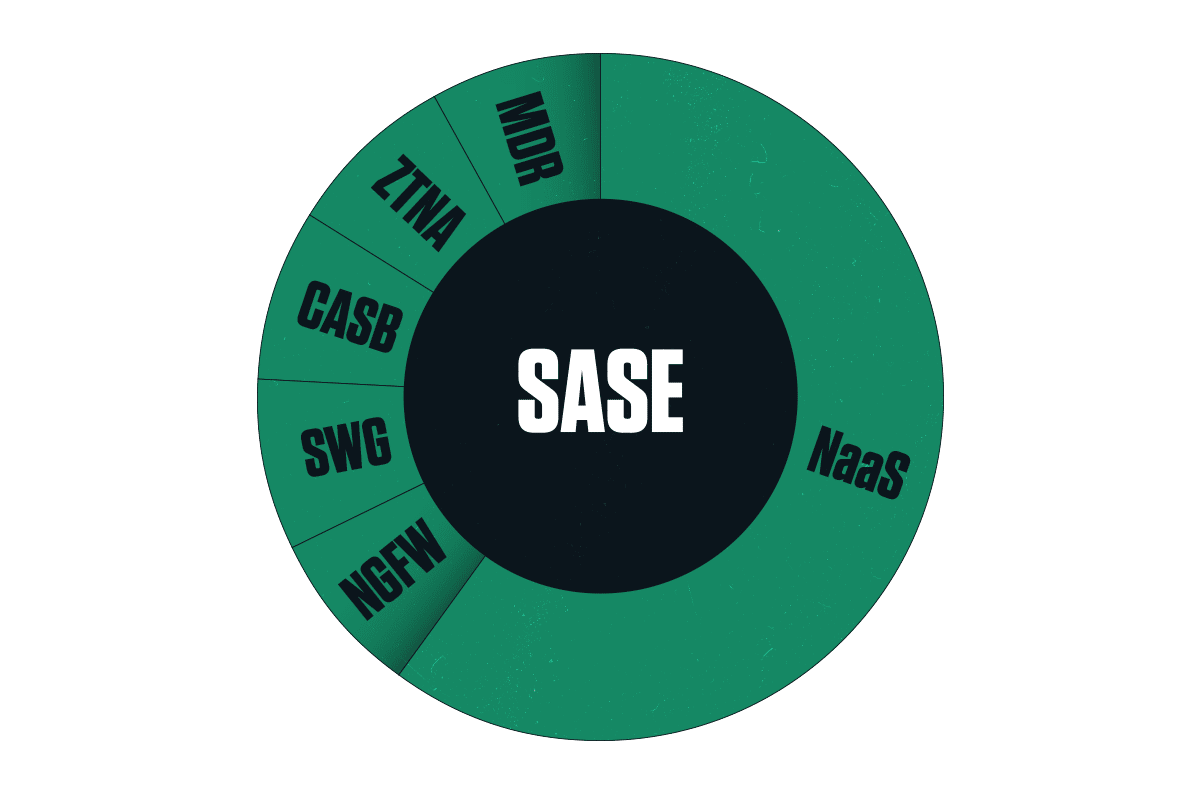
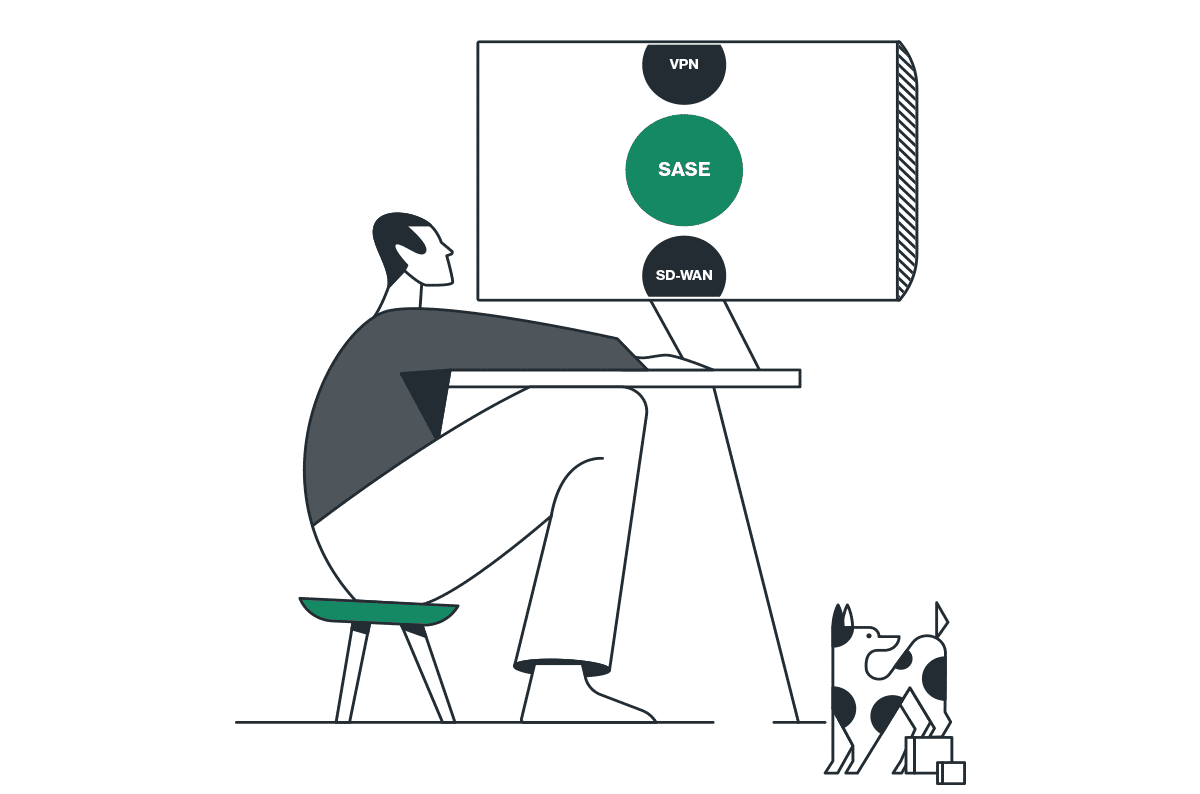
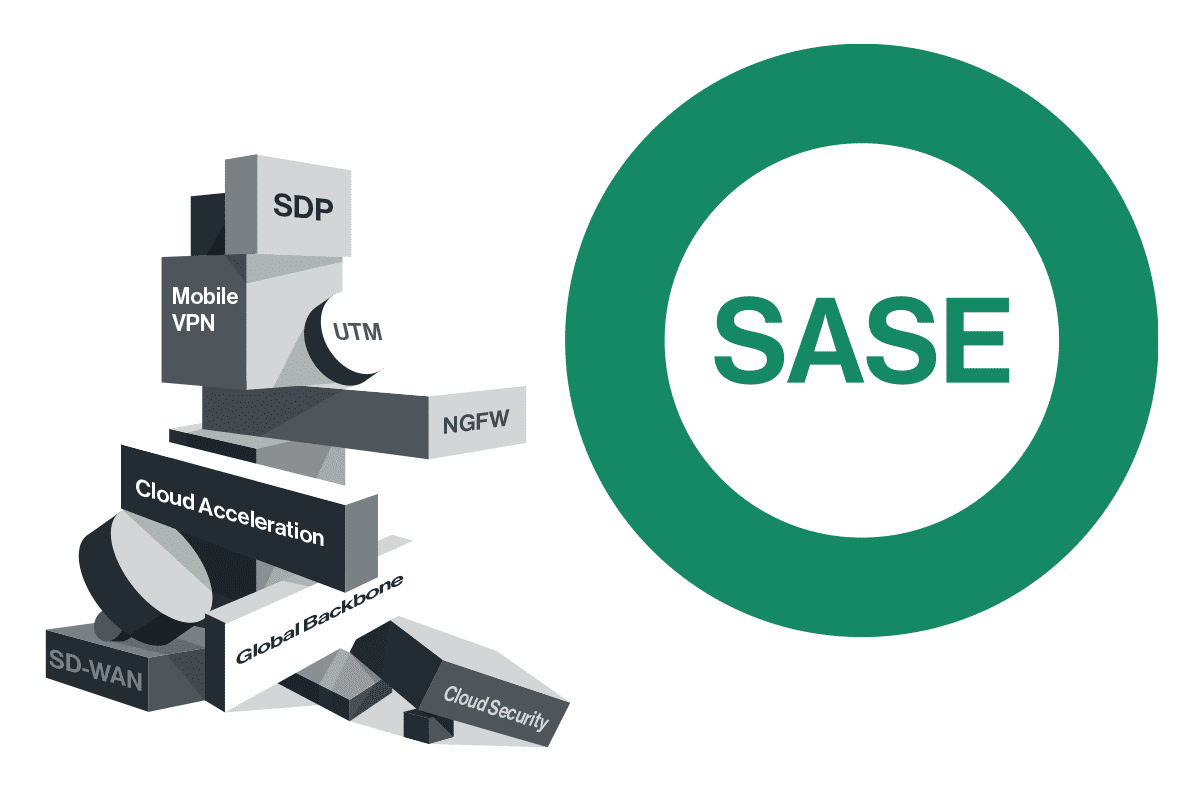
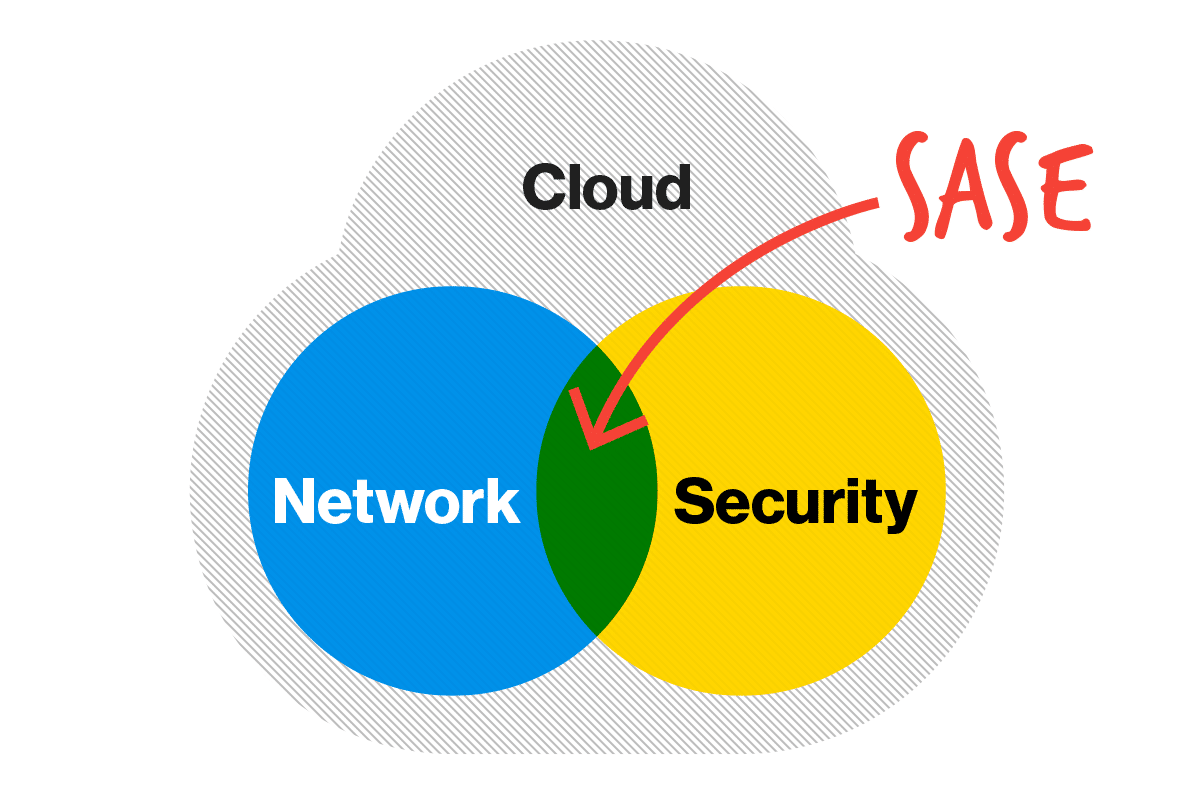
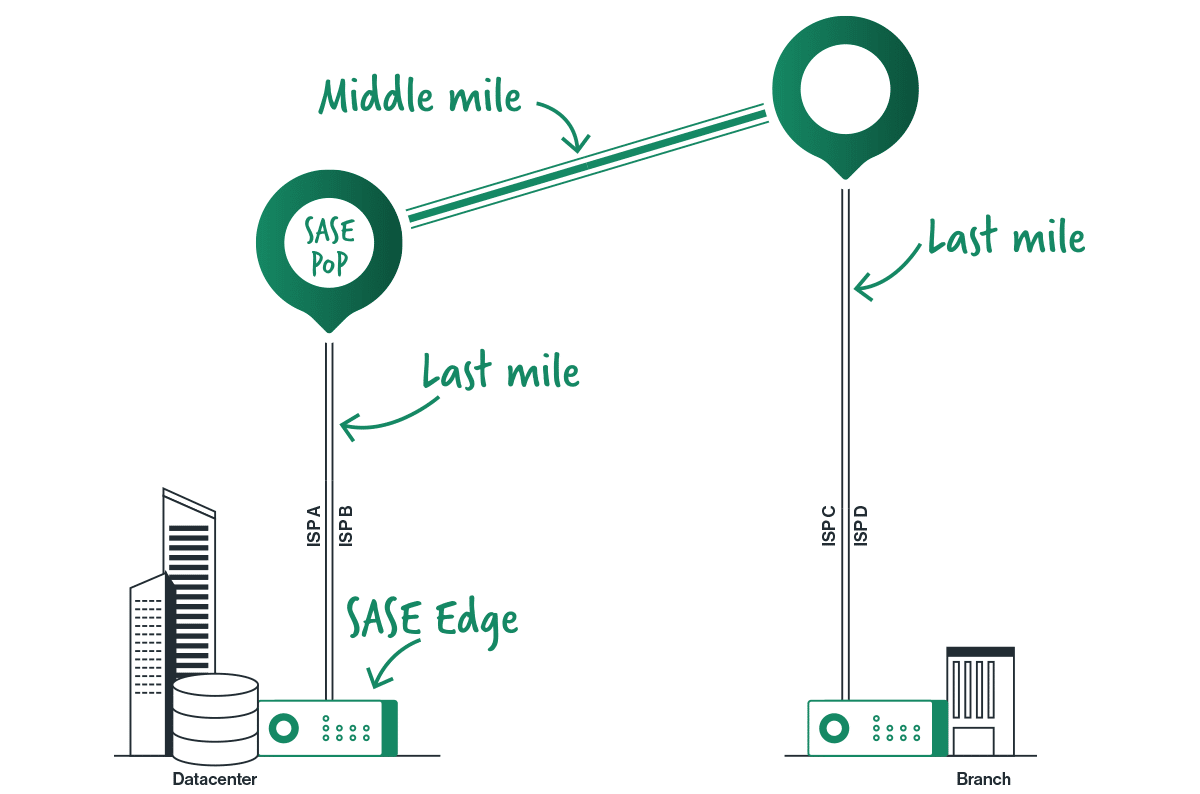
Meet the Industry’s First GPU-Powered SASE Platform with Native AI...
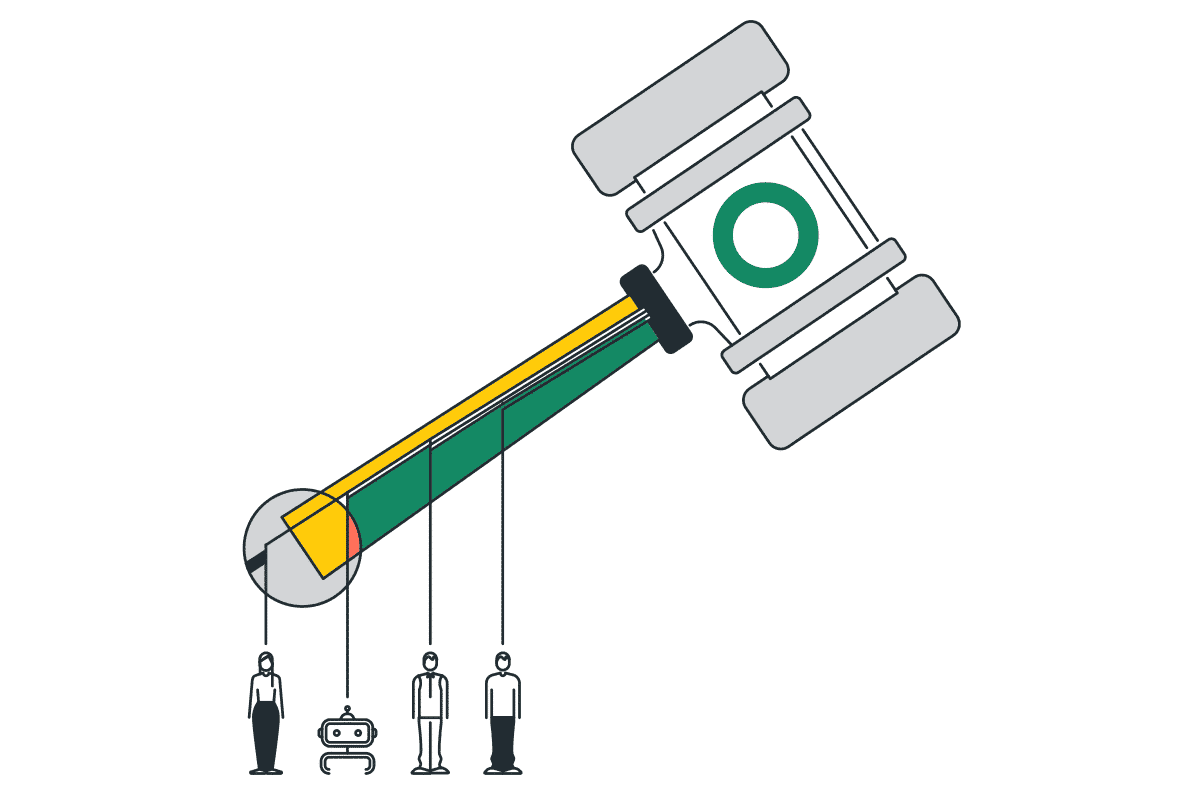
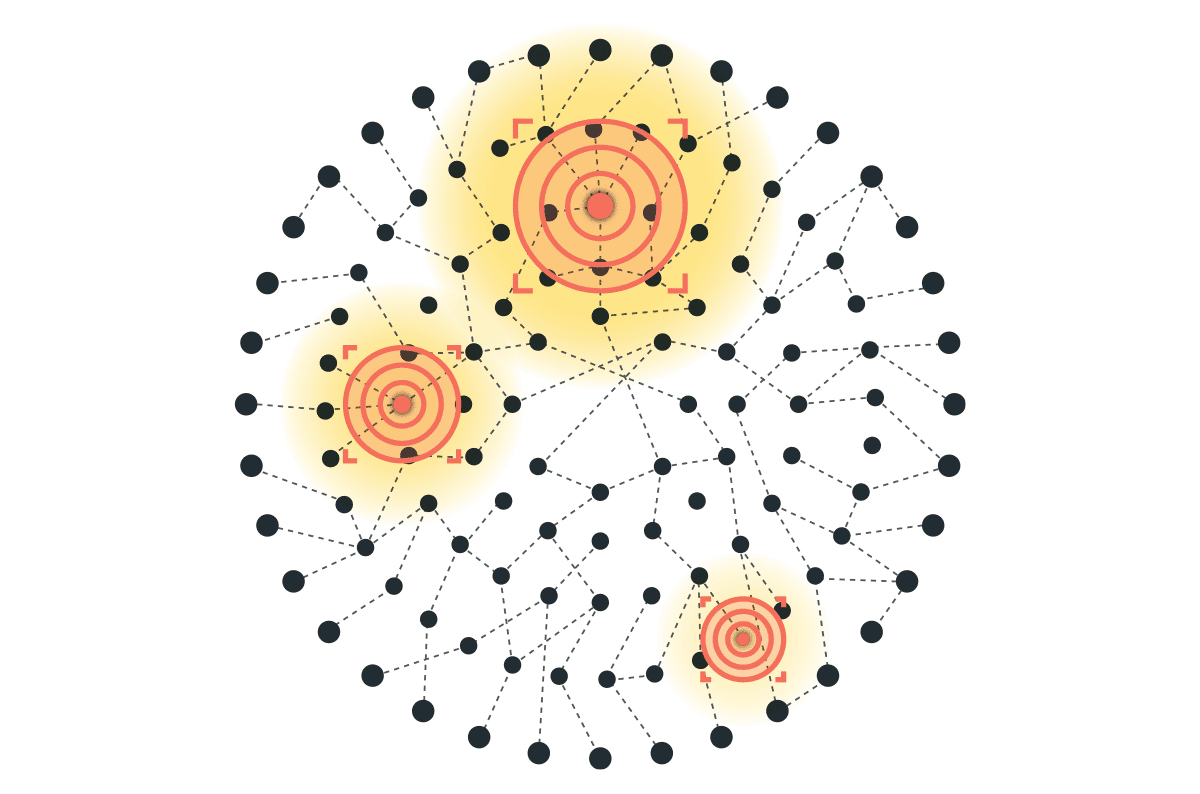
AI has moved from experimentation to a strategic enterprise imperative. It’s no longer about whether organizations will adopt AI, but whether their security architecture can...